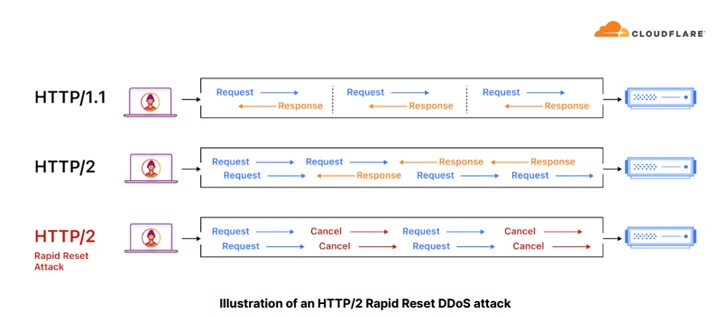
Cloudflare on Thursday mentioned it mitigated 1000’s of hyper-volumetric HTTP distributed denial-of-service (DDoS) assaults that exploited a lately disclosed flaw referred to as HTTP/2 Speedy Reset, 89 of which exceeded 100 million requests per second (RPS).
“The marketing campaign contributed to an total enhance of 65% in HTTP DDoS assault site visitors in Q3 in comparison with the earlier quarter,” the net infrastructure and safety firm mentioned in a report shared with The Hacker Information. “Equally, L3/4 DDoS assaults additionally elevated by 14%.”
The overall variety of HTTP DDoS assault requests within the quarter surged to eight.9 trillion, up from 5.4 trillion in Q2 2023 and 4.7 trillion in Q1 2023. The variety of assault requests in This fall 2022 stood at 6.5 trillion.
HTTP/2 Speedy Reset (CVE-2023-44487) got here to gentle earlier this month following an industry-wide coordinated disclosure that delved into DDoS assaults orchestrated by an unknown actor by leveraging the flaw to focus on varied suppliers akin to Amazon Net Providers (AWS), Cloudflare, and Google Cloud.
Fastly, in a disclosure of its personal on Wednesday, mentioned it countered the same assault that peaked at a quantity of about 250 million RPS and a length of roughly three minutes.
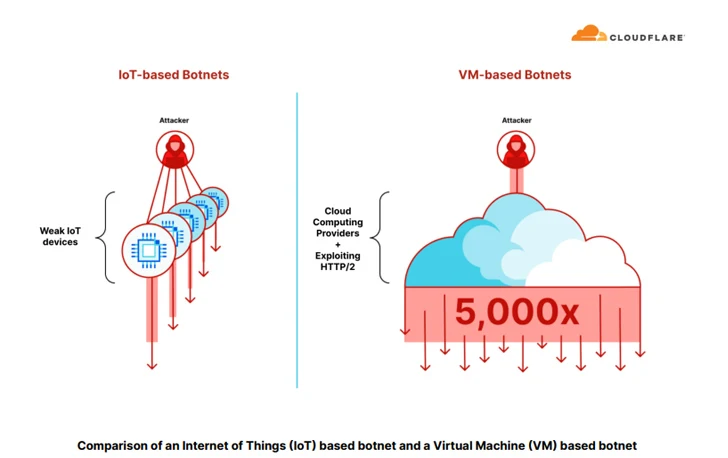
“Botnets that leverage cloud computing platforms and exploit HTTP/2 are capable of generate as much as x5,000 extra drive per botnet node,” Cloudflare famous. “This allowed them to launch hyper-volumetric DDoS assaults with a small botnet ranging 5-20 thousand nodes alone.”
A number of the high industries focused by HTTP DDoS assaults embody gaming, IT, cryptocurrency, laptop software program, and telecom, with the U.S., China, Brazil, Germany, and Indonesia accounting for the most important sources of software layer (L7) DDoS assaults.
Then again, the U.S., Singapore, China, Vietnam, and Canada emerged as the principle targets of HTTP DDoS assaults.
“For the second consecutive quarter, DNS-based DDoS assaults had been the commonest,” the corporate mentioned. “Virtually 47% of all assaults had been DNS-based. This represents a 44% enhance in comparison with the earlier quarter. SYN floods stay in second place, adopted by RST floods, UDP floods, and Mirai assaults.”
One other notable change is the lower in ransom DDoS assaults, which Cloudflare mentioned “is as a result of menace actors have realized that organizations won’t pay them.”
The disclosure comes amid web site visitors fluctuations and a spike in DDoS assaults within the aftermath of the Israel-Hamas warfare, with Cloudflare repelling a number of assault makes an attempt aimed toward Israeli and Palestinian web sites.