An up to date model of a complicated backdoor framework known as MATA has been utilized in assaults aimed toward over a dozen Jap European corporations within the oil and gasoline sector and protection trade as a part of a cyber espionage operation that happened between August 2022 and Might 2023.
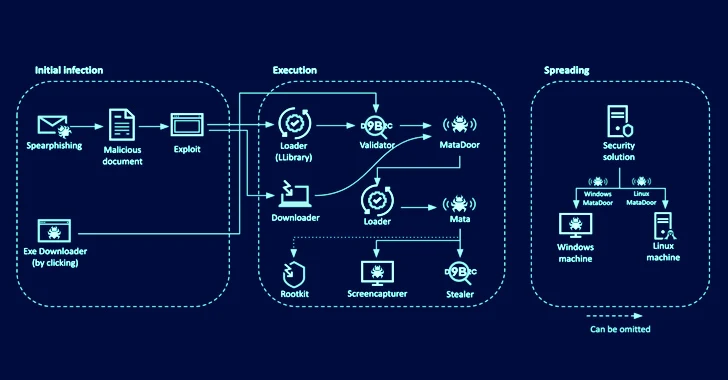
“The actors behind the assault used spear-phishing mails to focus on a number of victims, some had been contaminated with Home windows executable malware by downloading information via an web browser,” Kaspersky stated in a brand new exhaustive report printed this week.
“Every phishing doc comprises an exterior hyperlink to fetch a distant web page containing a CVE-2021-26411 exploit.”
CVE-2021-26411 (CVSS rating: 8.8) refers to a reminiscence corruption vulnerability in Web Explorer that might be triggered to execute arbitrary code by tricking a sufferer into visiting a specifically crafted web site. It was beforehand exploited by the Lazarus Group in early 2021 to focus on safety researchers.
The cross-platform MATA framework was first documented by the Russian cybersecurity firm in July 2020, linking it to the prolific North Korean state-sponsored crew in assaults focusing on numerous sectors in Poland, Germany, Turkey, Korea, Japan, and India since April 2018.
The usage of a revamped model of MATA to strike protection contractors was beforehand disclosed by Kaspersky in July 2023, though attribution to the Lazarus Group stays tenuous at finest because of the presence of methods utilized by 5 Eyes APT actors akin to Purple Lambert, Magenta Lambert, and Inexperienced Lambert.
That stated, a majority of the malicious Microsoft Phrase paperwork created by the attackers characteristic a Korean font known as Malgun Gothic, suggesting that the developer is both acquainted with Korean or works in a Korean surroundings.
Russian cybersecurity firm Optimistic Applied sciences, which shared particulars of the identical framework late final month, is monitoring the operators beneath the moniker Darkish River.
“The group’s important device, the MataDoor backdoor, has a modular structure, with a posh, totally designed system of community transports and versatile choices for communication between the backdoor operator and an contaminated machine,” safety researchers Denis Kuvshinov and Maxim Andreev stated.
“The code evaluation means that the builders invested appreciable assets into the device.”
The newest assault chains start with the actor sending spear-phishing paperwork to targets, in some circumstances by impersonating reliable workers, indicating prior reconnaissance and intensive preparation. These paperwork embrace a hyperlink to an HTML web page that embeds an exploit for CVE-2021-26411.
A profitable compromise results in the execution of a loader that, in flip, retrieves a Validator module from a distant server to ship system info and obtain and add information to and from the command-and-control (C2) server.
The Validator can also be designed to fetch MataDoor, which, in response to Kasperksy, is MATA era 4 that is geared up to run a variety of instructions able to gathering delicate info from compromised programs.
The assaults are additional characterised by way of stealer malware to seize content material from clipboard, file keystrokes, take screenshots, and siphon passwords and cookies from the Home windows Credential Supervisor and Web Explorer.
One other noteworthy device is a USB propagation module that permits for sending instructions to the contaminated system by way of detachable media, possible enabling the risk actors to infiltrate air-gapped networks. Additionally employed is an exploit known as CallbackHell to raise privileges and bypass endpoint safety merchandise in order to realize their objectives with out attracting consideration.
Kaspersky stated it additionally found a brand new MATA variant, dubbed MATA era 5 or MATAv5, that is “utterly rewritten from scratch” and “reveals a complicated and sophisticated structure making use of loadable and embedded modules and plugins.”
“The malware leverages inter-process communication (IPC) channels internally and employs a various vary of instructions, enabling it to ascertain proxy chains throughout numerous protocols – additionally inside the sufferer’s surroundings,” the corporate added.
In complete, the MATA framework and its cocktail of plugins incorporate assist for over 100 instructions pertaining to info gathering, occasion monitoring, course of administration, file administration, community reconnaissance, and proxy performance.
“The actor demonstrated excessive capabilities of navigating via and leveraging safety options deployed within the sufferer’s surroundings,” Kaspersky stated.
“Attackers used many methods to cover their exercise: rootkits and susceptible drivers, disguising information as reliable purposes, utilizing ports open for communication between purposes, multi-level encryption of information and community exercise of malware, [and] setting lengthy wait occasions between connections to manage servers.”