
Three malicious Chrome extensions posing as VPN (Digital Non-public Networks) contaminated had been downloaded 1.5 million instances, performing as browser hijackers, cashback hack instruments, and knowledge stealers.
In accordance with ReasonLabs, which found the malicious extensions, they’re unfold through an installer hidden in pirated copies of common video video games like Grand Theft Auto, Assassins Creed, and The Sims 4, that are distributed from torrent websites.
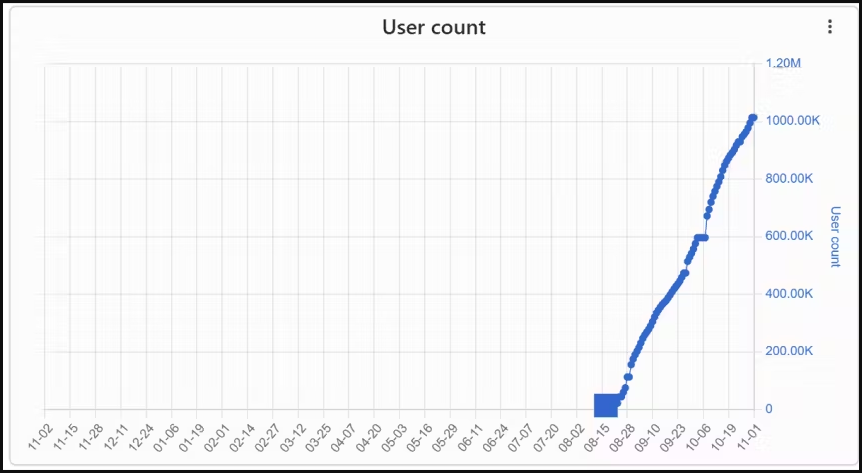
ReasonLabs notified Google of its findings, and the tech large eliminated the offending extensions from the Chrome Internet Retailer, however solely after these had amassed a complete of 1.5 million downloads.
Particularly, the malicious extensions had been netPlus (1 million installs), netSave, and netWin (500,000 installs).
Most infections are in Russia and international locations like Ukraine, Kazakhstan, and Belarus, so the marketing campaign seems to focus on Russian-speaking customers.
Planting faux VPN extensions
ReasonLabs found over a thousand distinct torrent information that ship the malicious installer file, which is an electron app measuring between 60MB and 100MB in dimension.
The set up of the VPN extensions is automated and compelled, happening on the registry degree, and doesn’t contain the consumer or require any motion on the sufferer’s facet.
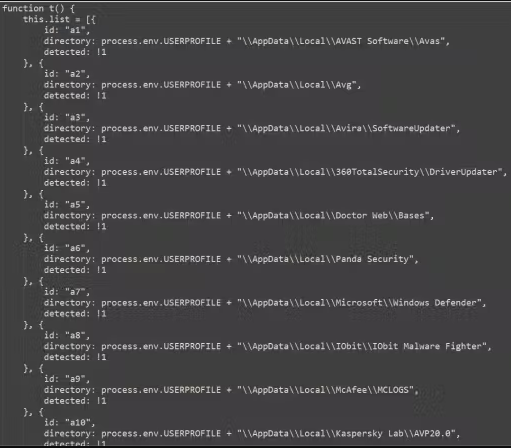
Ultimately, the installer checks for antivirus merchandise on the contaminated machine, then drops netSave on Google Chrome and netPlus on Microsoft Edge, protecting both use case.
The malicious extensions use a practical VPN consumer interface with some performance and a paid subscription choice to create a way of authenticity.
Code evaluation reveals that the extension additionally has entry to “tabs,” “storage,” “proxy,” “webRequest,” “webRequestBlocking,” “declarativeNetRequest,” “scripting,” “alarms,” “cookies,” “activeTab,” “administration,” and “offscreen.”
ReasonLabs factors out that the abuse of the ‘offscreen’ permission permits the malware to run scripts by means of the Offscreen API and stealthily work together with the net web page’s present DOM (Doc Object Mannequin).
This intensive entry to the DOM permits the extensions to steal delicate consumer knowledge, carry out searching hijacks, manipulate internet requests, and even disable different extensions put in on the browser.
One other operate of the extension is to disable different cashback and coupon extensions to remove competitors on the contaminated machine and redirect earnings to the attackers.
ReasonLabs studies the malware targets over 100 cashback extensions, together with Avast SafePrice, AVG SafePrice, Honey: Automated Coupons & Rewards, LetyShops, Megabonus, AliRadar Procuring Assistant, Yandex.Market Adviser, ChinaHelper, and Backlit.
The extensions’ communication with the C2 (command and management) servers includes knowledge alternate regarding directions and instructions, IDing the sufferer, exfiltrating delicate knowledge, and extra.
This report highlights the huge safety points round internet browser extensions, lots of that are extremely obfuscated to make it more durable to find out what habits they exhibit.
Because of this, it’s best to routinely examine the extensions put in in your browser and examine for brand new opinions within the Chrome Internet Retailer to see if others are reporting malicious habits.


