
A phishing marketing campaign is utilizing a pretend Google Account safety web page to ship a web-based app able to stealing one-time passcodes, harvesting cryptocurrency pockets addresses, and proxying attacker site visitors via victims’ browsers.
The assault leverages Progressive Internet App (PWA) options and social engineering to deceive customers into believing they’re interacting with a legit Google Safety internet web page and inadvertently putting in the malware.
PWAs run within the browser and may be put in from a web site, identical to a standalone common utility, which is displayed in its personal window with none seen browser controls.
Sufferer browser turns into attacker’s proxy
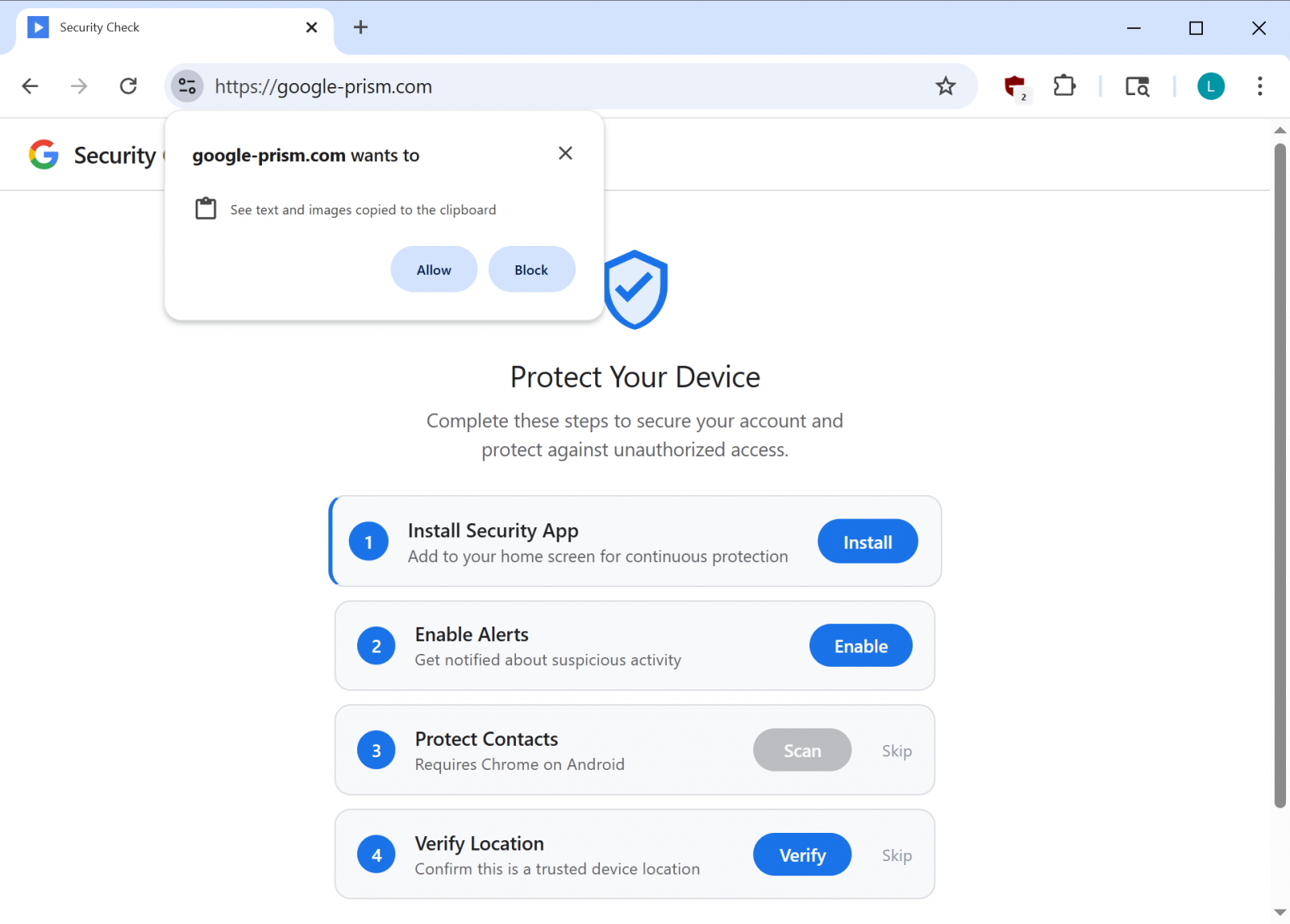
The marketing campaign depends on social engineering to acquire the mandatory permissions from the consumer beneath the guise of a safety verify and elevated safety for units.
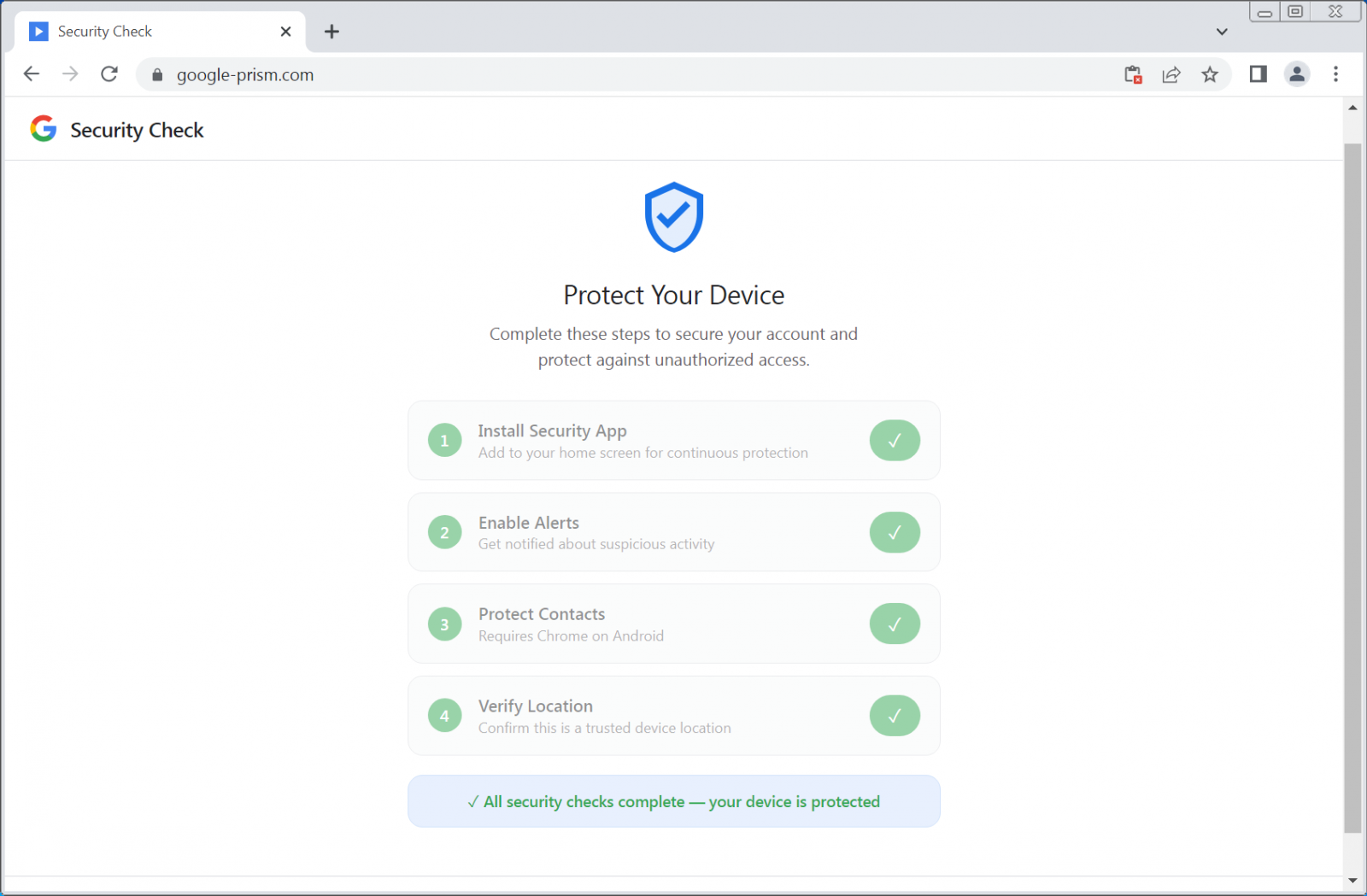
The cybercriminals use the area google-prism[.]com, which poses as a legit security-related service from Google, displaying a four-step setup course of that features giving dangerous permissions and putting in a malicious PWA app. In some situations, the positioning may even promote a companion Android app to “defend” contacts.
Based on researchers at cybersecurity firm Malwarebytes, the PWA app can exfiltrate contacts, real-time GPS knowledge, and clipboard contents.
Further performance noticed contains performing as a community proxy and inner port scanner, which permits the attacker to route requests via the sufferer’s browser and establish stay hosts on the community.
The web site additionally requests permissions to entry textual content and pictures copied to the clipboard, which might happen solely when the app is open.
supply: BleepingComputer
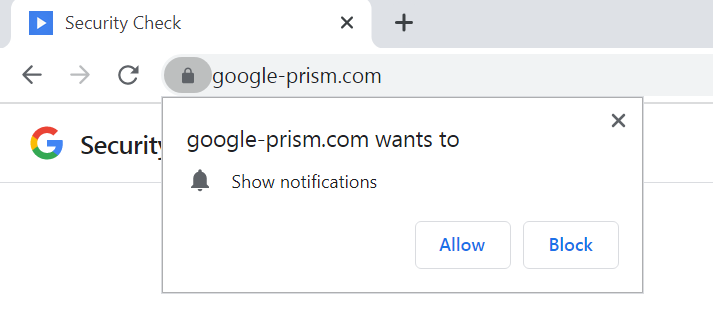
Nevertheless, the pretend web site additionally asks for permission to indicate notifications, which permits the attacker to push alerts, new duties, or set off knowledge exfiltration.
Moreover, the malware makes use of the WebOTP API on supported browsers in an try to intercept SMS verification codes, and checks the /api/heartbeat each 30 seconds for brand spanking new instructions.
Because the PWA app can solely steal the contents of the clipboard and OTP codes when it’s open, notifications can be utilized to ship pretend safety alerts that immediate the consumer to open the PWA once more.
supply: BleepingComputer
Malwarebytes says that the main focus is on stealing one-time passwords (OTP) and cryptocurrency pockets addresses, and that the malware additionally “builds an in depth system fingerprint.”
One other element within the malicious PWA is a service employee that’s answerable for push notifications, operating duties from obtained payloads, and getting ready stolen knowledge regionally for exfiltration.
The researchers say that probably the most regarding element is the WebSocket relay that permits the attacker to go internet requests via the browser as in the event that they have been on the sufferer’s community.
“The malware acts as an HTTP proxy, executing fetch requests with no matter methodology, headers, credentials, and physique the attacker specifies, then returns the complete response together with headers” – Malwarebytes
As a result of the employee features a handler for Periodic Background Sync, which permits internet apps in Chromium-based browsers to periodically synchronize knowledge within the background, the attacker can connect with a compromised system for so long as the malicious PWA app is put in.
Malware Android companion
Customers who select to activate all of the security measures for his or her account additionally obtain an APK file for his or her Android units that guarantees to increase safety to the record of contacts.
supply: BleepingComputer
The payload is described as a “vital safety replace, ”claims to be verified by Google, and requires 33 permissions that embrace entry to SMS texts, name logs, the microphone, contacts, and the accessibility service.
These alone are high-risk permissions that allow knowledge theft, full system compromise, and monetary fraud.
The malicious APK file contains a number of elements, resembling a customized keyboard to seize keystrokes, a notification listener for entry to incoming notifications, and a service to intercept credentials crammed mechanically.
“To boost persistence, the APK registers as a tool administrator (which might complicate uninstallation), units a boot receiver to execute on startup, and schedules alarms supposed to restart elements if terminated,” the researchers say.
Malwarebytes noticed elements that may very well be used for overlay-based assaults, which point out plans for potential credential phishing in sure apps.
By combining legit browser options with social engineering, the attacker doesn’t want to use any vulnerability. As an alternative, they trick the sufferer into offering all of the wanted permissions for malicious exercise to happen.
The researchers warn that even when the Android APK is just not put in, the online app can acquire contacts, intercept one-time passwords, monitor location, scan inner networks, and proxy site visitors via the sufferer’s system.
Customers must be conscious that Google doesn’t run safety checks via pop-ups on internet pages or request any software program set up for enhanced safety options. All safety instruments can be found via the Google Account at myaccount.google.com.
To take away the malicious APK file, Malwarebytes recommends customers search for a “Safety Verify” entry within the record of put in apps and prioritize uninstalling it.
If an app referred to as “System Service” with a bundle title com.system.sync is current and has system administrator entry, customers ought to revoke it beneath Settings > Safety > System admin apps after which uninstall it.
Malwarebytes researchers additionally present detailed steps for eradicating the malicious internet app from each Chromium-based Home windows, resembling Google Chrome and Microsoft Edge, in addition to from Safari.
They be aware that on Firefox and Safari browsers, most of the malicious app’s capabilities are severely restricted, however push notifications nonetheless work.



