
Greater than 40,000 Cisco units working the IOS XE working system have been compromised after hackers exploited a just lately disclosed most severity vulnerability tracked as CVE-2023-20198.
There is no such thing as a patch or a workaround accessible and the one suggestion for purchasers to safe the units is to “disable the HTTP Server characteristic on all internet-facing programs.”
Networking gear working Cisco IOS XE consists of enterprise switches, industrial routers, entry factors, wi-fi controllers, aggregation, and department routers.
Tens of hundreds of Cisco units uncovered
Preliminary estimates of breached Cisco IOS XE units have been round 10,000 and the quantity began rising as safety researchers scanned the web for a extra correct determine.
On Tuesday, the LeakIX engine for indexing providers and net functions uncovered on the general public net stated they discovered about 30,000 contaminated units, with out counting the rebooted programs.
The search relied on the symptoms of compromise (IoCs) that Cisco supplied to find out the profitable exploitation of CVE-2023-20198 on an uncovered machine and revealed hundreds of contaminated hosts in the US, the Philippines, and Chile.

supply: LeakIX
Utilizing the identical verification methodology from Cisco, the non-public CERT from Orange introduced on Wednesday that there have been greater than 34,500 Cisco IOS XE IP addresses with a malicious implant because of exploiting CVE-2023-20198.
CERT Orange additionally printed a Python script to scan for the presence of a malicious implant on a community machine working Cisco IOS XE.
In an replace on October 18, the Censys search platform for assessing assault floor for internet-connected units stated that the variety of compromised units it discovered elevated to 41,983.
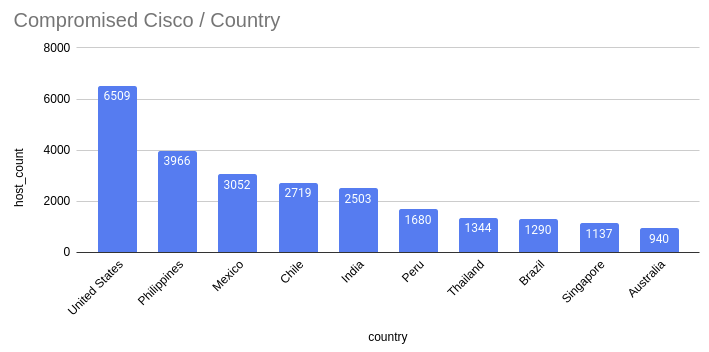
supply: Censys
A exact variety of Cisco IOS XE units reachable over the general public web is tough to acquire however Shodan exhibits a bit of over 145,000 hosts, most of them within the U.S.
Beneath is a screenshot with Shodan outcomes for Cisco units which have their Internet UI accessible over the web, utilizing a question from Simo Kohonen, the CEO of Aves Netsec cybersecurity firm.
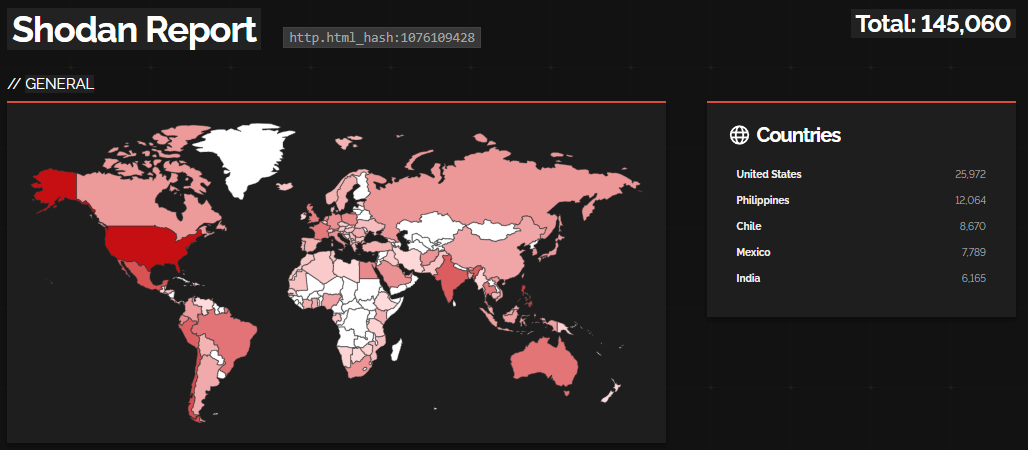
supply: BleepingComputer
Safety researcher Yutaka Sejiyama additionally searched Shodan for Cisco IOS XE units weak to CVE-2023-20198 and located near 90,000 hosts uncovered on the internet.
Within the U.S., lots of the units are from communications suppliers reminiscent of Comcast, Verizon, Cox Communications, Frontier, AT&T, Spirit, CenturyLink, Constitution, Cobridge, Windstream, and Google Fiber.
Sejiyama’s checklist additionally consists of medical facilities, universities, sheriff’s workplaces, college districts, comfort shops, banks, hospitals, and authorities entities with Cisco IOS XE units uncovered on-line.
“There is no such thing as a want to reveal the IOS XE login display screen on the Web within the first place,” Sejiyama advised BleepingComputer, echoing Cisco’s recommendation of not exposing the online UI and administration providers to the general public net or to untrusted networks.
The researcher expressed concern at this practices, saying that “organizations utilizing the tools in such a fashion are prone to be unaware of this vulnerability or breach.”
Threat persists after machine reboot
Cisco disclosed CVE-2023-20198 on Monday however menace actors had been leveraging it earlier than September 28, when it was a zero-day, to create a high-privilege account on affected hosts and take full management of the machine.
Cisco up to date its advisory at the moment with new attacker IP addresses and usernames, in addition to contemporary guidelines for the Snort open-source community intrusion detection system and intrusion prevention system.
The researchers notice that menace actors behind these assaults use a malicious implant, which doesn’t have persistence and is eliminated after rebooting the machine.
Nevertheless, the brand new accounts it helped create proceed to be lively and “have degree 15 privileges, that means they’ve full administrator entry to the machine.”
Primarily based on Cisco’s evaluation, the menace actor collects particulars in regards to the machine and carries out preliminary reconnaissance exercise. The attacker can be clearing logs and eradicating customers, most likely to cover their exercise.
The researchers consider that behind these assaults is just one menace actor however couldn’t decide the preliminary supply mechanism.
Cisco has not disclosed further particulars in regards to the assaults however promised to supply extra info when it completes the investigation and when a repair is accessible.


