
Web safety watchdog Shadowserver has discovered over 25,000 Fortinet gadgets uncovered on-line with FortiCloud SSO enabled, amid ongoing assaults concentrating on a essential authentication bypass vulnerability.
Fortinet famous on December ninth, when it patched the safety flaw tracked as CVE-2025-59718 (FortiOS, FortiProxy, FortiSwitchManager) and CVE-2025-59719 (FortiWeb), that the susceptible FortiCloud SSO login characteristic isn’t enabled till admins register the machine with the corporate’s FortiCare help service.
As cybersecurity firm Arctic Wolf reported on Monday, the vulnerability is now actively exploited to compromise admin accounts through malicious single sign-on (SSO) logins.
Menace actors are abusing it in susceptible merchandise through a maliciously crafted SAML message to achieve admin-level entry to the net administration interface and obtain system configuration information. These delicate information expose doubtlessly susceptible interfaces, hashed passwords that attackers could crack, internet-facing companies, community layouts, and firewall insurance policies.
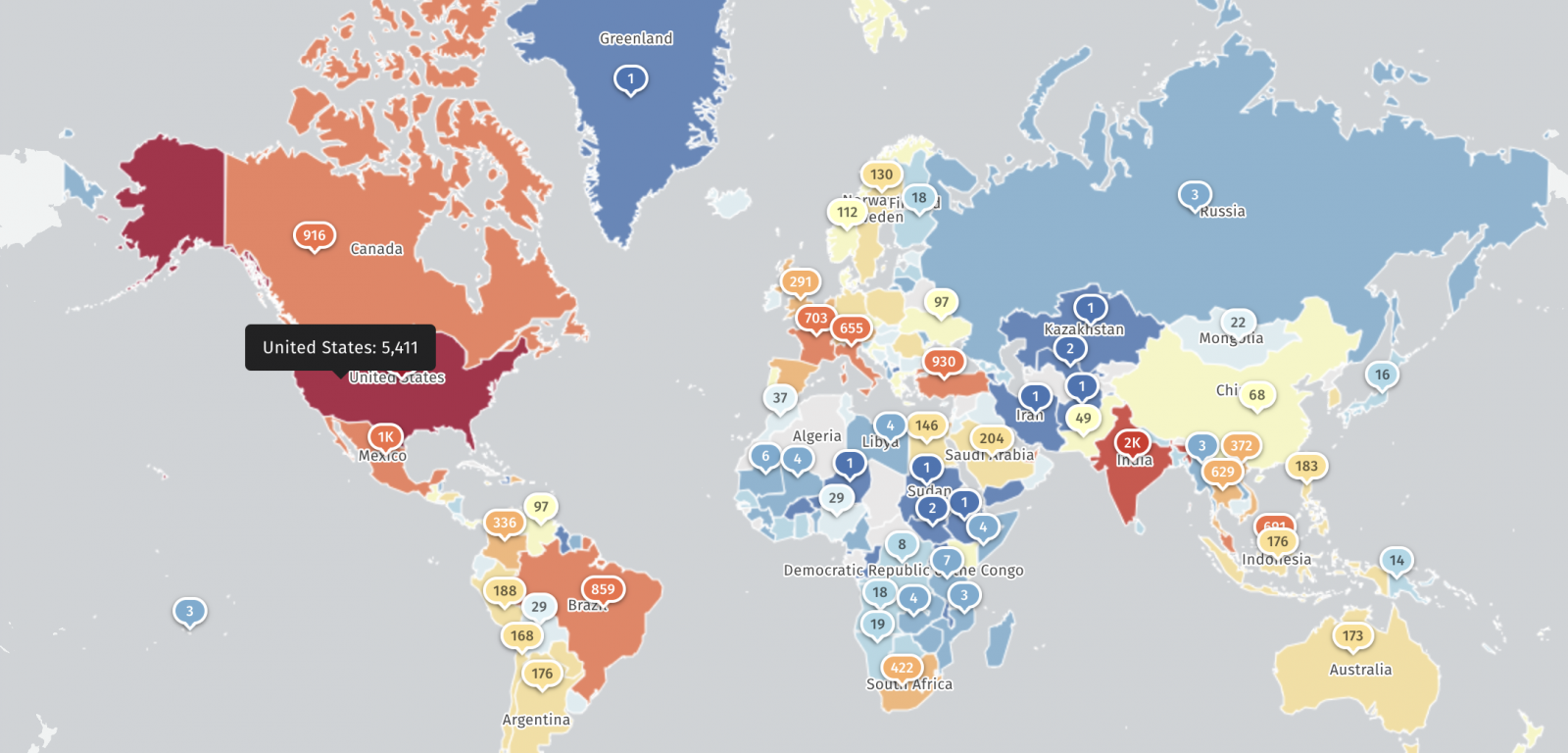
Immediately, Shadowserver mentioned it is monitoring over 25,000 IP addresses with a FortiCloud SSO fingerprint, greater than 5,400 in america and almost 2,000 in India.
Nonetheless, there is presently no data relating to what number of have been secured towards assaults exploiting the CVE-2025-59718/CVE-2025-59719 vulnerability.
Macnica menace researcher Yutaka Sejiyama additionally instructed BleepingComputer that his scans returned over 30,000 Fortinet gadgets with FortiCloud SSO enabled, which additionally expose susceptible internet administration interfaces to the web.
“Given how incessantly FortiOS admin GUI vulnerabilities have been exploited prior to now, it’s shocking that this many admin interfaces stay publicly accessible,” Sejiyama mentioned.
On Tuesday, CISA added the FortiCloud SSO auth bypass flaw to its catalog of actively exploited vulnerabilities, ordering U.S. authorities businesses to patch inside per week, by December twenty third, as mandated by the Binding Operational Directive 22-01.
Fortinet safety flaws are incessantly exploited by cyber-espionage, cybercrime, or ransomware teams, usually as zero-day vulnerabilities.
For example, in February, Fortinet disclosed that the infamous Chinese language Volt Storm hacking group exploited two FortiOS SSL VPN flaws (CVE-2023-27997 and CVE-2022-42475) to backdoor a Dutch Ministry of Defence navy community utilizing customized Coathanger distant entry trojan (RAT) malware.
Extra just lately, in November, Fortinet warned of a FortiWeb zero-day (CVE-2025-58034) being exploited within the wild, one week after confirming that it had silently patched one other FortiWeb zero-day (CVE-2025-64446) that was abused in widespread assaults.
Damaged IAM is not simply an IT downside – the affect ripples throughout your complete enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM appears like, and a easy guidelines for constructing a scalable technique.




