A brand new malware is bypassing an Android 13 safety measure that restricts permissions to apps downloaded out of the respectable Google Play Retailer.
A brand new report from ThreatFabric, a fraud safety firm, exposes SecuriDropper malware, which is able to bypassing Android 13 restricted settings. The malware makes Android take into account the set up as coming from the Google Play Retailer, although in actuality it isn’t.
It’s extremely advisable for organizations to make use of Cell System Administration options and strategies to allow extra management on staff’ Android units and to limit putting in apps on their units by utilizing an inventory of authorised purposes and forbidding every other.
Leap to:
What are Android 13’s restricted settings?
Android 13 launched a brand new safety characteristic referred to as restricted settings. This new characteristic prevents sideloaded purposes (i.e., downloaded out of the Google Play Retailer) from instantly requesting accessibility settings and notification listener entry — two options which might be typically abused by malware in response to ThreatFabric’s researchers.
On Android programs, purposes downloaded from the respectable Google Play Retailer aren’t topic to the identical course of as these not originating from it. The principle cause why is that purposes which have made it efficiently to the Google Play Retailer have supplied extra data and visibility and have handed completely different safety assessments to make sure they don’t comprise malware functionalities. Due to this fact, purposes from the Google Play Retailer aren’t involved by the restricted settings characteristic.
Functions downloaded from the Play Google Retailer use a particular set up technique — a “session-based” bundle installer — that isn’t usually utilized by sideloaded purposes.
Meet SecuriDropper malware
The SecuriDropper malware makes use of the identical set up technique as respectable software program from the respectable Google Play Retailer. After being executed by the unsuspecting consumer, the malware requests two key permissions: Learn & Write Exterior Storage and Set up & Delete Packages.
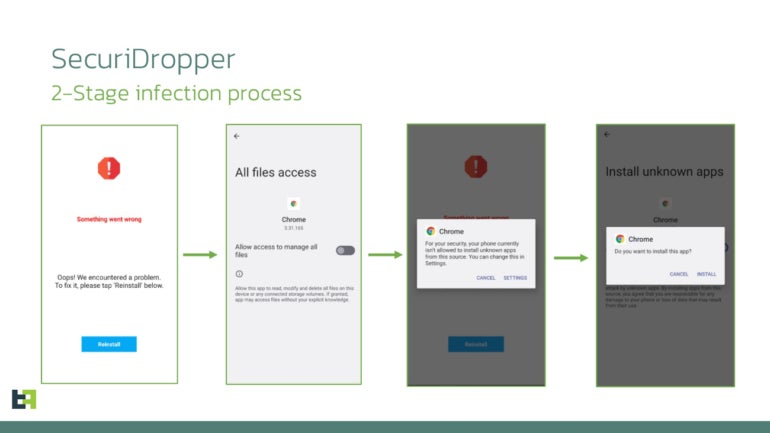
As soon as permissions are given, the malware checks if it already exists on the system; if it does, the malware runs, and if it doesn’t, the malware exhibits the consumer a message telling them one thing went flawed and the consumer must click on a reinstall button. The message is completely different based mostly on the system’s location and language configured.
When executed, the session-based set up begins, and the consumer is requested for permission to allow the Accessibility Service, which turns into potential because of the bypass of the restricted settings characteristic (Determine A).
Determine A
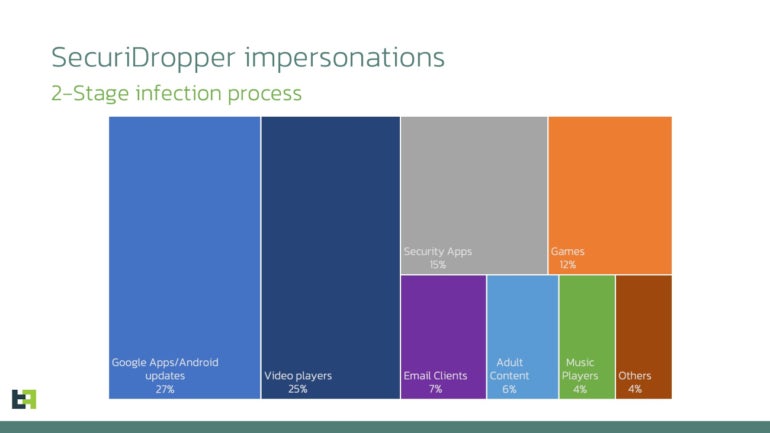
The malware has been noticed disguising itself as numerous Android purposes similar to Google Apps or Android updates (27%), video gamers (25%), safety purposes (15%) or video games (12%), adopted by e-mail purchasers, grownup content material, music gamers and different apps (Determine B).
Determine B
SecuriDropper’s numerous ultimate payloads
Any type of malicious code may very well be dropped and put in by SecuriDropper, because the malware’s ultimate objective is to put in different malware on contaminated units. ThreatFabric noticed two campaigns utilizing SecuriDropper.
The primary one is an assault marketing campaign delivering SpyNote, a malware with distant administration device options. The malicious payload was being distributed via phishing web sites and deployed by SecuriDropper. The SpyNote malware, which is ready to seize delicate data on the system, in addition to steal SMS and name logs and take screenshots, completely wants permissions that will be unavailable as a result of Android’s restricted settings. Its set up by way of SecuriDropper allows the SpyNote malware to maintain infecting units, even on Android 13, with no need to vary its code.
In one other assault marketing campaign, SecuriDropper was noticed putting in the ERMAC banking trojan. The malware was deployed by way of Discord, a communication device beforehand used primarily by avid gamers however more and more utilized by different communities, together with company entities.
Extra malware will use this system
Totally different malware households will use this system sooner or later. One service that’s already utilizing this system is Zombinder.
As reported by ThreatFabric, the DarkNet platform Zombinder began promoting for its new model that bypasses Android 13 restricted settings. The Zombinder service permits an attacker to efficiently bind a respectable utility with malware. When the an infection is completed, the respectable utility runs usually, whereas the malware is being executed within the background, unnoticed.
Zombinder additionally sells builders with the Android 13 restrictions bypass functionality. The builders from Zombinder are software program able to dropping malware on an contaminated system (aka dropper), bought at $1,000 USD.
As written by ThreatFabric, “the emergence of providers like Zombinder are indications of a booming market in cybercrime, providing builders and instruments for evading Android 13’s defenses. It’s a testomony to the resourcefulness of these looking for to take advantage of safety vulnerabilities for his or her achieve.”
Disclosure: I work for Development Micro, however the views expressed on this article are mine.


