A hacking group that leveraged a not too long ago disclosed safety flaw within the WinRAR software program as a zero-day has now been categorized as a completely new superior persistent menace (APT).
Cybersecurity firm NSFOCUS has described DarkCasino as an “economically motivated” actor that first got here to gentle in 2021.
“DarkCasino is an APT menace actor with sturdy technical and studying potential, who is sweet at integrating varied well-liked APT assault applied sciences into its assault course of,” the corporate mentioned in an evaluation.
“Assaults launched by the APT group DarkCasino are very frequent, demonstrating a powerful want to steal on-line property.”
DarkCasino was most not too long ago linked to the zero-day exploitation of CVE-2023-38831 (CVSS rating: 7.8), a safety flaw that may be weaponized to launch malicious payloads.
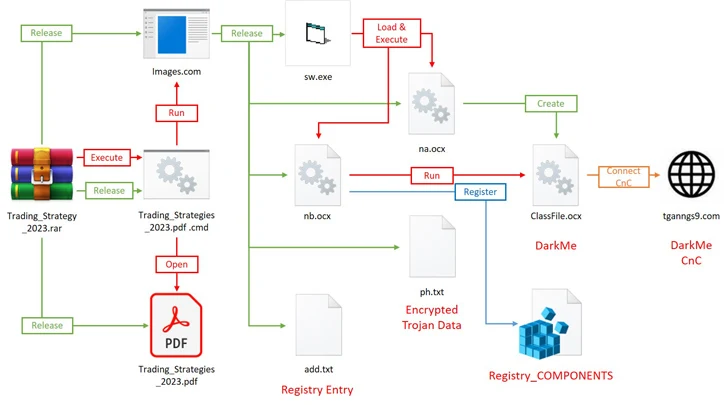
In August 2023, Group-IB disclosed real-world assaults weaponizing the vulnerability and aimed toward on-line buying and selling boards at the very least since April 2023 to ship a closing payload named DarkMe, which is a Visible Fundamental trojan attributed to DarkCasino.
The malware is supplied to gather host data, take screenshots, manipulate recordsdata and Home windows Registry, execute arbitrary instructions, and self-update itself on the compromised host.
Whereas DarkCasino was beforehand categorized as a phishing marketing campaign orchestrated by the Evilnum group concentrating on European and Asian on-line playing, cryptocurrency, and credit score platforms, NSFOCUS mentioned its steady monitoring of the adversary’s actions has allowed it rule out any potential connections with recognized menace actors.
The precise provenance of the menace actor is presently unknown.
“Within the early days, DarkCasino primarily operated in international locations across the Mediterranean and different Asian international locations utilizing on-line monetary providers,” it mentioned.
“Extra not too long ago, with the change of phishing strategies, its assaults have reached customers of cryptocurrencies worldwide, even together with non-English-speaking Asian international locations equivalent to South Korea and Vietnam.”
A number of menace actors have joined the CVE-2023-38831 exploitation bandwagon in current months, together with APT28, APT40, Darkish Pink, Ghostwriter, Konni, and Sandworm.
Ghostwriter’s assault chains leveraging the shortcoming have been noticed to pave the best way for PicassoLoader, an intermediate malware that acts as a loader for different payloads.
“The WinRAR vulnerability CVE-2023-38831 introduced by the APT group DarkCasino brings uncertainties to the APT assault state of affairs within the second half of 2023,” NSFOCUS mentioned.
“Many APT teams have taken benefit of the window interval of this vulnerability to assault important targets equivalent to governments, hoping to bypass the safety system of the targets and obtain their functions.”