A phishing marketing campaign has been noticed delivering an data stealer malware known as MrAnon Stealer to unsuspecting victims through seemingly benign booking-themed PDF lures.
“This malware is a Python-based data stealer compressed with cx-Freeze to evade detection,” Fortinet FortiGuard Labs researcher Cara Lin mentioned. “MrAnon Stealer steals its victims’ credentials, system data, browser classes, and cryptocurrency extensions.”
There’s proof to counsel that Germany is the first goal of the assault as of November 2023, owing to the variety of instances the downloader URL internet hosting the payload has been queried.
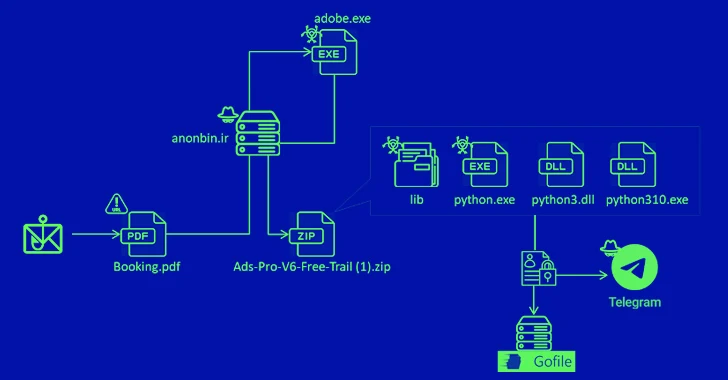
Masquerading as an organization trying to ebook resort rooms, the phishing e-mail bears a PDF file that, upon opening, prompts the an infection by prompting the recipient to obtain an up to date model of Adobe Flash.
Doing so leads to the execution of .NET executables and PowerShell scripts to finally run a pernicious Python script, which is able to gathering knowledge from a number of purposes and exfiltrating it to a public file-sharing web site and the risk actor’s Telegram channel.
It is also able to capturing data from prompt messaging apps, VPN purchasers, and recordsdata matching a desired listing of extensions.
MrAnon Stealer is obtainable by the authors for $500 per thirty days (or $750 for 2 months), alongside a crypter ($250 per thirty days) and a stealthy loader ($250 per thirty days).
“The marketing campaign initially disseminated Cstealer in July and August however transitioned to distributing MrAnon Stealer in October and November,” Lin mentioned. “This sample suggests a strategic strategy involving the continued use of phishing emails to propagate a wide range of Python-based stealers.”
The disclosure comes because the China-linked Mustang Panda is behind a spear-phishing e-mail marketing campaign focusing on the Taiwanese authorities and diplomats with an intention to deploy SmugX, a brand new variant of the PlugX backdoor that was beforehand uncovered by Test Level in July 2023.