Authorities entities within the Center East are the goal of recent phishing campaigns which can be designed to ship a brand new preliminary entry downloader dubbed IronWind.
The exercise, detected between July and October 2023, has been attributed by Proofpoint to a risk actor it tracks beneath the title TA402, which is also called Molerats, Gaza Cyber Gang, and shares tactical overlaps with a pro-Hamas hacking crew often called APT-C-23 (aka Arid Viper).
“In the case of state-aligned risk actors, North Korea, Russia, China, and Iran usually reap the lion’s share of consideration,” Joshua Miller, senior risk researcher at Proofpoint, mentioned in an announcement shared with The Hacker Information.
“However TA402, a Center Japanese superior persistent risk (APT) group that traditionally has operated within the pursuits of the Palestinian Territories, has constantly confirmed to be an intriguing risk actor able to extremely subtle cyber espionage with a deal with intelligence assortment.”
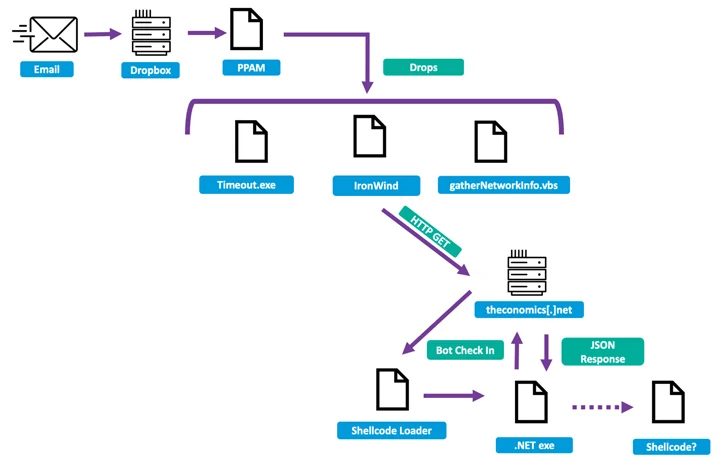
Coinciding with using IronWind are constant updates to its malware supply mechanisms, utilizing Dropbox hyperlinks, XLL file attachments, and RAR archives to distribute IronWind.
Using IronWind is a shift from prior assault chains, which had been linked to the propagation of a backdoor codenamed NimbleMamba in intrusions concentrating on Center Japanese governments and overseas coverage assume tanks.
TA402’s newest campaigns are characterised by way of a compromised e mail account belonging to the Ministry of International Affairs to ship phishing lures pointing to Dropbox hyperlinks that facilitate the deployment of IronWind.
The downloader is engineered to contact an attacker-controlled server to fetch further payloads, together with a post-exploitation toolkit referred to as SharpSploit, following a multi-stage sequence.
Subsequent social engineering campaigns in August and October 2023 have been discovered to leverage XLL file and RAR archive attachments embedded in e mail messages to set off the deployment of IronWind. One other notable tactic employed by the group is the reliance on geofencing methods to complicate detection efforts.
“The continued battle within the Center East doesn’t seem to have hindered their ongoing operations, as they proceed to iterate and use new and intelligent supply strategies to bypass detection efforts,” Miller mentioned.
“Utilizing complicated an infection chains and drumming up new malware to assault their targets, TA402 continues to have interaction in extraordinarily focused exercise with a robust deal with authorities entities based mostly within the Center East and North Africa.”
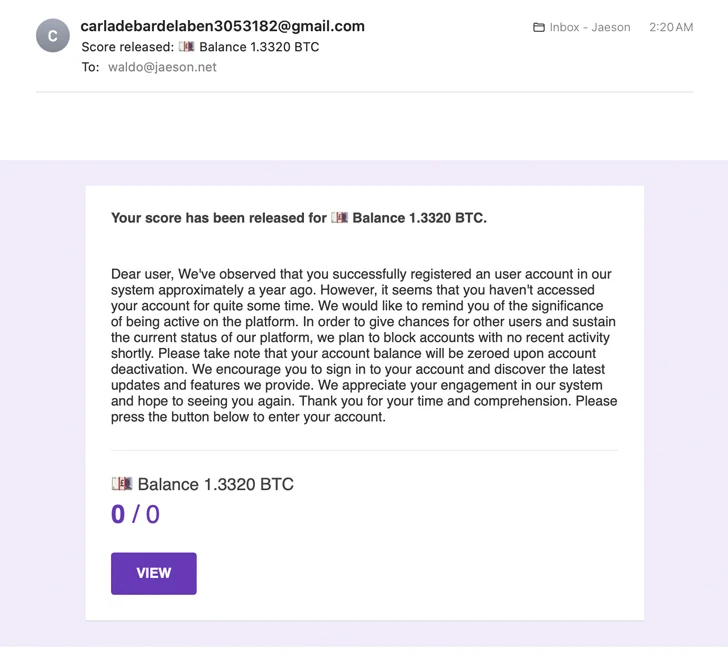
The event comes as Cisco Talos revealed that cybercriminals have been noticed exploiting the “Launch scores” function of Google Kinds quizzes to ship e mail and orchestrate elaborate cryptocurrency scams, highlighting the inventive methods risk actors resort to with the intention to meet their goals.
“The emails originate from Google’s personal servers and consequently might have a better time bypassing anti-spam protections and discovering the sufferer’s inbox,” safety researcher Jaeson Schultz mentioned final week.