An unspecified authorities entity in Afghanistan was focused by a beforehand undocumented net shell known as HrServ in what’s suspected to be a sophisticated persistent risk (APT) assault.
The online shell, a dynamic-link library (DLL) named “hrserv.dll,” reveals “subtle options reminiscent of customized encoding strategies for shopper communication and in-memory execution,” Kaspersky safety researcher Mert Degirmenci mentioned in an evaluation revealed this week.
The Russian cybersecurity agency mentioned it recognized variants of the malware courting all the best way again to early 2021 primarily based on the compilation timestamps of those artifacts.
Net shells are sometimes malicious instruments that present distant management over a compromised server. As soon as uploaded, it permits risk actors to hold out a variety of post-exploitation actions, together with information theft, server monitoring, and lateral development throughout the community.
The assault chain includes the PAExec distant administration software, a substitute for PsExec that is used as a launchpad to create a scheduled job that masquerades as a Microsoft replace (“MicrosoftsUpdate”), which subsequently is configured to execute a Home windows batch script (“JKNLA.bat”).
The Batch script accepts as an argument absolutely the path to a DLL file (“hrserv.dll”) that is then executed as a service to provoke an HTTP server that is able to parsing incoming HTTP requests for follow-on actions.
“Based mostly on the kind and knowledge inside an HTTP request, particular features are activated,” Degirmenci mentioned, including “the GET parameters used within the hrserv.dll file, which is used to imitate Google companies, embody ‘hl.'”
That is probably an try by the risk actor to mix these rogue requests in community site visitors and make it much more difficult to differentiate malicious exercise from benign occasions.
Embedded inside these HTTP GET and POST requests is a parameter known as cp, whose worth – starting from 0 to 7 – determines the following plan of action. This contains spawning new threads, creating information with arbitrary information written to them, studying information, and accessing Outlook Net App HTML information.
If the worth of cp within the POST request equals “6,” it triggers code execution by parsing the encoded information and copying it into the reminiscence, following which a brand new thread is created and the method enters a sleep state.
The online shell can be able to activating the execution of a stealthy “multifunctional implant” in reminiscence that is chargeable for erasing the forensic path by deleting the “MicrosoftsUpdate” job in addition to the preliminary DLL and batch information.
The risk actor behind the online shell is at present not identified, however the presence of a number of typos within the supply code signifies that the malware creator just isn’t a local English speaker.
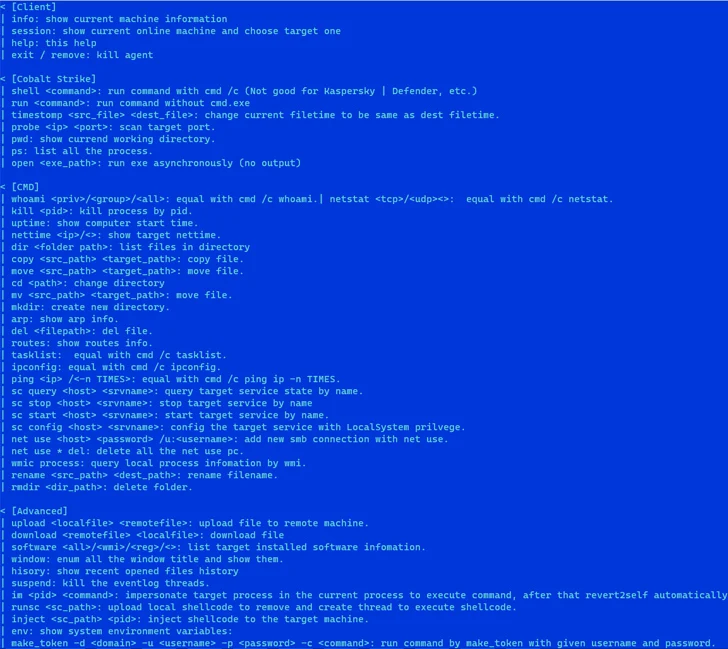
“Notably, the online shell and reminiscence implant use completely different strings for particular situations,” Degirmenci concluded. “As well as, the reminiscence implant encompasses a meticulously crafted assist message.”
“Contemplating these components, the malware’s traits are extra in line with financially motivated malicious exercise. Nonetheless, its operational methodology reveals similarities with APT conduct.”