A medium-severity flaw has been found in Synology’s DiskStation Supervisor (DSM) that might be exploited to decipher an administrator’s password and remotely hijack the account.
“Below some uncommon circumstances, an attacker might leak sufficient info to revive the seed of the pseudorandom quantity generator (PRNG), reconstruct the admin password, and remotely take over the admin account,” Claroty’s Sharon Brizinov stated in a Tuesday report.
The flaw, assigned the identifier CVE-2023-2729, is rated 5.9 for severity on the CVSS scoring scale. The flaw was addressed by Synology as a part of updates launched in June 2023.
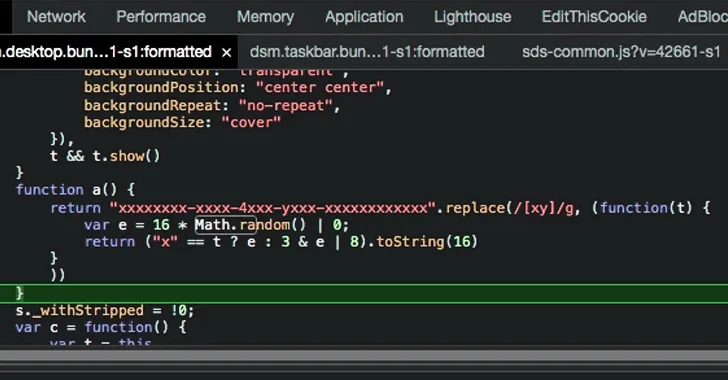
The issue is rooted in the truth that the software program makes use of a weak random quantity generator that depends on the JavaScript Math.random() technique to programmatically assemble the admin password for the network-attached storage (NAS) machine.
Known as insecure randomness, it arises when a operate that may produce predictable values, or does not have sufficient entropy, is used as a supply of randomness in a safety context, enabling an attacker to crack the encryption and defeat the integrity of delicate info and methods.
Profitable exploitation of such flaws, due to this fact, might enable the risk actor to predict the generated password and achieve entry to in any other case restricted performance.
“By leaking the output of some Math.Random() generated numbers, we had been in a position to reconstruct the seed for the PRNG and use it to brute-force the admin password,” Brizinov defined. “Lastly we had been ready to make use of the password to login to the admin account (after enabling it).”
The assault, nonetheless, hinges on an attacker efficiently extracting a number of GUIDs which might be additionally generated utilizing the identical technique through the setup course of to have the ability to reconstruct the seed phrase for the pseudorandom quantity generator (PRNG).
“In an actual life situation the attacker will first must leak the aforementioned GUIDs, brute power the Math.Random state, and achieve the admin password,” Brizinov stated. “Even after doing so, by default the builtin admin person account is disabled and most customers will not allow it.”
“Once more, it is vital to keep in mind that Math.random() doesn’t present cryptographically safe random numbers. Don’t use them for something associated to safety. Use the Net Crypto API as an alternative, and extra exactly the window.crypto.getRandomValues() technique.”