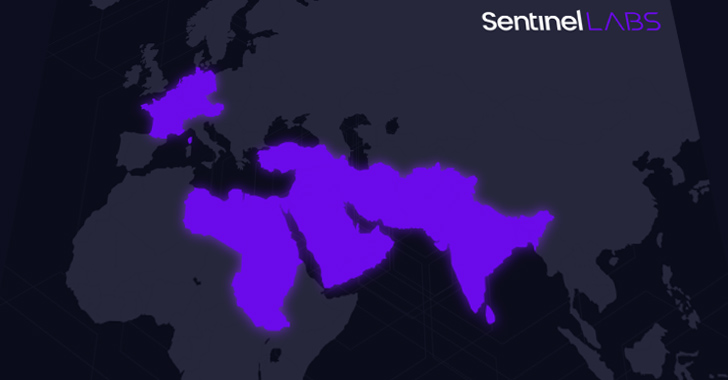
A beforehand undocumented risk actor dubbed Sandman has been attributed to a set of cyber assaults focusing on telecommunic koation suppliers within the Center East, Western Europe, and the South Asian subcontinent.
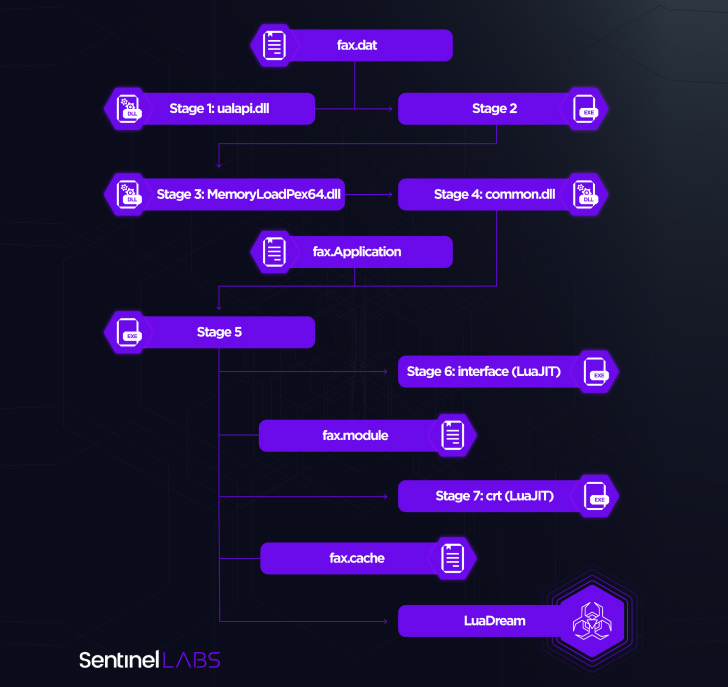
Notably, the intrusions leverage a just-in-time (JIT) compiler for the Lua programming language often called LuaJIT as a automobile to deploy a novel implant referred to as LuaDream.
“The actions we noticed are characterised by strategic lateral motion to particular focused workstations and minimal engagement, suggesting a deliberate method geared toward reaching the set aims whereas minimizing the danger of detection,” SentinelOne safety researcher Aleksandar Milenkoski mentioned in an evaluation printed in collaboration with QGroup.
“The implementation of LuaDream signifies a well-executed, maintained, and actively developed mission of a substantial scale.”
Neither the marketing campaign nor its techniques have been correlated with any identified risk actor or group, though obtainable proof factors to a cyber espionage adversary with a penchant for focusing on the telecom sector throughout geographies. The assaults had been first noticed over a number of weeks in August 2023.
“The LuaDream staging chain is designed to evade detection and thwart evaluation whereas deploying the malware immediately into reminiscence,” Milenkoski defined. “LuaDream’s implementation and staging course of leverage the LuaJIT platform, the just-in-time compiler for the Lua scripting language. That is primarily to make malicious Lua script code tough to detect.”

String artifacts contained throughout the implant’s supply code reference June 3, 2022, indicating that the preparatory work has been underway for greater than a yr.
It is suspected that LuaDream is a variant of a brand new malware pressure known as DreamLand by Kaspersky in its APT tendencies report for Q1 2023, with the Russian cybersecurity firm describing it as using “the Lua scripting language together with its just-in-time (JIT) compiler to execute malicious code that’s tough to detect.”
The usage of Lua-based malware is one thing of a rarity within the risk panorama, having been beforehand noticed solely in three completely different cases since 2012: Flame, Animal Farm (aka SNOWGLOBE), and Undertaking Sauron.
The precise mode of preliminary entry stays unclear, nevertheless it has been noticed stealing administrative credentials and conducting reconnaissance to breach workstations of curiosity and finally ship LuaDream.
A modular, multi-protocol backdoor with 13 core and 21 help parts, LuaDream is primarily designed to exfiltrate system and person data in addition to handle attacker-provided plugins that broaden on its options, reminiscent of command execution. It additionally options numerous anti-debugging capabilities to evade detection and thwart evaluation.
Command-and-control (C2) communication is completed by establishing contact with a site named “mode.encagil[.]com” utilizing the WebSocket protocol. However it will probably additionally hear for incoming connections over TCP, HTTPS, and QUIC protocols.
The core modules implement all the aforementioned options, whereas the help parts are chargeable for augmenting the backdoor’s capabilities to await connections primarily based on the Home windows HTTP server API and execute instructions.
“LuaDream stands as a compelling illustration of the continual innovation and development efforts that cyber espionage risk actors pour into their ever-evolving malware arsenal,” Milenkoski mentioned.
The disclosure coincides with a parallel report from SentinelOne which detailed sustained strategic intrusions by Chinese language risk actors in Africa, together with these geared toward telecommunication, finance and authorities sectors in Africa, as a part of exercise clusters dubbed BackdoorDiplomacy, Earth Estries, and Operation Tainted Love.
AI vs. AI: Harnessing AI Defenses In opposition to AI-Powered Dangers
Able to sort out new AI-driven cybersecurity challenges? Be a part of our insightful webinar with Zscaler to deal with the rising risk of generative AI in cybersecurity.
The aim, the corporate mentioned, is to increase affect all through the continent and leverage such offensives as a part of its tender energy agenda.
SentinelOne mentioned it detected a compromise of a telecommunications entity primarily based in North Africa by the identical risk actor behind Operation Tainted Love, including the timing of the assault aligned with the group’s personal negotiations for additional regional enlargement.
“Focused intrusions by the BackdoorDiplomacy APT and the risk group orchestrating Operation Tainted Love point out a degree intention directed at supporting [China in its efforts to] form insurance policies and narratives aligned with its geostrategic ambitions, establishing itself as a pivotal and defining power in Africa’s digital evolution,” safety researcher Tom Hegel mentioned.
It additionally comes days after Cisco Talos revealed that telecommunication service suppliers within the Center East are the goal of a brand new intrusion set dubbed ShroudedSnooper that employs a set of stealthy backdoors referred to as HTTPSnoop and PipeSnoop.