Again in Could 2023, I wrote the blogpost You might not care the place you obtain software program from, however malware does as a name to arms, warning in regards to the dangers of operating software program downloaded from so-called “trusted sources” of pirated software program. After all, these recordsdata have been something however reliable and contained malware, reminiscent of ransomware or infostealers, particularly focused at that demographic. My hope was that by educating the general public in regards to the dangers concerned, individuals would study methods to keep away from such harmful apps and search safer options.
Within the yr or so since that blogpost, issues haven’t gotten a lot better: From studying the ESET Risk Report for the first half of 2024, we’ve seen a marked improve within the variety of info stealers being detected. And this time, they aren’t simply embedded in pirated Home windows video games, cracks, and dishonest instruments, but in addition impersonating generative AI instruments. Nor are they restricted to Home windows, both. The GoldDigger household of information-stealing malware runs on Android OS, and the long-running Ebury malware marketing campaign has been energetic in stealing bank cards, cryptocurrencies, and SSH credentials for over a decade on UNIX-like working techniques.
Taking a look at infostealer detections over a two-year interval, from August 2022 to August 2024, exhibits they remained energetic all through this era, though there have been noticeable drops in exercise round December and January of every yr.
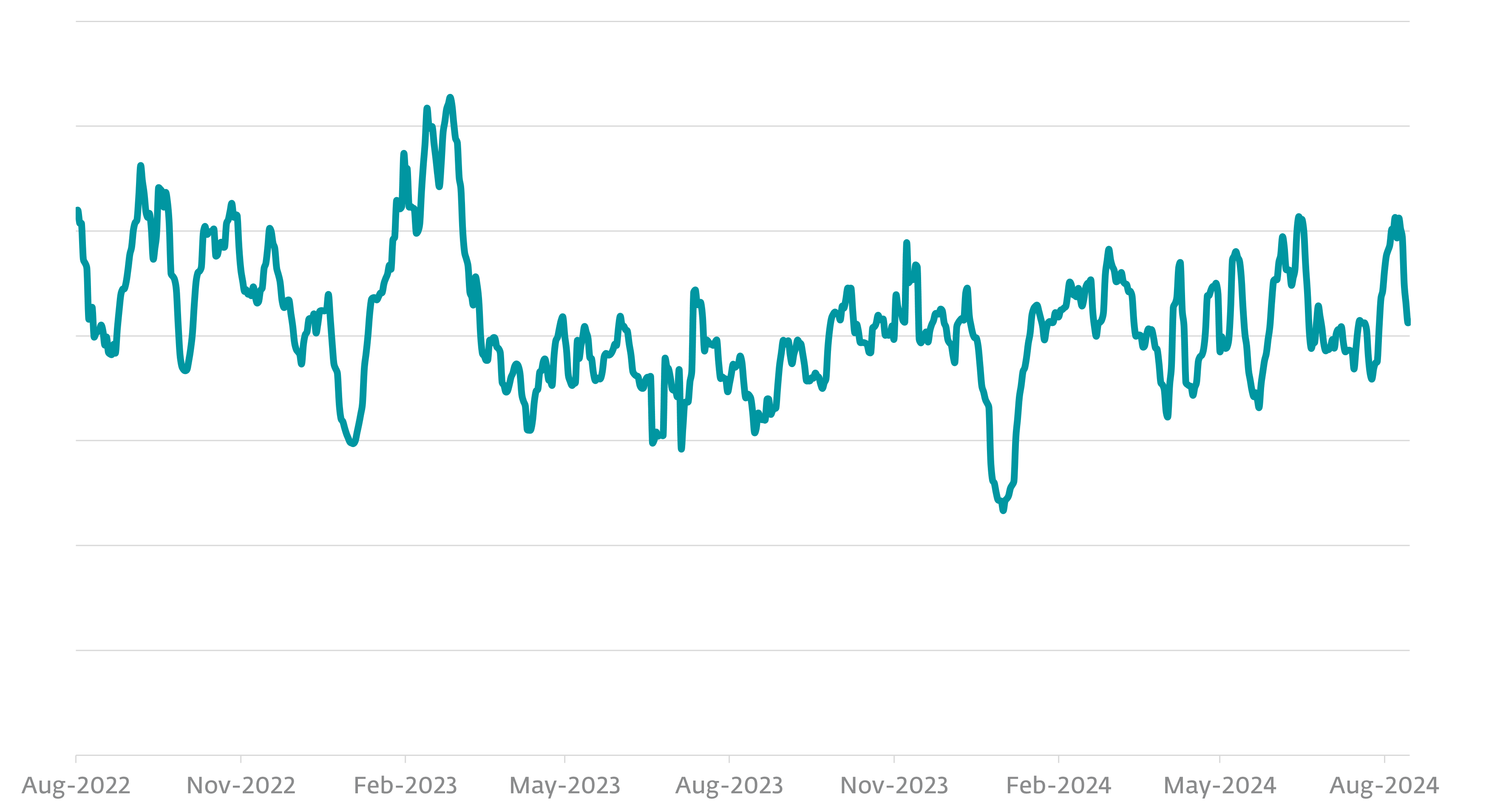
We’re unsure of the precise motive for this, however speculate that it could be resulting from decreased laptop utilization by the victims or their attackers taking a break for the vacations, which has develop into widespread as particular person felony hackers have morphed into organized felony enterprises, resembling one thing like companies.
Whereas ESET acknowledges many households of infostealers, the highest ten account for simply over 56% of these detected by ESET, with Agent Tesla on the prime, with 16.2%.
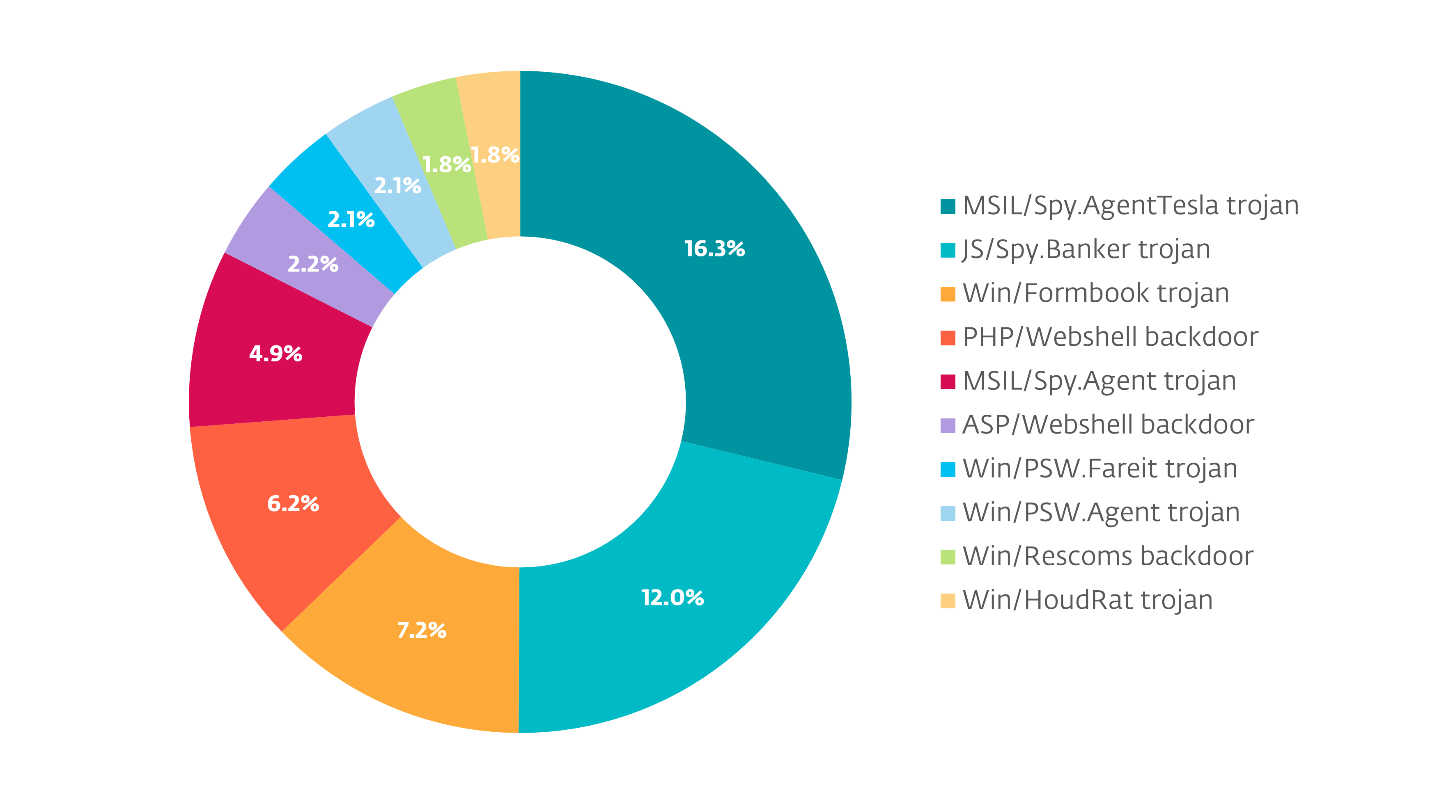
One factor to remember is that whereas most of those detections are for Home windows-based malware, there are info stealers which can be net primarily based as properly. Though they’d decrease encounter charges, it’s doable that they have been capable of efficiently steal info from individuals not operating ESET software program, so their impression could also be higher.
Protecting in thoughts that these statistics are derived from ESET telemetry knowledge, it’s doable that different safety firms’ knowledge could present completely different outcomes. This isn’t resulting from anybody being higher than one other however the results of elements reminiscent of classifying threats in a different way, having completely different buyer bases with very completely different danger profiles, utilization underneath completely different circumstances, and others.
All of which implies we will all report completely different encounter charges for varied sorts of malware, reminiscent of info stealers.
One of many issues I used to be interested in was whether or not ESET’s knowledge was much like that of different safety firms. As one instance, in their malware tendencies report for the second quarter of 2024, sandbox vendor ANY.RUN famous that info stealers dropped from first place to fourth place from the previous quarter. Now, this doesn’t imply that there’s any distinction in knowledge high quality between ESET and ANY.RUN. There’s a broad ecosystem of safety instruments on the market, and with every firm’s instruments utilized in fairly numerous methods, some of these variances in reporting are to be anticipated.
Info stealing for enjoyable however principally revenue
ESET classifies info stealers underneath their very own separate risk class of Infostealer. Initially, they have been categorized underneath extra common names reminiscent of Agent or Trojan till the amount of packages participating in information-stealing exercise elevated to the purpose that it made sense to cluster them underneath their very own nom de plume. Different safety software program builders could classify them extra broadly as distant entry trojans or spyware and adware, which is completely acceptable, too. The purpose of detecting malware is to forestall it at the beginning. The naming of these threats and the taxonomies underneath which they’re categorised is usually unimportant exterior of analysis actions or advertising and marketing actions in response to a mass malware outbreak, reminiscent of WannaCryptor.
So, with all of that in thoughts, what precisely is an info stealer, and what occurs if you run one?
Because the title implies, this sort of malware steals any info it could possibly discover in your laptop that its operator considers of worth. This consists not simply of usernames and passwords for varied web sites accessed through the online browsers put in in your PC, but in addition these for functions. Recreation accounts might be stolen, looted of helpful gadgets, used to make present purchases, or resold of their entirety. Streaming media might be resold, as can e mail and social media accounts. As an “added bonus”, the latter can use your account to entice on-line mates into downloading and operating the knowledge stealer, turning into new victims to it, and having its puppeteers unfold it from these accounts as properly, advert infinitum.
It’s not simply usernames and passwords that get stolen, both. Wallets for cryptocurrencies might be particularly profitable, as can account session tokens. For that matter, the knowledge stealer could even take a screenshot of the desktop on the time it was run in order that its operator can promote the screenshot and e mail tackle to different criminals for sending rip-off extortion emails later.
In case you’re questioning what a session token is, some web sites and apps have a “keep in mind this machine” function that permits you to entry the service with out having to log again in or enter your second issue of authentication. That is completed by storing a session token in your machine. One can consider it as being a specialised type of net browser cookie that tells the web site being visited (or service being accessed via an app) that the person has been efficiently authenticated and to permit them in. Criminals search for and goal these, as a result of they permit them to log into an account, bypassing the traditional checks. So far as the service is anxious, it simply appears such as you’re accessing it out of your beforehand approved machine.
The enterprise of data stealing
Info stealers are a kind of malware that’s typically offered as a service, so what precisely it did whereas on a pc goes to range a bit primarily based on what the felony who bought it needed it to search for and steal. Usually, they take away themselves after they’ve completed stealing info with a view to make it more durable to find out what occurred and when. If the sufferer is feeling so overwhelmed by the invasion of their privateness that they delay taking instant motion, it offers the criminals extra time to make use of or fence the knowledge stolen from the pc.
However since info stealers are crimeware-as-a-service, it’s also doable that it was used to put in extra malware on the system with a view to preserve entry to it, simply in case the criminals determine to come back again to the pc sooner or later and see if there’s something new to steal from it.
Restoration from an information-stealing assault
Until the pc’s drive(s) must be preserved as proof, the very first thing to do could be to wipe the pc’s drive and reinstall its working system. That assumes the pc was backed up commonly, so erasing its drive(s) and shedding all the knowledge saved on it (them?) isn’t a giant deal, since it’s already backed up elsewhere. If that’s not the case, and there’s helpful, essential knowledge saved on the pc, it could make sense to take away its drive(s), substitute it with a clean one, and carry out a clear set up of the working system to that. Getting some type of exterior case to place the drive in later to repeat the non-backed up knowledge off of will probably be essential as properly.
After wiping the pc, putting in Home windows, putting in safety software program, and getting all of that up to date, one can then begin accessing the web utilizing the pc to alter the passwords for the entire on-line accounts that have been ever accessed from it.
Every password must be modified to one thing that’s not solely advanced but in addition completely different for every service. Merely changing Summer2024 with Autumn2024, or P@ssW0rd123 with P@ssW0rd1234 is one thing an attacker may simply guess after reviewing your entire stolen passwords. That approach, if one is misplaced (or guessed), the attacker gained’t be capable to make guesses about what the opposite passwords is likely to be. A few of ESET’s subscriptions include a password supervisor, or your net browser could have one which’s constructed into it. ESET additionally presents a free instrument for producing advanced passwords.
Enabling two-factor authentication (generally known as multi-factor authentication) for the entire accounts that help it would make it exponentially more durable for attackers to compromise sooner or later, even when they know the passwords to them.
When altering passwords, you will need to make them distinctive or completely different from any beforehand used passwords: if the brand new passwords are related sufficient to the outdated passwords, a felony who has all of the outdated passwords will very doubtless be capable to make all kinds of educated guesses about what the brand new passwords is likely to be for the assorted providers. So, be sure to’re not biking via similar-sounding or earlier passwords.
As talked about earlier, it’s not simply passwords it’s a must to change, however session tokens as properly. These are focused by information-stealing malware as a result of they permit criminals to impersonate you by hijacking one in all your beforehand approved periods. Some web sites and apps have the power to indicate you different energetic periods or units on which you accessed them, but in addition to sign off or disconnect these different energetic periods. Do this as properly.
On the danger of sounding considerably repetitive, you will need to do that for each single on-line service. Even ones which can be now not commonly used. That is extraordinarily essential for any monetary web sites, on-line shops, social media, and e mail accounts, since these are among the many most dear to criminals. If there have been any reused passwords and even related themes between them, the criminals who stole the credentials are going to strive spraying them towards all of the widespread shops, banks, and providers.
Two of the underlooked actions when recovering from an information-stealing assault are to (1) file a report with the police; and (2) notify your monetary establishments. Making regulation enforcement conscious {that a} crime has occurred could also be useful in recovering stolen accounts. Within the case of monetary establishments, having a police report back to share with them can improve the probabilities of getting again stolen funds. Even in case you are not in america, submitting a report with the Web Crime Compliant Middle (IC3) may help regulation enforcement companies establish and observe information-stealing criminals.
Defensive methods
Coping with the aftermath of an info stealer assault is an extended and painful course of that may drag on for days, weeks, and even months. Whereas we’ve offered the fundamentals wanted to begin the method of recovering from such assaults, info stealers are neither the only real nor essentially the most extensively occurring methodology of getting one’s accounts stolen. The locks and keys for our on-line identities are usernames (which are sometimes e mail addresses) and passwords, and knowledge breaches involving these have develop into more and more widespread.
Having establish theft safety may help mitigate among the worst features of this sort of violation, however like having an insurance coverage coverage (or backups of their laptop’s knowledge), it’s one thing lots of people don’t think about till after one thing dangerous occurs to them.
One wonderful supply of discovering out whether or not your e mail tackle has been concerned in an information breach is Troy Hunt’s Have I Been Pwned (HIBP) web site, which always receives up to date details about knowledge breaches which have occurred all world wide and can notify you in case your e mail tackle has been present in any of them. Whereas that doesn’t essentially imply your e mail account itself is in any hazard, it may imply the account could possibly be on the service from which it was leaked. The HIBP service is free for people.
Knowledge breaches might be troublesome to keep away from, since they’re the results of securing points involving third events. Info stealers, alternatively, are usually the results of participating in dangerous habits. Listed here are some steps you may take to scale back the impression and get better extra rapidly from some of these assaults:
- Use lengthy and completely different passwords for every web site and utility. A password supervisor can significantly ease this advanced course of for you.
- Allow two-factor authentication for all providers that permit it. {Hardware} tokens or smartphone apps are safer than e mail or SMS notification, as an attacker could have entry to your e mail or smartphone.
- Some providers allow you to see all of the units logged into your account. Periodically overview these and disable ones that you don’t acknowledge or haven’t been energetic for some time.
- Use an information breach monitoring or an id theft safety service to inform you of compromised accounts.
- Do not use pirated software program, cracks, keygens or related instruments irrespective of how reliable you think about them. It’s trivial to make these seem protected and trusted when criminals have stolen the accounts score them.
- Preserve your working system and functions updated with the most recent totally patched variations.
- Use the most recent model of safety software program from trusted, established distributors.
- Preserve updated on the most recent safety tendencies, points and information out of your favourite info safety blogs.
Following these can cut back the probabilities of turning into a sufferer, or enable you to get better extra rapidly within the occasion that you’ve got develop into one.


