
Microsoft will quickly begin rolling out Conditional Entry insurance policies requiring multifactor authentication (MFA) from directors when signing into Microsoft admin portals reminiscent of Microsoft Entra, Microsoft 365, Trade, and Azure.
The corporate may even roll out insurance policies that may require MFA for per-user MFA customers for all cloud apps and one that may require MFA for high-risk sign-ins (the latter solely accessible to Microsoft Entra ID Premium Plan 2 prospects).
These Microsoft-managed insurance policies (created by Microsoft on prospects’ tenants) will regularly be added in report-only mode to eligible Microsoft Entra tenants beginning subsequent week. After the rollout reaches their tenant, admins may have 90 days to overview them and select in the event that they wish to allow them or not.
Redmond will robotically allow these Conditional Entry insurance policies solely on tenants the place they weren’t toggled off inside 90 days after the rollout.
“Pay numerous consideration to the primary coverage. It is our sturdy suggestion—and a coverage we’ll deploy your behalf—that multifactor authentication shield all consumer entry to admin portals reminiscent of https://portal.azure.com, Microsoft 365 admin heart, and Trade admin heart,” stated Microsoft Vice President for Identification Safety Alex Weinert.
“Please word that when you can decide out of those insurance policies, groups at Microsoft will more and more require multifactor authentication for particular interactions, as they already do for sure Azure subscription administration eventualities, Accomplice Heart, and Microsoft Intune machine enrollment.”
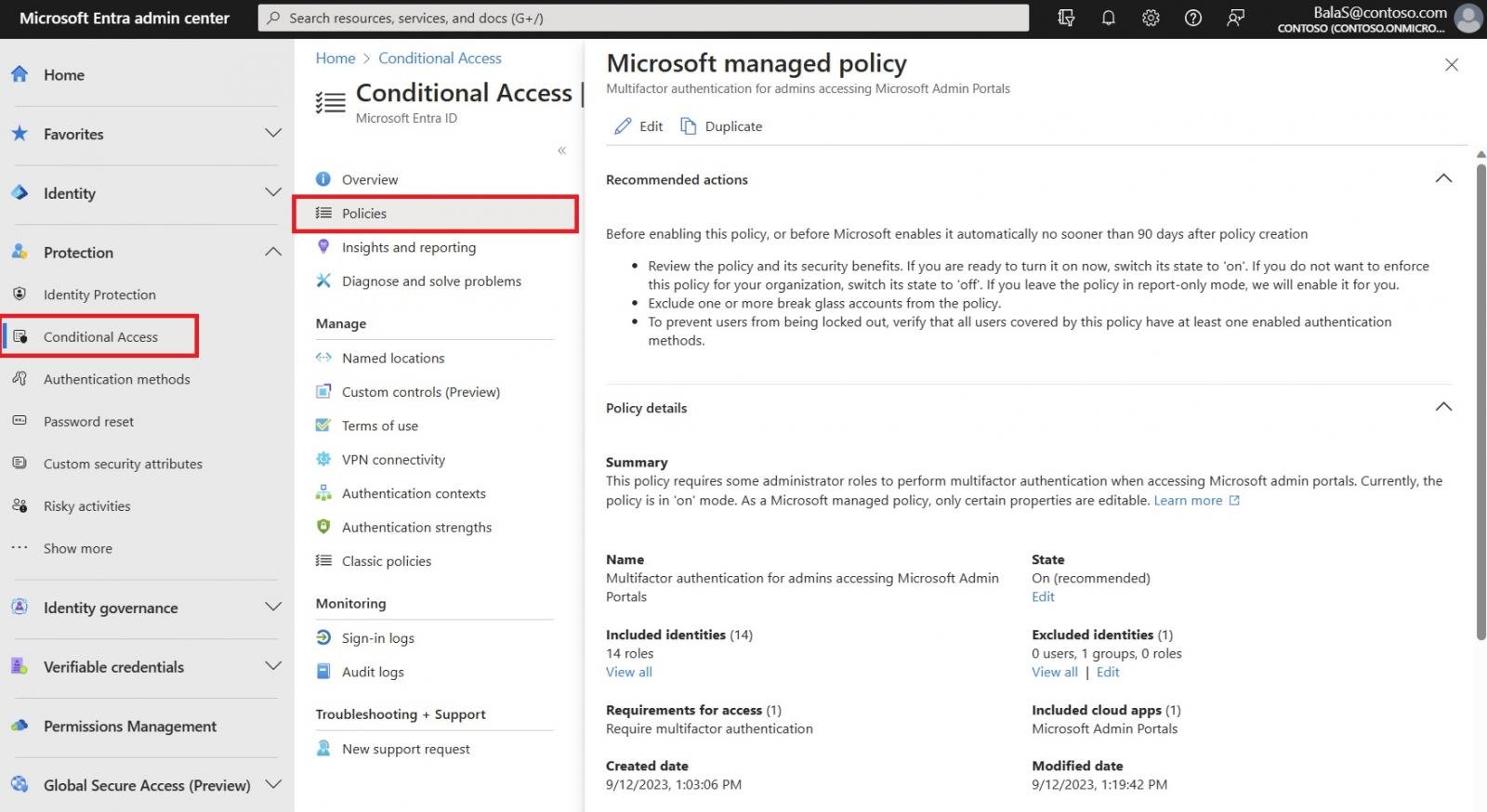
As soon as added, directors with at the very least the Conditional Entry Administrator position can discover these insurance policies within the Microsoft Entra admin heart below Safety > Conditional Entry > Insurance policies.
They’ll additionally modify the state (On, Off, or Report-only) for all Microsoft-managed insurance policies, in addition to excluded identities (Customers, Teams, and Roles) inside the coverage.
Redmond advises organizations to exclude emergency entry or break-glass accounts from these insurance policies, simply as they’d with different Conditional Entry insurance policies.
Microsoft additionally offers the choice to switch these insurance policies additional by cloning them utilizing the Duplicate button within the coverage record view and tailoring them like another Conditional Entry coverage, beginning with Microsoft-recommended defaults.
“Our objective is one hundred pc multifactor authentication. On condition that formal research present multifactor authentication reduces the danger of account takeover by over 99 p.c, each consumer who authenticates ought to accomplish that with trendy sturdy authentication,” Weinert stated.
“Our eventual objective is to mix machine learning-based coverage insights and proposals with automated coverage rollout to strengthen your safety posture in your behalf with the best controls.”


