Cyberattackers are doubling down on their assaults towards regulation companies and company authorized departments, transferring past their historic exercise of hacking and leaking secrets and techniques to focusing on the sector with monetary assaults, equivalent to ransomware and enterprise e-mail compromise (BEC).
On Nov. 24, managed service supplier CTS, which offers IT providers to regulation companies, acknowledged that the agency had suffered a breach, however didn’t give particulars concerning the supply of the assault. The incident has reportedly affected providers to dozens of regulation companies, significantly in the true property sector. The assault follows claims by the LockBit group that it compromised London-based regulation agency Allen & Overy, itemizing the agency among the many victims on its data-leak web site and demanding a ransom. The agency confirmed a breach, however didn’t acknowledge the ransomware assault.
The assaults are solely the most recent to focus on regulation companies and authorized departments. A minimum of one assault group has focused regulation companies particularly, seeding compromised websites with authorized jargon to make the websites rise in search rankings after which ship a ransomware assault chain to guests, says Keegan Keplinger, a senior safety researcher with managed detection and response agency eSentire.
“When [the targeting] hasn’t been a authorized group, it is usually been the authorized division or a authorized person — a paralegal or the authorized guide — in a corporation,” he says. “We noticed a hospital get hit as soon as, nevertheless it was the authorized person in that hospital that downloaded [the malware].”
GootLoader, which results in Blackcat ransomware, has targeted closely on regulation companies. Supply: eSentire
Hackers have lengthy favored regulation companies as a approach to steal secrets and techniques, absconding with Uber drivers’ private info from regulation agency Genova Burns LLC in January; hijacking knowledge on the contracts and private emails from 200 high-profile celebrities — together with Woman Gaga, Madonna, and Rod Stewart — from New York regulation agency Grubman Shire Meiselas & Sacks in 2020; and allegedly leaking the “Panama Papers” — 11.5 million paperwork on rich tax evaders — from Panama-based regulation agency Mossack Fonseca.
Historically, the attraction for on-line attackers has not been cash, says Ilia Kolochenko, chief architect at software safety agency ImmuniWeb.
“Legislation companies are fairly removed from being enticing victims for cybercriminals,” he says. “Nonetheless, their purchasers — particularly, secrets and techniques of their purchasers — make regulation companies a magnet for all type of cybercriminals.”
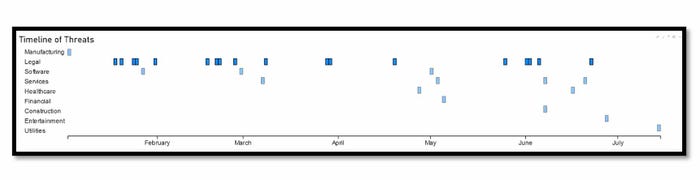
Clickbait Turns to search engine optimisation Poisoning
That has modified, as cybercriminals more and more give attention to regulation companies as a approach to money in with ransomware and BEC assaults. Greater than 1 / 4 of regulation companies (27%) suffered a safety breach in 2022, up from 25% in 2021, based on the American Bar Affiliation’s annual cybersecurity report, which stresses {that a} safety breach just isn’t as extreme a classification as a knowledge breach. The authorized sector is the fourth most focused sector by cybercriminals — behind providers, manufacturing, and monetary companies, based on eSentire’s knowledge.
Essentially the most important risk to regulation companies could also be GootLoader, a browser-based risk that’s delivered by way of SEO (search engine optimisation) poisoning. The group behind GootLoader has seeded malicious content material and malvertising linked to three.5 million search phrases, a excessive proportion of that are authorized phrases. Because of this, a lawyer or paralegal who searches for particular content material might discover the highest search consequence resulting in a GootLoader-infected file. Downloading and opening the file will execute this system, which just about all the time results in BlackCat ransomware, says Joe Stewart, a principal safety researcher at eSentire.
“This [is] what I name a landmine method,” he says. “They’re simply mining the complete Internet with these search key phrases and simply ready for any person within the authorized career, or any person who wants this authorized doc, to simply hit upon it and open it up, say, ‘What’s this? Oh, I’ll click on on this JavaScript. No drawback.'”
Ransomware just isn’t the one fear for regulation companies. Plenty of risk teams are additionally focusing on regulation companies with BEC scams. Legislation companies are the proper victims for such schemes, says Dan Caplin, director of cybersecurity and incident response at S-RM, a cybersecurity consultancy.
“Firstly, they do plenty of enterprise over and in emails, and secondly, regulation companies usually occupy a privileged place in conditions the place cost directions and particulars are exchanged — this, once more, is generally accomplished over e-mail,” he says. “This makes e-mail account takeover, intercepting a thread a couple of respectable cost, and diverting funds to a fraudulent checking account a extremely efficient method.”
Will Get Worse Earlier than It Will get Higher
As a result of regulation companies are typically smaller, usually only one or two individuals, cybersecurity information is usually missing, says ImmuniWeb’s Kolochenko.
“Solo practitioners and small regulation companies are normally poorly protected, having very modest budgets for cybersecurity,” he says. “Massive regulation companies, nevertheless, more and more spend extra on cybersecurity and cyber protection, [but most firms] have related issues as all different industries together with shadow IT, working from dwelling, [and] underprotected third events.”
Sadly, regulation companies are sometimes tasked because the custodian of extraordinarily delicate info, making any breach an issue and making the agency extra prone to pay a ransom. It is little surprise that GootLoader has focused the business, says eSentire’s Keplinger.
“For a wide range of causes, regulation companies are behind the curve a bit bit on safety,” he says. “With ransomware — particularly the double whammy (each stealing and encrypting the info) — authorized companies are an apparent group that will be susceptible to that — particularly, that will care about publishing their knowledge.”


