ESET researchers have just lately noticed a brand new occasion of Operation DreamJob – a marketing campaign that we observe beneath the umbrella of North Korea-aligned Lazarus – by which a number of European corporations lively within the protection business had been focused. A few of these are closely concerned within the unmanned aerial car (UAV) sector, suggesting that the operation could also be linked to North Korea’s present efforts to scale up its drone program. This blogpost discusses the broader geopolitical implications of the marketing campaign, and offers a high-level overview of the toolset utilized by the attackers.
Key factors of this blogpost:
- Lazarus assaults in opposition to corporations creating UAV know-how align with just lately reported developments within the North Korean drone program.
- The suspected major aim of the attackers was doubtless the theft of proprietary info and manufacturing know-how.
- Based mostly on the social-engineering approach used for preliminary entry, trojanizing open-source initiatives from GitHub, and the deployment of ScoringMathTea, we contemplate these assaults to be a brand new wave of the Operation DreamJob marketing campaign.
- The group’s most vital evolution is the introduction of recent libraries designed for DLL proxying and the choice of new open-source initiatives to trojanize for improved evasion.
Profile of Lazarus and its Operation DreamJob
The Lazarus group (often known as HIDDEN COBRA) is an APT group linked to North Korea that has been lively since at the least 2009. It’s answerable for high-profile incidents reminiscent of each the Sony Footage Leisure hack and tens-of-millions-of-dollar cyberheists in 2016, the WannaCryptor (aka WannaCry) outbreak in 2017, and an extended historical past of disruptive assaults in opposition to South Korean public and important infrastructure since at the least 2011. The range, quantity, and eccentricity in implementation of Lazarus campaigns outline this group, in addition to that it performs all three pillars of cybercriminal actions: cyberespionage, cybersabotage, and pursuit of monetary acquire.
Operation DreamJob is a codename for Lazarus campaigns that rely totally on social engineering, particularly utilizing faux job provides for prestigious or high-profile positions (the “dream job” lure). This identify was coined in a 2020 blogpost by ClearSky, and overlaps with campaigns like DeathNote or Operation North Star. Targets are predominantly within the aerospace and protection sectors, adopted by engineering and know-how corporations and the media and leisure sector. In these campaigns, the attackers often deploy trojanized open-source plugins for software program like Notepad++ and WinMerge that function droppers and loaders, and payloads like ImprudentCook, ScoringMathTea, BlindingCan, miniBlindingCan, LightlessCan for Home windows, and SimplexTea for Linux. The first aim is cyberespionage, specializing in stealing delicate information, mental property, and proprietary info, and the secondary aim is monetary acquire.
Overview
Beginning in late March 2025, we noticed in ESET telemetry cyberattacks harking back to Operation DreamJob campaigns. The in-the-wild assaults successively focused three European corporations lively within the protection sector. Though their actions are considerably numerous, these entities may be described as:
- a steel engineering firm (Southeastern Europe),
- a producer of plane elements (Central Europe), and
- a protection firm (Central Europe).
All instances concerned droppers which have the fascinating inside DLL identify, DroneEXEHijackingLoader.dll, which led us down the drone phase rabbit gap. Additionally, preliminary entry was doubtless achieved through social engineering – an Operation DreamJob specialty. The dominant theme is a profitable however fake job supply with a aspect of malware: the goal receives a decoy doc with a job description and a trojanized PDF reader to open it.
The principle payload deployed to the targets was ScoringMathTea, a RAT that provides the attackers full management over the compromised machine. Its first look dates to late 2022, when its dropper was uploaded to VirusTotal. Quickly after, it was seen within the wild, and since then in a number of assaults attributed to Lazarus’ Operation DreamJob campaigns, which makes it the attacker’s payload of selection for already three years. It makes use of compromised servers for C&C communication, with the server half often saved beneath the WordPress folder containing design templates or plugins.
In abstract, we attribute this exercise with a excessive stage of confidence to Lazarus, notably to its campaigns associated to Operation DreamJob, primarily based on the next:
- Preliminary entry was obtained by social engineering, convincing the goal to execute malware disguised as a job description, so as to reach a hiring course of.
- Trojanizing open-source initiatives after which crafting their exports to suit the DLL side-loading appears to be an method particular to Operation DreamJob.
- The flagship payload for later levels, ScoringMathTea, was utilized in a number of related assaults previously.
- The focused sectors, situated in Europe, align with the targets of the earlier cases of Operation DreamJob (aerospace, protection, engineering).
Geopolitical context
The three focused organizations manufacture various kinds of army tools (or elements thereof), a lot of that are at present deployed in Ukraine because of European international locations’ army help. On the time of Operation DreamJob’s noticed exercise, North Korean troopers had been deployed in Russia, reportedly to assist Moscow repel Ukraine’s offensive within the Kursk oblast. It’s thus doable that Operation DreamJob was desirous about accumulating delicate info on some Western-made weapons techniques at present employed within the Russia-Ukraine struggle.
Extra usually, these entities are concerned within the manufacturing of varieties of materiel that North Korea additionally manufactures domestically, and for which it is perhaps hoping to good its personal designs and processes. In any case, there isn’t any indication that the focused corporations provide army tools to the South Korean armed forces – which may have been one other aspect explaining Operation DreamJob’s curiosity in these corporations. Apparently, nevertheless, at the least two of those organizations are clearly concerned within the improvement of UAV know-how, with one manufacturing essential drone elements and the opposite reportedly engaged within the design of UAV-related software program.
The curiosity in UAV-related know-how is notable, because it echoes latest media studies indicating that Pyongyang is investing closely in home drone manufacturing capabilities. Though this endeavor may be traced again to greater than a decade in the past, many observers posit that North Korea’s latest expertise of contemporary warfare within the Russia-Ukraine struggle has solely strengthened Pyongyang’s decision with regard to its drone program. The North Korean regime is now reportedly receiving help from Russia to provide its personal model of the Iranian-made Shahed suicide drone and can also be apparently engaged on low-cost assault UAVs that could possibly be exported to African or Center Japanese international locations.
Assessing the “drone connection”
If one factor is evident, it’s that North Korea has relied closely on reverse engineering and mental property theft to develop its home UAV capabilities. As latest open-source studies illustrate, North Korea’s present flagship reconnaissance drone, the Saetbyol‑4, appears like a carbon copy of the Northrop Grumman RQ‑4 International Hawk, whereas its multipurpose fight drone, the Saetbyol‑9, bears a hanging resemblance to Common Atomics’ MQ‑9 Reaper. The truth that each designations replicate the quantity related to their US equal may even be a not-so-subtle nod to that impact. Though these aircrafts’ efficiency might effectively differ from these of their US counterparts, there may be little doubt that the latter served as a robust inspiration for North Korea’s designs.
That is in all probability the place cybercapabilities enter the fray. Whereas different intelligence sources had been doubtless mobilized by Pyongyang to assist copy Western UAVs, there are indications that cyberespionage might have performed a task. In recent times, a number of campaigns affecting the aerospace sector (together with UAV know-how particularly) have been attributed to North Korea-aligned APT teams, with Operation North Star (a marketing campaign presenting some overlap with Operation DreamJob) being certainly one of them. In 2020, ESET researchers documented an identical marketing campaign, which we then named Operation In(ter)ception and later attributed to Lazarus with excessive confidence. As a number of teams associated to Lazarus have been formally linked to North Korean intelligence companies by US authorities and others, these precedents strongly recommend that cyberespionage is probably going one of many instruments leveraged by the regime for reverse engineering Western UAVs – and that teams working beneath the broad Lazarus umbrella are taking an lively half on this effort.
On this context, we consider that it’s doubtless that Operation DreamJob was – at the least partially – aimed toward stealing proprietary info, and manufacturing know-how, concerning UAVs. The Drone point out noticed in one of many droppers considerably reinforces this speculation.
To be clear, we are able to solely hypothesize as to the particular type of info that Operation DreamJob was after. Nevertheless, we’ve discovered proof that one of many focused entities is concerned within the manufacturing of at the least two UAV fashions which might be at present employed in Ukraine, and which North Korea might have encountered on the frontline. This entity can also be concerned within the provide chain of superior single-rotor drones (i.e., unmanned helicopters), a sort of plane that Pyongyang is actively creating however has not proved in a position to militarize to date. These could also be a number of the potential motivations behind Operation DreamJob’s noticed actions. Extra usually, as North Korea is reportedly within the technique of constructing a manufacturing facility for mass-producing UAVs, it may also be searching for privileged information concerning UAV-related industrial processes and manufacturing methods.
Toolset
Experiences from Google’s Mandiant in September 2024 and from Kaspersky in December 2024 describe instruments utilized by Lazarus in its Operation DreamJob in 2024. On this part, we point out the instruments to which the group shifted in Operation DreamJob in 2025. Based mostly on their place within the execution chain, we distinguish two varieties of instruments: early levels that consist of assorted droppers, loaders, and downloaders; and the principle levels that symbolize payloads like RATs and sophisticated downloaders that give the attackers adequate management over the compromised machine.
Moreover the in-the-wild instances seen in ESET telemetry, the exercise of the attackers additionally manifested as VirusTotal submissions occurring on the identical time. A trojanized MuPDF reader, QuanPinLoader, a loader disguised as a Microsoft DirectInput library (dinput.dll), and a variant of ScoringMathTea had been submitted from Italy in April and June 2025; BinMergeLoader was submitted in August 2025 from Spain.
Droppers, loaders, and downloaders
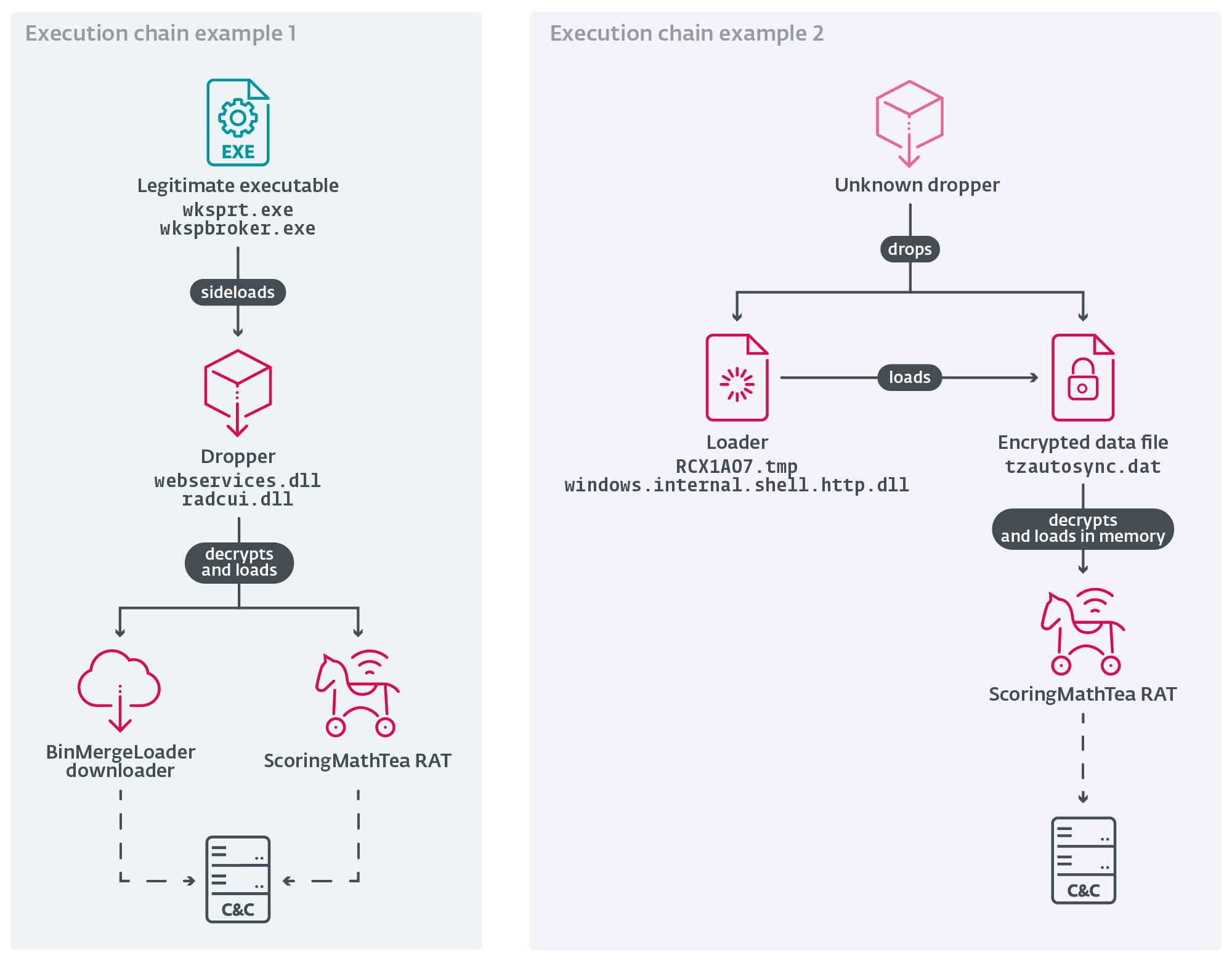
Typically, Lazarus attackers are extremely lively and deploy their backdoors in opposition to a number of targets. This frequent use exposes these instruments and permits them to develop into detected. As a countermeasure, the group’s instruments are preceded within the execution chain by a collection of droppers, loaders, and easy downloaders. Sometimes, the loaders used search for the subsequent stage on the file system or within the registry, decrypt it utilizing AES-128 or ChaCha20, and manually load it in reminiscence through the routines applied within the MemoryModule library; a dropper is principally a loader however accommodates the subsequent stage embedded in its physique. The principle payload, ScoringMathTea in all instances noticed, is rarely current on the disk in unencrypted kind. Instance execution chains are seen in Determine 1. In some instances, the attackers additionally deployed a fancy downloader that we name BinMergeLoader, which is analogous to the MISTPEN malware reported by Google’s Mandiant. BinMergeLoader leverages the Microsoft Graph API and makes use of Microsoft API tokens for authentication.
The attackers determined to include their malicious loading routines into open-source initiatives out there on GitHub. The selection of undertaking varies from one assault to a different. In 2025, we noticed the next malware:
- Trojanized TightVNC Viewer and MuPDF reader that function downloaders.
- A trojanized end-of-life libpcre v8.45 library for Home windows, serving as a loader.
- A loader that has the Mandarin Chinese language image 样 (yàng within the Pinyin transliteration) as an icon within the sources. It additionally accommodates the string SampleIMESimplifiedQuanPin.txt, which means that it’s in all probability primarily based on the open-source undertaking Pattern IME, a TSF-based enter technique editor demo. We name this QuanPinLoader.
- Loaders constructed from the open-source undertaking DirectX Wrappers.
- Downloaders constructed from open-source plugins for WinMerge (DisplayBinaryFiles and HideFirstLetter). We name the 2 trojanized plugins BinMergeLoader.
- Trojanized open-source plugins for Notepad++, particularly a downloader similar to BinMergeLoader (NPPHexEditor v10.0.0 by MacKenzie Cumings) and a dropper of an unknown payload (ComparePlus v1.1.0 by Pavel Nedev). The latter binary accommodates the PDB path E:WorkTroy안정화wksprtcomparePlus-masterNotepad++pluginsComparePlusComparePlus.pdb, which suggests the origin of the undertaking (comparePlus-master) and its meant respectable guardian course of (wksprt). Additionally, 안정화 means steady in Korean, which signifies that the code was doubtless correctly examined and dependable.
One of many droppers (SHA-1: 03D9B8F0FCF9173D2964CE7173D21E681DFA8DA4) has the inner DLL identify DroneEXEHijackingLoader.dll and is disguised as a Home windows Net Providers Runtime library so as to be efficiently side-loaded; see Determine 2. We consider that the substring drone is there to designate each a UAV system and the attacker’s inside marketing campaign identify.
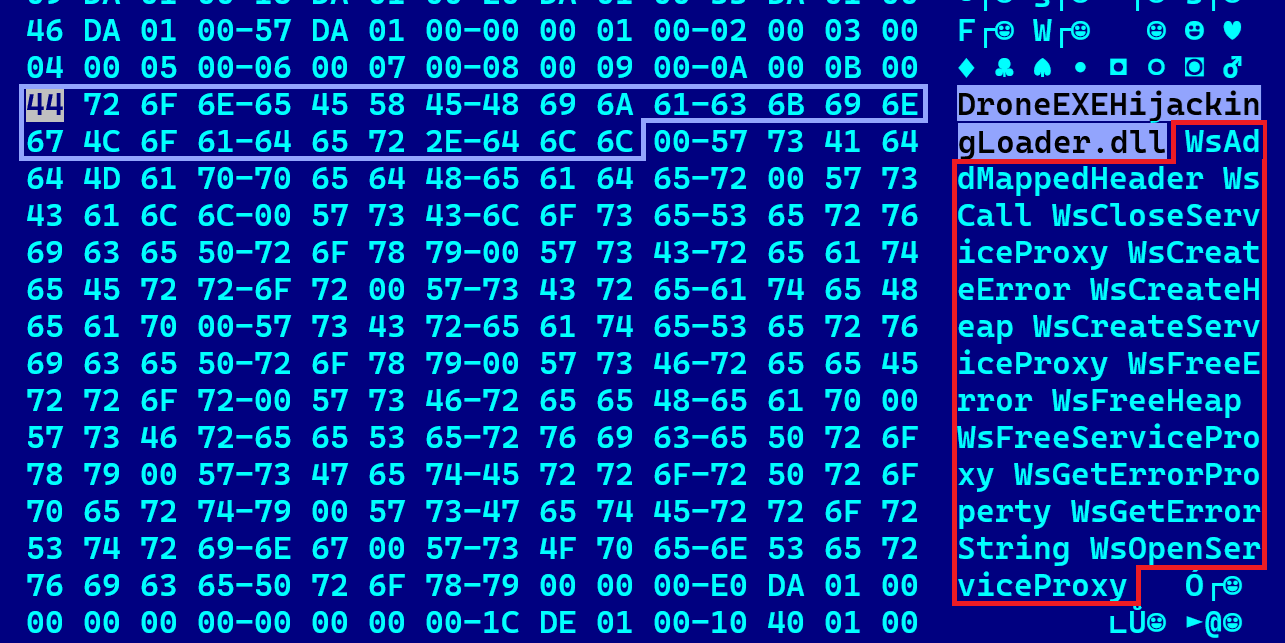
Desk 1 reveals a typical mixture of respectable executable information (EXEs) and malicious dynamic hyperlink libraries (DLLs) delivered to the sufferer’s system (that is analogous to Desk 1 in our blogpost on an assault in opposition to a Spanish aerospace firm in 2023). The DLLs within the third column are both trojanized open-source purposes (see the fourth column for the underlying undertaking) or a standalone malware binary with out such benign context, with a respectable EXE side-loading it. The placement folder (the primary column) is uncommon for such respectable purposes. Malicious DLLs use the DLL proxying approach, so as to not break the execution. Due to this fact, when a DLL can also be a trojanized undertaking, it accommodates two heterogeneous varieties of exports: first the set of features required for DLL proxying, and second the set of features exported from the open-source undertaking.
Desk 1. Abstract of binaries concerned within the assault
| Location folder | Respectable guardian course of | Malicious side-loaded DLL | Trojanized undertaking (payload) |
| N/A | wksprt.exe* | webservices | ComparePlus v1.1.0 (N/A) |
%ALLUSERSPROFILEpercentEMC %ALLUSERSPROFILEpercentAdobe | wksprt.exe | webservices | Standalone (ScoringMathTea) |
| %ALLUSERSPROFILE% | wkspbroker.exe | radcui.dll | DirectX wrappers d3d8.dll/ddraw.dll (ScoringMathTea) |
| %APPDATApercentMicrosoftRemoteApp | wkspbroker.exe | radcui.dll | Standalone (BinMergeLoader) |
* Denotes a VirusTotal submission and its doubtless guardian course of. The payload is unknown, since an extended command-line argument is required for its decryption from the trojanized undertaking.
ScoringMathTea
ScoringMathTea is a fancy RAT that helps round 40 instructions. Its identify is a mix of the basis ScoringMath, taken from a C&C area utilized by an early variant (www.scoringmnmathleague[.]org), and the suffix -Tea, which is ESET Analysis’s designation for a North Korea-aligned payload. It was first publicly documented by Kaspersky in April 2023 and later by Microsoft in October 2023 beneath the identify ForestTiger, which follows the inner DLL identify or the PDB info present in some samples.
Its first look may be traced again to VirusTotal submissions from Portugal and Germany in October 2022, the place its dropper posed as an Airbus-themed job supply lure. The applied performance is the standard required by Lazarus: manipulation of information and processes, exchanging the configuration, accumulating the sufferer’s system information, opening a TCP connection, and executing native instructions or new payloads downloaded from the C&C server. The present model doesn’t present any dramatic modifications in its characteristic set or its command parsing. So the payload might be receiving steady, quite minor enhancements and bug fixes.
Concerning ESET telemetry, ScoringMathTea was seen in assaults in opposition to an Indian know-how firm in January 2023, a Polish protection firm in March 2023, a British industrial automation firm in October 2023, and an Italian aerospace firm in September 2025. Evidently it is without doubt one of the flagship payloads for Operation DreamJob campaigns, despite the fact that Lazarus has extra refined payloads like LightlessCan at its disposal.
Conclusion
For practically three years, Lazarus has maintained a constant modus operandi, deploying its most well-liked important payload, ScoringMathTea, and utilizing related strategies to trojanize open-source purposes. This predictable, but efficient, technique delivers adequate polymorphism to evade safety detection, even whether it is inadequate to masks the group’s identification and obscure the attribution course of. Additionally, even with widespread media protection of Operation DreamJob and its use of social engineering, the extent of worker consciousness in delicate sectors – know-how, engineering, and protection – is inadequate to deal with the potential dangers of a suspicious hiring course of.
Though different hypotheses are conceivable, there are good causes to assume that this Operation DreamJob marketing campaign was in no small half meant to gather delicate info on UAV-related know-how. Contemplating North Korea’s present efforts at scaling up its drone business and arsenal, it appears doubtless that different organizations lively on this sector will whet the urge for food of North Korea-aligned risk actors within the close to future.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis provides non-public APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete listing of indicators of compromise and samples may be present in our GitHub repository.
Recordsdata
SHA-1 Filename Detection Description 28978E987BC59E75CA22 TSMSISrv.dll Win64/NukeSped.TL QuanPinLoader. 5E5BBA521F0034D342CC libmupdf.dll Win64/NukeSped.TE A loader disguised as a MuPDF rendering library v3.3.3. B12EEB595FEEC2CFBF9A radcui.dll Win64/NukeSped.TO A dropper disguised as a RemoteApp and Desktop Connection UI Part library. 26AA2643B07C48CB6943 HideFirstLetter Win64/NukeSped.TO BinMergeLoader. 0CB73D70FD4132A4FF54 libpcre.dll Win64/NukeSped.TP A loader that may be a trojanized libpcre library. 03D9B8F0FCF9173D2964 webservices.dll Win64/NukeSped.RN A dropper disguised as a Microsoft Net Providers Runtime library. 71D0DDB7C6CAC4BA2BDE N/A Win64/NukeSped.RN ScoringMathTea. 87B2DF764455164C6982 webservices.dll Win64/NukeSped.RW A dropper disguised as a Microsoft Net Providers Runtime library. E670C4275EC24D403E0D N/A Win64/NukeSped.RW ScoringMathTea. B6D8D8F5E0864F5DA788 radcui.dll Win64/NukeSped.TF A loader disguised as a RemoteApp and Desktop Connection UI Part library. 5B85DD485FD516AA1F44 RCX1A07.tmp Win64/NukeSped.TH A loader of an encrypted ScoringMathTea. B68C49841DC48E367203 TSMSISrv.dll Win64/NukeSped.TL QuanPinLoader. AC16B1BAEDE349E48243 cache.dat Win64/NukeSped.QK A decrypted ScoringMathTea RAT. 2AA341B03FAC3054C576 msadomr.dll Win64/NukeSped.SP A loader disguised as a Microsoft DirectInput library. CB7834BE7DE07F893520 ComparePlus.dll Win64/NukeSped.SJ A trojanized Notepad++ plugin disguised as a Microsoft Net Providers Runtime library. A dropper from VirusTotal. 262B4ED6AC6A977135DE tzautosync.dat Win64/NukeSped.RW A decrypted ScoringMathTea, saved encrypted on the disk. 086816466D9D9C12FCAD N/A Win64/NukeSped.RN ScoringMathTea. 2A2B20FDDD65BA28E7C5 cache.dat Win64/NukeSped.SN A downloader just like BinMergeLoader constructed as a trojanized NPPHexEditor plugin.
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 23.111.133[.]162 | coralsunmarine[.]com | HIVELOCITY, Inc. | 2024-06-06 | ScoringMathTea C&C server: https://coralsunmarine[.]com/wp-content/themes/flatsome/inc/features/function-hand.php |
| 104.21.80[.]1 | kazitradebd[.]com | Cloudflare, Inc. | 2025-01-11 | ScoringMathTea C&C server: https://kazitradebd[.]com/wp-content/themes/hello-elementor/contains/customizer/customizer-hand.php |
| 70.32.24[.]131 | oldlinewoodwork | A2 Internet hosting, Inc. | 2024-06-14 | ScoringMathTea C&C server: https://oldlinewoodwork[.]com/wp-content/themes/zubin/inc/index.php |
| 185.148.129[.]24 | www.mnmathleague | A2 Internet hosting, Inc. | 2024-06-15 | ScoringMathTea C&C server: https://www.mnmathleague[.]org/ckeditor/adapters/index.php |
| 66.29.144[.]75 | pierregems[.]com | Namecheap, Inc. | 2024-08-11 | ScoringMathTea C&C server: https://pierregems[.]com/wp-content/themes/woodmart/inc/configs/js-hand.php |
| 108.181.92[.]71 | www.scgestor.com[.]br | Psychz Networks | 2024-07-15 | ScoringMathTea C&C server: https://www.scgestor.com[.]br/wp-content/themes/vantage/inc/template-headers.php |
| 104.247.162[.]67 | galaterrace[.]com | GNET Web Telekomunikasyon A.S. | 2024-06-27 | ScoringMathTea C&C server: https://galaterrace[.]com/wp-content/themes/hello-elementor/contains/features.php |
| 193.39.187[.]165 | ecudecode[.]mx | Heymman Servers Company | 2025-05-14 | ScoringMathTea C&C server: https://ecudecode[.]mx/redsocial/wp-content/themes/buddyx/inc/Customizer/usercomp.php |
| 172.67.193[.]139 | www.anvil.org[.]ph | Cloudflare, Inc. | 2025-02-22 | ScoringMathTea C&C server: https://www.anvil.org[.]ph/listing/pictures/index.php |
| 77.55.252[.]111 | partnerls[.]pl | Nazwa.pl Sp.z.o.o. | 2025-06-02 | ScoringMathTea C&C server: https://partnerls.pl/wp-content/themes/public/index.php |
| 45.148.29[.]122 | trainingpharmacist | Webdock.io ApS | 2024-06-13 | ScoringMathTea C&C server: https://trainingpharmacist.co.uk/bootstrap/bootstrap.php |
| 75.102.23[.]3 | mediostresbarbas | DEFT.COM | 2024-06-05 | ScoringMathTea C&C server: https://mediostresbarbas.com[.]ar/php_scrip/banahosting/index.php |
| 152.42.239[.]211 | www.bandarpowder | DigitalOcean, LLC | 2024-09-19 | ScoringMathTea C&C server: https://www.bandarpowder[.]com/public/property/buttons/bootstrap.php |
| 95.217.119[.]214 | spaincaramoon | Hetzner On-line GmbH | 2025-04-30 | ScoringMathTea C&C server: https://spaincaramoon[.]com/realestate/wp-content/plugins/gravityforms/ahead.php |
MITRE ATT&CK methods
This desk was constructed utilizing model 17 of the MITRE ATT&CK framework.
Tactic | ID | Title | Description |
Useful resource Growth | Compromise Infrastructure: Server | ScoringMathTea makes use of compromised servers for C&C. | |
Develop Capabilities: Malware | All levels within the assault had been doubtless developed by the attackers. | ||
Execution | Native API | Home windows APIs are important for ScoringMathTea to perform and are resolved dynamically at runtime. | |
Shared Modules | ScoringMathTea is ready to load a downloaded DLL with the exports fun00 or exportfun00. | ||
Consumer Execution: Malicious File | Lazarus attackers relied on the execution of trojanized PDF readers. | ||
Persistence | Hijack Execution Circulation: DLL Aspect-Loading | Trojanized droppers (webservices.dll, radcui.dll) use respectable packages (wksprt.exe, wkspbroker.exe) for his or her loading. | |
Protection Evasion | Entry Token Manipulation: Create Course of with Token | ScoringMathTea can create a brand new course of within the safety context of the consumer represented by a specified token. | |
Deobfuscate/Decode Recordsdata or Info | The principle payload, ScoringMathTea, is at all times encrypted on the file system. | ||
Obfuscated Recordsdata or Info: Dynamic API Decision | ScoringMathTea resolves Home windows APIs dynamically. | ||
Obfuscated Recordsdata or Info: Embedded Payloads | The droppers of all malicious chains include an embedded information array with a further stage. | ||
Reflective Code Loading | The droppers and loaders use reflective DLL injection. | ||
Course of Injection | ScoringMathTea and BinMergeLoader can reflectively load a DLL within the course of specified by the PID. | ||
Discovery | File and Listing Discovery | ScoringMathTea can find a file by its identify. | |
Course of Discovery | ScoringMathTea can listing all operating processes. | ||
System Info Discovery | ScoringMathTea can mimic the ver command. | ||
Command and Management | Software Layer Protocol: Net Protocols | ScoringMathTea and BinMergeLoader use HTTP and HTTPS for C&C. | |
Encrypted Channel: Symmetric Cryptography | ScoringMathTea encrypts C&C visitors utilizing the IDEA algorithm and BinMergeLoader utilizing the AES algorithm. | ||
Knowledge Encoding: Commonplace Encoding | ScoringMathTea provides a base64-encoding layer to its encrypted C&C visitors. | ||
Exfiltration | Exfiltration Over C2 Channel | ScoringMathTea can exfiltrate information to its C&C server. |