
The North Korean Lazarus hacking group repeatedly compromised a software program vendor utilizing flaws in weak software program regardless of a number of patches and warnings being made out there by the developer.
The truth that Lazarus breached the identical sufferer a number of occasions signifies that the hackers aimed to steal supply code or try a provide chain assault.
“This recurring breach instructed a persistent and decided risk actor with the possible goal of stealing useful supply code or tampering with the software program provide chain, and so they continued to take advantage of vulnerabilities within the firm’s software program whereas concentrating on different software program makers,” explains Kaspersky.
The assault was found by Kaspersky in July 2023, which noticed Lazarus using a various an infection chain and post-compromise toolset.
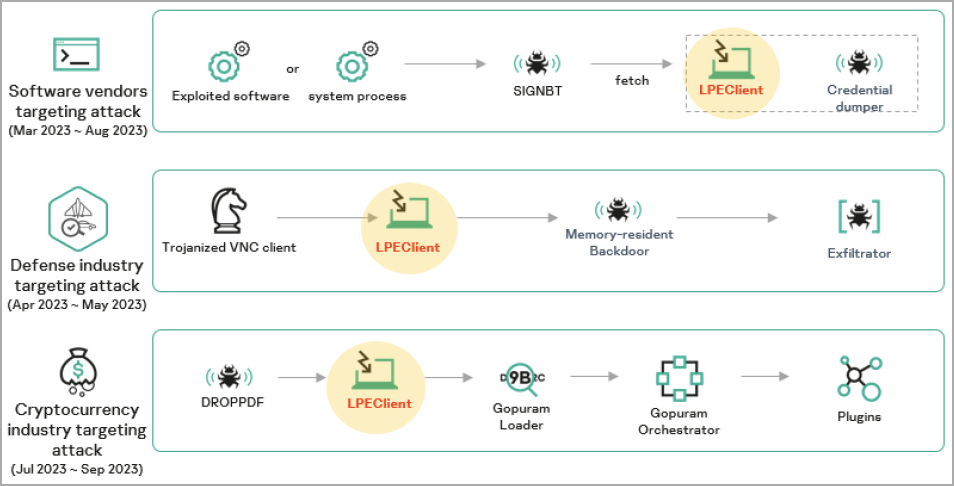
Kaspersky locations this assault throughout the broader scope of a marketing campaign through which Lazarus focused numerous software program distributors between March 2023 and August 2023.
The SIGNBT and LPEClient malware
The report mentions that Lazarus focused reputable safety software program used for the encryption of net communications. Nevertheless, the precise exploitation methodology the hackers adopted stays unknown.
The exploitation led to the deployment of the SIGNBT malware together with shellcode used for injecting the payload into reminiscence for stealthy execution.
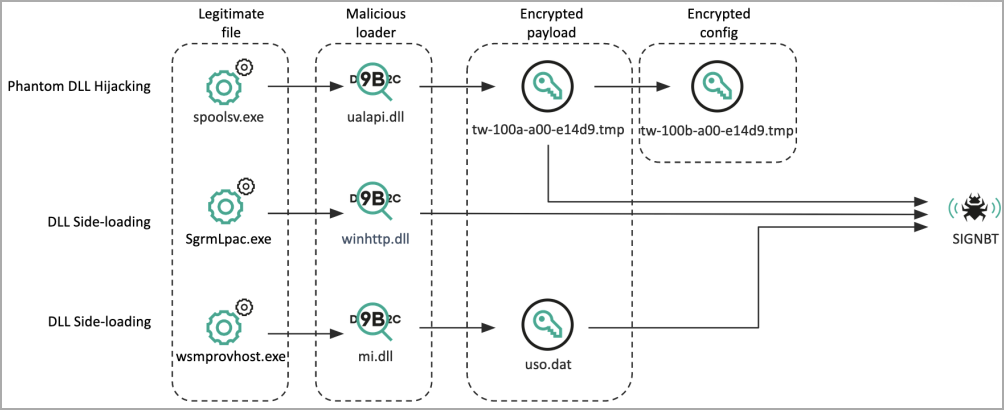
Persistence is established by including a malicious DLL (‘ualapi.dll’) onto Startup to be executed by ‘spoolsv.exe,’ or performing Home windows Registry modifications.
The malicious DLL file performs sufferer ID verification checks earlier than it decrypts and masses the SIGNBT payload from a neighborhood filesystem path to make sure the an infection proceeds onto the meant targets.
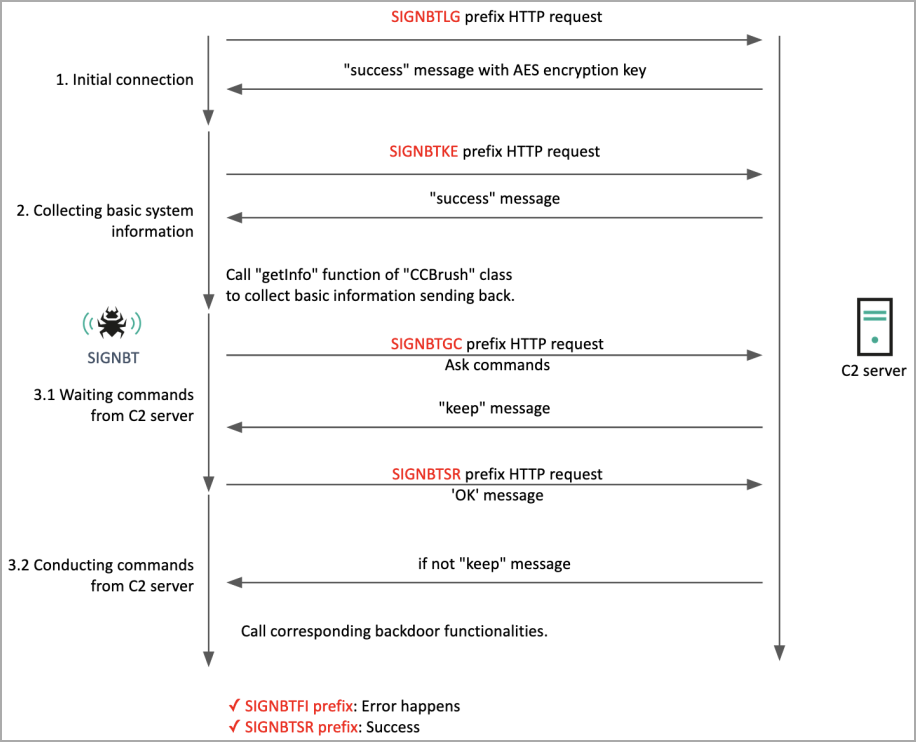
SIGNBT will get its title from the distinct strings it makes use of for command and management (C2) communications, sending details about the compromised system and receiving instructions for execution.
The instructions supported by SIGNBT are:
- CCBrush: Handles functionalities like getting details about the system, testing connectivity, and configuring settings.
- CCList: Manages processes, together with acquiring a listing of operating processes, killing processes, operating information, and DLL manipulations.
- CCComboBox: Works with the file system, equivalent to acquiring lists of drives, altering file properties, and creating new folders.
- CCButton: Downloads and uploads information, masses into reminiscence, and captures the display.
- CCBitmap: Implements generally used Home windows instructions and utilities.
SIGNBT may fetch extra payloads from the C2 and deploy them on the host, offering Lazarus with operational versatility.
Kaspersky has seen Lazarus leverage that function on SIGNBT to load credential dumping instruments and the LPEClient malware on compromised methods.

LPEClient is an info-stealer and malware loader on itself, which, in its newest variations, Kaspersky says demonstrates important evolution in comparison with beforehand documented samples.
“It now employs superior strategies to enhance its stealth and keep away from detection, equivalent to disabling user-mode syscall hooking and restoring system library reminiscence sections,” mentions Kaspersky.
Kaspersky says Lazarus incorporates the LPEClient on different campaigns it ran in 2023, albeit it used the malware at earlier an infection phases to inject different payloads.
Total, the Lazarus group stays one of the vital lively and harmful risk actors, sustaining a broad concentrating on scope throughout areas and industries.
Their latest actions underscore their refined techniques and chronic targets, emphasizing organizations’ must proactively patch software program and forestall straightforward exploitation of vulnerabilities for preliminary compromise.


