CISA flagged two Roundcube Webmail vulnerabilities as actively exploited in assaults and ordered U.S. federal businesses to patch them inside three weeks.
Roundcube Webmail is a web-based e mail shopper that has been the default mail interface for the extensively used cPanel webhosting management panel since 2008.
The primary vulnerability tagged as actively abused by risk actors is a crucial distant code execution flaw tracked as CVE-2025-49113, which was first flagged as exploited days after it was patched in June 2025, when Web safety watchdog Shadowserver warned that over 84,000 weak Roundcube webmail installations had been weak to assaults.
Roundcube patched the second (CVE-2025-68461) two months in the past, in December 2025, warning that distant, unauthenticated attackers can exploit it by way of low-complexity cross-site scripting (XSS) assaults that abuse the animate tag in SVG paperwork.
“We strongly advocate to replace all productive installations of Roundcube 1.6.x and 1.5.x with this new variations,” the Roundcube safety crew warned when it launched variations 1.6.12 and 1.5.12 that deal with this safety flaw.
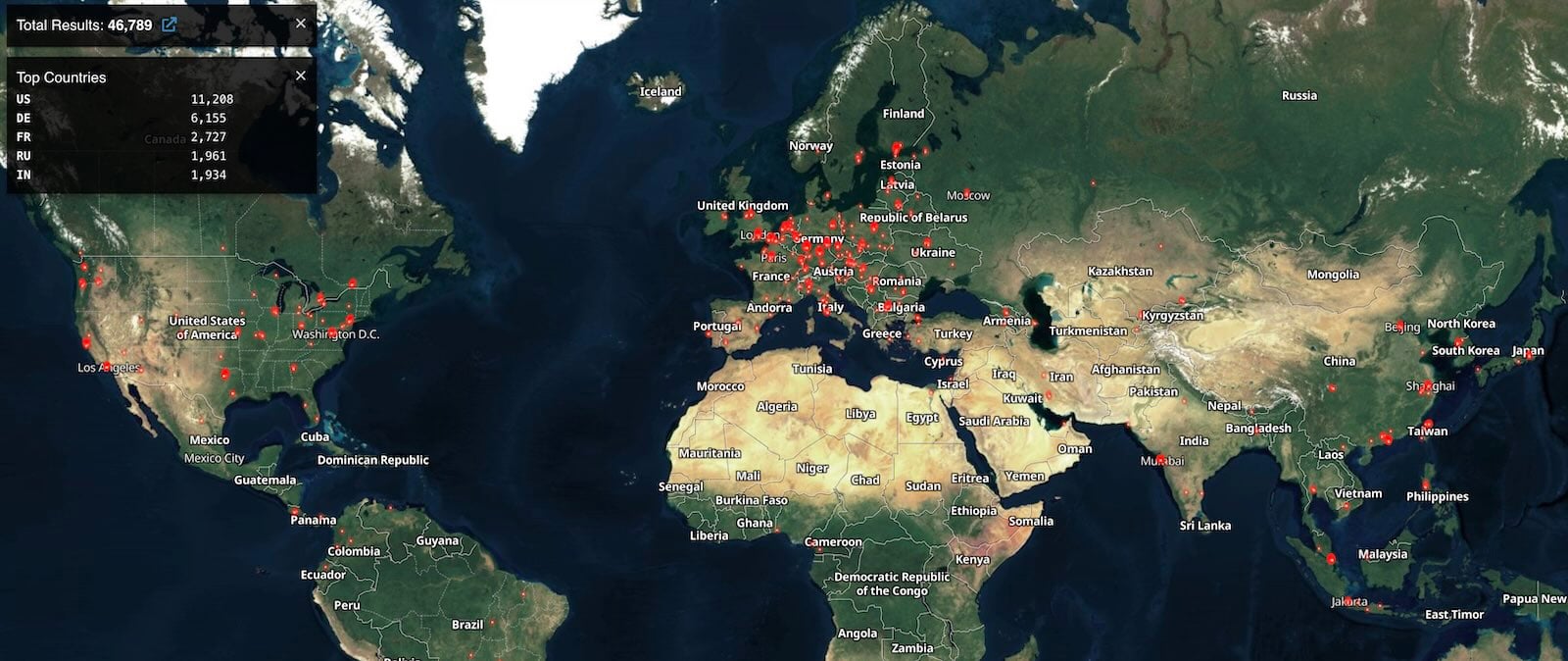
Shodan presently tracks over 46,000 Roundcube situations accessible on the web. Nevertheless, there is no such thing as a data on what number of of them are weak to CVE-2025-49113 or CVE-2025-68461 assaults.
Whereas it did not present any particulars on assaults exploiting these two safety flaws, CISA added them to its Identified Exploited Vulnerabilities (KEV) Catalog on Friday, warning that they’re “frequent assault vectors for malicious cyber actors and pose important dangers to the federal enterprise.”
CISA additionally tracks ten different Roundcube Webmail vulnerabilities which are both actively exploited in assaults or have been abused previously.
The U.S. cybersecurity company has ordered Federal Civilian Govt Department (FCEB) businesses to safe their methods towards these safety bugs inside three weeks, by March 13, as mandated by a binding operational directive (BOD 22-01) issued in November 2021.
Roundcube vulnerabilities have been a well-liked goal for cybercrime and state-sponsored risk teams, the newest being a saved cross-site scripting (XSS) vulnerability (CVE-2023-5631) exploited by the Winter Vivern (TA473) Russian hacking group in zero-day assaults focusing on European authorities entities and by the Russian APT28 cyber-espionage group to breach Ukrainian authorities e mail methods.
Trendy IT infrastructure strikes sooner than handbook workflows can deal with.
On this new Tines information, learn the way your crew can cut back hidden handbook delays, enhance reliability by way of automated response, and construct and scale clever workflows on high of instruments you already use.




