
CISA flagged a high-severity Ivanti Endpoint Supervisor (EPM) vulnerability as actively exploited in assaults and ordered U.S. federal businesses to patch techniques inside three weeks.
Ivanti’s EPM software program is an all-in-one endpoint administration resolution for managing shopper gadgets throughout Home windows, macOS, Linux, Chrome OS, and IoT platforms.
Tracked as CVE-2026-1603, this safety flaw could be exploited by distant menace actors with out privileges to bypass authentication and steal credential information in low-complexity cross-site scripting assaults that require no consumer interplay.
Ivanti patched the vulnerability one month in the past, when it launched Ivanti EPM 2024 SU5, which additionally addresses an SQL injection flaw that permits distant, authenticated attackers to learn arbitrary information from the database.
Whereas CISA has now tagged CVE-2026-1603 as exploited within the wild, Ivanti stated it acquired no experiences of exploitation when BleepingComputer reached out for affirmation on Monday.
“We aren’t conscious of any clients being exploited by these vulnerabilities previous to public disclosure. These vulnerabilities have been disclosed by our accountable disclosure program,” Ivanti says within the unique advisory.
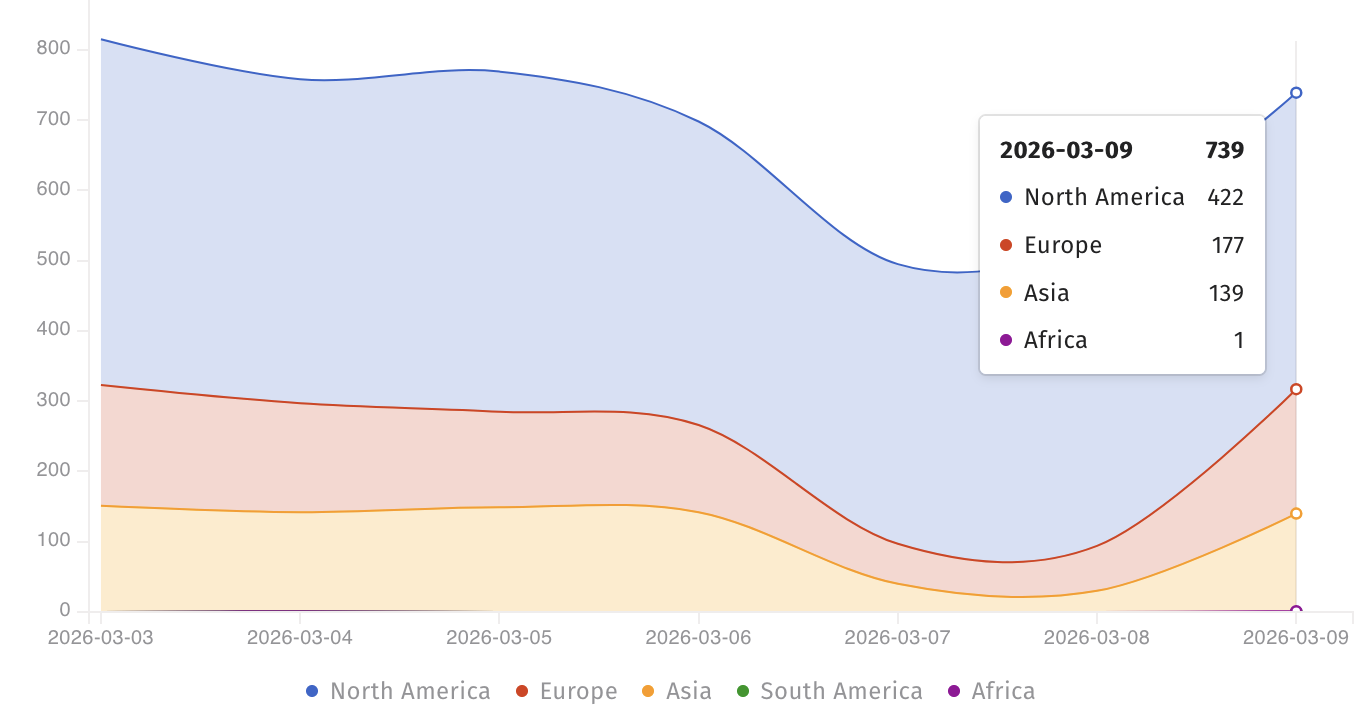
In the mean time, the Shadowserver menace monitoring platform tracks over 700 Web-facing Ivanti EPM cases, most of them in North America. Nevertheless, there isn’t a info on what number of of them are nonetheless weak to CVE-2026-1603 assaults.
Though it did not present any particulars on assaults exploiting this flaw, CISA added it to its Identified Exploited Vulnerabilities (KEV) Catalog on Monday, warning that such safety bugs are “frequent assault vectors for malicious cyber actors and pose vital dangers to the federal enterprise.”
The U.S. cybersecurity company has additionally ordered Federal Civilian Government Department (FCEB) businesses to patch their techniques inside three weeks, by March 23, as mandated by a binding operational directive (BOD 22-01) issued in November 2021.
Whereas Ivanti has but to seek out proof of energetic CVE-2026-1603 exploitation, menace actors usually goal Ivanti EPM vulnerabilities in assaults.
One 12 months in the past, CISA warned federal businesses to safe their networks in opposition to three different EPM flaws (CVE-2024-13159, CVE-2024-13160, and CVE-2024-13161) that have been exploited within the wild.
CISA additionally ordered U.S. authorities businesses to patch one other actively exploited EPM flaw (CVE-2024-29824) in October 2024.
Ivanti gives system and IT asset administration merchandise to greater than 40,000 firms by a community of greater than 7,000 companions worldwide.



