Sophos X-Ops is warning the hospitality business {that a} marketing campaign concentrating on resorts worldwide with password-stealing malware is utilizing emailed complaints about service issues or requests for info as a social engineering lure to realize the belief of the marketing campaign’s targets, earlier than sending them hyperlinks to malicious payloads.
The attackers are utilizing a technique much like the one Sophos X-Ops uncovered within the months main as much as the US federal tax submitting deadline in April 2023: They initially contact the goal over electronic mail that accommodates nothing however textual content, however with subject material a service-oriented enterprise (like a lodge) would wish to reply to shortly. Solely after the goal responds to the menace actor’s preliminary electronic mail does the menace actor ship a followup message linking to what they declare is particulars about their request or criticism.
The social engineering angle spans all kinds of subject material, however might be categorized into two generalized buckets: complaints about critical points the sender claims to have skilled in a current keep, or requests for info to assist with a possible future reserving.
Sophos X-Ops has already briefed representatives of the Retail and Hospitality Info Sharing and Evaluation Heart (RH-ISAC) about this assault concentrating on their business throughout the busy end-of-year vacation journey season.
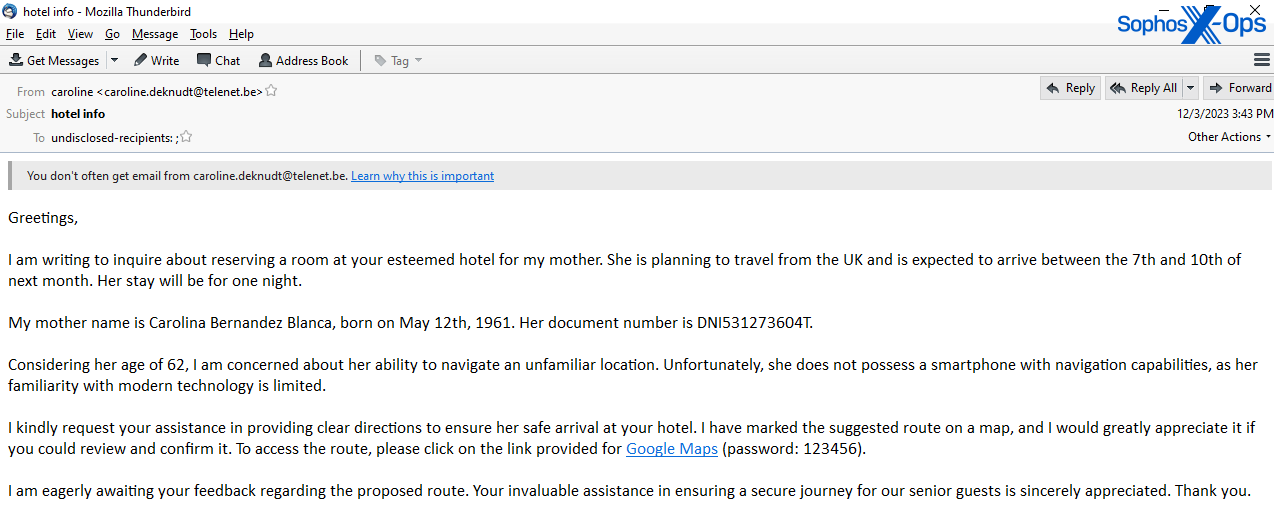
I’m writing to inquire
The content material of the ‘criticism’-style messages vary from allegations of violent assaults or bigoted habits by members of the lodge employees, to assertions that the “visitor” had gadgets stolen or misplaced from their room. The ‘requests for info’-type messages included emails asking for lodging for somebody with extreme allergy symptoms, messages about how the lodge might assist a enterprise assembly, or inquiries about accessibility inside the lodge for a disabled or aged visitor.
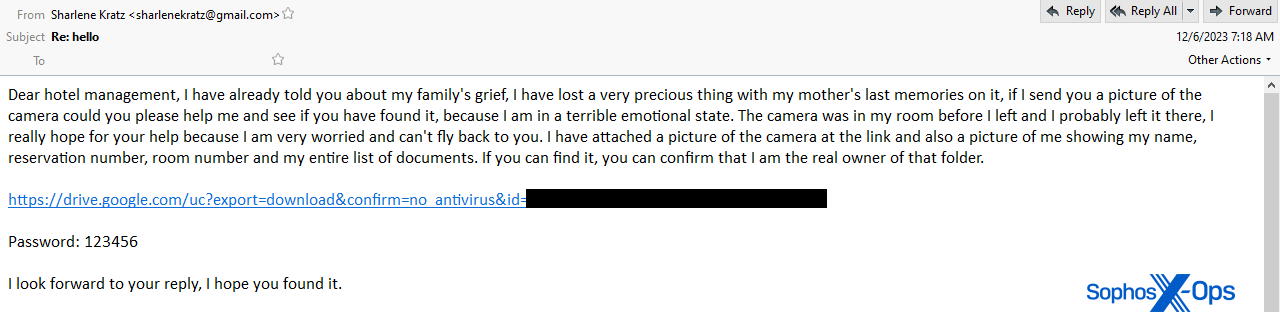
In each case, as soon as a consultant from the lodge responded to the preliminary inquiry asking for extra info, the menace actor replied with a message that – the attacker claims – hyperlinks to documentation or proof supporting their claims or requests. The “documentation” will not be precise documentation, however the malware payload, wrapped in a password-protected archive file.
The hyperlinks level to public cloud storage providers, similar to Google Drive, and the physique of the message accommodates a password (often numeric) that the recipient is prompted to make use of to open the Zip or Rar archive on the different finish of the obtain hyperlink.
Widespread traits of electronic mail messages within the marketing campaign
The messages attackers ship to lodge employees share some traits that make them extra suspicious and advantage further warning by recipients.
Like many profitable malspam campaigns, the messages are engineered to play on feelings and on the goal’s want to render help – a self-selecting trait for profitable individuals working within the hospitality business.
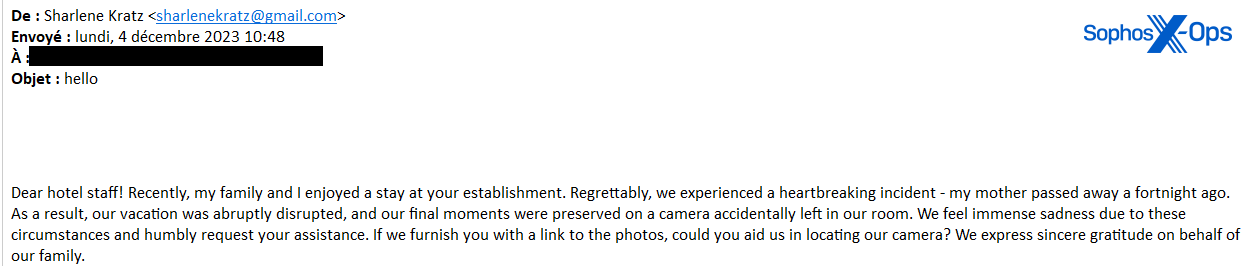
In a single instance, the menace actor tells a lodge staffer that they left a digicam behind in a room that accommodates pictures of a not too long ago deceased relative, and asks the lodge for assist finding the digicam.
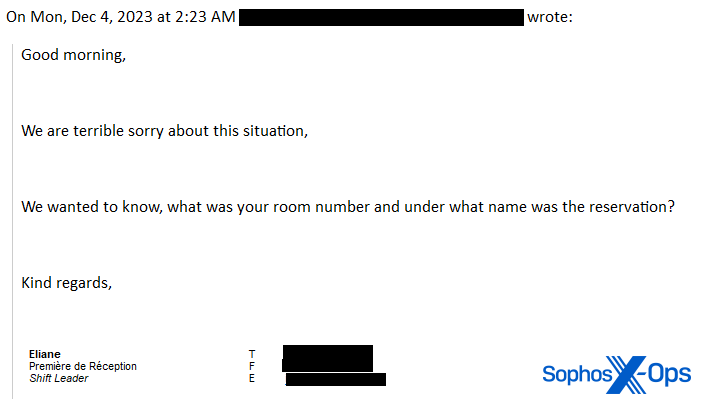
When the lodge employees replied, asking for the room quantity and identify the reservation was beneath, the menace actor replies, feigning exasperation.
“I’ve already informed you about my household’s grief, I’ve misplaced a really valuable factor with my mom’s final recollections on it, if I ship you an image of the digicam might you please assist me” together with a hyperlink to a file hosted on Google Drive, and the textual content “Password: 123456” under the hyperlink.
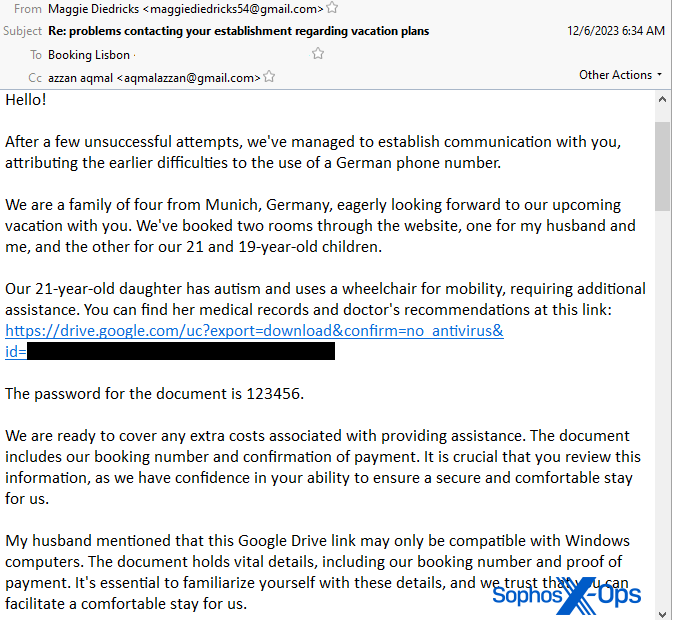
In one other instance, the menace actor emails a lodge and asks them to answer as a result of they “have been unable to contact you thru the web site or by cellphone.” When the reserving agent from the lodge asks them to offer extra particulars about their plans, the menace actor replies, claiming they’ve booked rooms by way of the web site however must make preparations for the lodging of a member of the family with a incapacity. Their second electronic mail hyperlinks to a zipper file hosted on Google Drive they declare accommodates “medical data and physician’s suggestions” and, once more, a password of 123456 wanted to open the file.
In that message, the menace actor provides the next “My husband talked about that this Google Drive hyperlink might solely be appropriate with Home windows computer systems. The doc holds important particulars, together with our reserving quantity and proof of fee. It’s important to familiarize your self with these particulars.”
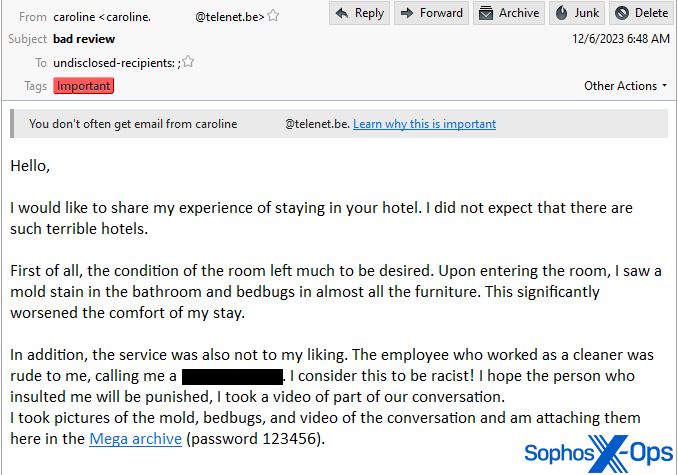
In what is likely to be essentially the most egregious instance, the menace actor requested for contact with a supervisor to deal with an issue they’d on the lodge. As soon as the supervisor replies, the menace actor writes “I didn’t count on there are such horrible resorts,” describing a horrifying (fictitious) expertise that included mouldy partitions, “bedbugs in virtually all of the furnishings” that “considerably worsened the consolation of my keep,” and an worker who used a racist epithet. The e-mail hyperlinks to a RAR archive file hosted on the Mega.nz cloud internet hosting supplier, additionally with a password of 123456, that the sender alleges accommodates a video of the confrontation between the visitor and employees member.
The emails all contrive an excuse to share documentation with the lodge employees by way of cloud storage, from Google Drive, Mega.nz, Dropbox, or from an tackle within the content material internet hosting area of the chat platform Discord. The malicious payloads linked from these messages have been compressed in both the Zip or Rar compression format, and used one of many following checklist of passwords.
- 1111
- 123456
- 2023
- info2023
- lodge
- 501949
We noticed many extra examples of inventive writing by the menace actor. Emails complained about friends contracting quite a lot of ailments; considerations over allergic reactions to cleansing merchandise; allegations of being poisoned within the lodge; stains on mattresses, partitions, or in bogs; bugs on furnishings within the rooms; purses, rings, costly watches or cameras being left behind or stolen from rooms; a necessity for lodging or help for friends with restricted mobility or entry to know-how; and impolite, violent, or bigoted habits by employees directed on the visitor.
Payloads designed to evade sandboxing
The malware payloads themselves have been created with the intent to make it tougher to scan or detect the malicious content material.
The archives are all password-protected, which prevents the cloud service internet hosting them from casually scanning the contents and detecting whether or not the payload is malicious.
When unpacked from their archive containers, the malware itself has traits that additionally assist it elude fast detection.
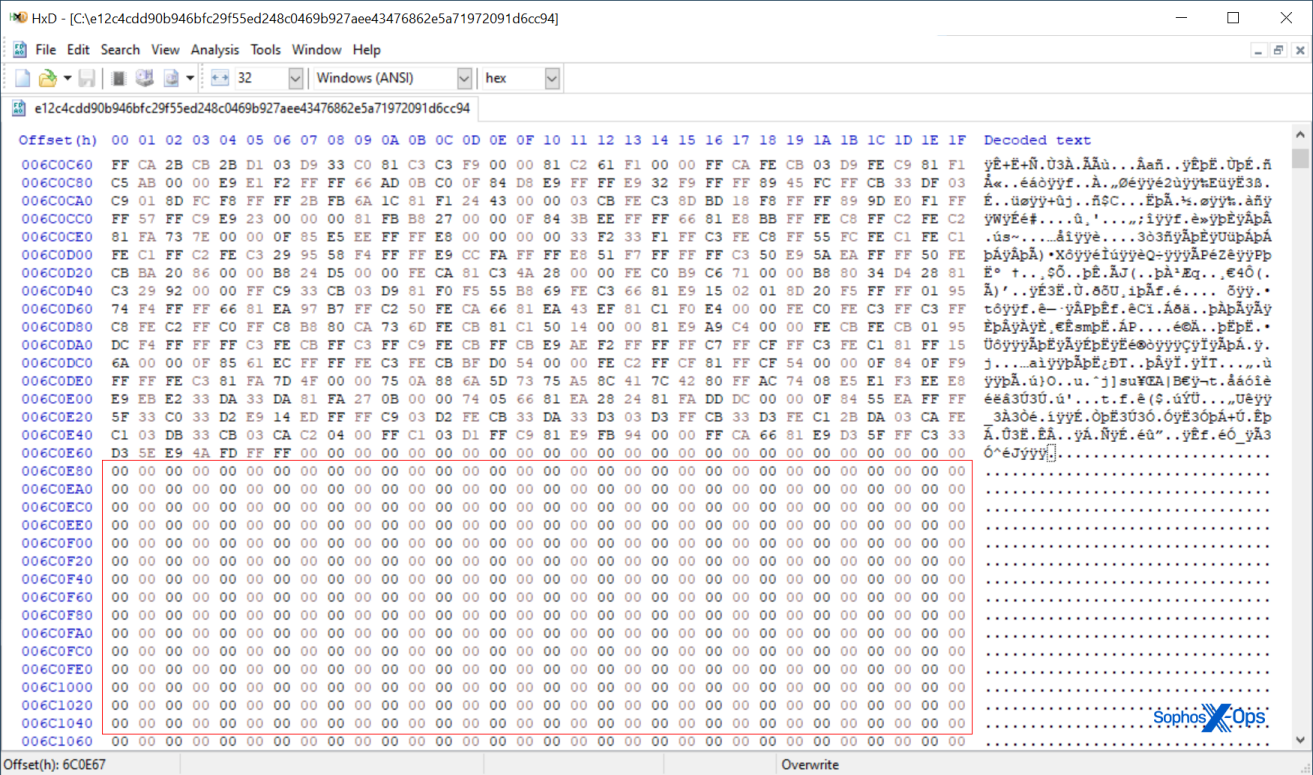
Lots of the unzipped or de-archived payload recordsdata are vastly bigger than a typical executable. A number of of the samples we uncovered weigh in at properly above 600MB in measurement. Recordsdata of this measurement is likely to be missed by static endpoint safety scanners designed to course of a lot smaller recordsdata.
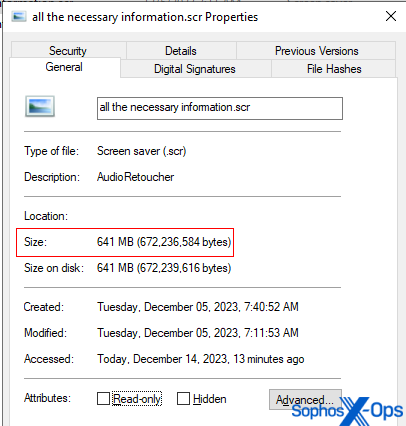 The overwhelming majority of the inner content material of these recordsdata was simply bytes containing zeroes, used as space-filler.
The overwhelming majority of the inner content material of these recordsdata was simply bytes containing zeroes, used as space-filler.
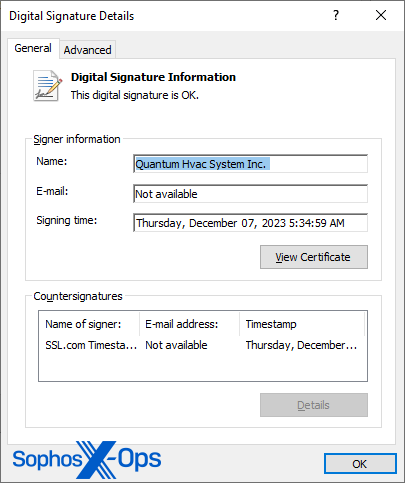
Practically all the samples have been signed with a code-validation certificates. Lots of the certificates are model new – obtained throughout the course of the marketing campaign’s operational interval – and queries of a few of these certificates point out the signature stays legitimate for most of the samples, whereas others seem like faked or counterfeit, and don’t cross validation.
Some endpoint safety instruments will robotically exclude executables with legitimate signatures from scanning; Some will solely search for the presence of a certificates, not bothering to test whether or not it’s legitimate.
Easy however efficient password-stealer malware
A lot of the samples seem like variants of a malware household variously referred to as Redline Stealer or Vidar Stealer. Regardless of their measurement, 99% of the amount of the malware executables (with both an .exe or .scr extension) which are better than 600MB in measurement are simply zeroes. The malware code is tacked on to the tip of the very giant recordsdata with soar instructions that leap over the empty area.
When executed, the malware instantly connects to a URL on the Telegram encrypted messaging service. The URL factors to a chat room, the title of which is an online tackle used for the bot’s command-and-control. On the time we examined this malware, the C2 tackle was an IP tackle and a high-numbered, nonstandard TCP port.
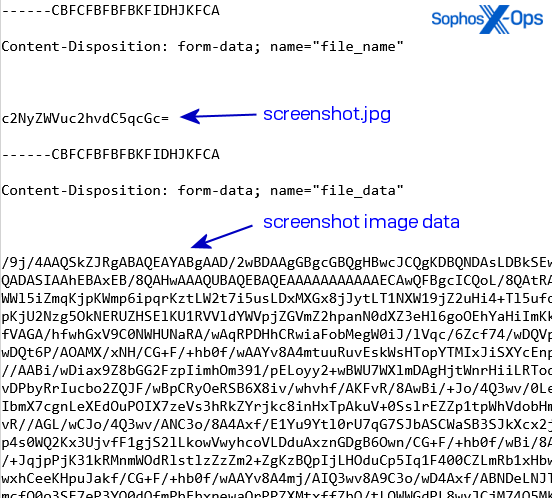
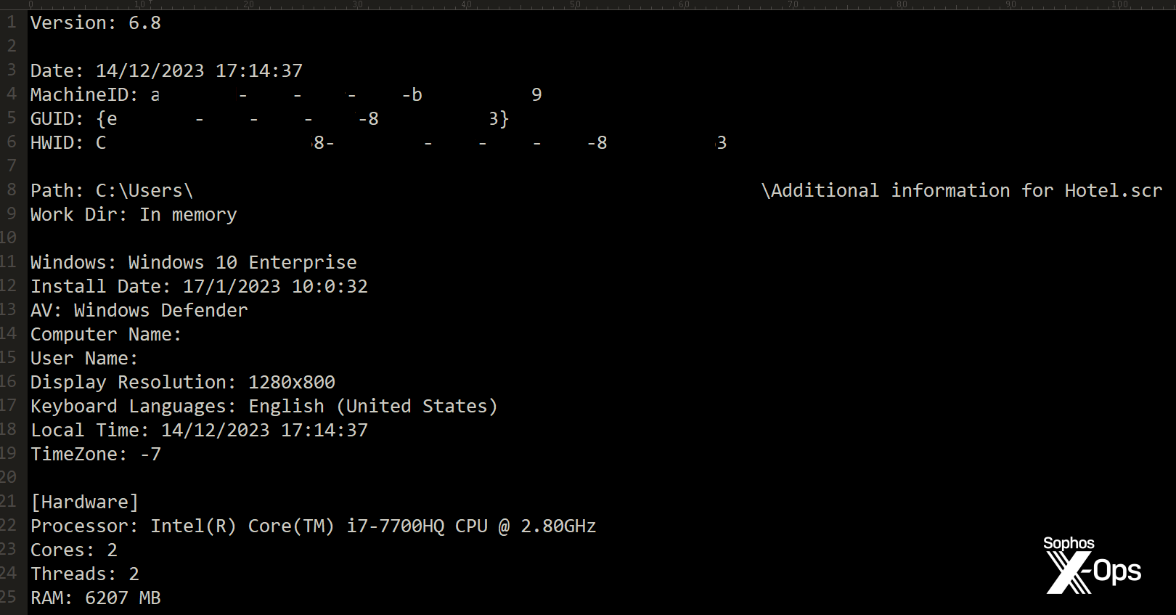
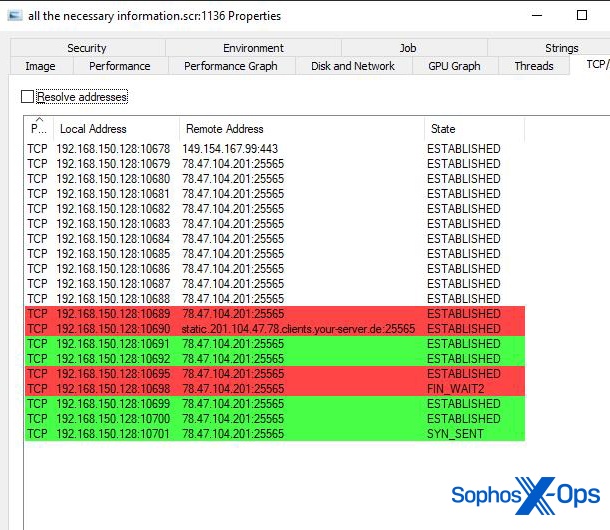 The bot then connects to the tackle it retrieves from the Telegram channel and downloads a payload able to quite a lot of options from that tackle. It makes use of HTTP POST requests to the C2 server to submit telemetry concerning the contaminated machine, together with particulars of account info saved within the browser and screenshots of the desktop. The server delivers info the bot can use to encrypt its communication in response.
The bot then connects to the tackle it retrieves from the Telegram channel and downloads a payload able to quite a lot of options from that tackle. It makes use of HTTP POST requests to the C2 server to submit telemetry concerning the contaminated machine, together with particulars of account info saved within the browser and screenshots of the desktop. The server delivers info the bot can use to encrypt its communication in response.
 The malware doesn’t set up persistence on the host machine. It runs as soon as, does its work extracting then exfiltrating the info it needs to steal, then quits. Along with passwords and cookie info, the bot profiles the machine it’s operating on, and sends every little thing about it to the bot controller. The samples we ran didn’t even delete themselves after operating.
The malware doesn’t set up persistence on the host machine. It runs as soon as, does its work extracting then exfiltrating the info it needs to steal, then quits. Along with passwords and cookie info, the bot profiles the machine it’s operating on, and sends every little thing about it to the bot controller. The samples we ran didn’t even delete themselves after operating.
 On the time of this writing, Sophos X-Ops has retrieved greater than 50 distinctive samples from cloud storage the place the recordsdata have been hosted by the menace actors conducting this marketing campaign. Now we have additionally reported the malicious hyperlinks to the varied cloud storage suppliers internet hosting the malware. Most of these samples displayed few-to-no detections in Virustotal.
On the time of this writing, Sophos X-Ops has retrieved greater than 50 distinctive samples from cloud storage the place the recordsdata have been hosted by the menace actors conducting this marketing campaign. Now we have additionally reported the malicious hyperlinks to the varied cloud storage suppliers internet hosting the malware. Most of these samples displayed few-to-no detections in Virustotal.
Sophos has printed indicators of compromise to our Github repository.
Sophos endpoint safety merchandise will detect the malware as Troj/Agent-BKJE. Makes an attempt to exfiltrate credentials are blocked utilizing the behavioral detection Creds_2D.
Acknowledgments
Sophos X-Ops thanks Senior Menace Researchers Felix Weyne and Anand Ajjan for recognizing the marketing campaign in its early levels and elevating the alarm, and employees on the RH-ISAC for his or her assist disseminating warnings about this assault to their members and the lodge business at giant.