An advert fraud botnet dubbed PEACHPIT leveraged a military of tons of of hundreds of Android and iOS gadgets to generate illicit earnings for the risk actors behind the scheme.
The botnet is a component of a bigger China-based operation codenamed BADBOX, which additionally entails promoting off-brand cellular and related TV (CTV) gadgets on standard on-line retailers and resale websites which can be backdoored with an Android malware pressure referred to as Triada.
“The PEACHPIT botnet’s conglomerate of related apps had been present in 227 international locations and territories, with an estimated peak of 121,000 gadgets a day on Android and 159,000 gadgets a day on iOS,” HUMAN mentioned.
The infections are mentioned to have been realized via a group of 39 apps that had been put in greater than 15 million instances. Units fitted with the malware allowed the operators to steal delicate information, create residential proxy exit friends, and commit advert fraud via the bogus apps.
It is at the moment not clear how the Android gadgets are compromised with a firmware backdoor, however proof factors to a {hardware} provide chain assault.
“Risk actors may use the backdoored gadgets to create WhatsApp messaging accounts by stealing one-time passwords from the gadgets,” the corporate mentioned.
“Moreover, risk actors can use the gadgets to create Gmail accounts, evading typical bot detection as a result of the account seems to be prefer it was created from a standard pill or smartphone, by an actual particular person.”
Particulars in regards to the felony enterprise had been first documented by Pattern Micro in Could 2023, attributing it to an adversary it tracks as Lemon Group.
HUMAN mentioned that it recognized at the least 200 distinct Android gadget sorts, together with cellphones, tablets, and CTV merchandise, which have exhibited indicators of BADBOX an infection, suggesting a widespread operation.
A notable facet of the advert fraud is the usage of counterfeit apps on Android and iOS made obtainable on main app marketplaces such because the Apple App Retailer and Google Play Retailer in addition to these which can be routinely downloaded to backdoored BADBOX gadgets.
Current throughout the Android apps is a module liable for creating hidden WebViews which can be then used to request, render, and click on on advertisements, and masquerading the advert requests as originating from respectable apps, a method beforehand noticed within the case of VASTFLUX.
The fraud prevention agency famous that it labored with Apple and Google to disrupt the operation, including “the rest of BADBOX must be thought-about dormant: the C2 servers powering the BADBOX firmware backdoor an infection have been taken down by the risk actors.”
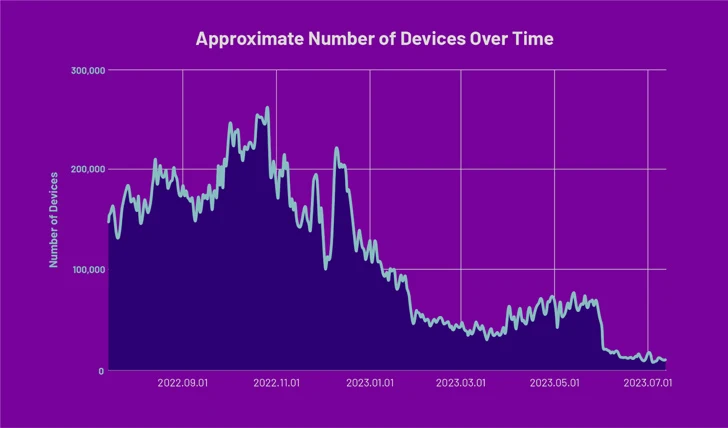
What’s extra, an replace pushed out earlier this 12 months has been discovered to take away the modules powering PEACHPIT on BADBOX-infected gadgets in response to mitigation measures deployed in November 2022.
That having mentioned, it is suspected the attackers are adjusting their ways in a possible try to avoid the defenses.
“What makes issues worse is the extent of obfuscation the operators went via to go undetected, an indication of their elevated sophistication,” HUMAN mentioned. “Anybody can by accident purchase a BADBOX gadget on-line with out ever figuring out it was pretend, plugging it in, and unknowingly opening this backdoor malware.”