In a co-ordinated public-private operation between regulation enforcement companies and cybersecurity trade companions one of many world’s most prolific phishing-as-a-service platforms has been dismantled.
First showing in August 2023, Tycoon 2FA was designed particularly to assist fraudsters hack into accounts defended by multi-factor authentication and steal session cookies, and was liable for tens of hundreds of thousands of fraudulent emails and nearly tens of hundreds of confirmed victims around the globe.
What many pc customers don’t realise is that though enabling multi-factor authentication (MFA) on their Microsoft 365 or Gmail accounts is advisable and hardens their safety towards hackers, it doesn’t make it unattainable for them to be breached.
Tycoon 2FA’s key trick was the way it may bypass MFA by sitting between the sufferer and the reliable service. A pretend web site that appeared equivalent to the true one does not simply acquire a sufferer’s login credentials – it instantly forwards them to the true website in actual time, performing as a clear proxy. When the sufferer enters their one-time-password on the pretend website, it’s forwarded to the true website earlier than it expires, and the assault positive aspects a fully-authenticated session.
For a beginning value of roughly US $120 per thirty days, Tycoon 2FA’s clients gained entry by way of non-public Telegram channels to an off-the-shelf phishing equipment, permitting even these with restricted technical experience to run refined account-takeover campaigns at scale.
By mid-2025, Tycoon 2FA is claimed to have accounted for about 62% of all phishing makes an attempt blocked by Microsoft, together with greater than 30 million emails in a single month.
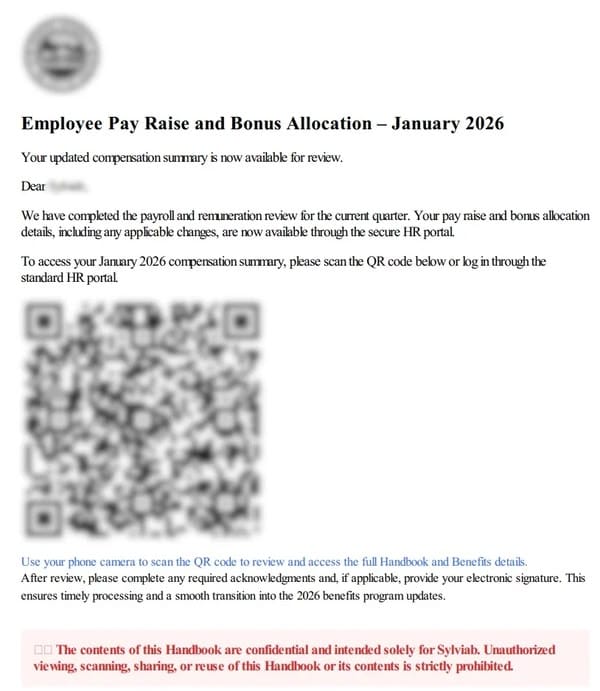
In keeping with experiences, healthcare and training organisations have been hit onerous with greater than 100 members of threat-sharing group Well being-ISAC have been focused. In New York alone, not less than two hospitals, six municipal colleges, and three universities confronted tried or profitable compromised — inflicting disruption and delays to affected person care and operations.
Performing below a US. court docket order, Microsoft seized 330 energetic domains powering Tycoon 2FA’s core infrastructure. In the meantime, regulation enforcement authorities in Latvia, Lithuania, Portugal, Poland, Spain, and the UK additionally seized infrastructure utilized by the legal operation.
Tech agency Cloudflare went additional, asserting that it has banned hundreds of domains and Employees initiatives, suspended associated accounts, and erased all related Employees scripts — blocking the equipment’s proxy performance on the edge. For domains that would not be legally seized as native regulation enforcement companies have been non-cooperative, Cloudflare deployed warning pages to dam victims trying to entry phishing hyperlinks.
Clearly it is a good factor that one of the vital harmful phishing platforms in existence has been taken offline. Nevertheless it have to be remembered that the cybercrime trade abhors a vacuum, and chances are high that different legal operators are prone to fill the void rapidly.
One lesson to study is that not all MFA is created equal. We have now prior to now inspired customers to not depend upon SMS-based multi-factor authentication due to the issue of SIM-swapping attackers the place fraudsters divert login codes to telephones below their very own management. Tycoon-style proxy assaults, in the meantime, are rather more troublesome for fraudsters to efficiently pull off if customers have protected their accounts with {hardware} safety keys or passkeys.



