The shape and quiz-building software is a well-liked vector for social engineering and malware. Right here’s the right way to keep protected.
23 Apr 2025
•
,
5 min. learn

When Google enters a specific market, it usually means dangerous information for the incumbents. So it was with Google Varieties, the tech big’s kind and quiz-building software that launched in 2008. In accordance with one estimate, it now has a market share of practically 50%.
Nevertheless, with nice market share comes higher scrutiny from nefarious parts. Menace actors are previous masters at abusing common know-how for their very own ends. And they’re doing so with Google Varieties to harvest delicate info from their victims and even trick them into putting in malware.
Why Google Varieties?
Malicious actors are at all times on the lookout for methods so as to add legitimacy to scams and evade e mail safety filters. Google Varieties presents an incredible alternative to do each. It’s favored by cybercriminals as a result of it’s:
- Free, that means risk actors can launch campaigns at scale with a doubtlessly profitable return on their funding
- Trusted by customers, which will increase the probabilities of victims believing that the Google Type they’re being despatched or redirected to is reputable
- A reputable service, that means that malicious Google Varieties and hyperlinks to malicious kinds are sometimes waved by means of by conventional e mail safety instruments
- Straightforward to make use of, which is sweet for customers but in addition helpful for cybercriminals – that means they will launch convincing phishing campaigns with little or no effort or prior data of the software
- Cybercriminals additionally reap the benefits of the truth that Google Varieties communications are encrypted with TLS, which can make it more durable for safety instruments to see in and test for any malicious exercise. Equally, the answer usually makes use of dynamic URLs, which can make it difficult for some e mail safety filters to identify malicious kinds.
What do Google Varieties assaults appear like?
Most Google Varieties threats use the software to trick customers into handing over their private and monetary info, though there are slight variations on how risk actors obtain this. Listed below are a number of the important methods to look out for:
Phishing-related kinds
Menace actors create Google Varieties designed to spoof reputable manufacturers, akin to log-in pages for social media websites, banks and universities, and even fee pages. As talked about, the benefit for the dangerous guys is that it’s faster, simpler and cheaper to take action than construct a devoted phishing website, and fewer prone to be blocked by safety filters.
Usually, you’ll obtain a hyperlink to one in every of these malicious Google Varieties by way of a phishing e mail, which itself could also be spoofed to impersonate a reputable model or sender. The e-mail could even come from a reputable account that has been hijacked. Both manner, the tip objective is normally to:
- Harvest your log-ins, which may then be used to hijack accounts and commit id fraud
- Steal your card particulars or banking/crypto info as a way to take over these accounts and drain them of funds or commit fee fraud
- Persuade you to click on on a hyperlink within the malicious Google Type that redirects you to a website which covertly installs malware in your machine
Name again phishing
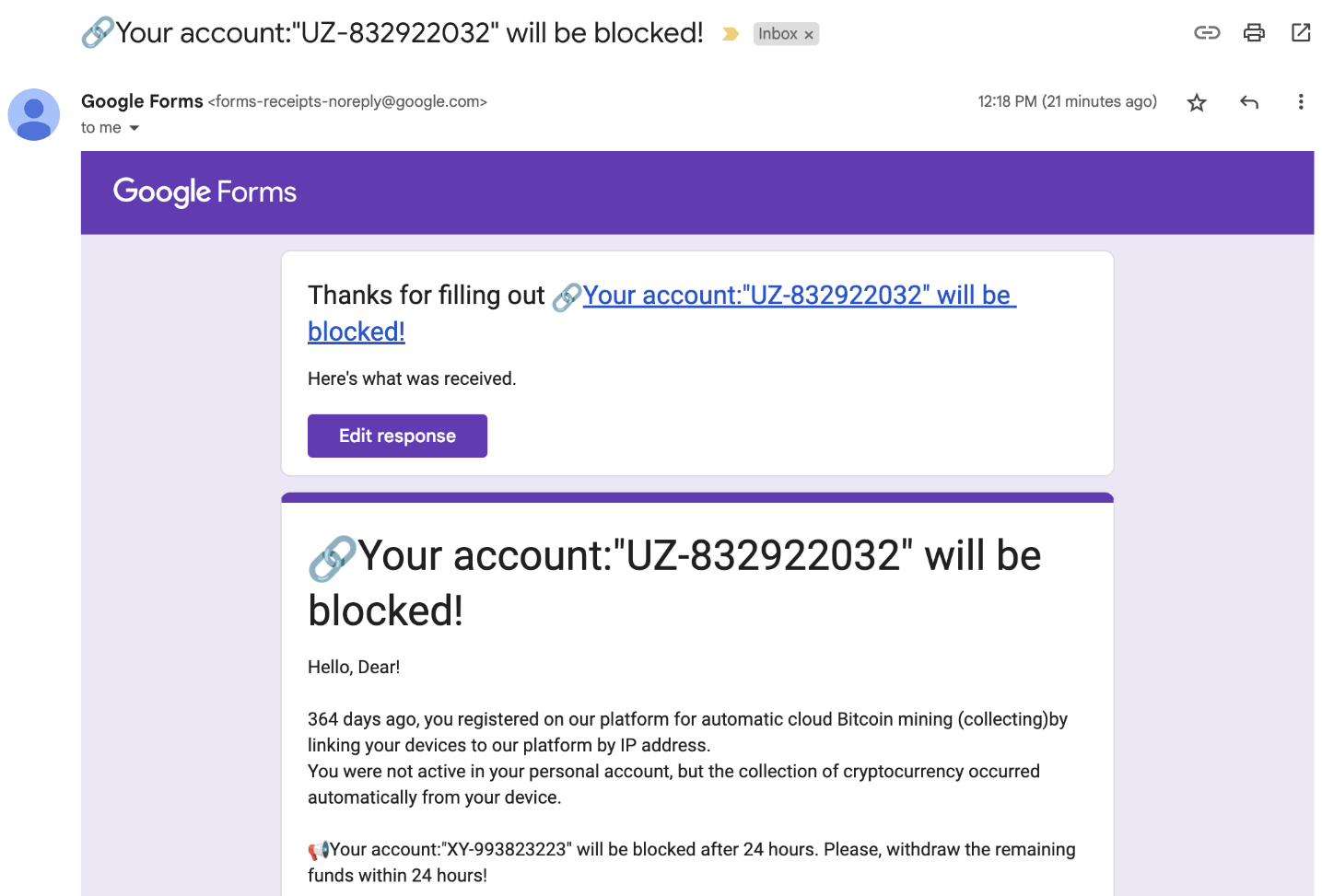
Attackers ship you a malicious Google Type crafted to trick you into calling a cellphone quantity listed on it. The shape could also be spoofed to seem as if despatched from a financial institution or different trusted service supplier. A way of urgency is created to rush you into making a rash determination – calling the quantity with out pondering issues by means of first. Typically the shape will state that your account might be blocked or that cash was taken (or might be taken out of your account) except you get in contact.
When you name again, you’ll be chatting with a member of a voice phishing (vishing) gang that makes use of attraction to persuade you into handing over private and monetary info. They might additionally recommend downloading distant entry software program to your machine, which might give them full management over your pc.
Quiz spam
Cybercriminals may abuse the quiz function in Google Varieties – by making a quiz and including your e mail deal with. Hitting “launch scores” will generate a message which the risk actor can customise – probably including hyperlinks to phishing, malware or rip-off websites.
Assaults within the wild
Among the many real-world campaigns safety researchers have seen lately are:
BazarCall
A vishing-type risk through which victims obtained an e mail containing a malicious Google Type impersonating PayPal, Netflix, or one in every of a number of different big-name manufacturers. The shape contained particulars of a faux cost which is about to be utilized, except the recipient calls the cellphone quantity equipped.
Phishing focusing on US universities
Google detected a rise in assaults on the US schooling sector final 12 months. Victims obtained phishing emails containing a hyperlink to a malicious Google Type. Each the preliminary e mail and kind had been spoofed to seem as if despatched by the college, by that includes logos, mascots and references to the college identify. The tip objective was to reap logins and/or monetary particulars.
Conserving your defenses up
Consciousness is half the battle with regards to mitigating the impression of social engineering threats like this. Now that you know the way the dangerous guys function, it must be more durable for them to trick you into making dangerous selections on-line. To maintain Google Type threats at bay, take into account the next:
- Use multi-layered safety software program from a good supplier on all computer systems and cellular units. It will assist to make sure that, even for those who click on on a malicious hyperlink, the malware obtain might be blocked. Good software program can even spot suspicious patterns, even when the Google Type itself seems reputable, in addition to scan your machine/system periodically and maintain you protected from something malicious.
- Keep alert to potential phishing scams. You shouldn’t belief something unsolicited which asks you to click on on a hyperlink or name a quantity urgently. As an alternative, take a deep breath, loosen up, and get in touch with the sender individually; not by way of the quantity or hyperlink offered. One other helpful tactic is to hover over hyperlinks to test the true vacation spot. Be certain your e mail safety answer
- Improve safety at log-in by utilizing robust, distinctive passwords for each account, saved in a password supervisor for simple recall. Then swap on multi-factor authentication (MFA) for each account you utilize on-line. Because of this, even when hackers pay money for your password, they will’t entry your account. A hardware-based safety key or an authenticator app is finest.
- Concentrate: Google at all times shows a warning on Google Varieties, telling recipients “By no means submit passwords by means of Google Varieties”. Comply with its recommendation.
If the worst occurs and also you suppose you’ve fallen sufferer to a Google Varieties assault, change your passwords, run a malware scan, and inform your financial institution to freeze any playing cards (for those who’ve submitted card particulars). Swap on MFA for all accounts for those who’ve not already, and monitor your accounts for any uncommon exercise.
Just by studying this text, you can be in a great place with regards to warding off the risk from malicious Google Varieties. Be skeptical of any unsolicited e mail you obtain – even when it’s from a trusted model.



