
A complicated malicious marketing campaign that researchers name OneClik has been leveraging Microsoft’s ClickOnce software program deployment device and customized Golang backdoors to compromise organizations inside the power, oil, and fuel sectors.
The hackers depend on authentic AWS cloud providers (AWS, Cloudfront, API Gateway, Lambda) to maintain the command and management (C2) infrastructure hidden.
ClickOnce is a deployment expertise from Microsoft that enables builders to create self-updating Home windows-based purposes, lowering consumer interplay to a minimal.
Safety researchers at cybersecurity firm Trellix analyzed three variants of the marketing campaign (v1a, BPI-MDM, and v1d), all of them deploying “a complicated Golanguage backdoor” known as RunnerBeacon by way of a .NET-based loader tracked as OneClikNet.
Based on them, every model of the OneClik marketing campaign developed with superior techniques and C2 obfuscation, sturdy anti-analysis, and sandbox evasion strategies.
Whereas operational indicators level to China-affiliated risk actors, the researchers are cautious in making an attribution.
Abusing Microsoft’s ClickOnce deployment device
OneClik assaults mix authentic instruments with customized malware and cloud and enterprise tooling, which permits the risk actor to evade detection of the operation.
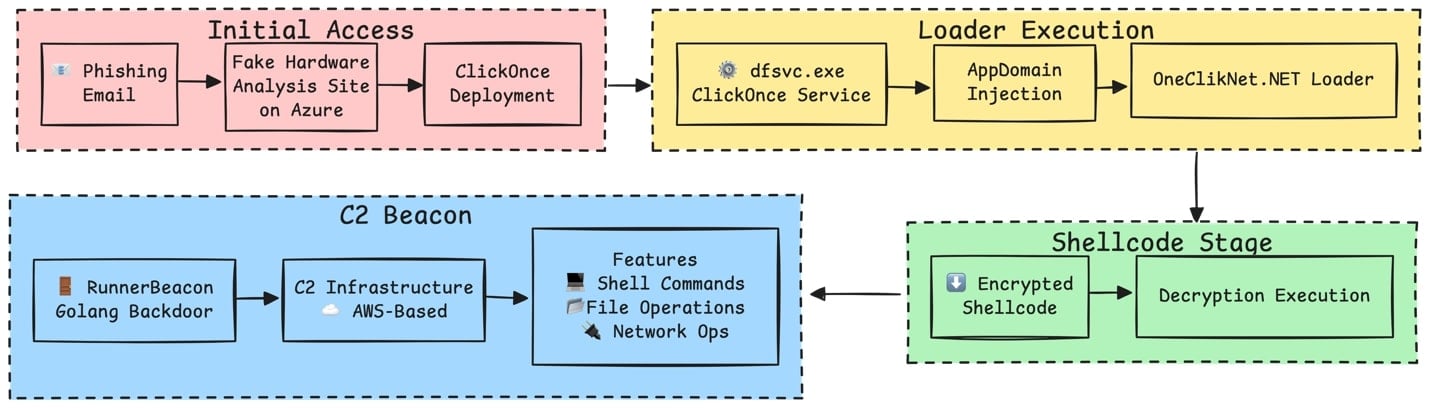
It begins with a phishing electronic mail with a hyperlink to a faux {hardware} evaluation web site hosted within the Azure ecosystem that delivers a .APPLICATION file (ClickOnce manifest) disguised as a authentic device.
Trellix researchers say that the attacker used ClickOnce apps as a supply mechanism for malicious payloads with out triggering the consumer account management mechanism.
“ClickOnce apps launch underneath the Deployment Service (dfsvc.exe), enabling attackers to proxy execution of malicious payloads by this trusted host.
As a result of ClickOnce purposes run with user-level privileges (no consumer account management required), they provide an interesting supply mechanism for risk actors aiming to keep away from privilege escalation,” the researchers clarify.
supply: Trellix
After execution, the ClickOnce loader runs malicious payloads by hijacking how the .NET utility masses assemblies, a way known as AppDomainManager injection.
Within the case of OneClik, this allowed the risk actor to make use of a authentic .NET executable, similar to ZSATray.exe, umt.exe, or ied.exe, to load one thing else than the traditional dependencies.
“With the loader in place, payload execution proceeds underneath dfsvc.exe, mixing with benign ClickOnce actions,” Trellix researchers say.
To hide the operation for an extended interval, the risk actor leveraged authentic AWS providers, which made C2 communication seem as regular cloud utilization because it blended with innocent CDN visitors.
Within the OneClik v1a variant, the beacon contacted a Cloudfront distribution area and an API Gateway endpoint. Within the v1d it used an AWS Lambda operate URL because the HTTP callback tackle.
“By “hiding within the cloud,” attackers exploit the excessive belief and availability of AWS: defenders should decrypt SSL or denylist whole AWS domains to note this visitors, which is usually impractical,” Trellix researchers make clear.
Go-based RunnerBeacon backdoor
An evaluation of the Golang-based RunnerBeacon backdoor confirmed that its C2 protocol encrypted all visitors utilizing the RC4 stream cipher algorithm and serialized information utilizing MessagePack.
It incorporates a modular message protocol with a number of message sorts, amongst them BeaconData, FileRequest, CommandRequest, SOCKSRequest, and FileUpload.
A few of the strategies the backdoor makes use of to hinder evaluation, the researchers discovered an “obfuscate_and_sleep” routine and randomized “jitter” in beacon intervals.
The researchers additionally noticed high-level instructions that enable the risk actor to:
- execute shell instructions (CreateProcessW)
- numerate processes
- run file operations (listing itemizing, add, obtain)
- perform network-related duties (port scanning)
- set up a SOCKS5 tunnel to proxy information visitors
Further RunnerBeacon capabilities embrace superior operations like course of injection and setting the stage for privilege escalation.
Trellix says that RunnerBeacon’s design is much like identified Go-based Cobalt Strike beacons like these within the Geacon household.
Because of the similarities within the set of instructions and the usage of cross-protocol C2, they are saying that “RunnerBeacon could also be an developed fork or privately modified variant of Geacon, tailor-made for stealthier, and cloud-friendly operations”
Cautious attribution
Though the OneClik marketing campaign was found lately, at first of March, a variant of the RunnerBeacon loader was recognized in September 2023 at an organization within the Center East within the oil and fuel sector.
The supply technique couldn’t be decided however the variant’s code is sort of an identical to the analyzed module from the OneClik operation.
The clues pointing to exercise associated to a China-affiliated state actor embrace techniques, strategies, and procedures seen in different campaigns attributed to Chinese language risk actors.
Trellix highlights that the .NET AppDomainManager injection method has been utilized in a number of cyberattacks attributed to Chinese language risk actors. The identical goes for the tactic used to deploy the encrypted payload.
Moreover, earlier China-linked campaigns present a desire for cloud-based staging utilizing providers from Alibaba and Amazon.
Nonetheless, these overlaps will not be sufficient to attribute the OneClik assaults to a selected risk actor.
The report from Trellix features a complete listing of indicators of compromise for all parts within the OneClik marketing campaign, starting from phishing lures and malware loaders to configuration recordsdata, backdoor binaries, authentic executables, domains, and configuration parameters.



