
A China-aligned APT menace actor named “TheWizards” abuses an IPv6 networking function to launch adversary-in-the-middle (AitM) assaults that hijack software program updates to put in Home windows malware.
In keeping with ESET, the group has been energetic since at the least 2022, concentrating on entities within the Philippines, Cambodia, the United Arab Emirates, China, and Hong Kong. Victims embody people, playing firms, and different organizations.
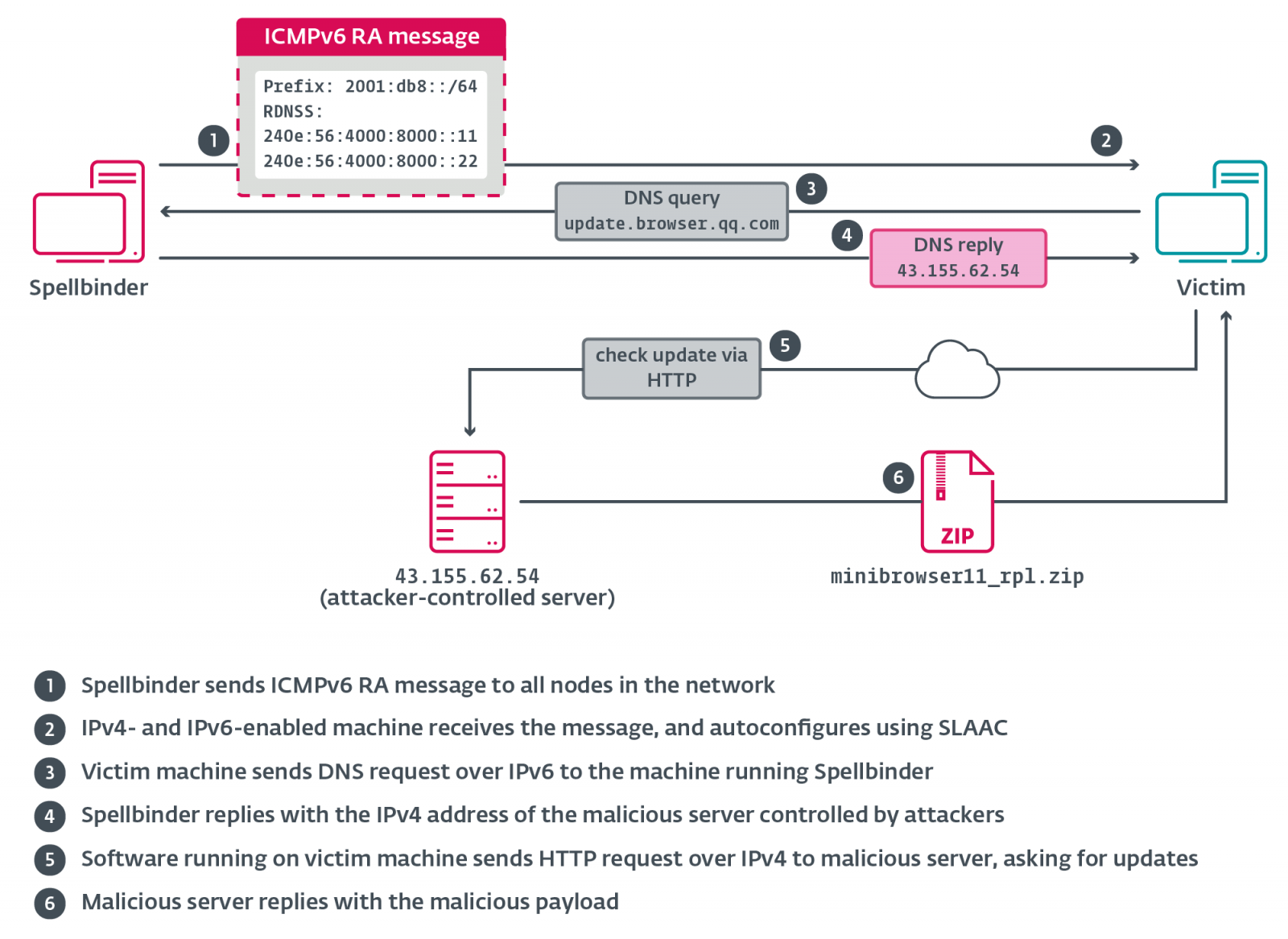
The assaults make the most of a customized instrument dubbed “Spellbinder” by ESET that abuses the IPv6 Stateless Deal with Autoconfiguration (SLAAC) function to conduct SLACC assaults.
SLAAC is a function of the IPv6 networking protocol that permits gadgets to mechanically configure their very own IP addresses and default gateway with no need a DHCP server. As a substitute, it makes use of Router Commercial (RA) messages to obtain IP addresses from IPv6-supported routers.
The hacker’s Spellbinder instrument abuses this function by sending spoofed RA messages over the community, inflicting close by methods to mechanically obtain a brand new IPv6 IP handle, new DNS servers, and a brand new, most popular IPv6 gateway.
This default gateway, although, is the IP handle of the Spellbinder instrument, which permits it to intercept communications and reroute visitors by way of attacker-controlled servers.
“Spellbinder sends a multicast RA packet each 200 ms to ff02::1 (“all nodes”); Home windows machines within the community with IPv6 enabled will autoconfigure by way of stateless handle autoconfiguration (SLAAC) utilizing data supplied within the RA message, and start sending IPv6 visitors to the machine operating Spellbinder, the place packets can be intercepted, analyzed, and replied to the place relevant,” explains ESET.
Supply: ESET
ESET mentioned assaults deploy Spellbinder utilizing an archive named AVGApplicationFrameHostS.zip, which extracts right into a listing mimicking official software program: “%PROGRAMFILESpercentAVG Applied sciences.”
Inside this listing are AVGApplicationFrameHost.exe, wsc.dll, log.dat, and a official copy of winpcap.exe. The WinPcap executable is used to side-load the malicious wsc.dll, which masses Spellbinder into reminiscence.
As soon as a tool is contaminated, Spellbinder begins capturing and analyzing community visitors making an attempt to attach particular domains, akin to these associated to Chinese language software program replace servers.
ESET says the malware displays for domains belonging to the next firms: Tencent, Baidu, Xunlei, Youku, iQIYI, Kingsoft, Mango TV, Funshion, Yuodao, Xiaomi, Xiaomi Miui, PPLive, Meitu, Quihoo 360, and Baofeng.
The instrument then redirects these requests to obtain and set up malicious updates that deploy a backdoor named “WizardNet.”
The WizardNet backdoor provides attackers persistent entry to the contaminated machine and permits them to put in further malware as wanted.
To guard towards all these assaults, organizations can monitor IPv6 visitors or flip off the protocol if it’s not required of their setting.
In January, ESET additionally reported on one other hacking group named “Blackwood” hijacking the WPS Workplace software program replace function to put in malware.



