Menace actors are abusing the special-use “.arpa” area and IPv6 reverse DNS in phishing campaigns that extra simply evade area fame checks and electronic mail safety gateways.
The .arpa area is a particular top-level area reserved for web infrastructure moderately than regular web sites. It’s used for reverse DNS lookups, which permit techniques to map an IP handle again to a hostname.
IPv4 reverse lookups use the in-addr.arpa area, whereas IPv6 makes use of ip6.arpa. In these lookups, DNS queries a hostname derived from the IP handle, written in reverse order and appended to certainly one of these domains.
For instance, www.google.com has the IP addresses 192.178.50.36 (IPv4) and 2607:f8b0:4008:802::2004 (IPv6). Querying Google’s IP of 192.178.50.36 through the dig software resolves to an in-addr.arpa hostname and finally an everyday hostname:
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 192.178.50.36
;; international choices: +cmd
;; Obtained reply:
;; ->>HEADER<<- opcode: QUERY, standing: NOERROR, id: 59754
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: model: 0, flags:; udp: 4096
;; QUESTION SECTION:
;36.50.178.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
36.50.178.192.in-addr.arpa. 1386 IN PTR lcmiaa-aa-in-f4.1e100.web.
;; Question time: 7 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:57:31 EST 2026
;; MSG SIZE rcvd: 94Querying Google’s IPv6 handle of 2607:f8b0:4008:802::2004 reveals that it first resolves to an IPv6.arpa hostname after which a hostname, as proven beneath.
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 2607:f8b0:4008:802::2004
;; international choices: +cmd
;; Obtained reply:
;; ->>HEADER<<- opcode: QUERY, standing: NOERROR, id: 31116
;; flags: qr rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: model: 0, flags:; udp: 4096
;; QUESTION SECTION:
;4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. IN PTR
;; ANSWER SECTION:
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR tzmiaa-af-in-x04.1e100.web.
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR mia07s48-in-x04.1e100.web.
;; Question time: 10 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:58:43 EST 2026
;; MSG SIZE rcvd: 171Phishing marketing campaign abuses in .arpa domains
A phishing marketing campaign noticed by Infoblox makes use of the ip6.arpa reverse DNS TLD, which usually maps IPv6 addresses again to hostnames utilizing PTR information.
Nonetheless, attackers discovered that in the event that they reserve their very own IPv6 handle area, they will abuse the reverse DNS zone for the IP vary by configuring further DNS information for phishing websites.
In regular DNS performance, reverse DNS domains are used for PTR information, which permit techniques to find out the hostname related to a queried IP handle.
Nonetheless, attackers found that after they gained management over the DNS zone for an IPv6 vary, some DNS administration platforms allowed them to configure different report sorts that may be abused for phishing assaults.
“We now have seen menace actors abuse Hurricane Electrical and Cloudflare to create these information—each of which have good reputations that actors leverage—and we confirmed that another DNS suppliers additionally enable these configurations,” explains Infoblox.
“Our checks weren’t exhaustive, however we notified the suppliers the place we found a niche. Determine 2 depicts the method the menace actor used to create the area used within the phishing emails.”
To arrange the infrastructure, the attackers first obtained a block of IPv6 addresses through IPv6 tunneling providers.
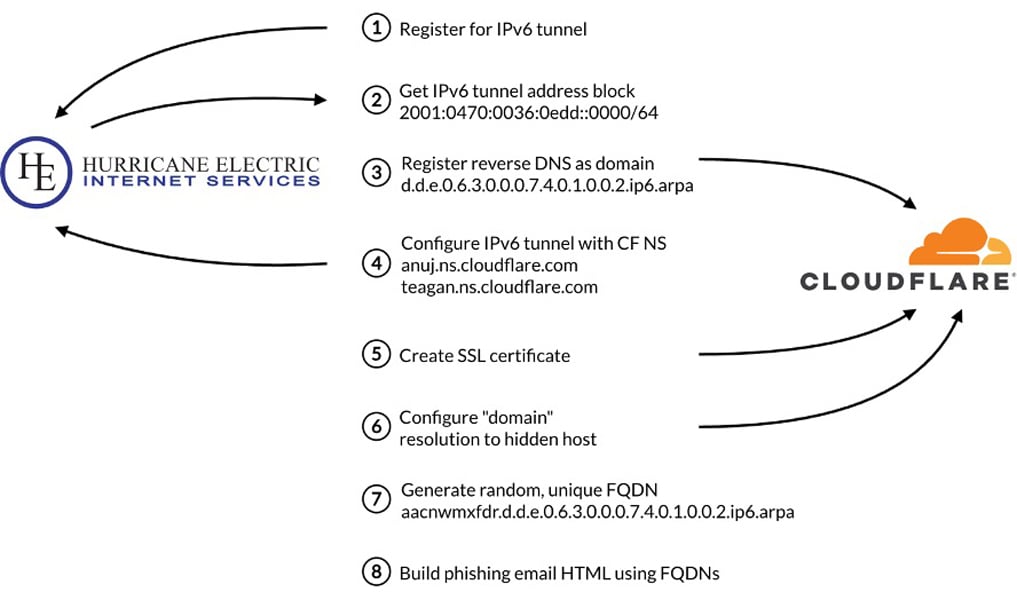
Supply: Infoblox
After gaining management of the handle area, the attackers then generate reverse DNS hostnames from the IPv6 handle vary utilizing randomly generated subdomains which can be tough to detect or block.
As an alternative of configuring PTR information as anticipated, the attackers create A information that time these reverse DNS domains to infrastructure internet hosting phishing websites.
The phishing emails on this marketing campaign use lures that promise a prize, a survey reward, or an account notification. The lures are embedded within the emails as photos linked to a reverse IPv6 DNS report, resembling “d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa,” moderately than an everyday hostname, so the goal would not see an odd arpa hostname.
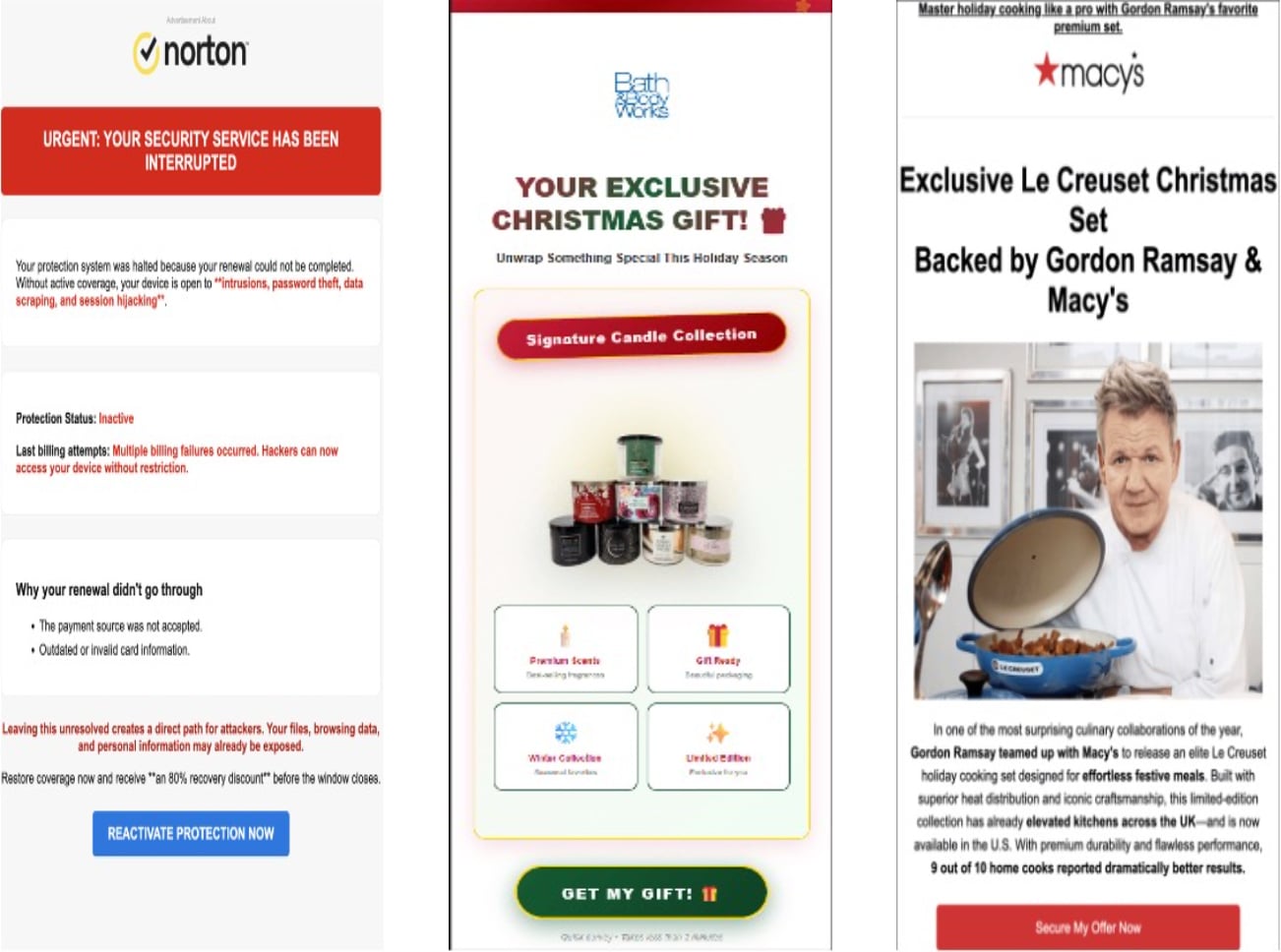
Supply: Infoblox
When a sufferer clicks the phishing electronic mail picture, the system resolves the attacker-controlled reverse DNS identify servers through a DNS supplier.
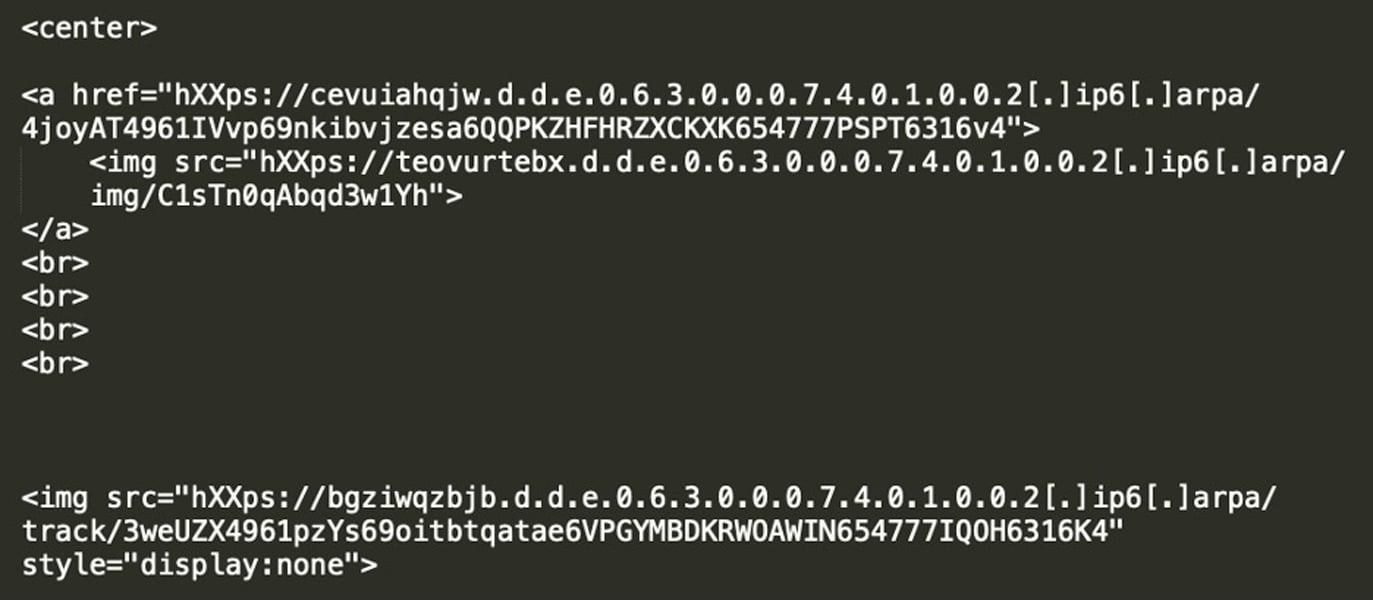
Supply: Infoblox
In some instances, the authoritative identify servers have been hosted by Cloudflare, and the reverse DNS domains resolved to Cloudflare IP addresses, hiding the situation of the backend phishing infrastructure.
After clicking the picture, victims are redirected by means of a site visitors distribution system (TDS) that determines whether or not they’re a sound goal, generally based mostly on system sort, IP handle, internet referers, and different standards. If the customer passes validation, they’re redirected to a phishing web site. In any other case, they’re despatched to a legit web site.
Infoblox says the phishing hyperlinks are short-lived, solely energetic for just a few days. After the hyperlinks expire, they redirect customers to area errors or different legit websites.
The researchers imagine that is finished to make it more durable for safety researchers to investigate and examine the phishing marketing campaign.
Moreover, because the ‘.arpa’ area is reserved for web infrastructure, it doesn’t embody information usually present in registered domains, resembling WHOIS information, area age, or contact info. This makes it more durable for electronic mail gateways and safety instruments to detect malicious domains.
The researchers additionally noticed the phishing marketing campaign utilizing different strategies, resembling hijacking dangling CNAME information and subdomain shadowing, permitting the attackers to push phishing content material by means of subdomains linked to legit organizations.
“We discovered over 100 cases the place the menace actor used hijacked CNAMEs of well-known authorities companies, universities, telecommunication firms, media organizations, and retailers,” defined Infoblox.
By weaponizing trusted reverse DNS options utilized by safety instruments, attackers can generate phishing URLs that bypass conventional detection strategies.
As at all times, one of the best ways to keep away from phishing assaults like these is to keep away from clicking on surprising hyperlinks in emails and as an alternative go to providers straight by means of their official web sites.




