
Google Menace Intelligence Group (GTIG) tracked 90 zero-day vulnerabilities actively exploited all through 2025, virtually half of them in enterprise software program and home equipment.
The determine is a 15% enhance in comparison with 2024, when 78 zero-days had been exploited within the wild, however decrease than the document 100 zero days tracked in 2023.
Zero-day vulnerabilities are safety points in software program merchandise that attackers exploit, often earlier than the seller learns about them and develops a patch. They’re extremely valued by risk actors as a result of they typically allow preliminary entry, distant code execution, or privilege escalation.
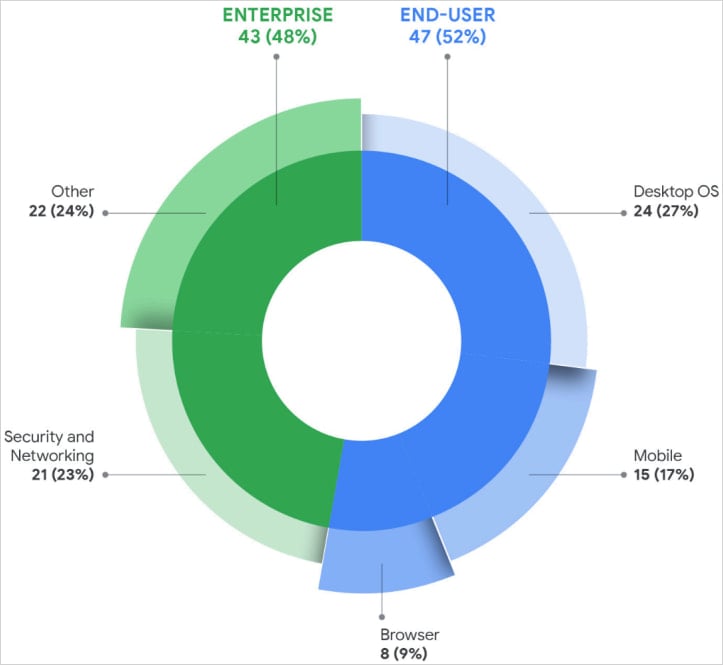
A report from GTIG as we speak notes that of the 90 zero-days tracked as exploited in 2025, 47 of them focused end-user platforms, and 43 focused enterprise merchandise.
The kind of exploited flaws consists of distant code execution, privilege escalation, injection and deserialization flaws, authorization bypasses, and reminiscence corruption (use-after-free) bugs. Google reviews that reminiscence questions of safety accounted for 35% of all exploited zero-day vulnerabilities final yr.
Probably the most focused enterprise programs had been safety home equipment, networking infrastructure, VPNs, and virtualization platforms, as these present privileged community entry and sometimes lack EDR monitoring.
GTIG reviews that bugs in working programs had been probably the most exploited class final yr, with assaults leveraging 24 zero-day vulnerabilities in desktop OSs and 15 in cell platforms.
Zero-day exploits in net browsers dropped to eight, a pointy decline in comparison with earlier years.
Google’s analysts speculate this is likely to be because of elevated safety hardening on this software program class, although it might even be a case of risk actors utilizing extra superior evasion ways and being higher at hiding malicious exercise.
Supply: Google
In response to GTIG researchers, Microsoft was the highest vendor focused with zero days final yr (25), adopted by Google with 11, Apple with eight, and Cisco and Fortinet with 4 every, and Ivanti and VMware with three every.
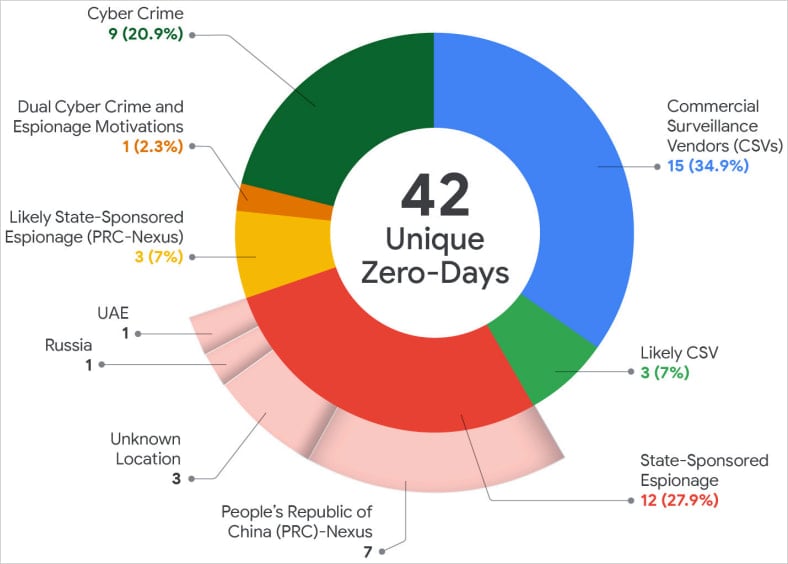
For the primary time since Google began monitoring zero-day exploitation, business spyware and adware distributors had been the most important customers of undocumented flaws, surpassing state-sponsored espionage teams, which can even be deploying more practical hiding methods.
“This continues to mirror a development we started to watch during the last a number of years–a rising proportion of zero-day exploitation is carried out by CSVs and/or their prospects, demonstrating a sluggish however positive motion within the panorama,” reads the GTIG report.
Supply: Google
Google researchers say that amongst state-sponsored actors, China-linked espionage teams stay probably the most energetic, with 10 zero-days exploited in 2025. The assaults focused primarily edge gadgets, safety home equipment, and networking tools for long-term persistent entry.
One other notable development noticed final yr was the rise in zero-day exploitation by financially motivated actors (ransomware, knowledge extortion), who accounted for 9 of the issues.
GTIG believes that the usage of AI instruments will assist automate vulnerability discovery and speed up exploit improvement, so exploitation of zero-day flaws in 2026 is anticipated to stay excessive.
The Brickstorm marketing campaign is highlighted within the report for instance of how hackers are shifting their focus from supply code theft to discovering flaws in future software program merchandise.
To detect and include zero-day exploitation, Google recommends lowering assault surfaces and privilege publicity, constantly monitoring programs for anomalous conduct, and sustaining fast patching and incident-response processes.



