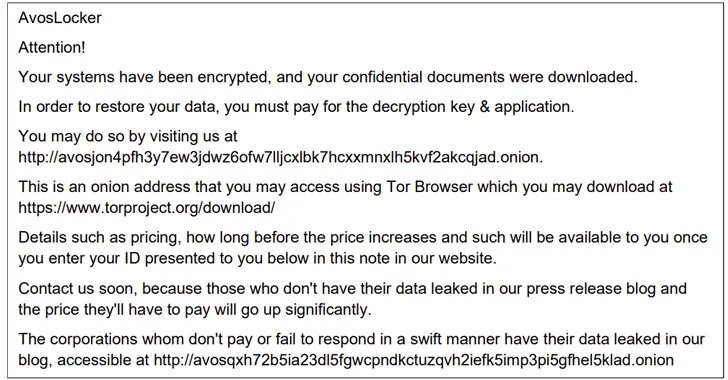
The AvosLocker ransomware gang has been linked to assaults towards important infrastructure sectors within the U.S., with a few of them detected as just lately as Might 2023.
That is in response to a brand new joint cybersecurity advisory launched by the U.S. Cybersecurity and Infrastructure Safety Company (CISA) and the Federal Bureau of Investigation (FBI) detailing the ransomware-as-a-service (RaaS) operation’s ways, methods, and procedures (TTPs).
“AvosLocker associates compromise organizations’ networks through the use of professional software program and open-source distant system administration instruments,” the businesses stated. “AvosLocker associates then use exfiltration-based knowledge extortion ways with threats of leaking and/or publishing stolen knowledge.”
The ransomware pressure first emerged on the scene in mid-2021, and has since leveraged subtle methods to disable antivirus safety as a detection evasion measure. It impacts Home windows, Linux, and VMware ESXi environments.
A key hallmark of AvosLocker assaults is the reliance on open-source instruments and living-off-the-land (LotL) ways, leaving no traces that would result in attribution. Additionally used are professional utilities like FileZilla and Rclone for knowledge exfiltration in addition to tunneling instruments reminiscent of Chisel and Ligolo.
Command-and-control (C2) is completed by the use of Cobalt Strike and Sliver, whereas Lazagne and Mimikatz are used for credential theft. The assaults additionally make use of customized PowerShell and Home windows Batch scripts for lateral motion, privilege escalation, and disarming safety software program.
“AvosLocker associates have uploaded and used customized internet shells to allow community entry,” the businesses famous. One other new part is an executable named NetMonitor.exe that masquerades as a community monitoring software however truly capabilities as a reverse proxy to permit the risk actors to hook up with the host from exterior the sufferer’s community.
CISA and FBI are recommending important infrastructure organizations to implement needed mitigations to scale back the chance and affect of AvosLocker ransomware and different ransomware incidents.
This contains adopting utility controls, limiting using RDP and different distant desktop providers, proscribing PowerShell use, requiring phishing-resistant multi-factor authentication, segmenting networks, preserving all programs up-to-date, and sustaining periodic offline backups.
The event comes as Mozilla warned of ransomware assaults leveraging malvertising campaigns that trick customers into putting in trojanized variations of Thunderbird, in the end resulting in the deployment of file-encrypting malware and commodity malware households reminiscent of IcedID.
Ransomware assaults in 2023 have witnessed a significant surge, whilst risk actors are transferring swiftly to deploy ransomware inside at some point of preliminary entry in additional than 50% of engagements, in response to Secureworks, dropping from the earlier median dwell time of 4.5 days in 2022.
What’s extra, in additional than 10 p.c of incidents, ransomware was deployed inside 5 hours.
“The motive force for the discount in median dwell time is probably going because of the cybercriminals’ need for a decrease likelihood of detection,” Don Smith, vice chairman of risk intelligence at Secureworks Counter Risk Unit, stated.
“Consequently, risk actors are specializing in easier and faster to implement operations, relatively than massive, multi-site enterprise-wide encryption occasions which might be considerably extra complicated. However the threat from these assaults continues to be excessive.”
Exploitation of public dealing with purposes, stolen credentials, off-the-shelf malware, and exterior distant providers have emerged because the three largest preliminary entry vectors for ransomware assaults.
Per newest steerage from CISA, distant desktop protocol (RDP), file switch protocol (FTP), TELNET, Server Message Block (SMB), and Digital Community Computing (VNC) are among the misconfigurations and weaknesses which might be recognized to have been generally weaponized in ransomware campaigns.
To rub salt into the wound, the RaaS mannequin and the prepared availability of leaked ransomware code have lowered the barrier to entry for even novice criminals, making it a profitable avenue to make illicit income.
“Whereas we nonetheless see acquainted names as essentially the most energetic risk actors, the emergence of a number of new and really energetic risk teams is fuelling a major rise in sufferer and knowledge leaks,” Smith added. “Regardless of excessive profile takedowns and sanctions, cybercriminals are masters of adaptation, and so the risk continues to assemble tempo.”
Microsoft, in its annual Digital Protection Report, stated 70% of organizations encountering human-operated ransomware had fewer than 500 staff, and that 80 to 90 p.c of all compromises originate from unmanaged units.
Telemetry knowledge gathered by the corporate reveals that human-operated ransomware assaults have gone up greater than 200 p.c since September 2022. Magniber, LockBit, Hive, and BlackCat comprised nearly 65 p.c of all ransomware encounters.
On prime of that, roughly 16 p.c of latest profitable human-operated ransomware assaults concerned each encryption and exfiltration, whereas a 13 p.c used exfiltration solely.
“Ransomware operators are additionally more and more exploiting vulnerabilities in much less widespread software program, making it tougher to foretell and defend towards their assaults,” the tech large stated. “This reinforces the significance of a holistic safety strategy.”
Redmond stated it additionally noticed a “sharp improve” in using distant encryption throughout human-operated ransomware assaults, accounting for 60 p.c on common over the previous 12 months.
“As an alternative of deploying malicious recordsdata on the sufferer machine, encryption is finished remotely, with the system course of performing the encryption, which renders process-based remediation ineffective,” Microsoft defined. “This can be a signal of attackers evolving to additional reduce their footprint.”