Authored by Dexter Shin
McAfee’s Cellular Analysis Crew found a brand new and lively Android malware marketing campaign focusing on Bengali-speaking customers, primarily Bangladeshi folks residing overseas. The app poses as fashionable monetary companies like TapTap Ship and AlimaPay. It’s distributed by means of phishing websites and FacebookFacekbook pages, and the app steals customers’ private and monetary data. The marketing campaign stays extremely lively, with the command-and-control (C2) server operational and related to a number of evolving domains. Whereas the assault methods are usually not new, the marketing campaign’s cultural focusing on and sustained exercise replicate how cybercriminals proceed to adapt their methods to succeed in particular communities. McAfee Cellular Safety already detects this risk as Android/FakeApp. For extra data, go to McAfee Cellular Safety.
Bangladeshi folks residing overseas, notably in international locations similar to Saudi Arabia, the UAE, Malaysia, and the UK, rely closely on cell cash companies to ship remittances and confirm their identities for varied functions. Providers like bKash, TapTap Ship, and AlimaPay are extensively used and trusted inside this group.
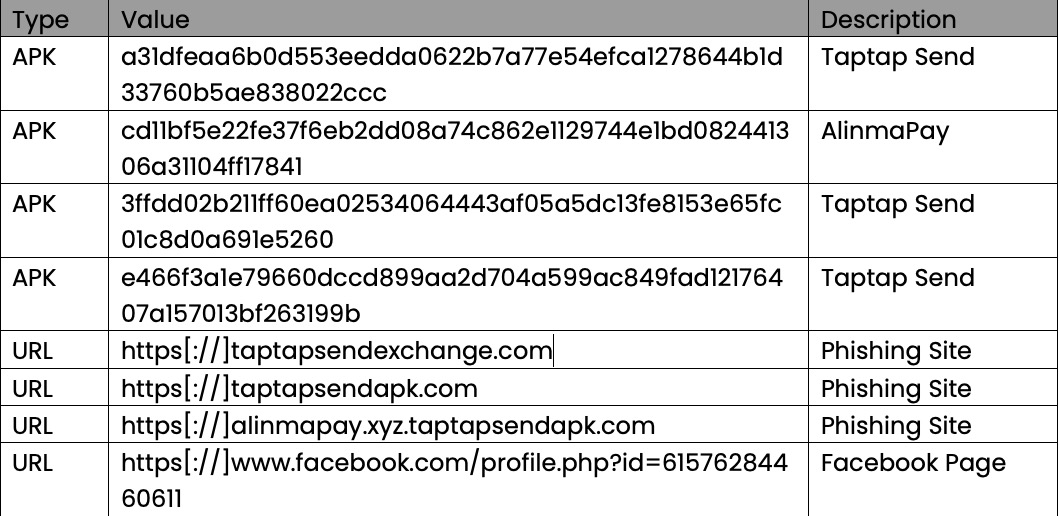
In 2024, annual remittances despatched to Bangladesh reached practically $26.6 billion, rating sixth globally and third in South Asia. This huge movement of cross-border funds highlights the financial significance and digital engagement of the Bangladeshi diaspora.
Determine 1. High Recipients of Remittances in 2024 (Supply: World Financial institution)
As extra folks use cell monetary apps, cybercriminals are discovering new methods to trick them utilizing pretend apps and phishing web sites. Many customers belief apps shared by pals or household, and a few might not know methods to spot scams. This makes them straightforward targets for attackers.
In Might 2025, McAfee’s Cellular Analysis Crew recognized a malware marketing campaign designed to take advantage of these situations. The pretend Android app impersonates well-known cash switch companies and steals private data such because the consumer’s title, e-mail deal with, cellphone quantity, and picture ID (similar to a passport or nationwide ID card). It additionally makes an attempt to gather monetary information like card numbers by means of pretend in-app pages. Furthermore, the C2 server’s storage is publicly uncovered, that means that the stolen information will be accessed by anybody, which considerably will increase the chance of abuse.
Technical Findings
Distribution Strategies
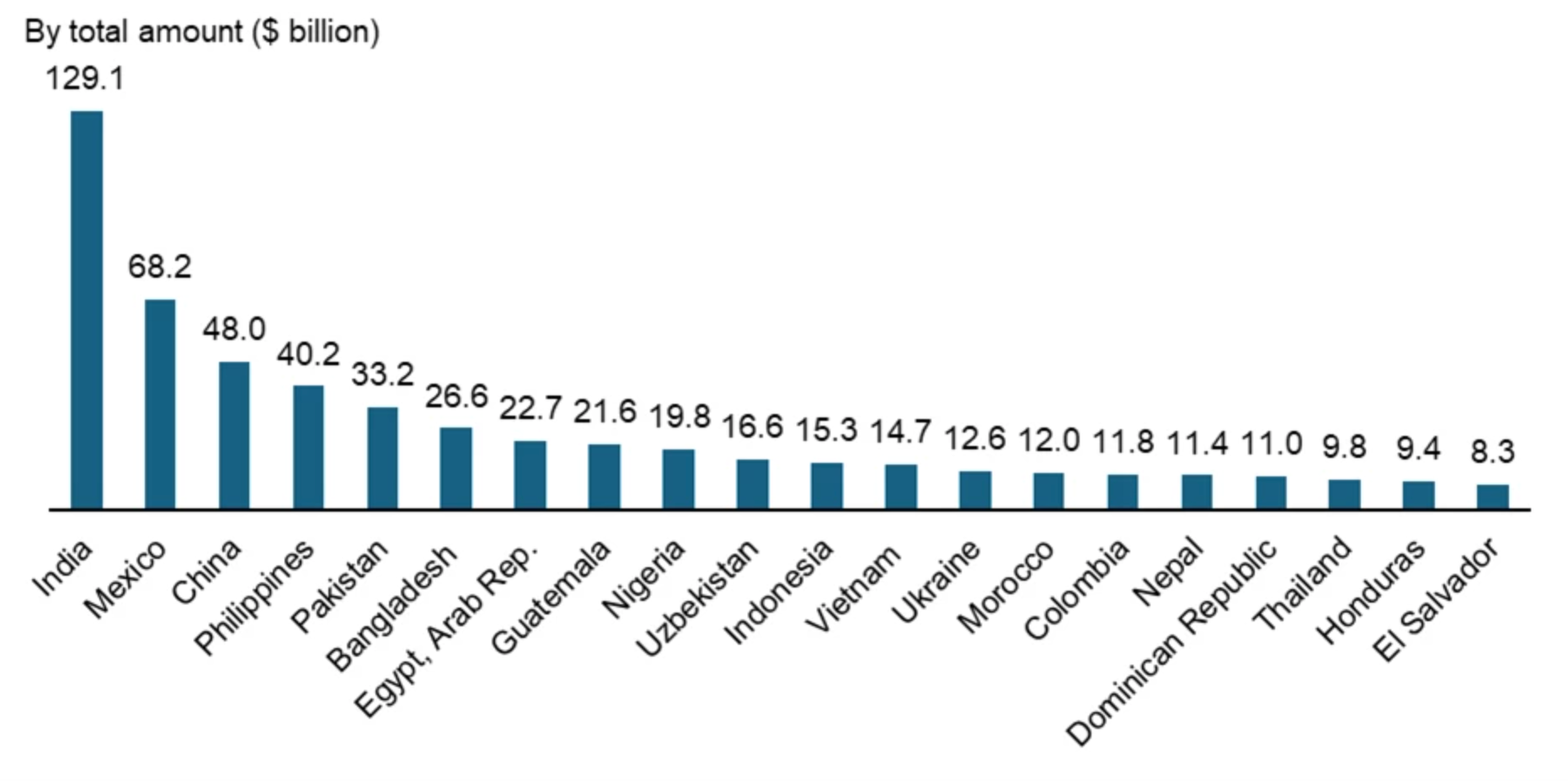
Over the previous few weeks, these pretend apps have continued to look, suggesting an lively and sustained marketing campaign focusing on Bengali-speaking customers. These apps are primarily distributed by means of phishing web sites that mimic trusted remittance companies, usually shared through pretend Fb pages.
Determine 2. Screenshot of a phishing web site
The web page is written solely in Bengali, mimicking a respectable remittance service generally utilized by Bangladeshi expatriates. Beneath is a translated excerpt of the primary message proven on the touchdown web page:
Bengali (authentic):
আসসালামু আলাইকুম।
প্রবাসী ভাইদের জন্য সুখবর। যারা কাজের পাশাপাশি বাড়তি আয় করতে চান, তারা বিকাশ, ফ্ল্যাশলোড ব্যবসা করতে পারেন। সম্পূর্ণ বৈধ উপায়ে। আপনার হাতের মধ্যে রয়েছে মোবাইলের মাধ্যমে। মোবাইল ব্যাংকিং করুন খুব সহজেই।
English (translation):
Peace be upon you.
Excellent news for our brothers residing overseas. When you’re seeking to earn additional revenue alongside together with your job, you are able to do enterprise with bKash or FlashLoad in a very authorized means. Every little thing is inside your attain by means of cell. Cellular banking may be very straightforward.
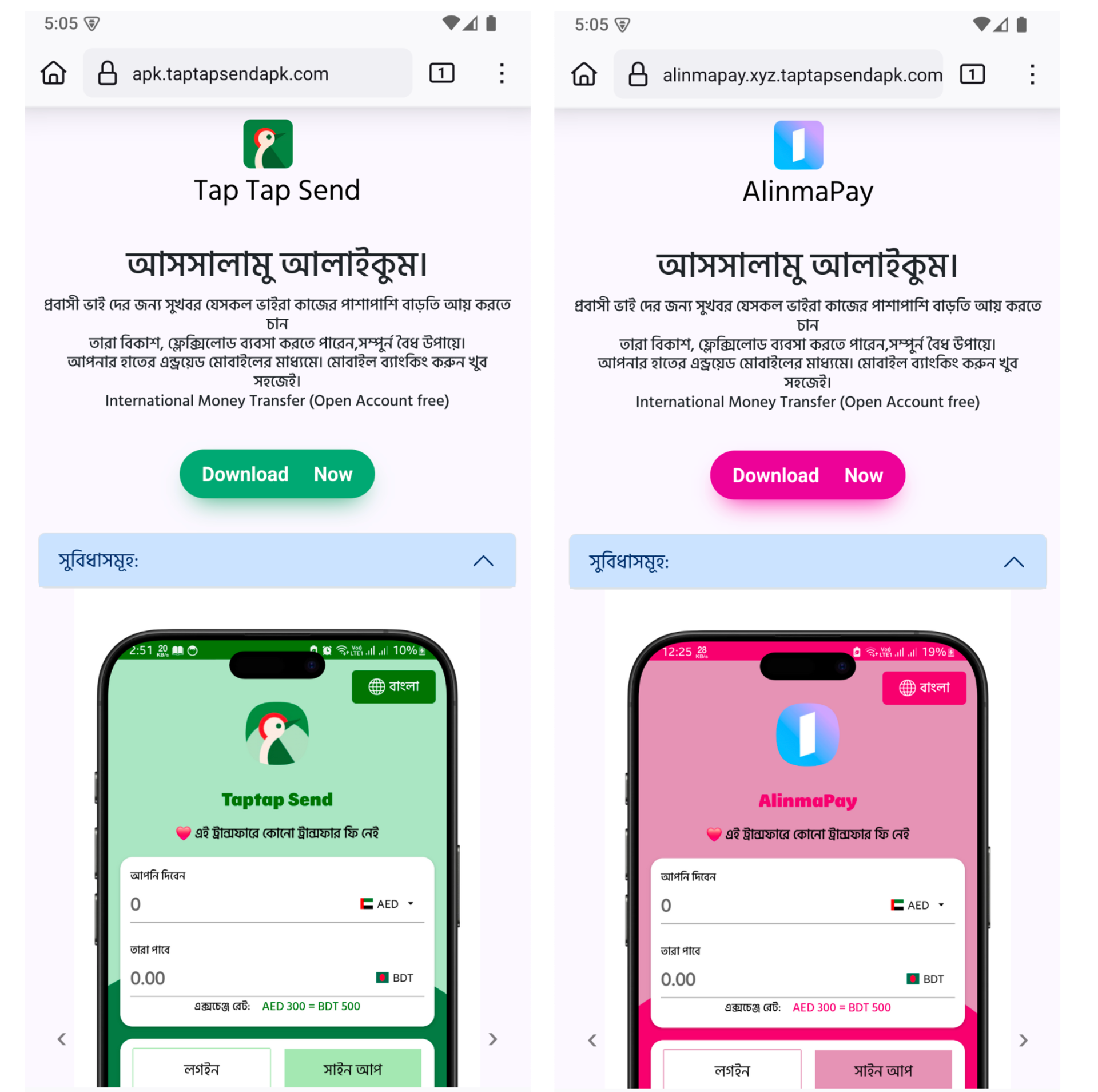
Along with phishing web sites, the attackers additionally created pretend Fb pages that intently resemble respectable remittance companies. These pages usually reuse official logos, promotional photos, and even movies taken from actual monetary platforms to look reliable. Nevertheless, the location hyperlinks on these pages level to phishing web sites internet hosting the malicious app.
Determine 3. Faux Fb web page mimicking a respectable remittance service
Faux App Evaluation
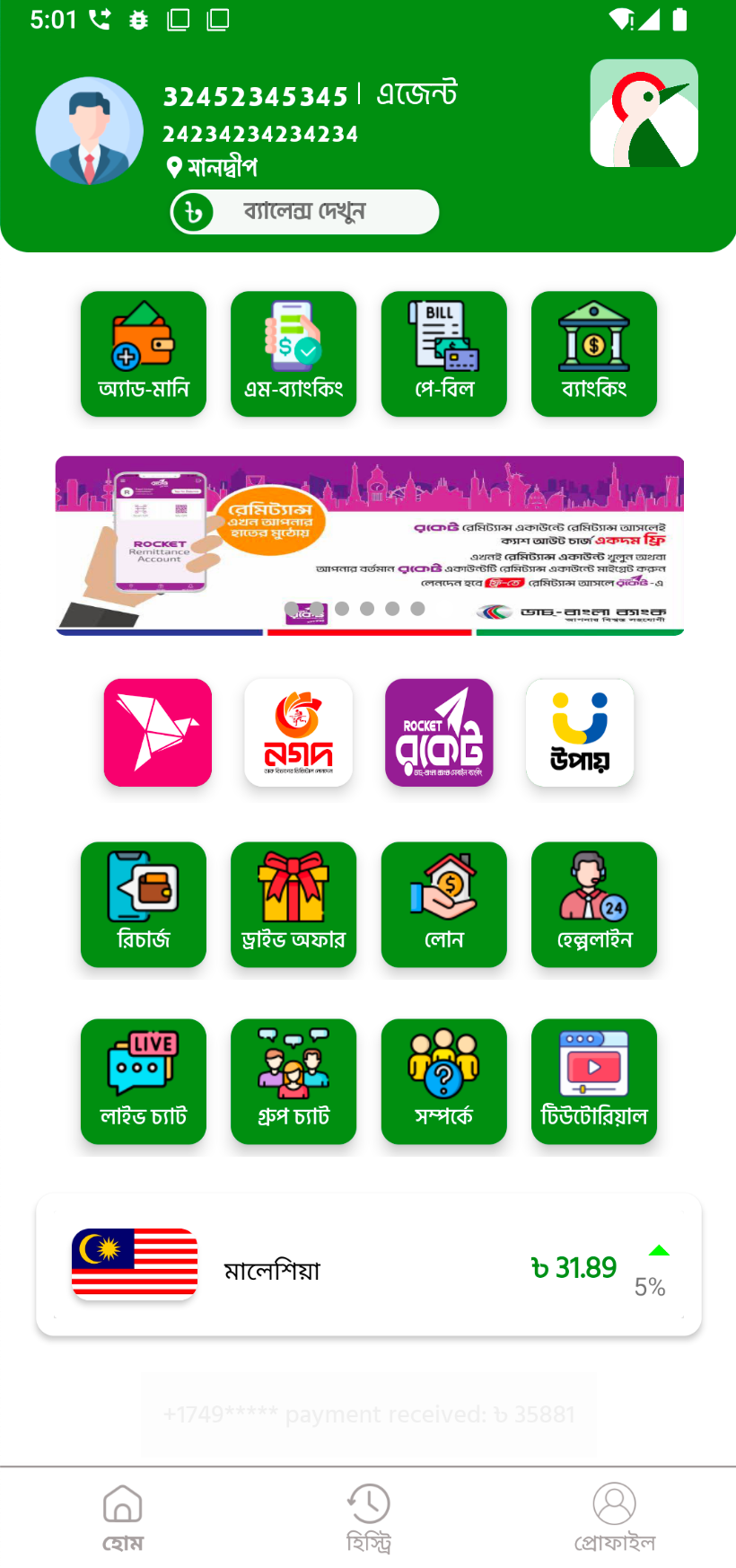
As soon as put in, the pretend app instantly presents an interface that intently resembles a respectable remittance utility. It helps each Bengali and English language choices and exhibits realistic-looking alternate charges.
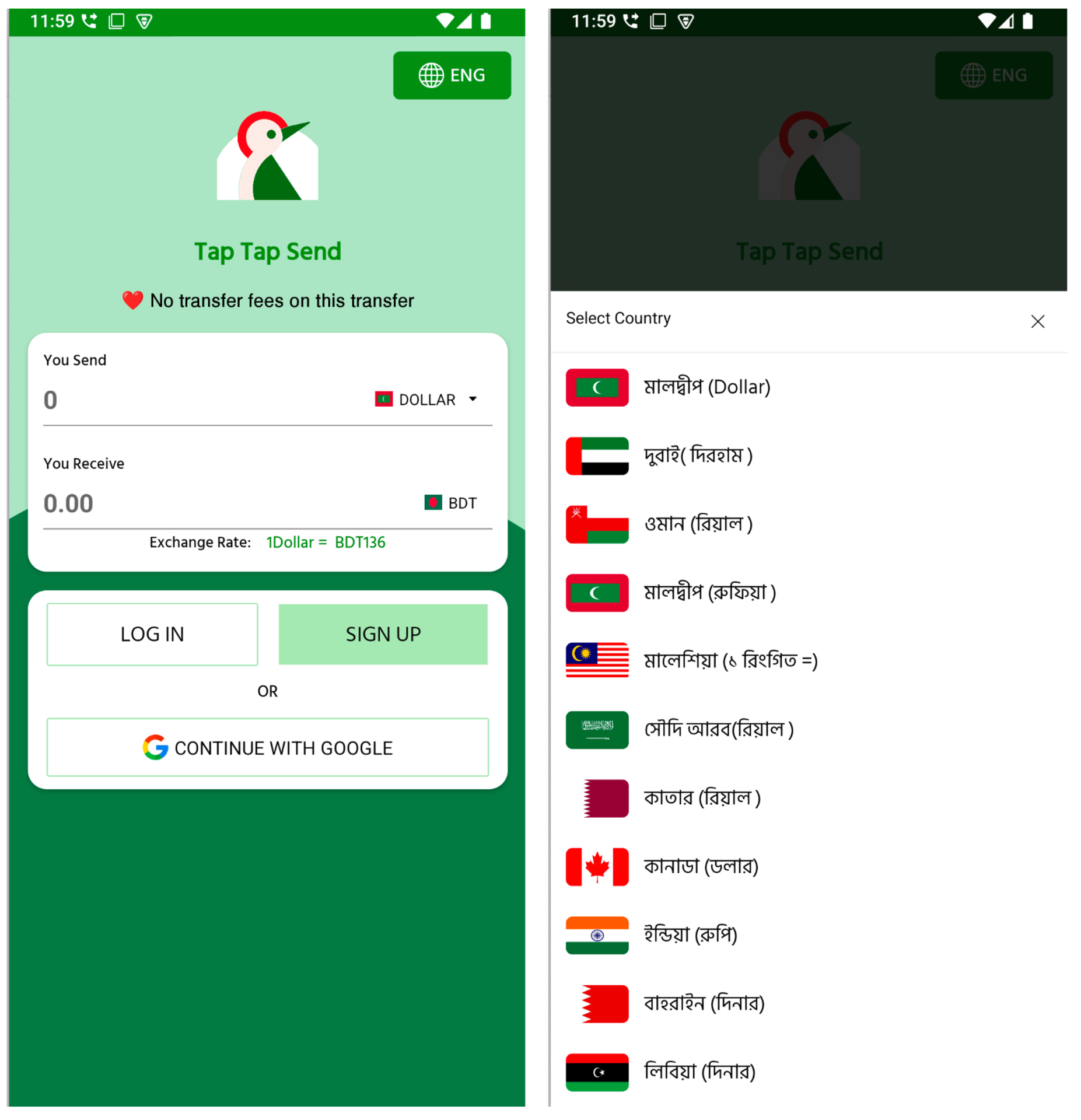
Determine 4. Preliminary UI of the pretend TapTap Ship app
Customers can choose from a listing of nations with massive Bangladeshi expatriate populations, similar to Maldives, Dubai, Oman, Saudi Arabia, Malaysia, Canada, and India, to simulate cash transfers to Bangladeshi Taka (BDT). These particulars are seemingly included to ascertain belief and make the app seem useful. Nevertheless, these screens function bait to encourage customers to proceed with account creation and enter private data. As customers proceed by means of the registration movement, the app requests more and more delicate information in a number of levels. First, it requests the consumer’s e-mail deal with and full title. Then, it prompts them to pick out their nation of residence and supply a sound cell quantity. Subsequent, customers are requested to decide on an account kind, both “Private” or “Agent”, a distinction generally seen in actual remittance platforms.
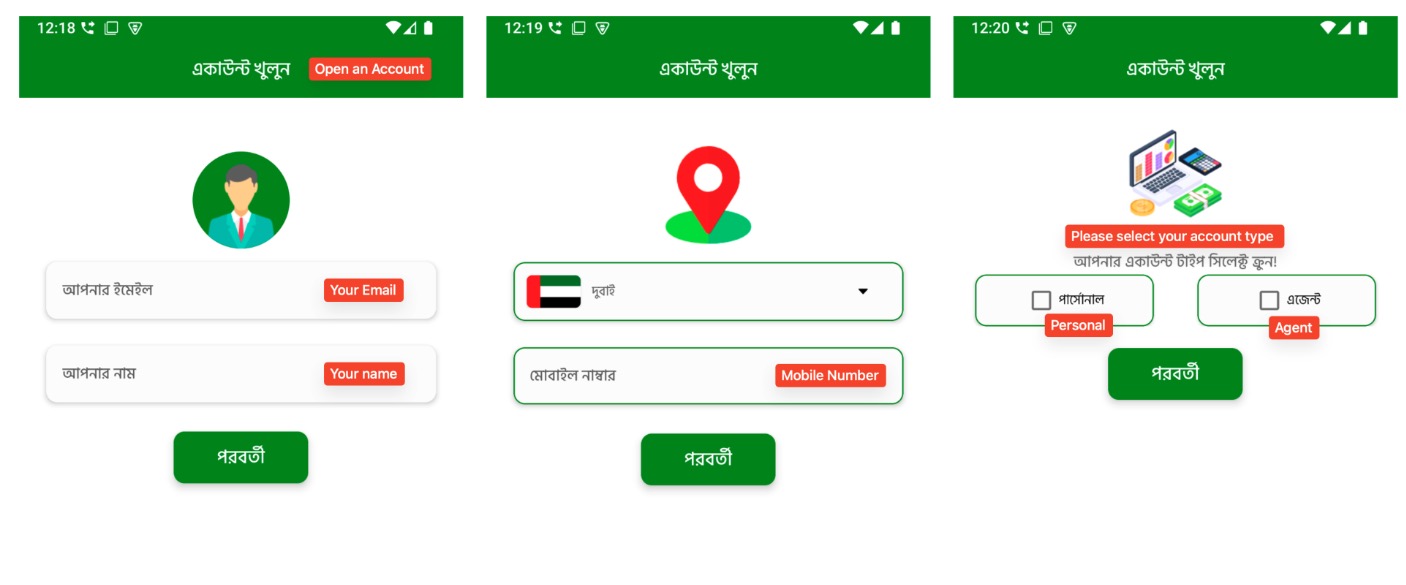
Determine 5. Multi-step registration movement (1)
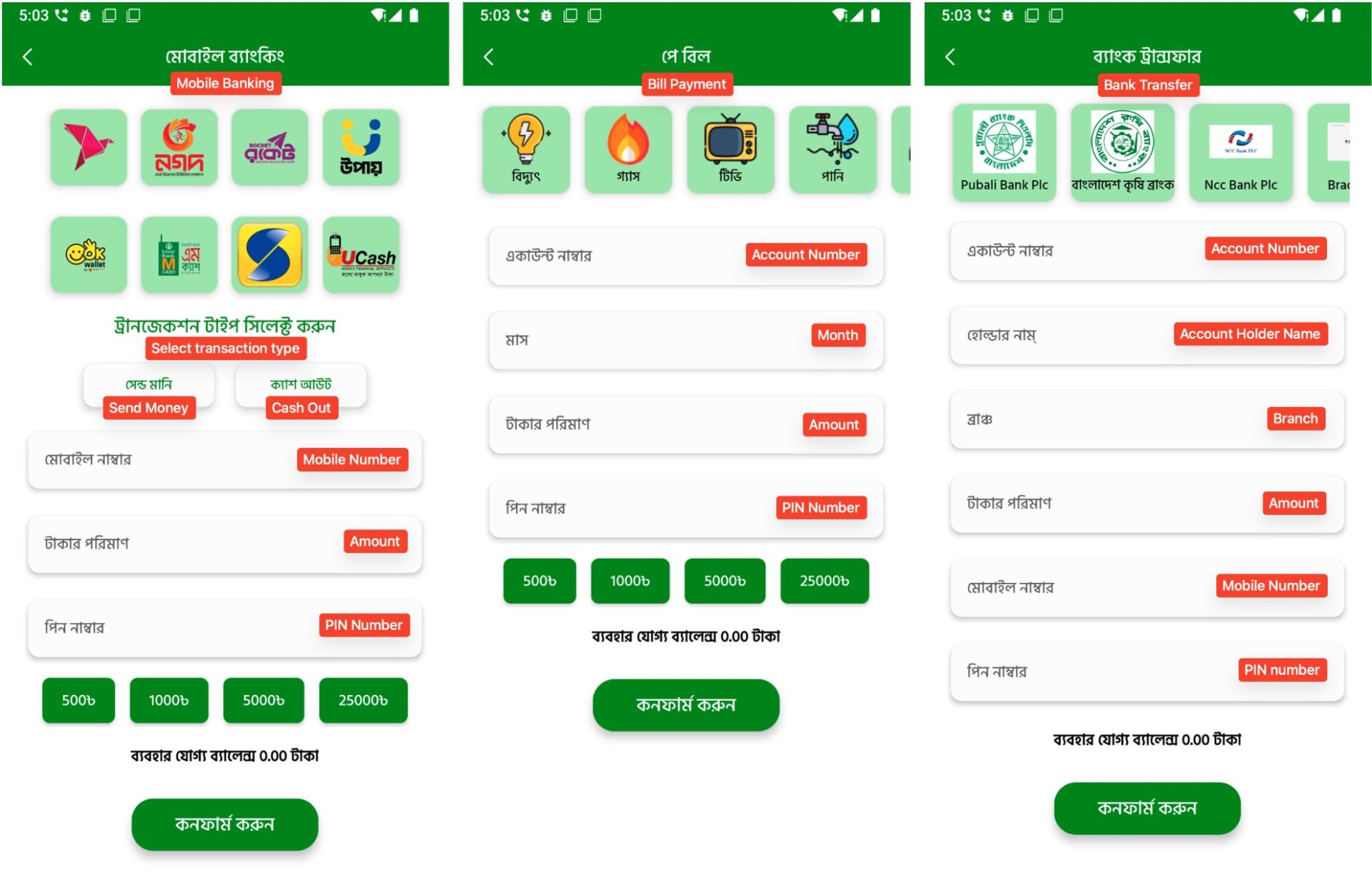
Following this, the app reaches its most delicate stage: it asks the consumer to take and add a photograph of an official ID, similar to a passport, nationwide ID (NID), or an e-commerce verification picture. This request is made within the native language and framed as a requirement to finish account setup. After importing the ID, customers are then requested to create a login password and a 5-digit PIN, similar to actual monetary apps. This step makes the app really feel extra reliable and safe, however the collected credentials might later be utilized in credential stuffing assaults. All of this data is distributed to the C2 server and saved, making it accessible for future fraud or identification theft.
Determine 6. Multi-step registration movement (2)
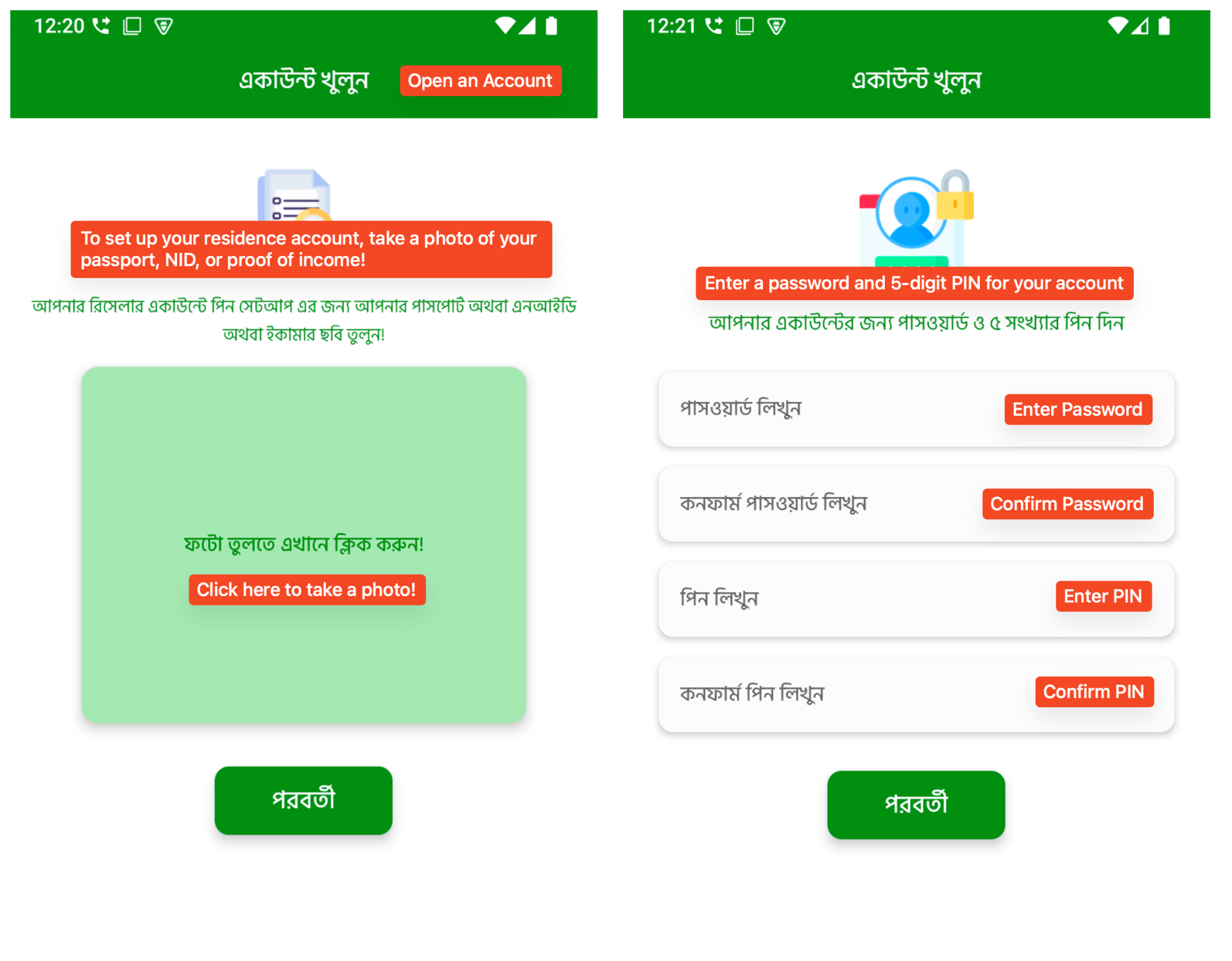
After finishing the registration course of, customers are taken to a totally designed dashboard. The interface mimics an actual monetary or remittance app, full with icons for cash switch, invoice cost, cell banking, and even buyer help options.
Determine 7. The pretend TapTap Ship app’s major dashboard
The malware contains a number of pretend transaction interfaces. These screens simulate cell cash transfers, invoice funds, and financial institution transfers utilizing logos from actual companies. Though no precise transaction is carried out, the app collects all entered data similar to cellphone numbers, account particulars, PINs, and cost quantities. This information is then transmitted to the C2 server.
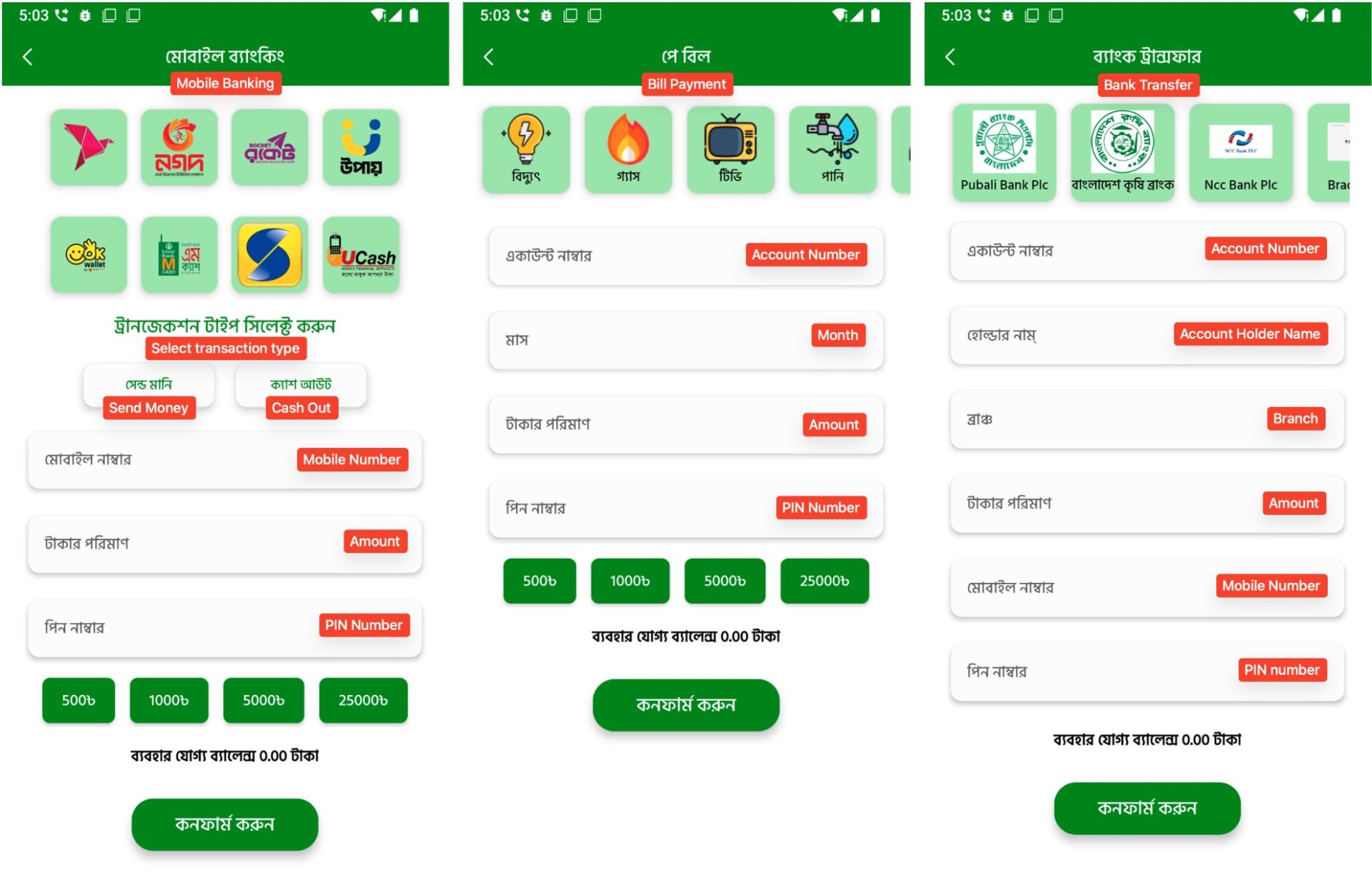
Determine 8. Faux transaction screens that imitate actual monetary companies
C2 Server and Knowledge Exfiltration
All the data collected by the pretend app, together with credentials, contact particulars, and picture IDs, is saved on the C2 server. Nevertheless, the server lacks primary safety settings. Listing itemizing is enabled, which suggests anybody can entry the uploaded information with out authentication. Throughout our investigation, we discovered that one of many C2 domains contained 297 picture information. These information look like picture IDs uploaded by customers throughout the registration course of.
Determine 9. Publicly accessible listing itemizing on the C2 server
These ID photos embody extremely delicate private data and are publicly accessible. If downloaded or misused, they might pose a critical privateness and identification theft danger.
Determine 10. Instance of a delicate picture ID picture uploaded throughout app registration

Determine 11. Geographic distribution of contaminated gadgets
As anticipated, telemetry exhibits exercise in international locations with massive Bangladeshi populations overseas, similar to Saudi Arabia, Malaysia, Bangladesh, and the United Arab Emirates. This aligns with the app’s focusing on of Bengali-speaking customers by means of culturally acquainted language and visuals. The marketing campaign stays lively, with new phishing domains and variants persevering with to look. Given the evolving nature of this risk and its use of trusted platforms like Fb to distribute malicious content material, customers ought to keep cautious when encountering monetary service promotions by means of social media or unknown web sites. We advocate downloading apps solely from trusted sources similar to Google Play, avoiding hyperlinks shared through social media, and being additional cautious when requested to supply private or banking data. Utilizing cell safety software program that may detect and block these threats can be strongly suggested.
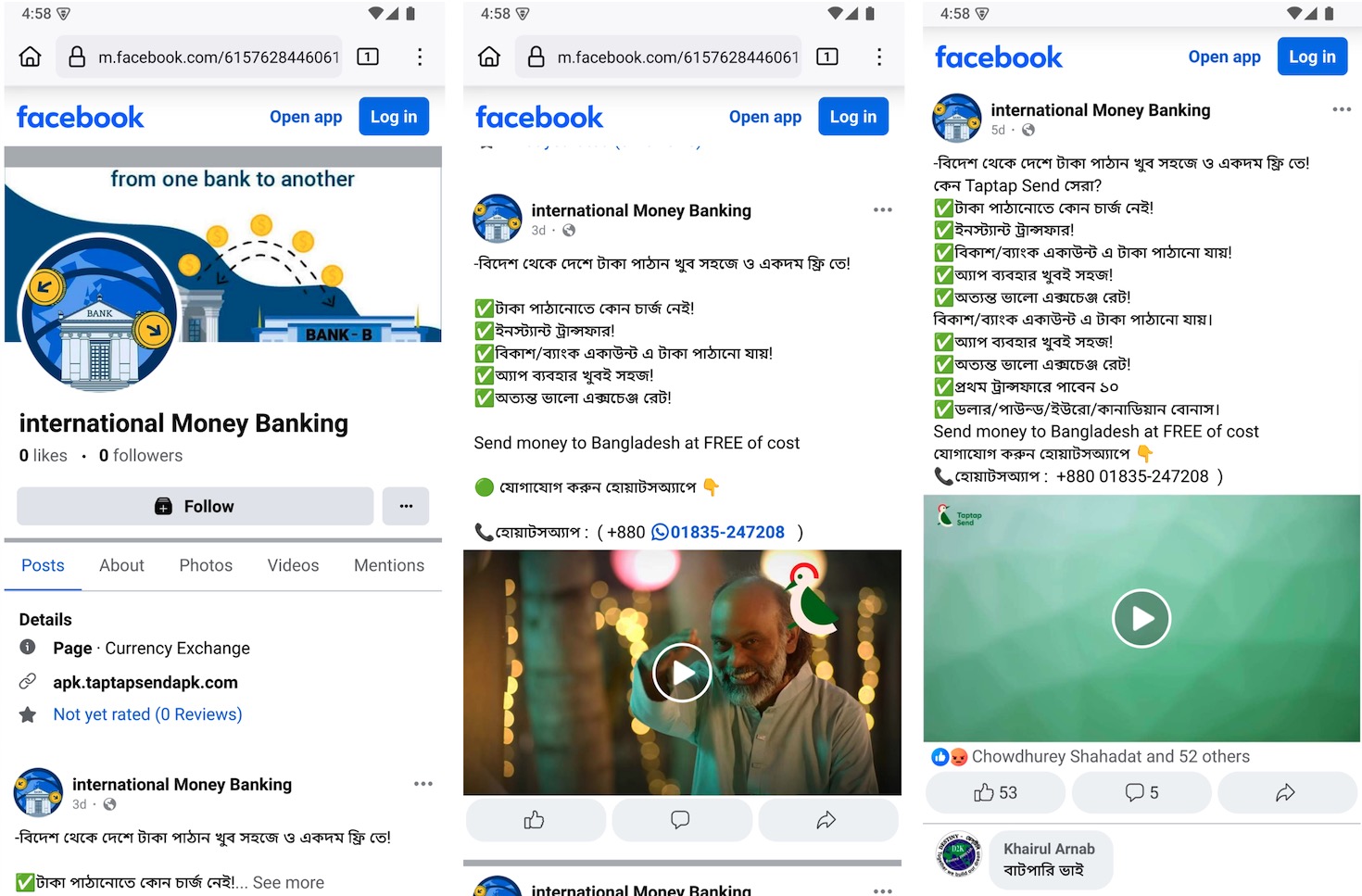
Indicators of Compromise (IOCs)