In 2014, a knowledge breach uncovered data of three billion Yahoo customers. In 2016, Sony Photos workers noticed delicate non-public data leaked together with 1000’s of firm paperwork. What do these two assaults have in frequent? Each began with a phishing e-mail.
E-mail threats are nonetheless some of the frequent methods attackers should entry delicate data or set up malware. Whereas most identified instances of phishing goal nameless customers, the attackers may also use emails containing faux hyperlinks or recordsdata to focus on particular people who maintain delicate data. And, as ESET researchers level out, in 2022, this sort of risk noticed a year-over-year improve of just about 30%. And as AI language fashions make it simpler to compose emails, likelihood is that these numbers are nearly to go up much more!
Phishing assaults are a type of social engineering that makes us react with a way of urgency and curiosity. Whereas we will all be victims of one of these assault, we will additionally be taught to keep away from it. Let’s check out some real-life examples of the most typical phishing used to trick us.
1. “Your session expired. Click on right here to sign up once more.”
Among the most typical phishing traces and techniques simply briefly inform you that you simply’ve been logged out of an account and it pushes you to fill in your credentials. Clicking the hyperlink will take you to a web site trying similar to the actual one. The distinction, nevertheless, is that inputting your credentials will ship them straight away to the attackers, who will then use them to entry your data. In some cases, they may even log in for you and alter the password to keep away from supplying you with entry.
This method depends on the customers’ behavior of responding to such messages routinely with out interested by the content material or with out checking for the everyday indicators of a phishing e-mail/message. (Study these indicators right here).
For instance, final yr, GitHub Safety warned about emails impersonating the favored software program improvement CI/CD platform CircleCI. The impersonators would ship an alert with “session expired” and request a brand new login utilizing GitHub credentials. “We’ve seen some uncommon exercise in your account. Please confirm.”
With this trick, scammers attempt to whip up a way of urgency. Who wouldn’t need to keep away from the sudden lack of an account, proper? Often, these emails impersonate messages from official providers equivalent to Amazon, PayPal, and so forth.
For instance, in late 2018, The US Federal Commerce Fee (FTC) issued a warning about phishing emails impersonating the streaming large Netflix. These emails claimed that an account was placed on maintain as a consequence of one thing flawed with cost particulars, asking individuals to replace their billing data utilizing an embedded hyperlink, which was, after all, malicious and used to acquire login credentials.
Equally, Apple clients had been focused in 2016 when scammers tried to steal their private data with phishing emails claiming that customers wanted to reconfirm their account particulars as a result of “a virus” had been present in Apple’s iTunes database.
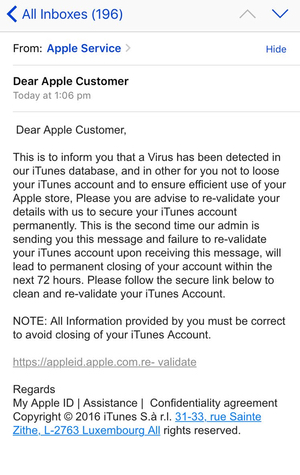
Spammed-out e-mail
2. “I would like you to make an pressing cost”
Impersonating company e-mail accounts has been a long-time champion amongst spearphishing campaigns that don’t goal nameless individuals however as a substitute go after one particular particular person or a bunch of workers in a particular firm.
Earlier than sending these fraudulent emails, scammers be taught as a lot as doable about company constructions, visuals, language, and so forth. of a enterprise, to make the phishing e-mail nearly indistinguishable from a real one.
A few of these emails particularly goal workers who’re answerable for money dealing with and monetary issues. They faux to be the CEO or a special superior approved to order a financial switch and ask the sufferer to ship funds to a particular account, supposedly the CEO’s, or perhaps the corporate’s.
In 2018, CEO impersonation was used to steal over CA$100,000 from the Canadian metropolis of Ottawa. Impersonating a request from town supervisor, town treasurer obtained a faux e-mail to switch the quantity that ended up within the pockets of fraudsters.
Grasping scammers additionally tried to deceive the treasurer for a second time, however when receiving one other e-mail, town supervisor was there to personally witness it. After asking whether or not the request was official, the rip-off was revealed, and the crooks had been caught in a lie.
3. “Expensive applicant…”
These phishing emails or messages depend on faux job provides because the lure. They might trick potential victims into clicking on a phishing hyperlink or opening malicious recordsdata despatched together with an e-mail message, asking the sufferer, for instance, to create an account and enter their private particulars as a method to use for the job.
As an example, the Lazarus risk group has run quite a few such campaigns, equivalent to Operation DreamJob, found by ESET researchers only in the near past, which lured its victims with faux job provides.
These scams additionally exist on widespread job promoting boards, so at all times attempt to confirm whether or not the headhunter who contacted you or the job give you see is official.
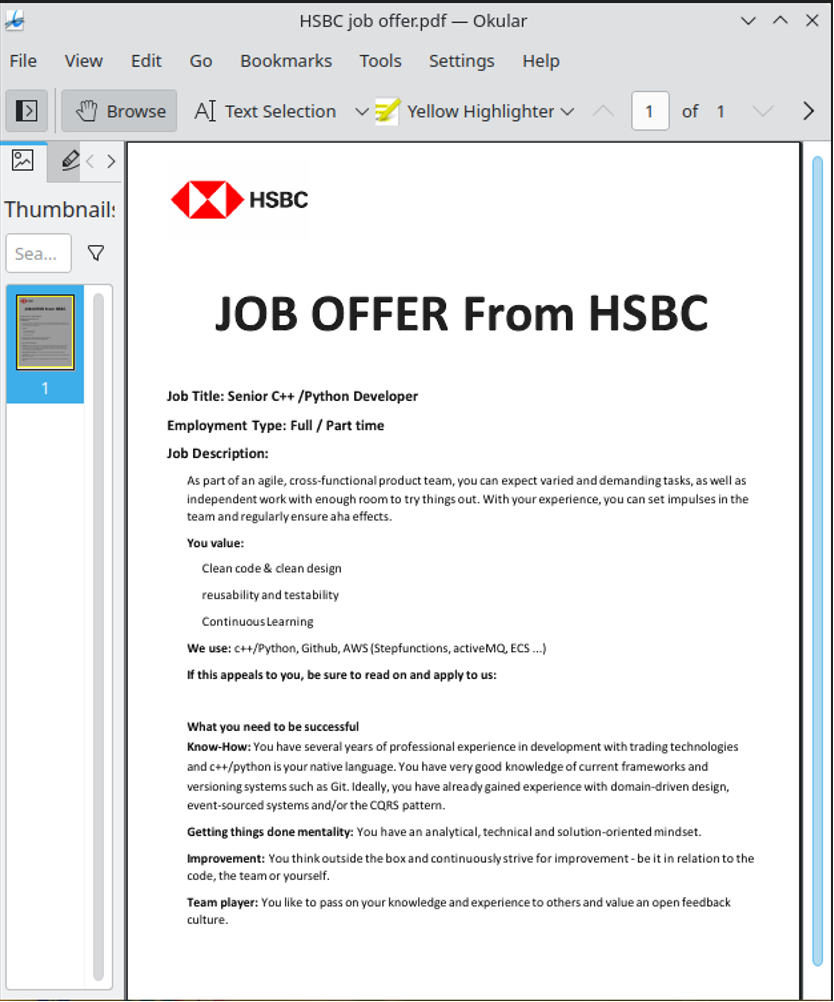
The most recent marketing campaign focused Linux customers with a ZIP file that delivers a faux HSBC job supply as a decoy.
4. “Because of the present scenario… “
Phishing can be on the rise in occasions of huge occasions – be it a sports activities occasion or a humanitarian disaster.
For instance, initially of 2023, the risk group Fancy Bear ran an e-mail marketing campaign associated to the struggle in Ukraine. The emails had been carrying a malicious RTF file known as “Nuclear Terrorism A Very Actual Risk.” As soon as open, it will not solely compromise that laptop, but it surely was additionally a weblog by the respected suppose tank Atlantic Council stating that the probability of Putin utilizing nuclear weapons within the struggle in Ukraine may be very low – the precise reverse of the declare within the doc identify and that prompted the victims to open it.
5. “Merry Christmas!”
Scams throughout holidays usually abuse the buying spree with emails impersonating messages from official distributors. Emails comprise “too-good-to-be-true” provides or create a false sense of urgency to catch the last-minute deal!
One other method for scammers is to ship emails with malicious recordsdata associated to holidays, together with Christmas playing cards, present vouchers, and so forth.
6. “We’re unable to course of your tax return”
Only some issues on this world are sure—demise, taxes, and phishing emails throughout tax season. As a result of individuals are submitting their taxes, it isn’t shocking for them to obtain some e-mail from a tax company.
Scammers abuse this case by sending phishing emails with faux tax company messages. Often, they declare that some data is lacking and request further private or monetary particulars.
Different emails supply a refund whereas asking for bank card data.
7. No response required
Some phishing emails have little to no content material, luring you to open an connected file to be taught extra concerning the matter.
For instance, ESET Analysis uncovered the malicious marketing campaign concentrating on company networks in Spanish-speaking nations utilizing quick emails with PDF attachments in 2021.
The topic of the e-mail could be so simple as on this case: “Companies Assertion Dublin”; there was no message other than a signature and a cell phone contact in Venezuela.
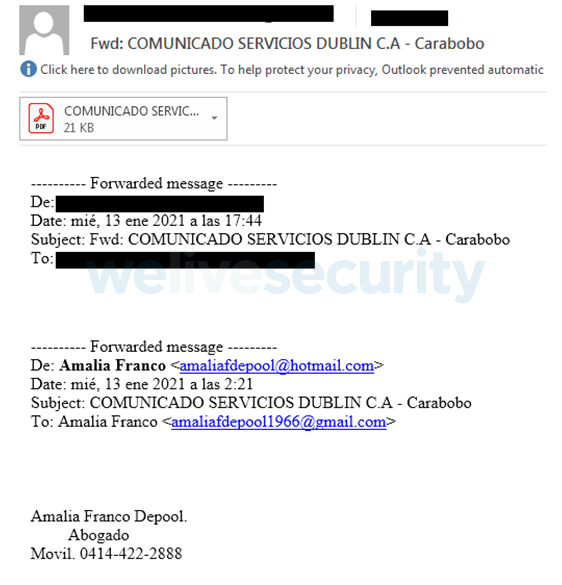
In the meantime, the attachment is an easy PDF file with no further informational worth, however contained a hyperlink redirecting victims to cloud storage providers, from which the malware may very well be downloaded.
shield towards phishing emails
- Rigorously learn the e-mail. Don’t click on on something routinely.
- Verify whether or not the e-mail tackle matches the actual area.
- Be cautions with sudden sudden emails from a financial institution, vendor, or some other group.
- Verify the purple flag, equivalent to pressing or threatening emails requiring rapid response or requests for credentials, private, and monetary data. Quite a few grammar errors, spelling errors, and typos are additionally a purple flag.
- Evaluate the connected URL with the respective area of a official firm or group. When you spot something suspicious, don’t click on on it.
- Pay attention to provides which can be too good to be true and sudden presents.
- Don’t ship cash unexpectedly. In case your superior abruptly asks for such a switch, method them instantly.
- Set up a cybersecurity product with integrated anti-phishing instruments.
Phishing emails are a prevalent risk, and even IT professionals could fall for this rip-off. Fortunately, most of these emails are fairly simple to identify, in the event you management the urge to click on hyperlinks or open attachments earlier than confirming who’s the sender.


