In recent times, EDR killers have develop into probably the most generally seen instruments in trendy ransomware intrusions: an attacker acquires excessive privileges, deploys such a device to disrupt safety, and solely then launches the encryptor. In addition to the dominating Carry Your Personal Susceptible Driver (BYOVD) method, we additionally see attackers often abusing official anti-rootkit utilities or utilizing driverless approaches to dam the communication of endpoint detection and response (EDR) software program or droop it in place. These instruments will not be simply plentiful, but in addition behave predictably and persistently, which is exactly why associates attain for them.
On this blogpost, we current our view of EDR killers, grounded in ESET telemetry and incident investigations. The analysis relies on the evaluation and monitoring of virtually 90 EDR killers actively used within the wild. Our focus goes past the weak drivers that dominate most discussions: we doc how associates choose, adapt, and function EDR killers throughout actual intrusions, and what which means for attribution and protection.
We clarify why driver-centric evaluation usually misleads group attribution, present concrete instances of driver reuse and switching throughout unrelated codebases, and spotlight the expansion of driverless disruption alongside commercialized, hardened kits. The result’s a transparent, evidence-based image of how EDR killers perform as a predictable stage in trendy ransomware operations.
Key factors of this blogpost:
- EDR killers are a elementary a part of trendy ransomware intrusions; associates want a brief, dependable window to run encryptors fairly than continuously modifying payloads.
- Associates, not operators, decide the EDR killers; bigger affiliate swimming pools result in higher tooling range.
- The identical driver seems in unrelated instruments, and the identical device can migrate between drivers. Consequently, driver-based attribution to teams is commonly deceptive.
- Packer as a service and “EDR killer as a product” enhance availability, muddy attribution, and add protection complexity.
- EDR killers implement protection evasion methods, whereas encryptors focus purely on encryption.
- We strongly suspect that AI assisted with the event of some EDR killers, and we offer a concrete instance with the Warlock gang.
- Whereas BYOVD dominates, customized scripts, anti-rootkits, and driverless EDR killers are utilized as nicely.
The EDR killer panorama
ESET researchers focus past the weak drivers so usually abused by these instruments. As we’ll show, drawing any connections solely based mostly on the misused drivers is inadequate and may result in incorrect assumptions.
The panorama this analysis unveils is huge, starting from infinite forking of proofs of idea (PoCs) to complicated skilled implementations. Specializing in business EDR killers (marketed on the darkish internet) permits us to realize a greater understanding of their buyer base and spot in any other case hidden affiliations. In-house developed EDR killers provide insights into the interior workings of closed teams. Moreover, vibe coding is making issues much more difficult. We offer a technical overview of EDR killers, together with weak drivers, within the The know-how behind EDR killers part.
On the time of writing, our perception into the EDR killer panorama relies on the next:
- We detect a complete of virtually 90 EDR killers actively used within the wild by mainly any ransomware gang, massive or small:
○ 54 of those are BYOVD-based, abusing a complete of 35 weak drivers,
○ 7 of those are script-based, and
○ 15 of those are anti-rootkits or different freely out there software program.
- For twenty-four of the BYOVD-based EDR killers, we aren’t conscious of a publicly out there PoC they’re based mostly on; we assess that their builders carried out these instruments from scratch and had been impressed solely by the driving force exploitation code.
All through this blogpost, we check with entities forming the ransomware-as-a-service mannequin as follows:
- Operators, who develop the ransomware payload, handle decryption keys, preserve the devoted leak website, usually negotiate the ransom cost with victims, and provide different tooling and providers for a month-to-month payment or a proportion from the ransom cost (usually 5–20%).
- Associates, who hire ransomware providers from operators, deploy encryptors to victims’ networks, and exfiltrate knowledge from victims’ machines.
Why are EDR killers so in style?
To efficiently encrypt knowledge, ransomware encryptors have to evade detection. These days, a variety of mature evasion methods is obtainable, starting from packing and code virtualization to stylish injection. Nonetheless, we hardly ever see any of those carried out in encryptors. As an alternative, ransomware attackers go for EDR killers to disrupt safety options proper earlier than encryptor deployment. This completely different strategy naturally raises the query: why not fairly make investments into making encryptors undetected?
Reliability and operational simplicity for encryptor builders
Ransomware gangs, particularly these with ransomware-as-a-service (RaaS) applications, often produce new builds of their encryptors, and guaranteeing that every new construct is reliably undetected may be time-consuming. Extra importantly, encryptors are inherently very noisy (as they inherently want to change numerous recordsdata in a brief interval); making such malware undetected is fairly difficult. EDR killers present a cleaner various. As an alternative of burying detection-evading logic inside each encryptor replace, attackers merely depend on an exterior device to disrupt or disable safety controls instantly earlier than execution, maintaining encryptors easy, secure, and simple to rebuild.
Low price, excessive energy
As proven all through this blogpost, EDR killers are extraordinarily accessible. Not all intruders or associates have the ability set to develop their very own protection evasion methods. However due to giant collections of public PoCs, EDR killers have basically develop into “plug-and-play”.
On the similar time, EDR killers usually depend on official but weak drivers, making protection considerably tougher with out risking disruption of legacy or enterprise software program. The result’s a category of instruments that provides kernel-level affect with minimal growth effort, making these instruments disproportionately highly effective given their simplicity.
Predictability and repeatability throughout intrusions
Packing or injecting code might assist an implant slip previous detection, nevertheless it doesn’t make sure the long-term stability of the ransomware payload throughout the ultimate part of the intrusion. As a result of layered safety offered by safety merchandise, packed encryptors should be detected in reminiscence or at different levels of execution. EDR killers, alternatively, present a predictable and repeatable step within the assault chain, giving attackers a extra deterministic workflow. Moreover, EDR killers purpose to disrupt the safety resolution as an entire, successfully eliminating all safety layers.
The know-how behind EDR killers
Scripts
The only EDR killers don’t depend on weak drivers or different superior methods. As an alternative, they abuse built-in administrative instruments and instructions resembling taskkill, internet cease, or sc delete to tamper with safety product processes and providers. These crude approaches nonetheless seem often however at the moment are largely related to low-skill ransomware menace actors and commodity malware.
Barely extra subtle variants mix scripting with Home windows Protected Mode. Since Protected Mode masses solely a minimal subset of the working system, and safety options usually aren’t included, malware has the next probability of disabling safety. On the similar time, such exercise could be very noisy, because it requires a reboot, which is dangerous and unreliable in unknown environments. Subsequently, it’s seen solely hardly ever within the wild.
Grey zone: Anti-rootkits
Years in the past, earlier than Microsoft enforced kernel-mode driver signing, rootkits flourished within the cybercrime ecosystem, hiding malicious exercise by manipulating kernel buildings. Their prevalence led to the event of specialised anti-rootkit instruments designed to detect and take away them. As a result of rootkits function in kernel mode, such instruments naturally require excessive privileges and their very own drivers to find, enumerate, and neutralize the rootkits.
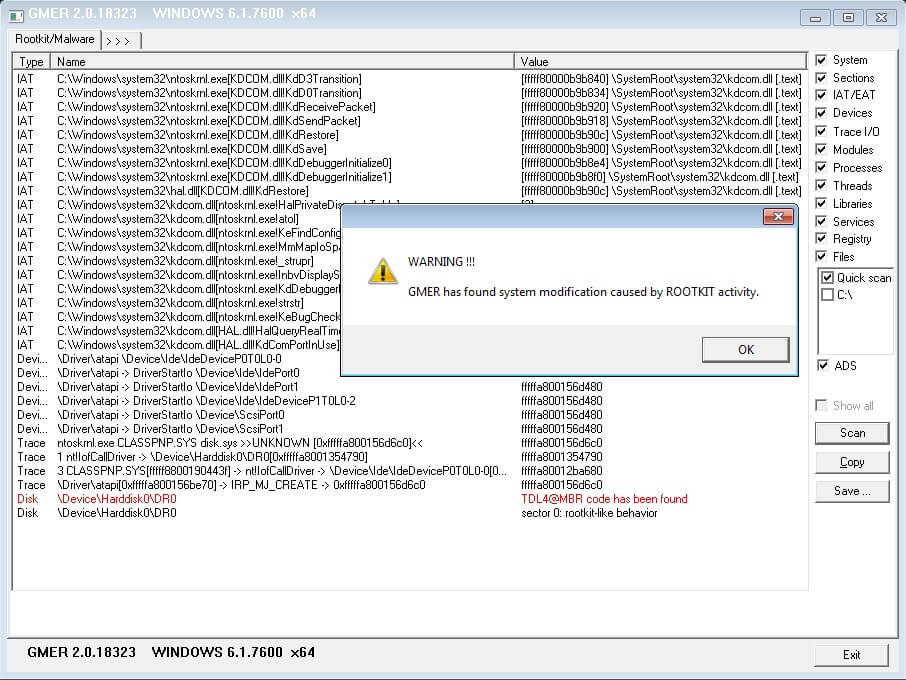
Immediately, ransomware associates often abuse these similar anti-rootkit instruments: to not take away rootkits, however to cripple safety options. Many anti-rootkits provide a user-friendly GUI that enables customers (together with attackers with little technical functionality) to terminate protected processes or providers. In different phrases, official remediation instruments have develop into handy EDR killers when misused. Such instruments embrace GMER (see Determine 1), HRSword, and PC Hunter.
Rootkits
Though rootkits are largely uncommon in trendy cybercrime, notable exceptions nonetheless floor. One instance from final 12 months is ABYSSWORKER, a kernel-mode rootkit that drew consideration after its creators managed to signal it utilizing certificates stolen from Chinese language corporations. These certificates had additionally been used to signal different malware and are due to this fact not particular to ABYSSWORKER. For the reason that stolen certificates belong to a trusted certificates chain, such a driver remains to be allowed to run within the kernel. And, to make issues extra difficult, even certificates revocation isn’t a bulletproof choice, as not too long ago demonstrated by Huntress.
Susceptible drivers
The BYOVD method has develop into the hallmark of recent EDR killers: dominant, dependable, and extensively used. In a typical state of affairs, an attacker drops a official however weak driver onto the sufferer machine, installs the driving force, after which runs malware that abuses the driving force’s vulnerability. The objective is to terminate protected processes or disable callbacks that safety merchandise depend on.
Though there are millions of official weak drivers, solely a relatively small subset is actively exploited in ransomware incidents. Nonetheless, the supply of public PoCs means that there’s successfully no restrict on the variety of menace actors that may undertake or adapt exploits for these vulnerabilities. Some attackers reuse present codebases with minimal or no modifications, others change no logic however reimplement them of their most popular programming language, and a few even develop solely new EDR killers (maintaining solely a small portion of the unique code accountable for driver exploitation) that they both use on their very own or provide as a service.
Driverless EDR killers
Lastly, a smaller however rising class of EDR killers achieves its objectives with out touching the kernel in any respect. As an alternative of terminating EDR processes, these instruments intrude with different important options. Examples embrace instruments like EDRSilencer, which blocks communication between an endpoint and its safety backend, and EDR-Freeze, which causes EDR processes to “grasp” or develop into unresponsive. These driverless methods are in style as a result of their unconventional strategy makes detection and mitigation more difficult, and they’re publicly out there. Certainly, ESET researchers have seen fast adoption of those instruments in a matter of days by ransomware menace actors.
Who develops EDR killers?
In 2025, ESET researchers revealed an evaluation of EDRKillShifter, an EDR killer developed by RansomHub operators and supplied on to their associates. On the time of writing, we aren’t conscious of another RaaS applications whose operators present their very own proprietary EDR killers. This makes the now-defunct RansomHub a notable exception within the ransomware panorama.
As an alternative, most menace actors fall into one of many following classes:
- non-RaaS gangs growing their very own EDR killers,
- attackers forking and barely modifying public proof-of-concept code, or
- attackers buying an EDR killer from underground marketplaces.
Let’s break these conditions down in additional element.
Closed teams
Non-RaaS gangs often function as absolutely closed ecosystems: no associates, no preliminary entry brokers, and no exterior companions. These teams preserve tight management over their intrusion workflows and usually depend on a repeatable, internally constant set of TTPs. Given this stage of operational self-discipline, growing their very own EDR killers turns into a pure extension of their toolset.
ESET researchers highlighted an early instance of this in-house growth mannequin in 2024 with the Embargo gang. On the time, Embargo relied on two EDR killers:
- a customized Protected Mode script, leveraging the method already described earlier, and
- MS4Killer, a device impressed by the publicly out there s4killer PoC.
Though MS4Killer was based mostly on an out there PoC, its builders made vital modifications: they added parallelism, modified the code circulation, and encrypted strings and the embedded driver. For the reason that publication of that analysis, Embargo has shifted to one more public PoC, evil‑mhyprot‑cli, this time with minimal code modifications.
A second, more moderen, instance is the DeadLock gang. DeadLock maintains a low profile by avoiding having a devoted leak website and conducting all negotiations by Session, a in style various to the extra frequent Tox. ESET researchers have noticed DeadLock utilizing two EDR killers, DLKiller (additionally talked about as an unnamed loader by Cisco Talos) and Susanoo, and anti-rootkits resembling GMER and PC Hunter. ESET researchers imagine with low confidence that DLKiller and the DeadLock encryptor are the work of the identical developer on account of notable, however by itself inconclusive, code similarities. Apparently, Susanoo gives a loading display screen and a GUI, each offered in Determine 2, permitting for handbook interplay and anticipating the attacker to have interactive entry to the sufferer’s machine.
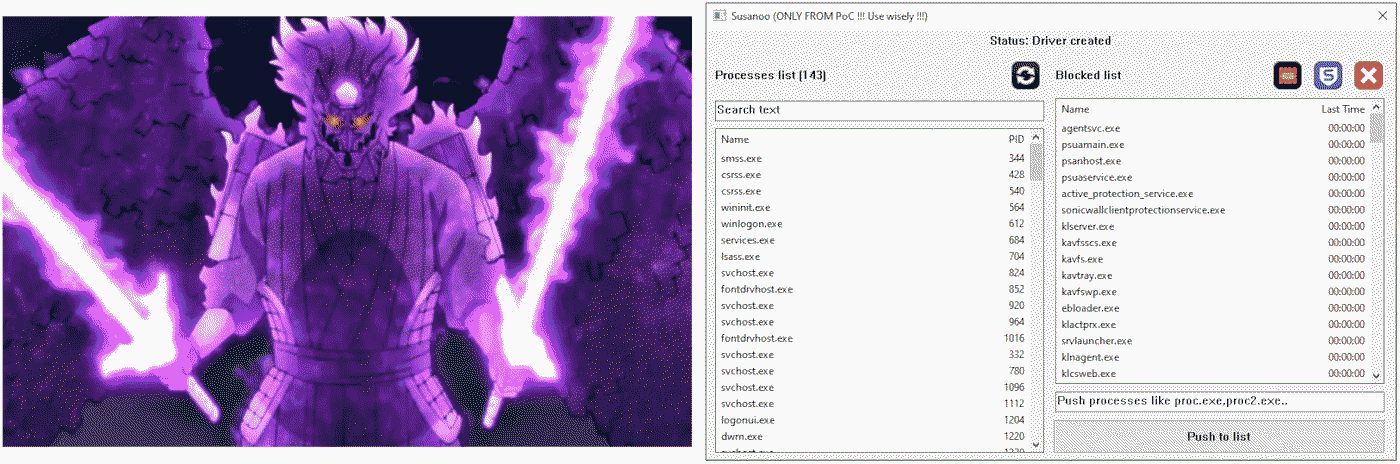
Because the screenshot clearly demonstrates, Susanoo gives buttons to pre-load the record of monitored processes – a devoted one focusing on Sophos-related processes and a “TNT” one focusing on all processes recognized to Susanoo.
The third and ultimate instance is Warlock. Though the Warlock leak website has been silent since November 6th, 2025, the group stays operational and retains increasing its technical arsenal. The gang is thought for its willingness to experiment: it tailored the VS Code abuse method for stealthy distant entry, beforehand documented in September 2024 and used by the Mustang Panda APT group, whereas additionally pioneering the malicious use of Velociraptor. Ever since, Warlock has persistently relied on these methods. Its strategy to encryptors mirrors this sample as nicely – Warlock has employed a number of completely different encryptors over time, starting from customized ones to variants based mostly on Babyk or generated utilizing the leaked LockBit Black builder.
Given all that, Warlock’s experimentation with EDR killers isn’t a surprise. For the reason that gang first appeared, it has routinely deployed a number of EDR killers per intrusion, typically even dozens throughout latest operations, successfully brute-forcing its solution to a working resolution. Warlock’s tooling is various not solely in amount but in addition in technical depth: the gang doesn’t restrict itself to a single weak driver and has abused not less than 9 completely different drivers thus far, together with some with none publicly out there PoC (not less than to our information); a element that underscores the group’s technical proficiency and its potential to adapt offensive instruments past what is quickly publicly out there.
Modification of a PoC
That is by far the commonest strategy noticed in ransomware intrusions. Risk actors often take an present, well-tested PoC, and alter solely the noncritical elements earlier than deploying it in actual assaults. These modifications usually embrace:
- eradicating or altering debugging messages,
- including code obfuscation,
- adjusting the record of focused safety merchandise, and
- rewriting the device in a unique programming language.
The essential level, nevertheless, is that the core exploitation logic, particularly the half that interacts with the weak driver, virtually by no means modifications. This logic is commonly so simple as calling the Home windows API DeviceIoControl with a “right” dwIoControlCode worth and the title of the method to terminate in lpInBuffer. Whereas renaming strings, restructuring the codebase, or reimplementing the device in one other language are operations that don’t require deep technical information, modifying the exploitation logic actually is and due to this fact is often averted.
Whereas there are lots of publicly out there PoCs for EDR killers, one repository stands out: BlackSnufkin’s BYOVD. Frequently up to date, it comprises (on the time of writing) PoCs for exploiting 10 weak drivers, every carried out following the identical modular template. The implementation permits for simple modifications, extensions, and new driver assist. Moreover, the code is nicely documented (see Determine 3), making this repository essentially the most often used one in ransomware exercise within the wild.
We detected one among BlackSnufkin’s EDR killers, TfSysMon-Killer, deployed throughout a Monti ransomware assault in February 2025; the deployed variant was similar functionality-wise, however was reimplemented from Rust to C++, more likely to align with different instruments of the menace actor. One other instance of language switching is dead-av, which its writer brazenly describes as a Go rewrite of GhostDriver, one other PoC created by BlackSnufkin.
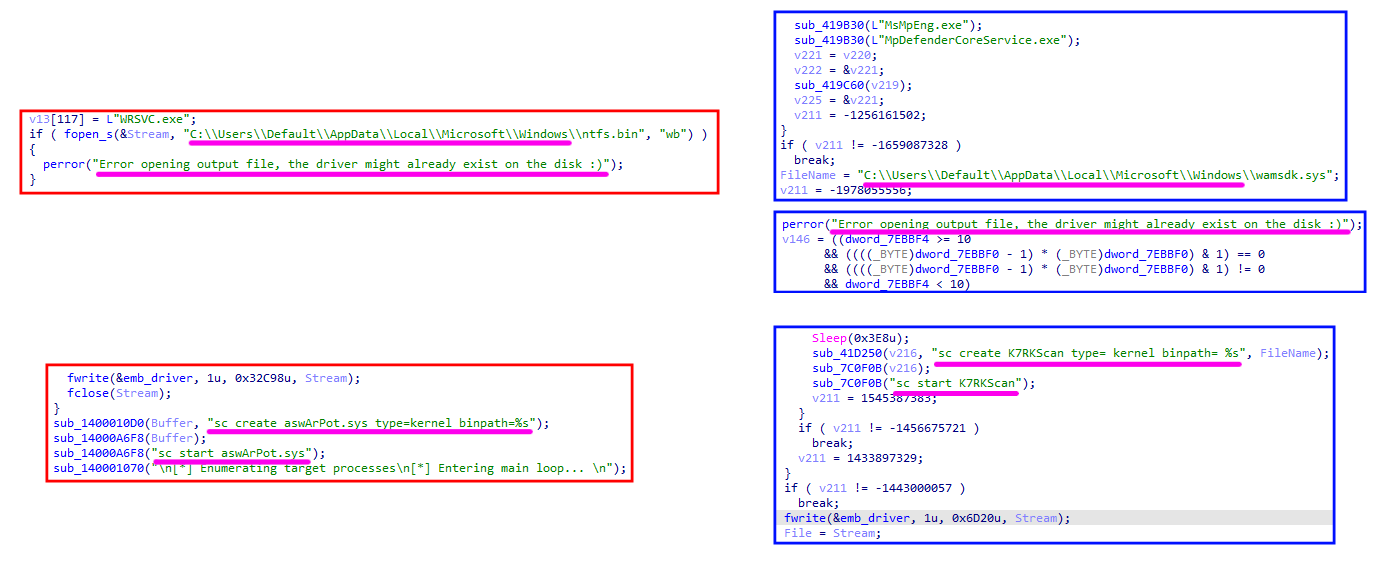
A extra in depth modification effort may be seen in SmilingKiller, an EDR killer not too long ago noticed by ESET researchers throughout LockBit and Dire Wolf intrusions. Its developer was impressed by kill-floor, an EDR killer PoC that abuses Avast’s aswArPot.sys. In addition to modifying debug messages and including control-flow flattening obfuscation (see Determine 4), the writer additionally switched the abused driver to K7RKScan.sys, the identical driver abused by K7Terminator, one other of BlackSnufkin’s PoCs.
EDR killer as a service
Given the robust and rising demand for EDR-disruption instruments, it’s no shock {that a} parallel market for business EDR killers has emerged. The vary of choices is huge: some ads present solely obscure guarantees with no technical particulars, whereas others embrace in depth characteristic lists, utilization directions, and even video demonstrations. Beneath are three notable examples.
One such commercial, disclosed by Flare in October 2025, originated from a menace actor utilizing the moniker Бафомет. The menace actor marketed an EDR killer that ESET researchers later named DemoKiller. ESET telemetry confirms that DemoKiller has been utilized by associates of the Qilin, Akira, and Gents gangs, and we additionally noticed it deployed as soon as throughout a RansomHouse intrusion. The commercial is proven in Determine 5.
One other paid EDR killer revolves across the ABYSSWORKER rootkit, beforehand mentioned on this blogpost. When paired with its HeartCrypt-packed loader part, which ESET researchers named AbyssKiller, this EDR killer has develop into probably the most generally noticed business ones within the wild. ESET researchers have seen AbyssKiller utilized by associates of the Medusa, DragonForce, and the now-disrupted BlackSuit gangs.
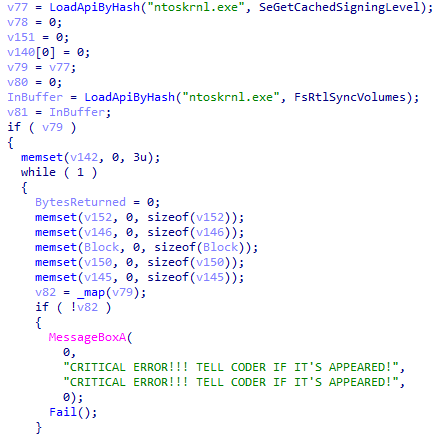
The ultimate noteworthy instance is an EDR killer that we name CardSpaceKiller. This device is persistently packed utilizing VX Crypt, a comparatively new packer as a service analyzed by Sophos in late 2025. VX Crypt isn’t distinctive to this EDR killer; it has additionally been used to guard different malware households resembling BumbleBee. In accordance with Sophos, CardSpaceKiller has appeared in intrusions involving Akira, Medusa, Qilin, and Crytox. ESET telemetry aligns with these findings and moreover exhibits deployment throughout MedusaLocker incidents. Analyzing the unpacked payload, it’s instantly clear that this EDR killer comes from a business providing, the place the developer tries to deal with edge instances with a warning (see Determine 6).
The character and worth of such commercially marketed instruments range. Some declare to promote supply code, others solely particular person builds. The value is commonly a matter of particular person negotiation; when disclosed publicly, the value has different from a whole lot to 1000’s of US {dollars}.
EDR killers and AI
Whereas the set of abused weak drivers stays comparatively small, the variety of distinct user-mode elements which can be a part of trendy EDR killers within the wild is rising quickly. Given this surge in quantity and selection, it’s pure in 2026 to ask: is AI contributing to this proliferation?
Figuring out whether or not AI straight assisted in producing a selected codebase is commonly virtually not possible. There isn’t any definitive forensic marker that reliably distinguishes AI-generated code from human-written code, particularly when attackers post-process or obfuscate it. Nonetheless, ESET researchers assess that not less than some not too long ago noticed EDR killers exhibit traits strongly suggestive of AI-assisted era.
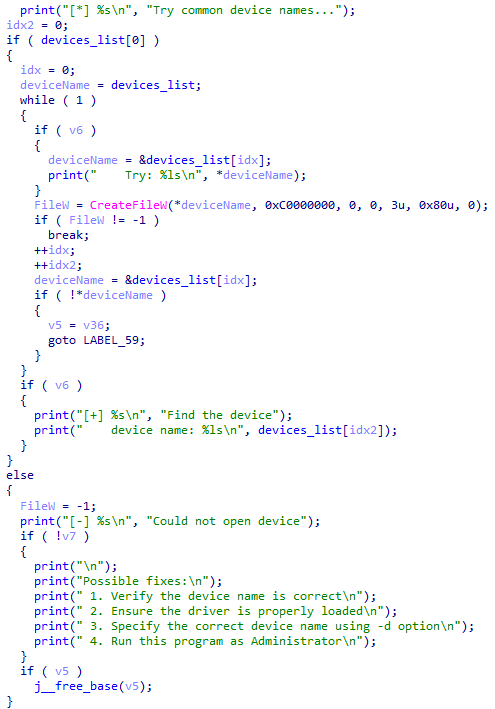
A transparent instance seems in an EDR killer not too long ago deployed by Warlock. The device comprises a piece of code that not solely prints a listing of Doable fixes, a sample typical for AI-generated boilerplate, but in addition, as an alternative of exploiting a selected driver, implements a trial-and-error mechanism that cycles by a number of unrelated, generally abused gadget names till it finds one which works. The corresponding code is proven in Determine 7.
Past the drivers
Totally understanding the EDR killer ecosystem requires trying far past weak drivers. Whereas driver exploitation stays a dominant pillar of many instruments, it’s only one a part of a wider panorama. Our analysis exhibits that specializing in drivers alone obscures significant relationships between instruments, associates, and exercise clusters.
A key remark is the division of labor in RaaS ecosystems. Operators usually provide the encryptor and supporting infrastructure, however EDR killer choice is left to associates. Which means the bigger the affiliate pool, the extra various the EDR killer tooling turns into. On the similar time, the constant reuse of particular instruments inside specific clusters may help establish new affiliations, strengthen infrastructure linkages, and reveal operator-affiliate relationships that will stay invisible if one seemed solely at encryptor households.
Driver reuse and switching
Public PoCs have made driver exploitation extensively accessible, however this has created a deceptive state of affairs: the identical weak driver is commonly reused throughout unrelated EDR killers, and the identical EDR killer can make the most of completely different drivers over time. Because of this, driver-based attribution alone is error-prone.
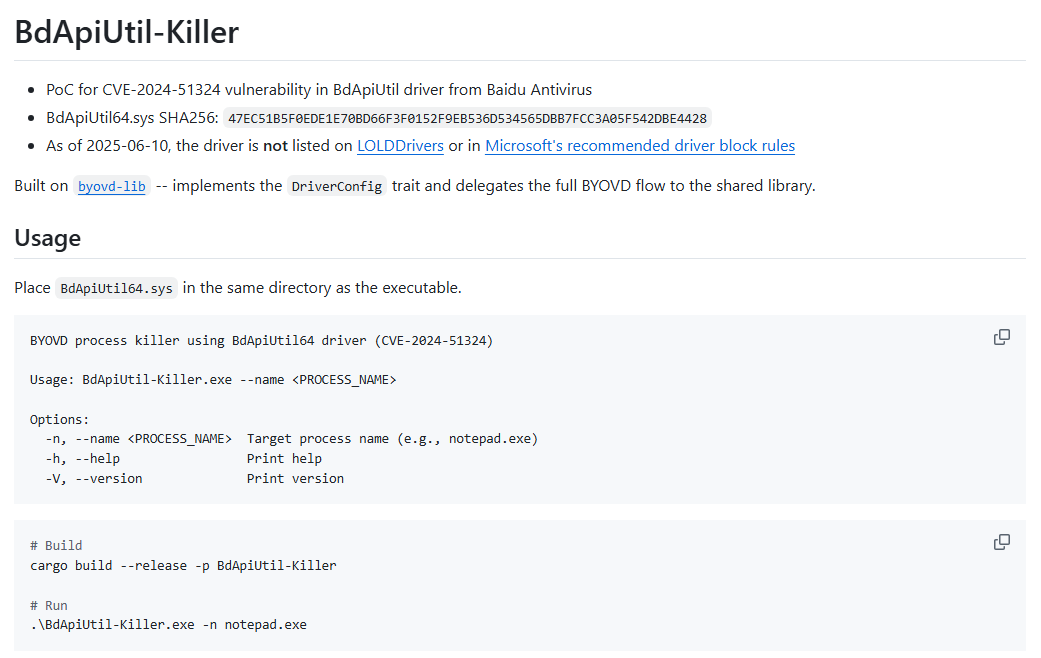
A transparent instance is the Baidu Antivirus driver BdApiUtil.sys, which seems in a number of impartial initiatives, together with:
- dead-av,
- BdApiUtil-Killer,
- DLKiller,
- HexKiller, one among Warlock’s EDR killers, and
- SevexKiller, a latest EDR killer detected throughout Akira deployments.
The identical sample seems with the TfSysMon.sys driver (ThreatFire System Monitor). It’s abused by TfSysMon-Killer, Susanoo, and EDRKillShifter – three codebases with distinct implementations and growth histories.
Driver switching is equally frequent. CardSpaceKiller, for instance, initially relied on HwRwDrv.sys, however later variants migrated to ThrottleStop.sys with minimal modifications to the remaining logic. The driving force is interchangeable; the exploitation layer stays largely the identical.
This illustrates the broader level: drivers are a commodity useful resource, and their presence alone gives little perception into menace actor sophistication or relationships.
Detection evasion
Attackers aren’t placing a lot effort into making their encryptors undetected. Moderately, all the delicate defense-evasion methods have shifted to the user-mode elements of EDR killers. This pattern is most seen in business EDR killers, which regularly incorporate mature anti-analysis and anti-detection capabilities. Notable recurring methods embrace:
- Driver decoupling. The killer and the driving force are sometimes delivered individually. Associates manually set up the driving force first, verifying that it masses efficiently earlier than executing the precise EDR-killing part.
- Use of business packers. Packers resembling VX Crypt (as used with CardSpaceKiller) and HeartCrypt (as used with AbyssKiller) present structure-level obfuscation, anti‑VM habits, and steady repacking to evade static signatures. Widespread code virtualization protectors like VMProtect and Themida are additionally favored.
- Encrypted embedded drivers. When a driver is bundled with an EDR killer, it’s often saved in encrypted kind.
- Exterior encrypted payloads. Some EDR killers retailer encrypted shellcode or auxiliary elements in separate recordsdata. This strategy successfully hides essential elements of the killer from being simply accessible to defenders.
- Code obfuscation. Widespread methods embrace control-flow flattening (SmilingKiller), call-by-hash decision (CardSpaceKiller), and string obfuscation
- Password safety. EDRKillShifter is an ideal instance of utilizing this method. Defending a vital a part of the EDR killer with a password creates detection challenges, but in addition gives analysis alternatives.
Defending in opposition to ransomware and EDR killers
Defending in opposition to ransomware requires a basically completely different mindset than defending in opposition to automated threats. Phishing emails, commodity malware, and exploit chains cease as soon as detected and neutralized by safety options; ransomware intrusions don’t. They’re interactive, human-driven operations, and intruders frequently adapt to detections, device failures, and environmental obstacles. Because of this, even when particular person steps are detected, they solely have defensive worth if defenders – whether or not an inside SOC staff, an MSSP, or an MDR supplier – reply accurately, instantly, and with ample decisiveness.
Most EDR killers depend on official however weak drivers, which is why defenders usually instinctively give attention to driver blocking. Blocking the driving force from loading is a vital step and does certainly neutralize the EDR killer, however solely on the final doable second. By the point an affiliate makes an attempt to put in the driving force, they usually have already got excessive privileges and are seconds away from launching the encryptor. If the EDR killer fails, they’ll merely attempt one other device.
As a result of these drivers are official, overly aggressive blocking dangers disrupting business-critical software program, complicating incident dealing with. Focused blocking additionally faces challenges. In February 2025, Test Level confirmed that menace actors had been in a position to create over 2,500 samples of Truesight.sys, all of them remaining validly signed on account of a weak spot within the signature validity checking course of. Truesight.sys can also be one among many examples of a weak spot in Microsoft’s driver signing coverage. A 12 months later, in February 2026, Huntress analyzed an intrusion the place EnPortv.sys was abused regardless of its certificates being expired and explicitly revoked.
For this reason a prevention-first technique is important. Blocking generally misused drivers from loading is an efficient and crucial protection mechanism, nevertheless it shouldn’t be the one one. Learning EDR killers permits defenders to provide you with a multilayered technique that expands the horizons; the objective is to cease the EDR killer earlier than execution. In spite of everything, on the subject of ransomware, the simplest protection technique is to have strategies in place to detect, comprise, and remediate the menace at each doable step.
Conclusion
EDR killers endure as a result of they’re low-cost, constant, and decoupled from the encryptor – an ideal match for each encryptor builders, who don’t have to give attention to making their encryptors undetectable, and associates, who possess an easy-to-use, highly effective utility to disrupt defenses previous to encryption.
Our analysis presents telemetry-backed insights into the EDR killer ecosystem that transfer previous the generally seen driver-centric strategy. We doc how associates, not operators, form tooling range, and the way codebases routinely reuse and swap drivers. We define how the previous 12 months noticed more and more commercialized choices for EDR killers, and showcase how business EDR killers particularly can provide the protection evasion methods generally lacking in encryptors.
We emphasize that whereas stopping weak drivers from loading is a vital step within the line of protection, it might additionally result in potential enterprise disruptions, which is why one mustn’t rely solely on that and purpose to disrupt EDR killers earlier than they even get an opportunity to load the driving force. Moreover, we demonstrated that driverless approaches, whether or not script- or vulnerability-based, are a well-liked addition to any ransomware menace actor’s arsenal.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis gives non-public APT intelligence stories and knowledge feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
A complete record of indicators of compromise (IoCs) and samples may be present in our GitHub repository.
Information
| SHA-1 | Filename | Detection | Description |
| 54547180A99474B0DBA2 | 2Gk8.exe | Win32/Loader.Ly | AbyssKiller EDR killer. |
| 75F85CAEA52FE5A124FA | smuot.sys | Win64/Rootkit. | The ABYSSWORKER rootkit. |
| 002573D80091F7F8167B | lasdjfioasdjfioer | Win64/HackTool. | EDRSilencer EDR killer. |
| 1E7567C0D525AD037FBB | EDR-Freeze.exe | Win64/HackTool. | EDR-Freeze EDR killer. |
| 65C2388B0AFB1D1F1860 | Killer.exe | Win64/KillAV.DQ | EDRKillShifter EDR killer. |
| A9F37104D2D89051F34E | EDRGay.exe | Win32/KillAV.NVJ | DLKiller EDR killer. |
| 083F604377D74C437782 | susanoo.exe | Win64/KillAV.CQ | Susanoo EDR killer. |
| 570161A420992280A8EC | vmtools.exe | Win32/KillAV.NVL | HexKiller EDR killer. |
| BBE0E14BC7ECE8A7A123 | Take a look at.exe | WinGo/KillAV.M | SevexKiller EDR killer. |
| 31CE76931CA09D3918B3 | TfSysMon-Killer.exe | Win64/KillAV.DP | TfSysMon-Killer EDR killer. |
| B9820BF443C375577CEE | deadav.exe | WinGo/KillAV.L | dead-av EDR killer. |
| 34270B07538B7357CF10 | zcasdfhsdjfhoqewruo | Win64/KillAV.DP | GhostDriver EDR killer. |
| 09735640D6634B030375 | pip.exe | Win32/KillAV.NVQ | SmilingKiller EDR killer. |
| 85BC0A4F67522D6AC6BE | kill-floor.exe | Win64/KillAV.AV | kill-floor EDR killer. |
| 711C95FEAD2215E9AC59 | demor.exe | Win64/Agent.GAJ | DemoKiller EDR killer. |
| BC65ED919988C8E4B8F5 | demo.exe | Win64/KillAV.DR | DemoKiller EDR killer. |
| 148C0CDE4F2EF807AEA7 | BdApiUtil64.sys drivergay.sys Gosling.sys kihost.sys | Win64/VulnDriver. | Baidu Antivirus BdApi weak driver. |
| 468121E7D6952799F929 | K7RKScan.sys K7RKScan_1516.sys wamsdk.sys | Win64/VulnDriver. | K7RKScan Kernel Module weak driver. |
| C881F43C7FE94A6F056A | elliot.sys kill.sys TfSysMon.sys WatchMgrs.sys | Win64/Riskware.PC | ThreatFire System Monitor weak driver. |
| 67D17CA90880B448D5C3 | 1721894530.sys rentdrv2.sys | Win64/VulnDriver. | Rentdrv2 weak driver. |
| F329AE0FDF1E198BEA6B | knowledge.sys | Win64/VulnDriver. | USB-C Energy Supply Firmware Replace Utility weak driver. |
| 82ED942A52CDCF120A89 | NitrogenK.sys rwdrv.sys ThrottleBlood.sys ThrottleStop.sys | Win64/VulnDriver. | ThrottleStop weak driver. |
| CE1B9909CEF820E52816 | hlpdrv.sys | Win64/Agent.GRL | Customized rootkit utilized by CardSpaceKiller. |
| 5D6B9E80E12BFC595D4D | aswArPot.sys kallmekris.sys | Win64/VulnDriver. | Avast anti-rootkit weak driver. |
| 7310D6399683BA3EB2F6 | probmon.sys Sysprox.sys | Win64/VulnDriver. | ITM SYSTEM File Filter weak driver. |
| C85C9A09CD1CB1691DA0 | kl.sys rspot.sys | Win64/VulnDriver. | Beijing Rising Community Safety weak driver. |
| 6EE94F6BDC4C4ED0FFF6 | msupdate.sys thelper.sys | Win32/IP-guard.E | OCular THelper weak driver. |
| BA14C43031411240A083 | praxisbackup.exe | Win64/Agent.ECW | MS4Killer EDR killer. |
| 127B50C8185986A52AE6 | model.dll | Win64/KillAV.Card | CardSpaceKiller EDR killer. |
| A3BDB419703A70157F2B | 0th3r_av5.exe | Win64/KillAV.Card | CardSpaceKiller EDR killer. |
| 4A57083122710D51F247 | DrKiller_Cry_0x000 | Win64/Kryptik.FBC | CardSpaceKiller EDR killer. |
| DB8BCB8693DDF715552F | HwRwDrv.sys MegaDrov.sys | Win64/VulnDriver. | CardSpaceKiller EDR killer. |
MITRE ATT&CK methods
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Execution | T1059.003 | Command and Scripting Interpreter: Home windows Command Shell | Script-based EDR killers use taskkill, sc, internet cease, and comparable instructions to tamper with safety. |
| T1569.002 | System Providers: Service Execution | EDR killers execute weak drivers as providers. | |
| Persistence | T1543.003 | Create or Modify System Course of: Home windows Service | Some EDR killers might create providers to run throughout Protected Mode or at subsequent boot. |
| T1037.001 | Boot or Logon Initialization Scripts: Logon Script (Home windows) | EDR killers register scripts and providers to run early at boot to intrude with EDR loading. | |
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation | BYOVD-based EDR killers exploit weak drivers to escalate kernel-level privileges. |
| Protection Evasion | T1562.001 | Impair Defenses: Disable or Modify Instruments | EDR killers terminate or droop EDR/AV processes and providers to bypass detection. |
| T1562.009 | Impair Defenses: Protected Mode Boot | Script-based EDR killers reboot techniques into Protected Mode to tamper with safety elements. | |
| T1070.004 | Indicator Elimination: File Deletion | EDR killers might try and delete EDR/AV recordsdata to disable protections. | |
| T1562.006 | Impair Defenses: Indicator Blocking | Driverless EDR killers block telemetry and community communication (e.g., EDRSilencer). | |
| T1027 | Obfuscated Information or Data | Business EDR killers particularly use obfuscation and encryption (e.g., CardSpaceKiller). | |
| T1027.009 | Obfuscated Information or Data: Embedded Payloads | Some EDR killers embed the drivers straight into their user-mode elements, usually encrypted. | |
| T1027.002 | Obfuscated Information or Data: Software program Packing | Business EDR killers depend on packers like HeartCrypt or VX Crypt, and in addition superior code protectors like Themida and VMProtect. | |
| T1027.005 | Obfuscated Information or Data: Indicator Elimination from Instruments | EDR killers like SmilingKiller use control-flow flattening and code obfuscation. | |
| T1140 | Deobfuscate/Decode Information or Data | Some EDR killers retailer encrypted drivers and shellcode in devoted recordsdata on disk. | |
| Impression | T1490 | Inhibit System Restoration | Some EDR killers delete or rename security-related recordsdata, impacting restoration. |
| T1489 | Service Cease | EDR killers cease protected providers of safety merchandise and tamper with their performance. |




