
Hackers are abusing a respectable however long-revoked EnCase kernel driver in an EDR killer that may detect 59 safety instruments in makes an attempt to deactivate them.
An EDR killer is a malicious software created particularly to bypass or disable endpoint detection and response (EDR) instruments, together with different safety options. They sometimes use susceptible drivers to unhook the protections on the system.
Normally, attackers depend on the ‘Carry Your Personal Susceptible Driver’ (BYOVD) method, the place they introduce a respectable however susceptible driver and use it to achieve kernel-level entry and terminate safety software program processes.
The method is well-documented and extremely popular, however regardless of Microsoft introducing varied defenses over time, Home windows methods are nonetheless susceptible to efficient bypasses.
Encase is a digital investigation software utilized in legislation enforcement forensic operations that permits extracting and analyzing information from computer systems, cell units, or cloud storage.
Huntress researchers responding to a cybersecurity incident earlier this month observed the deployment of a customized EDR killer that was disguised as a respectable firmware replace utility and used an outdated kernel driver.
The attackers breached the community utilizing compromised SonicWall SSL VPN credentials and exploiting the shortage of multi-factor authentication (MFA) for the VPN account.
After logging in, the attackers carried out aggressive inner reconnaissance, together with ICMP ping sweeps, NetBIOS title probes, and SMB-related exercise, SYN flooding exceeding 370 SYNs/sec.
The EDR killer used on this case is a 64-bit executable that abuses ‘EnPortv.sys,’ an outdated EnCase kernel driver, to disable safety instruments working on the host system.
The motive force’s certificates was issued in 2006, expired in 2010, and was subsequently revoked; nonetheless, as a result of the Driver Signature Enforcement system on Home windows works by validating cryptographic verification outcomes and timestamps, slightly than checking Certificates Revocation Lists (CRLs), the working system nonetheless accepts the outdated certificates.
Though Microsoft added a requirement in Home windows 10 model 1607 that kernel drivers have to be signed by way of the {Hardware} Dev Heart, an exception was made for certificates issued earlier than July 29, 2015, which applies on this case.
The kernel driver is put in and registered as a faux OEM {hardware} service, establishing reboot-resistant persistence.
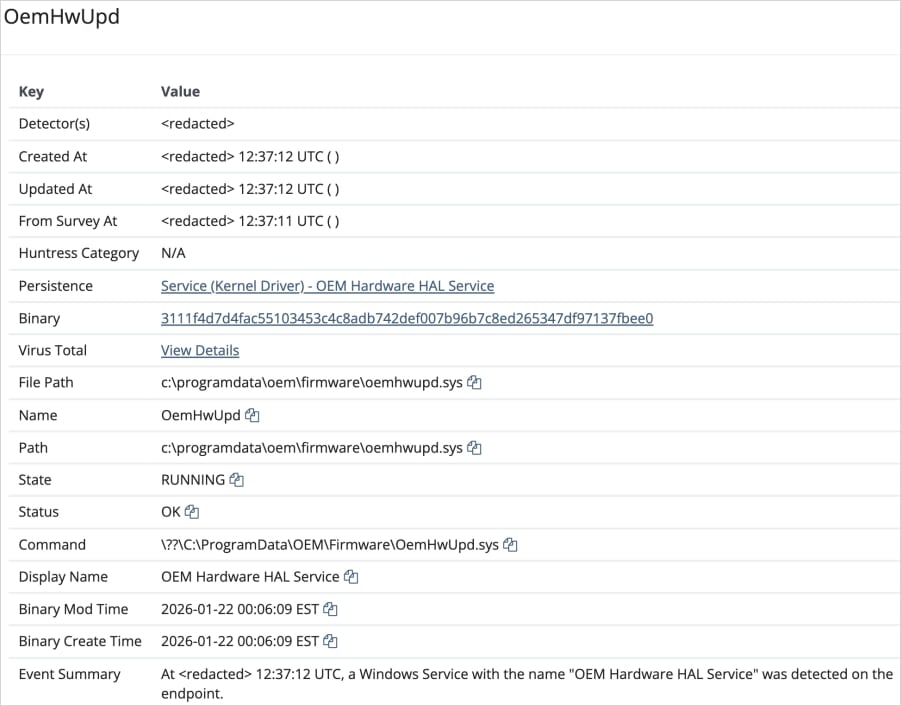
Supply: Huntress
The malware makes use of the driving force’s kernel-mode IOCTL interface to terminate service processes, bypassing current Home windows protections akin to Protected Course of Mild (PPL).
There are 59 focused processes associated to numerous EDR and antivirus instruments. The kill loop executes each second, instantly terminating any processes which might be restarted.
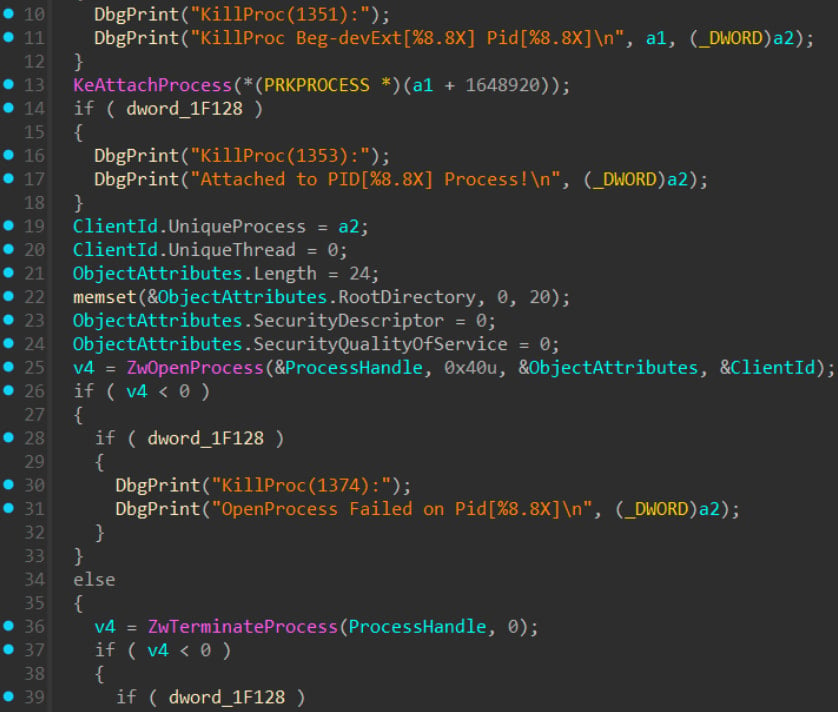
Supply: Huntress
Huntress believes that the intrusion was associated to ransomware exercise, though the assault was stopped earlier than the ultimate payload was deployed.
Key protection suggestions embrace enabling MFA on all distant entry companies, monitoring VPN logs for suspicious exercise, and enabling HVCI/Reminiscence Integrity to implement Microsoft’s susceptible driver blocklist.
Moreover, Huntress recommends monitoring for kernel companies masquerading as OEM or {hardware} parts and deploying WDAC and ASR guidelines to dam susceptible signed drivers.
Fashionable IT infrastructure strikes quicker than guide workflows can deal with.
On this new Tines information, find out how your workforce can cut back hidden guide delays, enhance reliability by means of automated response, and construct and scale clever workflows on prime of instruments you already use.




