
Russian state-sponsored hackers have been linked to an ongoing Sign and WhatsApp phishing marketing campaign focusing on authorities officers, navy personnel, and journalists to achieve entry to delicate messages.
This report comes from the Netherlands Defence Intelligence and Safety Service (MIVD) and the Netherlands Normal Intelligence and Safety Service (AIVD), who confirmed that Dutch authorities workers have been focused within the assaults.
The Dutch intelligence companies say the operation depends on phishing and social-engineering strategies that abuse legit authentication options to take over accounts and covertly monitor new messages.
Sign posted on social media that it’s conscious of focused phishing assaults which have resulted in account takeovers and warned customers to stay vigilant.
“We’re conscious of latest studies concerning focused phishing assaults which have resulted in account takeovers of some Sign customers, together with authorities officers and journalists,” Sign posted on BlueSky.
“We take this very significantly. To be clear: Sign’s encryption and infrastructure haven’t been compromised and stay sturdy. These assaults have been executed by way of subtle phishing campaigns, designed to trick customers into sharing data – SMS codes and/or Sign PIN – to achieve entry to customers’ accounts.”
Sign says that when sending SMS codes, they all the time warn to not share SMS codes or PINs with anybody, together with Sign workers or companies.
Phishing messages impersonate Sign assist
One of many main assault strategies entails impersonating a pretend “Sign Safety Assist Chatbot” that warns the consumer that suspicious exercise was detected on their account.
The message then tells the consumer to finish a “verification process” by sharing a verification code despatched to their cellphone.
“We have now seen suspicious exercise in your gadget, which might have led to information leak. We have now additionally detected makes an attempt to achieve entry to your non-public information in Sign,” reads the Sign phishing message.
“To stop this, it’s a must to go verification process, coming into the verification code to Sign Safety Assist Chatbot.”
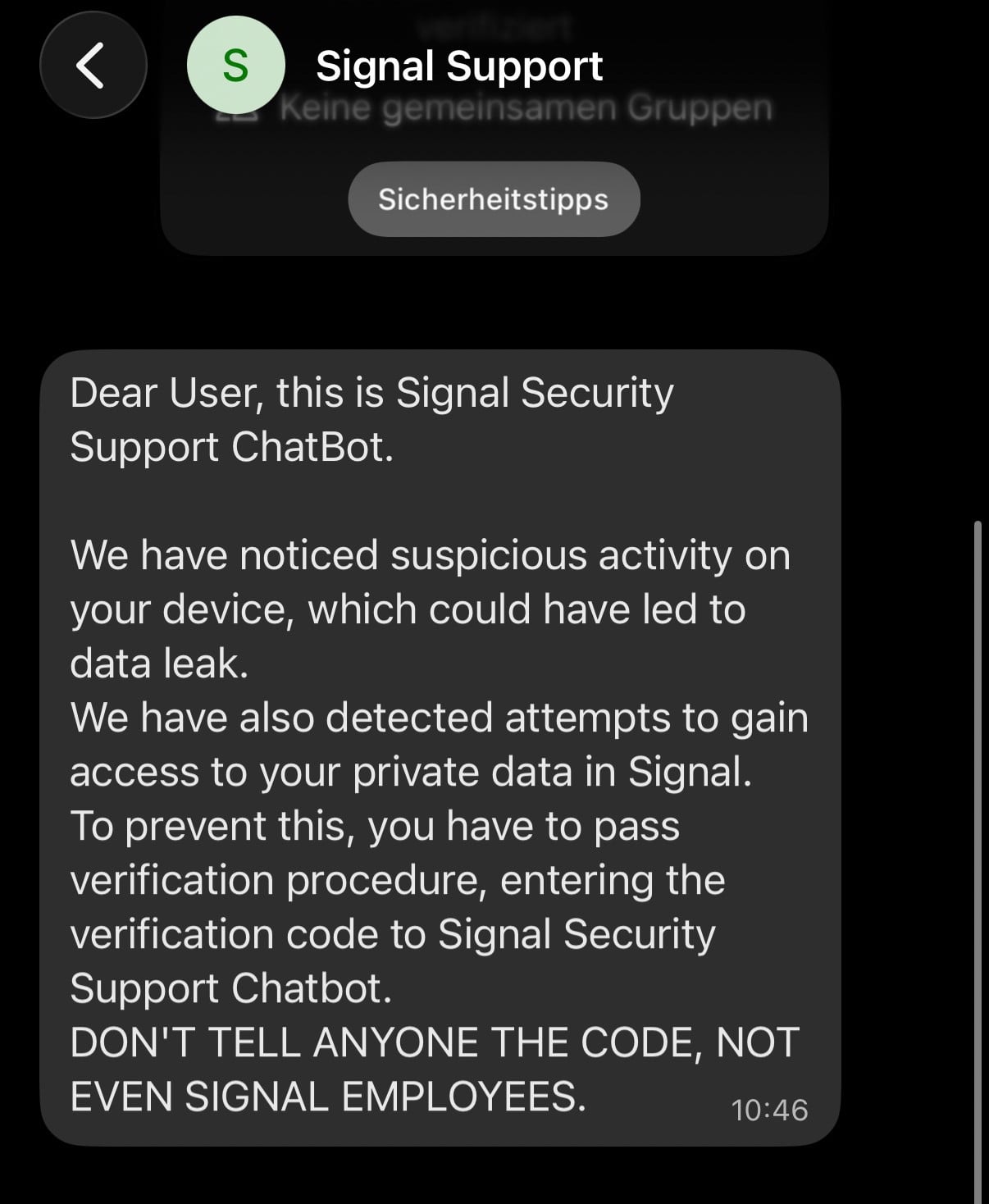
Supply: Sign
After the sufferer supplies the SMS verification code and their Sign PIN, attackers can take full management of the account by registering it on their very own gadget.
Based on the advisory, as soon as attackers acquire entry to an account, they will additionally change the cellphone quantity related to it to at least one underneath their management. This enables them to entry the sufferer’s contact record and incoming messages, together with messages despatched in group chats.
Attackers may impersonate the sufferer by sending messages from the compromised account.
As Sign shops chat historical past domestically on the gadget, when victims re-register a brand new account, they might regain entry to their previous messages, probably main them to imagine nothing uncommon occurred.
“The sufferer is unable to entry their account, though they can create a brand new Sign account utilizing their present phone quantity, because the actor has already linked the compromised account to a brand new phone quantity,” warns the Dutch intelligence companies.
“As a result of Sign shops the chat historical past domestically on the cellphone, a sufferer can regain entry to that historical past after re‑registering. In consequence, the sufferer might assume that nothing is flawed. The Dutch companies wish to stress that this assumption might be incorrect.”
The advisory additionally says a second technique was noticed abusing Sign’s and WhatsApp’s gadget linking performance.
Attackers ship victims a malicious QR code or hyperlink that seems to be an invite to hitch a chat group or join with one other consumer. When the sufferer scans the code or opens the hyperlink, it hyperlinks the attacker’s gadget to the sufferer’s account as a substitute.
Each Sign and WhatsApp supply a linked gadget function that permits customers to attach units, comparable to computer systems or tablets, to their accounts to allow them to ship and obtain messages from a number of units. That is usually completed by scanning a QR code generated by the principle cell gadget, which authorizes the brand new gadget to entry and synchronize the account’s messages.
As soon as related, the attacker features entry to the sufferer’s messages and could possibly learn chat historical past, monitor conversations in actual time, and ship messages within the sufferer’s title.
Not like account takeovers, victims usually retain entry to their accounts, which might make a breach tougher to detect.
The Dutch intelligence companies advise customers to not share delicate or labeled data by way of messaging apps except particularly accepted.
Additionally they suggest checking the record of units linked to Sign and WhatsApp accounts and instantly eradicating unknown units.
The identical precautions in opposition to electronic mail phishing assaults apply to messaging apps, which embody ignoring unsolicited invites, hyperlinks, or QR codes except they’ve verified their legitimacy by one other trusted communication channel.
Most of these messaging app phishing campaigns aren’t new.
Final 12 months, Google reported that Russian risk actors focused Sign customers by abusing options comparable to gadget linking to achieve entry to victims’ communications.
In December, GenDigital detected a WhatsApp device-linking QR code phishing marketing campaign focusing on customers in Czechia, although it was not attributed to any particular risk actor.



