Our pals at BlackBerry just lately launched an in-depth weblog put up on a marketing campaign by risk actors focusing on on-line cost companies that discusses what occurs from preliminary compromise to the skimmer scripts themselves. You may learn their weblog right here. This weblog is concentrated on what we discovered throughout the AT&T Cybersecurity buyer base as we seemed for the indications of compromise (IOCs) recognized within the BlackBerry weblog and on the quick-follow up evaluation we carried out and supplied to our clients.
As part of the AT&T Managed Menace Detection and Response (MTDR) risk hunter crew, we’ve the distinctive alternative to carry out risk looking throughout our fleet of shoppers in a really quick and environment friendly method. Leveraging the logs throughout tons of of information sources, we will give you our personal hunt hypotheses and develop extraordinarily complicated searches to seek out potential prior incidents and compromises.
We are able to additionally work with the AT&T Alien Labs crew to show that search syntax right into a correlation rule. The Alien Labs crew makes use of this backend knowledge that we collect to create 1000’s of guidelines and signatures inside the USM Wherever platform. Menace hunters also can seek for particular recognized techniques, methods, and procedures (TTPs) and indicators of compromise (IOCs) as we ingest and course of cyber risk intelligence from each open sources (i.e., publicly out there knowledge) and closed sources (i.e., authorities or personal knowledge that isn’t publicly out there).
Once we seemed for the TTPs that the attackers had been utilizing to deploy the bank card skimming scripts, our searches yielded no outcomes, however once we looked for IOCs associated to the place the bank card knowledge was exfiltrated throughout this marketing campaign, we noticed one area come up throughout just a few clients. Armed with key info equivalent to time frames and which clients and customers had been impacted, we may now go deeper into USM Wherever to analyze.
Determine 1 – Net request for bank card skimming exfiltration area
Determine 1 exhibits that the request for the bank card skimming web site referred from one other web site for a well known meals firm with a web-based buying possibility. We noticed this to be the case for all the opposite clients too, with the meals web site being both the direct referer or being the HTTP request proper earlier than the connection to the cdn[.]nightboxcdn[.]com web site. One of many different noticed impacted clients had a consumer’s credit score info skimmed from a unique compromised web site (see Determine 2).
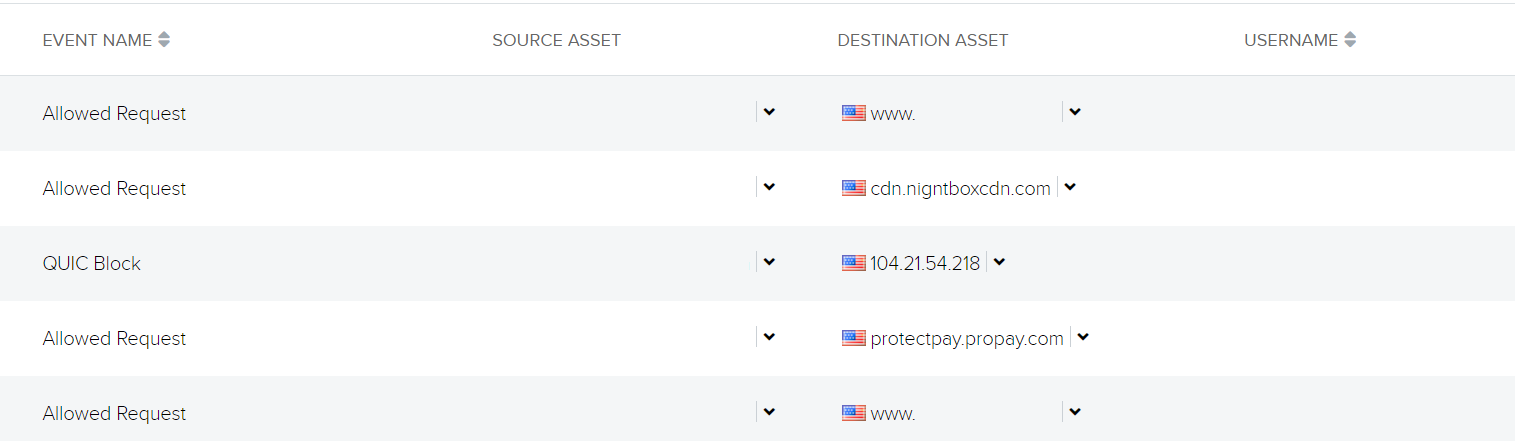
Determine 2 – Visitors going to procuring web site (redacted) adopted by visitors to the skim exfiltration after which a legit cost web site
We are able to see that the consumer is on a web-based procuring web site (redacted) adopted by visitors to the exfiltration area in addition to to a legit cost portal service. We are able to conclude from the visitors stream that the consumer went to checkout and that after they enter their cost particulars, this info went to each the exfiltration web site and the legit cost service, ProPay.
Through the use of the web site scanning software urlscan.io and by a scan of the procuring web site from Might 23, 2023, we may see the skimming script appended to the jquery.hoverIntent.js file (legit script ends after });).
Determine 3 – Skimming script appended to legit script
As soon as we decode the attacker-added code snippet and simplify it right down to its most elementary components, we will see that it extracts the sector values of first title, final title, telephone quantity, electronic mail handle, handle, metropolis, state, zip, card holder title, card quantity, expiration month and yr, and CVV. The info will then be despatched to the exfiltration area by way of a XMLHttpRequest:
Determine 4 – Decoded and simplified skimmer script
After we uncovered what was occurring, we rapidly notified our impacted clients so they might advise their workers to request new bank card numbers from their banks. Whereas it was good to know that our clients weren’t immediately compromised by the risk actor deploying these card skimmer scripts, the assaults exhibit the should be to be continuously conscious of the potential for different organizations to be compromised and the impression this might have on your finish customers.
Leveraging a defense-in-depth technique that features endpoint detection and response instruments, community controls and protection, safety monitoring, and worker education schemes is important to guard towards risk actors that may trigger what you are promoting monetary and reputational loss.
AT&T Cybersecurity has a broad portfolio of managed safety companies that can assist you shield throughout your assault floor. Contact us in case you’d prefer to study extra.