Extra particulars have emerged a few malicious Telegram bot known as Telekopye that is utilized by menace actors to tug off large-scale phishing scams.
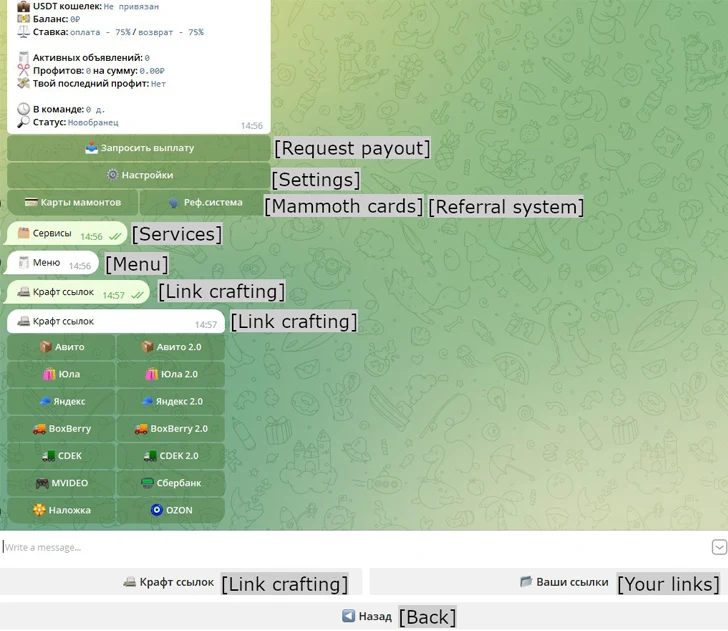
“Telekopye can craft phishing web sites, emails, SMS messages, and extra,” ESET safety researcher Radek Jizba mentioned in a brand new evaluation.
The menace actors behind the operation – codenamed Neanderthals – are identified to run the legal enterprise as a reliable firm, spawning a hierarchical construction that encompasses completely different members who tackle numerous roles.
As soon as aspiring Neanderthals are recruited through ads on underground boards, they’re invited to hitch designated Telegram channels which might be used for speaking with different Neanderthals and maintain monitor of transaction logs.
The last word objective of the operation is to tug off one of many three sorts of scams: vendor, purchaser, or refund.
Within the case of the previous, Neanderthals pose as sellers and attempt to lure unwary Mammoths into buying a non-existent merchandise. Purchaser scams entail the Neaderthals masquerading as consumers in order to dupe the Mammoths (i.e., retailers) into coming into their monetary particulars to half with their funds.
Different eventualities fall right into a class known as refund scams whereby Neaderthals trick the Mammoths a second time underneath the pretext of providing a refund, solely to deduct the identical sum of money once more.
Singapore headquartered cybersecurity agency Group-IB beforehand instructed The Hacker Information that the exercise tracked as Telekopye is identical as Classiscam, which refers to a scam-as-a-service program that has netted the legal actors $64.5 million in illicit income since its emergence in 2019.
“For the Vendor rip-off state of affairs, Neanderthals are suggested to arrange further images of the merchandise to be prepared if Mammoths ask for added particulars,” Jizba famous. “If Neanderthals are utilizing photos they downloaded on-line, they’re purported to edit them to make picture search harder.”
Selecting a Mammoth for a purchaser rip-off is a deliberate course of that takes under consideration the sufferer’s gender, age, expertise in on-line marketplaces, score, opinions, variety of accomplished trades, and the kind of objects they’re promoting, indicating a preparatory stage that includes intensive market analysis.
Additionally utilized by Neanderthals are internet scrapers to sift via on-line market listings and decide a perfect Mammoth who’s prone to fall for the bogus scheme.
Ought to a mammoth want in-person cost and in-person supply for offered items, the Neanderthals declare “they’re too far-off or that they’re leaving town for a enterprise journey for a number of days,” whereas concurrently demonstrating heightened curiosity within the merchandise to extend the probability of success of the rip-off.
Neanderthals have additionally been noticed use VPNs, proxies, and TOR to remain nameless, whereas additionally exploring actual property scams whereby they create bogus web sites with condominium listings and entice Mammoths into paying for a reservation price by clicking on a hyperlink that factors to a phishing web site.
“Neanderthals write to a reliable proprietor of an condominium, pretending to have an interest and ask for numerous particulars, comparable to further photos and how much neighbors the condominium has,” Jizba mentioned.
“The Neanderthals then take all this info and create their very own itemizing on one other web site, providing the condominium for lease. They lower the anticipated market worth by about 20%. The remainder of the state of affairs is an identical to the Vendor rip-off state of affairs.”
The disclosure comes as Examine Level detailed a rug pull rip-off that managed to pilfer almost $1 million by luring unsuspecting victims into investing in pretend tokens and executing simulated trades to create a veneer of legitimacy.
“As soon as the token had sufficiently lured in buyers, the scammer executed the ultimate transfer – withdrawal of liquidity from the token pool, leaving token purchasers with empty palms and depleted funds,” the corporate mentioned.