Malicious Chrome extensions on the Chrome Net Retailer masquerading as productiveness and safety instruments for enterprise HR and ERP platforms had been found stealing authentication credentials or blocking administration pages used to answer safety incidents.
The marketing campaign was found by cybersecurity agency Socket, which says it recognized 5 Chrome extensions concentrating on Workday, NetSuite, and SAP SuccessFactors, collectively put in greater than 2,300 occasions.
“The marketing campaign deploys three distinct assault varieties: cookie exfiltration to distant servers, DOM manipulation to dam safety administration pages, and bidirectional cookie injection for direct session hijacking,” studies Socket.
“The extensions goal the identical enterprise platforms and share similar safety device detection lists, API endpoint patterns, and code buildings, indicating a coordinated operation regardless of showing as separate publishers.”
The extensions had been printed below totally different names however the researchers say they share similar infrastructure, code patterns, and concentrating on. 4 of the extensions had been printed below the developer title databycloud1104, whereas the fifth used totally different branding below the title Software program Entry.
Whereas the extensions affected solely 2,300 customers, the theft of enterprise credentials might gasoline large-scale ransomware and information theft assaults.
Marketed as instruments for enterprise customers
Socket says the extensions had been promoted to customers of enterprise HR and ERP platforms, presenting themselves as instruments designed to enhance productiveness, streamline workflows, or improve safety controls.
A number of of the extensions claimed to supply simplified entry to “premium instruments” for Workday, NetSuite, and different platforms.
One of many extra fashionable extensions, Information By Cloud 2, was put in 1,000 occasions and promoted as a dashboard providing bulk administration instruments and sooner entry for customers managing a number of enterprise accounts.
One other extension, Software Entry 11, positioned itself as a security-focused add-on that may limit entry to delicate administrative options. Its itemizing claimed the extension might restrict consumer interactions with “particular instruments” to forestall account compromise.
Different extensions within the group used comparable language about offering “entry” to instruments and companies, requesting permissions that appeared in line with enterprise integrations.
Nevertheless, Socket says not one of the extensions disclosed cookie extraction, credential exfiltration, or the blocking of safety administration pages. The privateness insurance policies for the extensions additionally didn’t point out that consumer information can be collected.
Socket’s evaluation of the extensions discovered they used a mixture of malicious habits, together with authentication cookie exfiltration, administrative web page blocking, and session hijacking through cookie injection.
A number of extensions repeatedly extracted authentication cookies named “__session” for a focused area, which comprise energetic login tokens for Workday, NetSuite, and SuccessFactors.
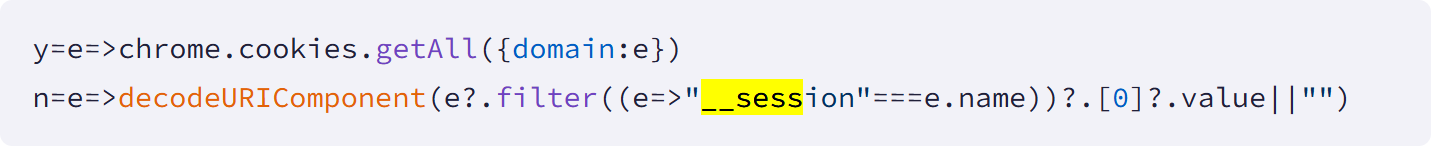
Supply: Socket
These tokens had been exfiltrated each 60 seconds to distant command-and-control servers, permitting attackers to keep up entry even when customers logged out and again in.
Two extensions, Software Entry 11 and Information By Cloud 2, blocked entry to safety and incident response pages inside Workday. Utilizing web page title detection, the extensions both erased content material on the pages or redirected directors from administration pages.
“Software Entry 11 targets 44 administrative pages together with authentication insurance policies, safety proxy configuration, IP vary administration, and session controls,” explains Socket.
“Information By Cloud 2 expands this to 56 pages by including password administration, account deactivation, 2FA machine controls, and safety audit logs.”
Blocking entry to those pages might stop professional directors from responding to safety incidents if one is detected.
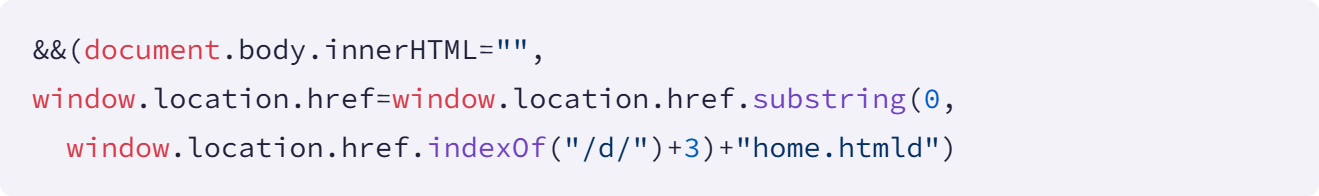
Supply: Socket
Lastly, Socket says the Software program Entry extension carried out essentially the most malicious habits by additionally together with a characteristic that permits bidirectional cookie manipulation. Along with stealing session tokens, the extension might obtain stolen cookies from the attacker’s server and inject them instantly right into a browser.
By setting authentication cookies through the C2, the researchers say that the attackers might take over authenticated classes with out coming into usernames, passwords, or multi-factor authentication codes. Socket says this enabled instant account takeover throughout focused enterprise platforms.
Socket says they reported the extensions to Google, and on the time of publishing this text, they seem to have been taken down.
Anybody who was utilizing these extensions ought to report them to their safety admins for additional incident response and alter their passwords on the focused platforms.
It is funds season! Over 300 CISOs and safety leaders have shared how they’re planning, spending, and prioritizing for the 12 months forward. This report compiles their insights, permitting readers to benchmark methods, establish rising developments, and evaluate their priorities as they head into 2026.
Learn the way prime leaders are turning funding into measurable affect.




