Cloudflare says the variety of hyper-volumetric HTTP DDoS (distributed denial of service) assaults recorded within the third quarter of 2023 surpasses each earlier 12 months, indicating that the menace panorama has entered a brand new chapter.
DDoS assaults are a kind of cyberattack that includes directing massive volumes of rubbish visitors or massive numbers of bogus requests to focused servers internet hosting apps, web sites, and on-line providers to overwhelm and make them unavailable to legit guests.
A Cloudflare report shared with BleepingComputer reveals that, throughout Q3 2023, the web firm mitigated hundreds of hyper volumetric HTTP DDoS assaults.
Over 89 of those assaults exceeded 100 million requests per second (rps), and the biggest one peaked at 201 million rps, 3 times bigger than the earlier report, which occurred in February 2023.
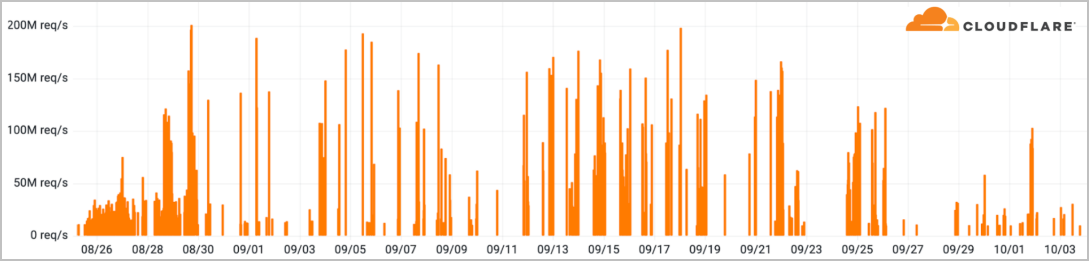
Supply: Cloudflare
These assaults are made attainable by exploiting a brand new method named ‘HTTP/2 Fast Reset,’ which menace actors have leveraged as a zero-day since August 2023.
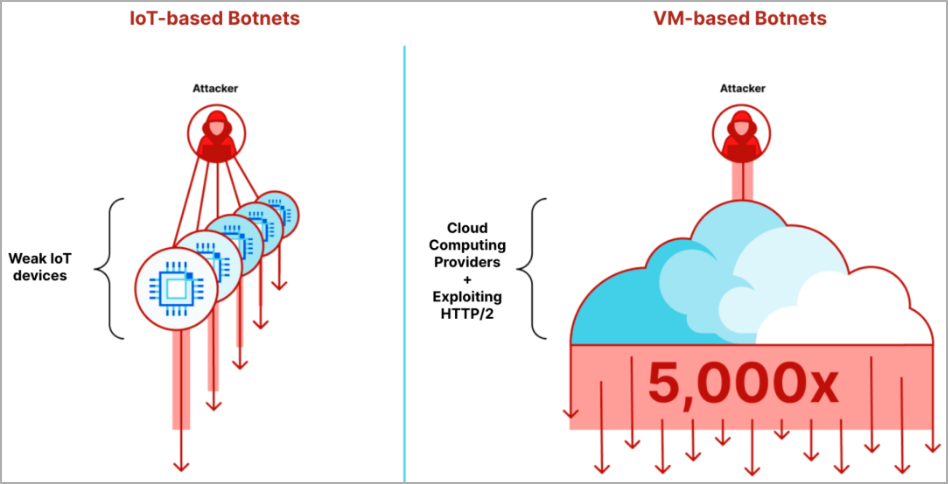
The corporate says HTTP/2 Fast Reset assaults have been using VM-based botnets sized between 5-20 thousand nodes as a substitute of tens of millions of weak IoTs, in a position to ship a way more vital punch per node.
General, Cloudflare experiences a 65% rise within the aggregated quantity of HTTP DDoS assault visitors within the final quarter and a rise of 14% in L3/L4 DDoS assaults.
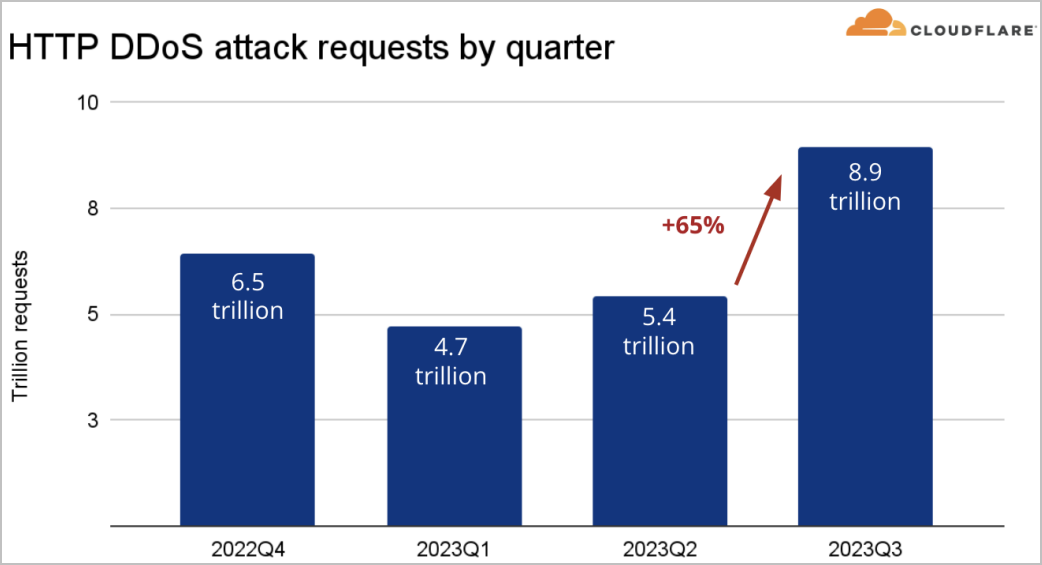
Supply: Cloudflare
Concerning the targets this quarter, gaming and playing entities took the lion’s share of HTTP DDoS, adopted by IT and web providers, cryptocurrency, software program, and telecommunications.
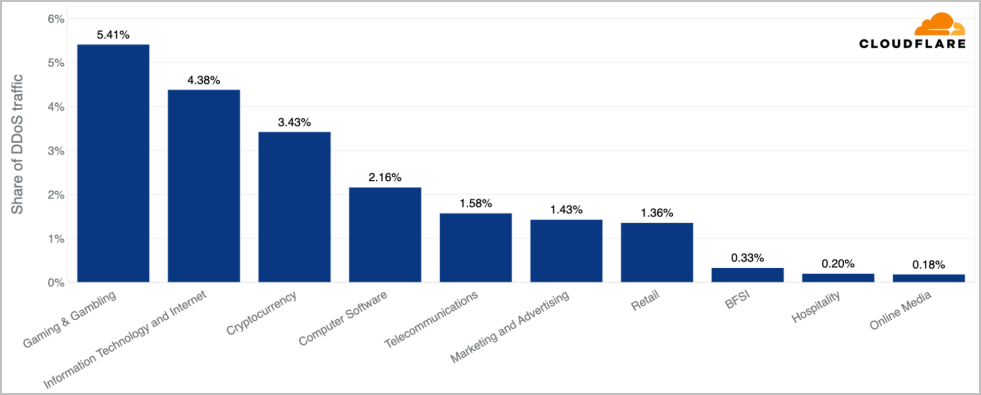
Supply: Cloudflare
Software-layer DDoS assaults, alternatively, largely focused mining corporations, non-profit organizations, prescribed drugs, and the U.S. Federal authorities.
Supply: Cloudflare
Practically 5% of all HTTP DDoS visitors was directed to entities in america, over 3.1% went to corporations in Singapore, and China got here third with 2.2%.
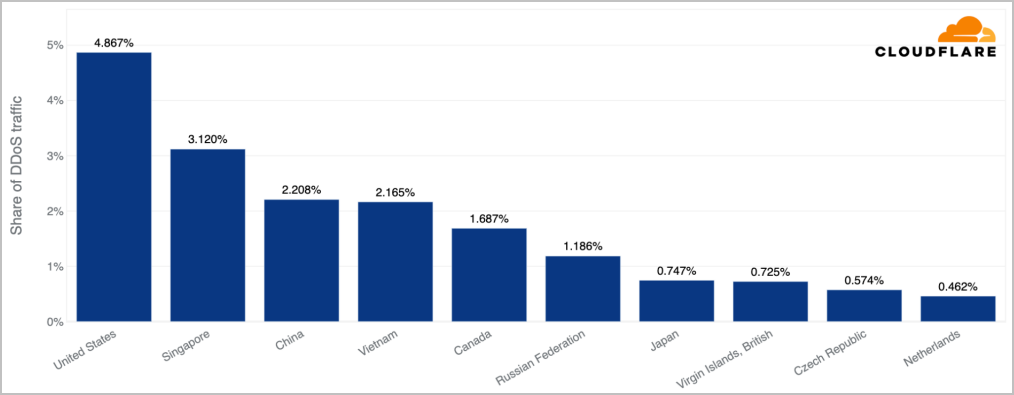
Supply: Cloudflare
Rising tendencies within the DDoS panorama
Cloudflare has additionally noticed tendencies in lesser-known assault vectors that would point out the emergence of latest assault methods.
The primary notable development is a quarterly improve of 456% within the noticed mDNS (multicast DNS) assaults.
MDNS is a UDP-based protocol for service/machine discovery in native networks that attackers exploit for amplification assaults, tricking weak mDNS servers to reply to malicious queries with the goal’s handle.
The second vital improve considerations CoAP (Constrained Software Protocol), which recorded an uptick of 387%.
CoAP is a protocol designed for light-weight communication between easy digital units. Attackers exploit poorly configured units to abuse the protocol’s multicast capabilities and generate undesirable visitors.
The third noticed development is a rise of 303% within the ESP (Encapsulating Safety Payload) DDoS assaults this quarter.
ESP, a part of IPsec, is a safe community communications protocol that may be abused in misconfigured or weak units to amplify DDoS assaults.
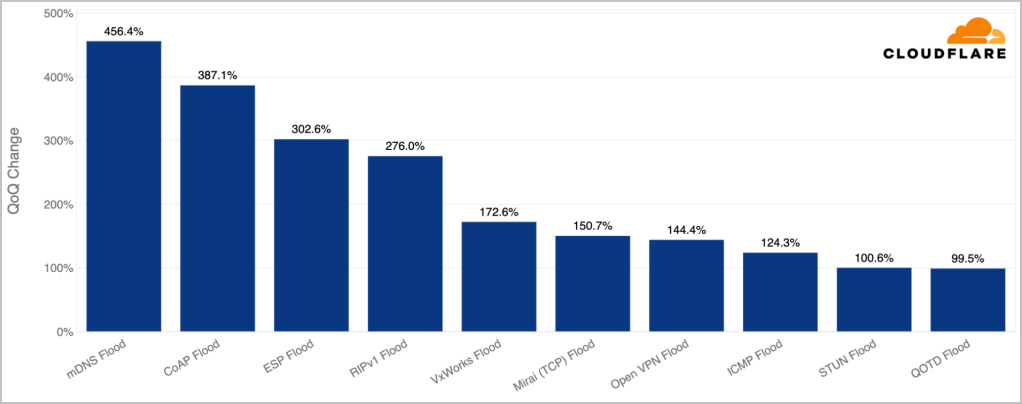
Supply: Cloudflare
Lastly, Cloudflare experiences that ransom DDoS assaults observe a destructive development, falling for the second successive quarter.
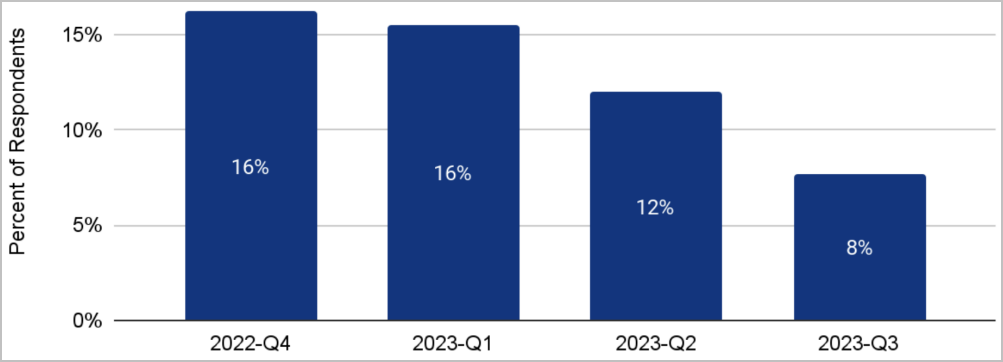
Supply: Cloudflare
DDoS assaults consistently evolve as menace actors adapt and discover new methods to avoid fashionable defenses. Moreover, hacktivist teams have more and more used DDoS assaults to focus on political entities or a rustic’s organizations that they’re protesting.
The simplest protection technique encompasses a complete, multi-layered strategy to boost DDoS resilience. Nonetheless, as new methods emerge, firms and safety firms might want to evolve their protection methods.


