Cloudflare has shared extra particulars a few latest 25-minute Border Gateway Protocol (BGP) route leak affecting IPv6 site visitors, which triggered measurable congestion, packet loss, and roughly 12 Gbps of dropped site visitors.
The BGP system helps route knowledge throughout completely different networks referred to as autonomous techniques (AS) that ship it to vacation spot by way of smaller networks on the web.
The incident was attributable to an unintentional coverage misconfiguration on a router and affected exterior networks past Cloudflare prospects.
“Throughout the incident on January 22, we triggered an identical sort of route leak, by which we took routes from a few of our friends and redistributed them in Miami to a few of our friends and suppliers,” reads the Cloudflare announcement.
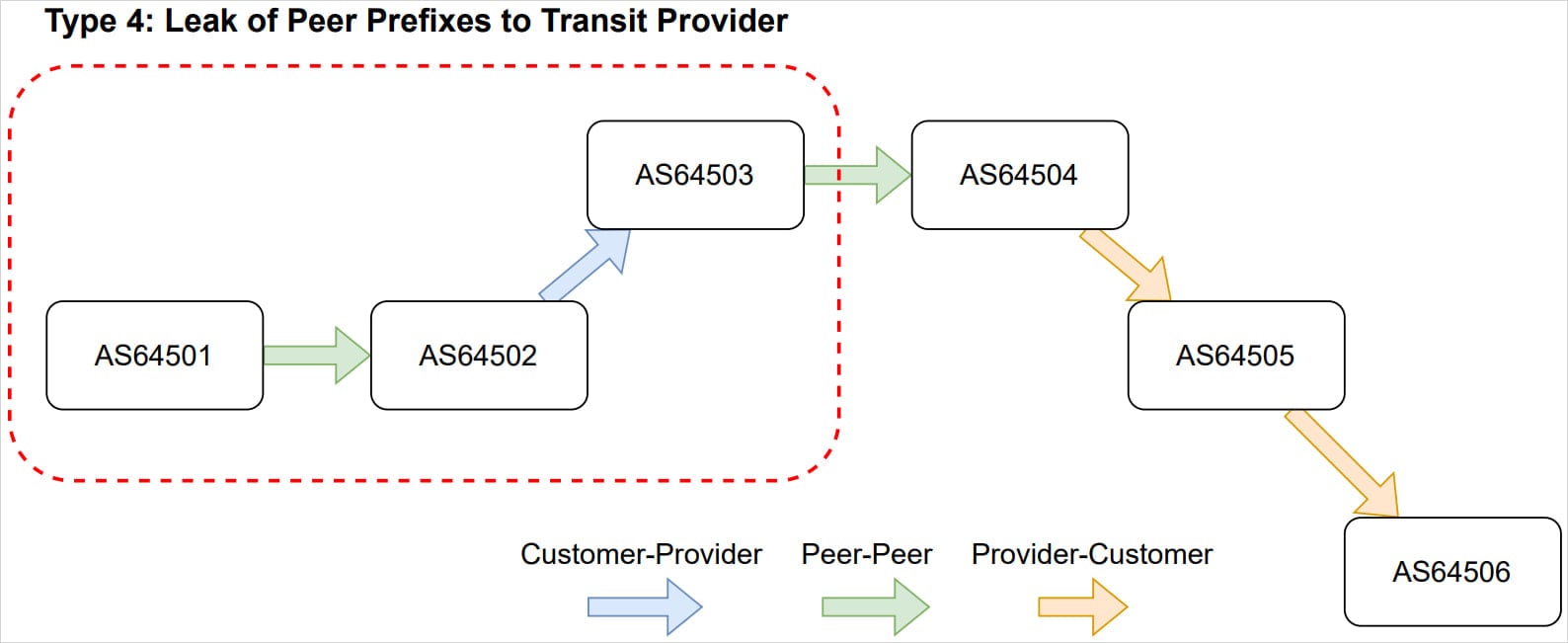
“Based on the route leak definitions in RFC7908, we triggered a combination of Kind 3 and Kind 4 route leaks on the Web.”
Supply: Cloudflare
A BGP route leak happens when an Autonomous System (AS) violates valley-free routing insurance policies by incorrectly promoting routes realized from one peer or supplier to a different peer or supplier.
Because of this, site visitors is distributed by way of a community that was by no means supposed to hold it. This usually causes congestion, drops, or suboptimal paths. When firewall filters are used to simply accept site visitors solely from particular suppliers, the site visitors is totally discarded.
Valley-free guidelines describe how routes are presupposed to be propagated based mostly on enterprise relationships between networks, and when they’re violated, site visitors is interested in networks that may’t carry it by way of longer or unstable paths, and, like on this case, dropped completely.
Though such incidents primarily trigger reliability points, they do have a safety dimension, as they’ll result in unauthorized events intercepting and analyzing site visitors in BGP hijacking incidents.
Cloudflare defined that the foundation reason for the BGP route leak was a coverage change supposed to forestall Miami from promoting Bogotá IPv6 prefixes.
Eradicating particular prefix lists made the export coverage overly permissive, permitting a route-type inside match to simply accept all inside (iBGP) IPv6 routes and export them externally.
“Because of this, all IPv6 prefixes that Cloudflare redistributes internally throughout the spine have been accepted by this coverage, and marketed to all our BGP neighbors in Miami,” defined Cloudflare.

Supply: Cloudflare
Cloudflare detected the issue shortly after it appeared, and its engineers manually reverted the configuration and paused automation, stopping the impression inside 25 minutes. The triggering code change was later reverted, and automation was safely re-enabled.
The web large says that this newest case is similar to a July 2020 incident and has additionally listed measures to forestall such occurrences sooner or later.
The proposed measures embrace including stricter community-based export safeguards, CI/CD checks for coverage errors, improved early detection, validating RFC 9234, and selling RPKI ASPA adoption.




