A brand new set of malicious Python packages has slithered their option to the Python Bundle Index (PyPI) repository with the final word goal of stealing delicate info from compromised developer methods.
The packages masquerade as seemingly innocuous obfuscation instruments, however harbor a bit of malware known as BlazeStealer, Checkmarx stated in a report shared with The Hacker Information.
“[BlazeStealer] retrieves a further malicious script from an exterior supply, enabling a Discord bot that provides attackers full management over the sufferer’s pc,” safety researcher Yehuda Gelb stated.
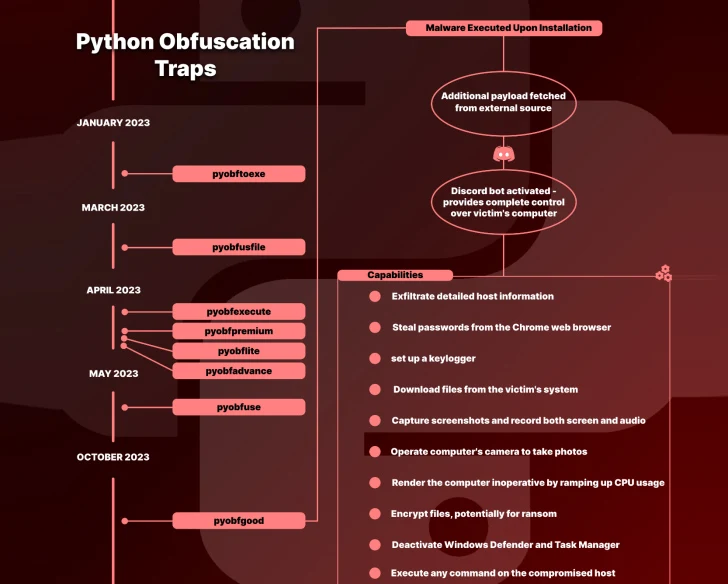
The marketing campaign, which commenced in January 2023, entails a complete of eight packages named Pyobftoexe, Pyobfusfile, Pyobfexecute, Pyobfpremium, Pyobflite, Pyobfadvance, Pyobfuse, and pyobfgood, the final of which was revealed in October.
These modules include setup.py and init.py information which might be designed to retrieve a Python script hosted on switch[.]sh, which will get executed instantly upon their set up.
Known as BlazeStealer, the malware runs a Discord bot and permits the risk actor to reap a variety of data, together with passwords from net browsers and screenshots, execute arbitrary instructions, encrypt information, and deactivate Microsoft Defender Antivirus on the contaminated host.
What’s extra, it could render the pc unusable by ramping up CPU utilization, inserting a Home windows Batch script within the startup listing to close down the machine, and even forcing a blue display of demise (BSoD) error.
“It stands to purpose that builders engaged in code obfuscation are seemingly coping with priceless and delicate info, and subsequently, to a hacker, this interprets to a goal price pursuing,” Gelb famous.
A majority of downloads related to the rogue packages originated from the U.S., adopted by China, Russia, Eire, Hong Kong, Croatia, France, and Spain. They had been collectively downloaded 2,438 occasions earlier than being taken down.
“The open-source area stays a fertile floor for innovation, but it surely calls for warning,” Gelb stated. “Builders should stay vigilant, and vet the packages previous to consumption.”
The event comes as software program provide chain safety agency Phylum found a set of crypto-themed npm modules – puma-com, erc20-testenv, blockledger, cryptotransact, and chainflow – with capabilities to stealthily ship a next-stage malware.
In recent times, open-source repositories have emerged as a profitable means for risk actors to unfold malware. In line with Phylum’s Evolution of Software program Provide Chain Safety Report for Q3 2023, 13,708 packages throughout a number of ecosystems had been discovered to execute suspicious code throughout set up.
“1,481 packages surreptitiously downloaded and executed code from a distant supply,” the corporate stated final month. “10,201 packages referenced recognized malicious URLs, [and] 2,598 typosquat packages had been recognized.”