
Safety researchers developed a brand new assault, which they named AutoSpill, to steal account credentials on Android through the autofill operation.
In a presentation on the Black Hat Europe safety convention, researchers from the Worldwide Institute of Data Know-how (IIIT) at Hyderabad mentioned that their exams confirmed that the majority password managers for Android are weak to AutoSpill, even when there is no such thing as a JavaScript injection.
How AutoSpill works
Android apps usually use WebView controls to render net content material, akin to login pages inside the app, as an alternative of redirecting the customers to the principle browser, which might be a extra cumbersome expertise on small-screen units.
Password managers on Android use the platform’s WebView framework to robotically kind in a consumer’s account credentials when an app hundreds the login web page to companies like Apple, Fb, Microsoft, or Google.
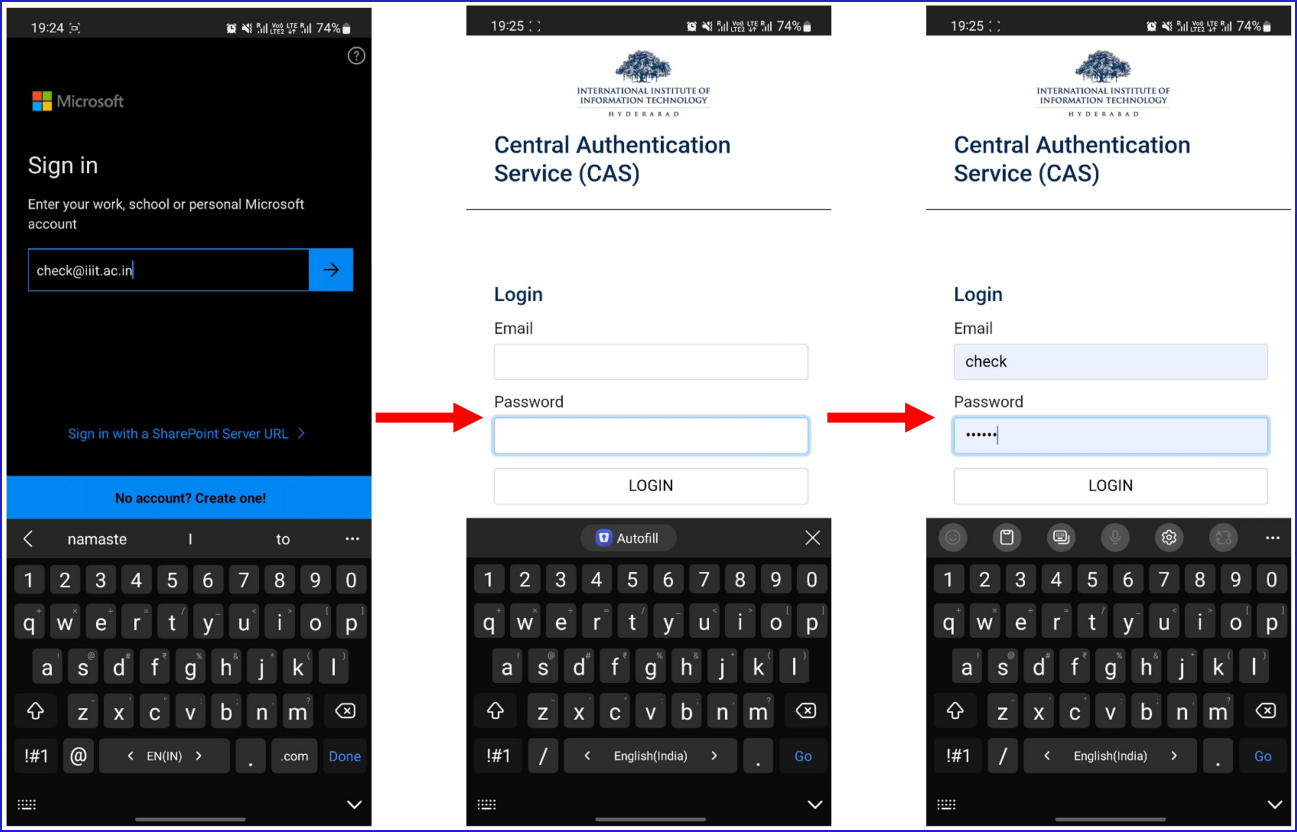
The researchers mentioned that it’s potential to use weaknesses on this course of to seize the auto-filled credentials on the invoking app, even with out JavaScript injection.
If JavaScript injections are enabled, the researchers say that each one password managers on Android are weak to the AutoSpill assault.
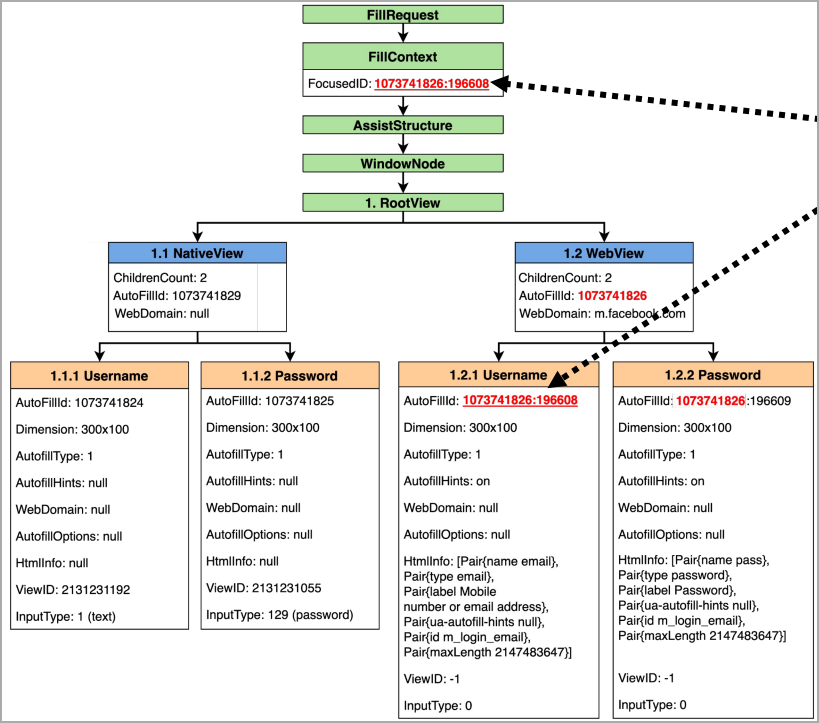
Particularly, the AutoSpill challenge stems from Android’s failure to implement or to obviously outline the accountability for the safe dealing with of the auto-filled information, which can lead to leaking it or being captured by the host app.
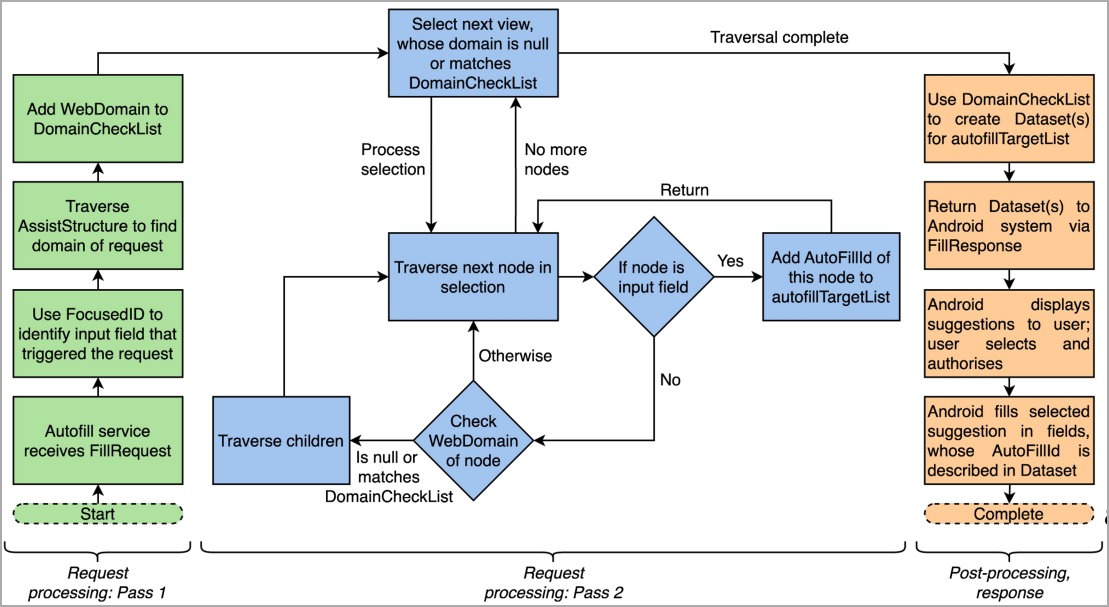
In an assault situation, a rogue app serving a login kind might seize the consumer’s credentials with out leaving any indication of the compromise. Further technical particulars concerning the AutoSpill assault can be found within the researchers’ slides from the Black Hat Europe presentation.
Extra particulars concerning the AutoSpill assault might be present in this doc, which comprises slides from the BlackHat presentation.
Affect and fixing
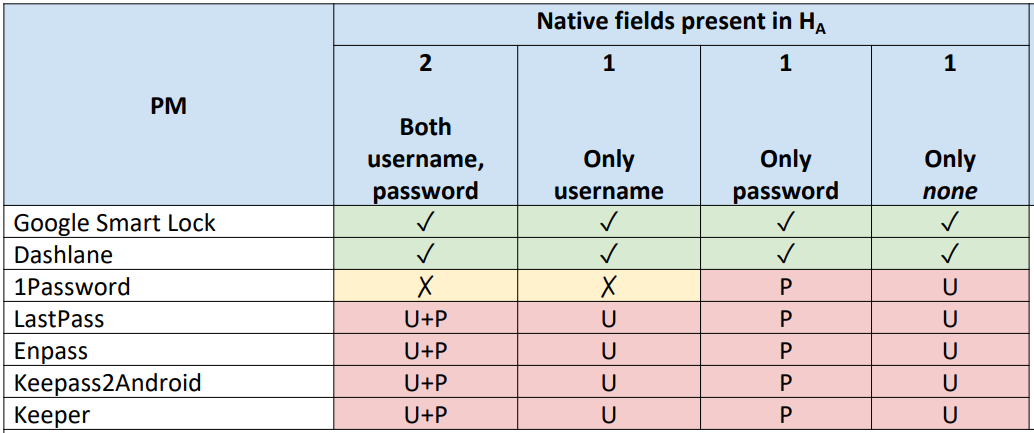
The researchers examined AutoSpill towards a number of password managers on Android 10, 11, and 12 and located that 1Password 7.9.4, LastPass 5.11.0.9519, Enpass 6.8.2.666, Keeper 16.4.3.1048, and Keepass2Android 1.09c-r0 are inclined to assaults on account of utilizing Android’s autofill framework.
Google Good Lock 13.30.8.26 and the DashLane 6.2221.3 adopted a unique technical method for the autofill course of. They did not leak delicate information to the host app except JavaScript injection was used.
The researchers disclosed their findings to impacted software program distributors and Android’s safety staff and shared their proposals for addressing the issue. Their report was acknowledged as legitimate, however no particulars about fixing plans have been shared.
BleepingComputer has contacted a number of suppliers of password administration merchandise which are impacted by AutoSpill, in addition to Google, asking about their plans to deal with the difficulty and we obtained the next feedback to this point:
Many individuals have develop into accustomed to utilizing autofill to shortly and simply enter their credentials. By a malicious app put in on the consumer’s gadget, a hacker could lead on a consumer to unintentionally autofill their credentials. AutoSpill highlights this downside.
Maintaining our prospects’ most vital information secure is our utmost precedence at 1Password. A repair for AutoSpill has been recognized and is at present being labored on.
Whereas the repair will additional strengthen our safety posture, 1Password’s autofill operate has been designed to require the consumer to take express motion.
The replace will present further safety by stopping native fields from being crammed with credentials which are solely meant for Android’s WebView. – 1Password spokesperson
In 2022, we engaged with Dr. Gangwal by way of Bugcrowd, our bug bounty program accomplice. We analyzed the findings he submitted and located it to be a low-risk vulnerability because of the mechanisms required for it to be exploited.
What’s vital to notice right here is that this vulnerability requires the power and alternative to put in a malicious app on the goal gadget, which might point out an entire compromise or the power to execute code on the focused gadget.
Previous to receiving Dr. Gangwal’s findings, LastPass already had a mitigation in place by way of an in-product pop-up warning when the app detected an try to leverage the exploit. After analyzing the findings, we added extra informative wording within the pop-up.
We confirmed this replace with Dr. Gangwal however didn’t obtain any acknowledgement of our replace. – LastPass spokesperson
On Might 31, 2022, Keeper obtained a report from the researcher a couple of potential vulnerability. We requested a video from the researcher to show the reported challenge. Based mostly upon our evaluation, we decided the researcher had first put in a malicious utility and subsequently, accepted a immediate by Keeper to power the affiliation of the malicious utility to a Keeper password document.
Keeper has safeguards in place to guard customers towards robotically filling credentials into an untrusted utility or a website that was not explicitly licensed by the consumer. On the Android platform, Keeper prompts the consumer when making an attempt to autofill credentials into an Android utility or web site. The consumer is requested to verify the affiliation of the applying to the Keeper password document previous to filling any data. On June 29, we knowledgeable the researcher of this data and likewise beneficial that he submit his report back to Google since it’s particularly associated to the Android platform.
Typically, a malicious Android utility would first have to be submitted to Google Play Retailer, reviewed by Google and subsequently, accredited for publication to the Google Play Retailer. The consumer would then want to put in the malicious utility from Google Play and transact with the applying. Alternatively, the consumer would want to override vital safety settings on their gadget with the intention to sideload a malicious utility.
Keeper all the time recommends that people be cautious and vigilant concerning the functions they set up and will solely set up printed Android functions from trusted app shops such because the Google Play Retailer. – Craig Lurey, CTO and co-founder of Keeper Safety
WebView is utilized in a wide range of methods by Android builders, which embody internet hosting login pages for their very own companies of their apps. This challenge is said to how password managers leverage the autofill APIs when interacting with WebViews.
We advocate third-party password managers be delicate as to the place passwords are being inputted, and we’ve got WebView greatest practices that we advocate all password managers implement. Android gives password managers with the required context to differentiate between native views and WebViews, in addition to whether or not the WebView being loaded is just not associated to the internet hosting app.
For instance, when utilizing the Google Password Supervisor for autofill on Android, customers are warned if they’re coming into a password for a site Google determines is probably not owned by the internet hosting app, and the password is simply stuffed in on the right discipline. Google implements server aspect protections for logins by way of WebView. – Google spokesperson


