The ASUS DriverHub driver administration utility was susceptible to a essential distant code execution flaw that allowed malicious websites to execute instructions on units with the software program put in.
The flaw was found by an impartial cybersecurity researcher from New Zealand named Paul (aka “MrBruh“), who discovered that the software program had poor validation of instructions despatched to the DriverHub background service.
This allowed the researcher to create an exploit chain using flaws tracked as CVE-2025-3462 and CVE-2025-3463 that, when mixed, obtain origin bypass and set off distant code execution on the goal.
The DriverHub drawback
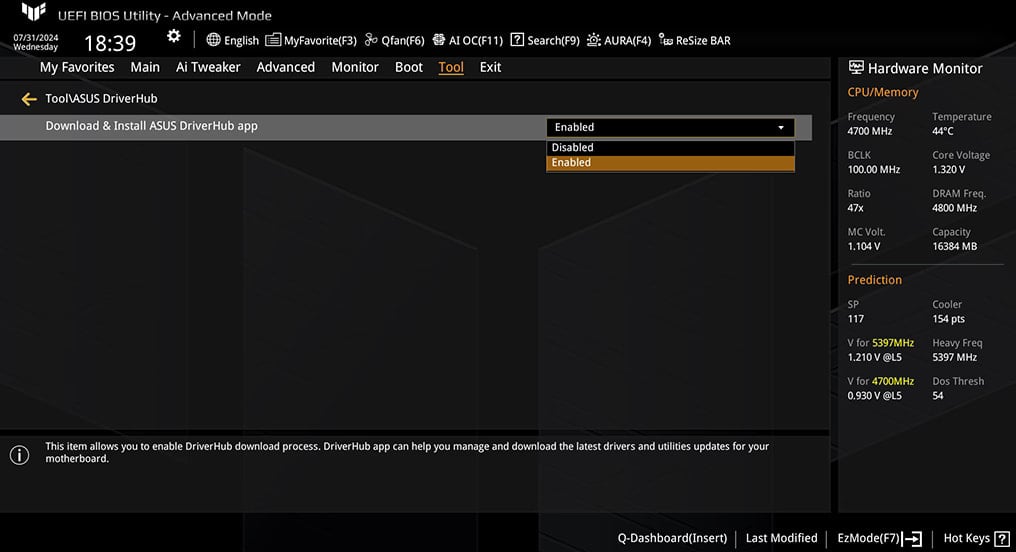
DriverHub is ASUS’s official driver administration software that’s routinely put in on the primary system boot when using sure ASUS motherboards.
This software program runs within the background, routinely detecting and fetching the newest driver variations for the detected motherboard mannequin and its chipset.
As soon as put in, the software stays lively and operating within the background through a neighborhood service on port 53000, frequently checking for essential driver updates.
In the meantime, most customers do not even know such a service is consistently operating on their system.
That service checks the Origin Header of incoming HTTP requests to reject something that does not come from ‘driverhub.asus.com.’
Nonetheless, this verify is poorly applied, as any web site that features that string is accepted even when it is not an actual match to ASUS’s official portal.
The second problem lies within the UpdateApp endpoint, which permits DriverHub to obtain and run .exe recordsdata from “.asus.com” URLs with out person affirmation.
Supply: MrBruh
Stealthy assault move
An attacker can goal any person with ASUS DriverHub operating on their system to trick them into visiting a malicious web site on their browser. This web site then sends “UpdateApp requests” to the native service at ‘http://127.0.0.1:53000.’
By spoofing the Origin Header to one thing like ‘driverhub.asus.com.mrbruh.com,’ the weak validation verify is bypassed, so DriverHub accepts the instructions.
Within the researcher’s demonstration, the instructions order the software program to obtain a professional ASUS-signed ‘AsusSetup.exe’ installer from the seller’s obtain portal, together with a malicious .ini file and .exe payload.
The ASUS-signed installer is silently run as admin and makes use of the configuration info within the .ini file. This ini file directs the professional ASUS driver installer to launch the malicious executable file.
The assault can be made doable by the software failing to delete recordsdata that fail signature checks, just like the .ini and payload, that are saved on the host after their obtain.
ASUS’ response and person motion
ASUS acquired the researcher’s reviews on April 8, 2025, and applied a repair on April 18, after validating it with MrBruh the day earlier than. The {hardware} big didn’t provide the researcher any bounty for his disclosure.
The CVE descriptions, which the Taiwanese vendor submitted, considerably downplays the difficulty with the next assertion:
“This problem is proscribed to motherboards and doesn’t have an effect on laptops, desktop computer systems, or different endpoints,” reads the CVE description.
That is complicated, because the talked about CVEs impression laptops and desktop computer systems with DriverHub put in.
Nonetheless, ASUS is clearer in its safety bulletin, advising customers to rapidly apply the newest replace.
“This replace contains essential safety updates and ASUS strongly recommends that customers replace their ASUS DriverHub set up to the newest model,” reads the bulletin.
“The most recent Software program Replace could be accessed by opening ASUS DriverHub, then clicking the “Replace Now” button.”
MrBruh says he monitored certificates transparency updates and located no different TLS certificates containing the “driverhub.asus.com” string, indicating it was not exploited within the wild.
In case you’re uncomfortable with a background service routinely fetching doubtlessly harmful recordsdata upon visiting web sites, chances are you’ll disable DriverHub out of your BIOS settings.



