In what is the newest evolution of risk actors abusing authentic infrastructure for nefarious ends, new findings present that nation-state hacking teams have entered the fray in leveraging the social platform for focusing on essential infrastructure.
Discord, in recent times, has grow to be a profitable goal, appearing as a fertile floor for internet hosting malware utilizing its content material supply community (CDN) in addition to permitting data stealers to siphon delicate information off the app and facilitating information exfiltration by way of webhooks.
“The utilization of Discord is basically restricted to data stealers and grabbers that anybody should purchase or obtain from the Web,” Trellix researchers Ernesto Fernández Provecho and David Pastor Sanz stated in a Monday report.
However that could be altering, for the cybersecurity agency stated it discovered proof of an artifact focusing on Ukrainian essential infrastructures. There’s presently no proof linking it to a recognized risk group.
“”The potential emergence of APT malware campaigns exploiting Discord’s functionalities introduces a brand new layer of complexity to the risk panorama,” the researchers famous.
The pattern is a Microsoft OneNote file distributed through an e mail message impersonating the non-profit dobro.ua.
The file, as soon as opened, incorporates references to Ukrainian troopers to trick recipients into donating by clicking on a booby-trapped button, ensuing within the execution of Visible Fundamental Script (VBS) designed to extract and run a PowerShell script as a way to obtain one other PowerShell script from a GitHub repository.
For its half, within the ultimate stage, PowerShell takes benefit of a Discord webhook to exfiltrate system metadata.
“The truth that the one purpose of the ultimate payload is acquiring details about the system signifies that the marketing campaign continues to be in an early stage, which additionally matches with the utilization of Discord as [command-and-control],” the researchers stated.
“Nonetheless, you will need to spotlight that the actor may ship a extra subtle piece of malware to the compromised programs sooner or later by modifying the file saved within the GitHub repository.”
Trellix’s evaluation additional revealed that loaders similar to SmokeLoader, PrivateLoader, and GuLoader are among the many most prevalent malware households that make the most of Discord’s CDN to obtain a next-stage payload, together with stealers like RedLine, Vidar, Agent Tesla, and Umbral.
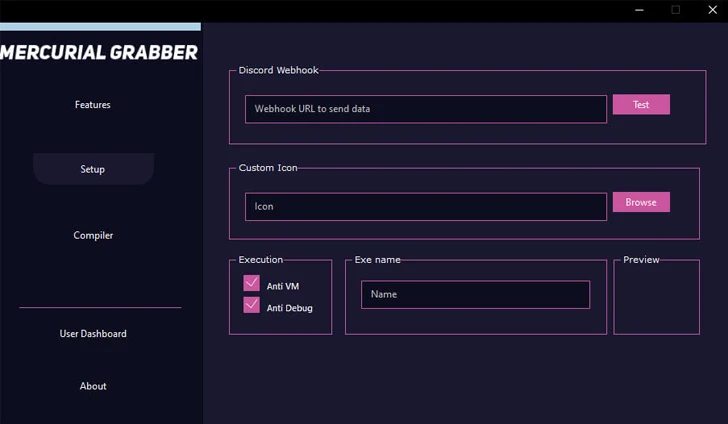
On high of that, a few of the frequent malware households which have been noticed utilizing Discord webhooks are Mercurial Grabber, Stealerium, Typhon Stealer, and Venom RAT.
“The abuse of Discord’s CDN as a distribution mechanism for extra malware payloads showcases the adaptability of cybercriminals to use collaborative purposes for his or her achieve,” the researchers stated.
“APTs are recognized for his or her subtle and focused assaults, and by infiltrating broadly used communication platforms like Discord, they will effectively set up long-term footholds inside networks, placing essential infrastructure and delicate information in danger.”