Microsoft on Tuesday launched patches for 57 vulnerabilities, together with 31 for Home windows. Eleven different product teams are additionally affected. Of the 57 CVEs addressed, simply 3 are thought-about Crucial in severity; 2 of these are in Home windows, whereas the third falls in Azure. One CVE, an Vital-severity elevation-of-privilege concern (CVE-2023-36049), impacts each .NET and Visible Studio; one other Vital-severity EoP impacts .NET, Visible Studio, and in addition ASP.NET.
At press time, three Home windows points are identified to be beneath exploit within the wild. (Or, relying on the way you depend these items, there are 4, as we’ll focus on within the Notable November Updates part under.) An extra 10 vulnerabilities in Home windows, Change, Workplace, and SharePoint are by the corporate’s estimation extra more likely to be exploited within the subsequent 30 days, with the Workplace vulnerability (CVE-2023-36413, a safety function bypass) publicly disclosed already.
Along with the 57 CVEs, Microsoft lists one official advisory, ADV990001, which covers their newest servicing stack updates. Nonetheless, the listing of information-only advisories is intensive this month. Along with 21 CVEs affecting Edge/Chromium (six of these Edge-specific), there’s data on an industry-wide concern affecting BlueTooth; an HTTP/2-related concern, presently beneath lively exploit within the wild, touching Home windows, ASP.NET, .NET and Visible Studio; 5 CBL-Mariner-related issued lined by CVEs from Kubernetes, Purple Hat, and MITRE; 17 Adobe-issued patches for Acrobat Reader, and 7 extra patches from Adobe for ColdFusion.
We don’t embody these 53 points within the CVE counts and graphics under, however we’ll present data on every little thing in an appendix on the finish of the article. We’re as traditional together with on the finish of this submit three appendices itemizing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product household.
Along with all of this, Home windows Server 2022, 23H2 Version (Server Core set up) is launched as a part of this replace.
By the numbers
- Whole Microsoft CVEs: 57
- Whole Microsoft advisories transport in replace: 1
- Whole different advisory points lined in replace: 52
- Publicly disclosed: 3
- Exploited: 3 plus one in non-Microsoft advisory concern
- Severity
- Crucial: 3
- Vital: 54
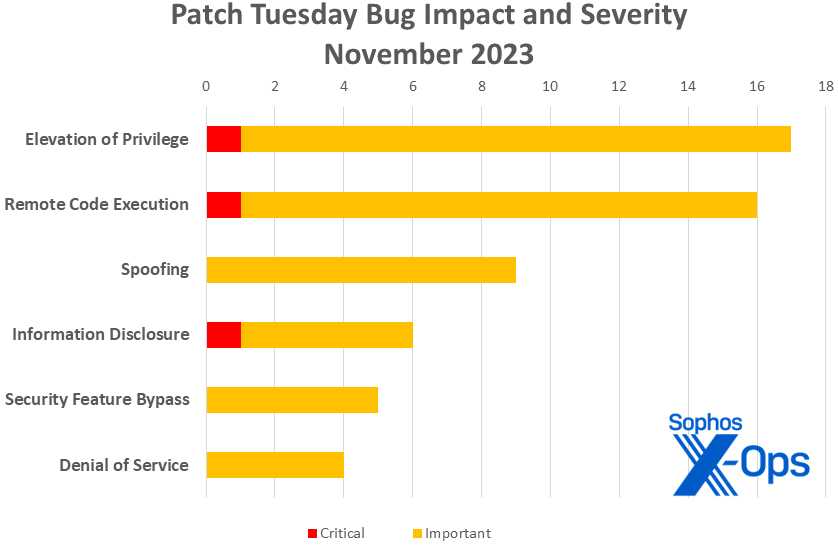
- Influence
- Elevation of Privilege: 17
- Distant Code Execution: 16
- Spoofing: 9
- Data Disclosure: 6
- Safety Function Bypass: 5
- Denial of Service: 4
Determine 1: This month elevation of privilege points have been barely extra prevalent than distant code execution for a change; spoofing additionally makes a powerful exhibiting
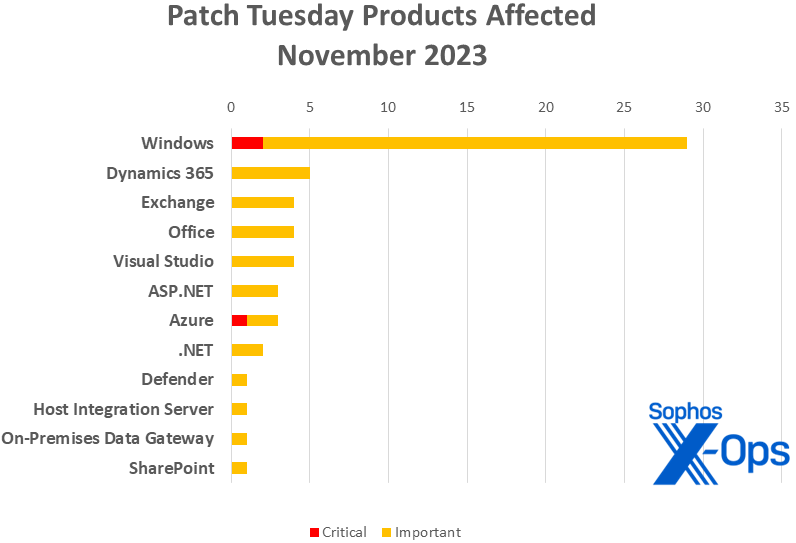
Merchandise
- Home windows: 31
- Dynamics 365: 5
- Change: 4
- Workplace: 4
- Visible Studio: 4, together with one shared with .NET and one shared with ASP.NET and .NET
- ASP.NET: 3, together with one shared with .NET and Visible Studio
- Azure: 3
- .NET: 2 (one shared with Visible Studio and one shared with ASP.NET and Visible Studio)
- Defender: 1
- Host Integration Server: 1
- On-Premises Information Gateway: 1
- SharePoint: 1
Determine 2: Home windows as traditional takes the lion’s share of patches in November, however there’s a reasonably huge number of extra specialised merchandise affected. (Within the case of patches touching a couple of product, every occasion is represented on this chart; as an example, CVE-2023-36049, which impacts each Visible Studio and .NET, is counted as soon as for every of the 2)
Notable November updates
Along with the problems mentioned above, a couple of attention-grabbing objects current themselves.
CVE-2023-36025 — Home windows SmartScreen Safety Function Bypass Vulnerability
There are three Home windows CVEs this month for which lively exploitation has been detected within the wild. (Or 4; extra on that in a minute.) This one, an Vital-class safety function bypass, has the very best CVSS base and temporal scores (Base 8.8 / Temporal 8.2) of the trio. All it takes is a malicious URL, and the attacker is ready to bypass Home windows Defender SmartScreen checks and the prompts the consumer would count on to see with these.
CVE-2023-36397 — Home windows Pragmatic Common Multicast (PGM) Distant Code Execution Vulnerability
Is message queuing enabled in your system? This vulnerability, which will be triggered by an attacker sending a maliciously crafted file over the community, is critical-severity (CVSS 3.1 9.8/8.5) and may result in RCE. Along with the opposite protections launched for this, Microsoft notes that customers can verify their publicity by checking to see if the service known as Message Queuing is operating, and if TCP port 1801 is in listening mode.
CVE-2020-8554, CVE-2023-46753, CVE-2023-46316, CVE-2020-14343, CVE-2020-1747 (5 CVEs)
These 5 CVEs usually are not a part of Microsoft’s official launch, however nobody utilizing Microsoft’s CBL-Mariner (Widespread Base Linux Mariner) ought to sleep on them. CBL-Mariner is Microsoft’s personal Linux distro; first developed in-house for inside growth and Azure administration. The distro was quietly made publicly accessible to the general public final 12 months. Not one of the three CVEs are straight from Microsoft, however from Kubernetes (CVE-2020-8554), Purple Hat (CVE-2020-14343, CVE-2020-1747), and MITRE (CVE-2023-46316, CVE-2023-46753). As a result of obvious age of a number of of those CVEs and their severity – three of the 5 have a CVSS base rating of 9.8 out of 10 – customers are inspired to maintain themselves updated.
CVE-2023-24023 — MITRE: CVE-2023-24023 Bluetooth Spoofing Vulnerability
CVE-2023-44487 — MITRE: CVE-2023-44487 HTTP/2 Speedy Reset Assault
Talking of MITRE, the group options in two extra CVEs about which Microsoft is publishing data. As one would count on, the MITRE CVEs are relevant for a lot of firms, not solely Microsoft. CVE-2023-24023 covers an important-severity spoofing vulnerability reported to BlueTooth’s governing physique. As for CVE-2023-44487, this CVE makes an uncommon repeat look on the Patch Tuesday roster; readers might keep in mind that we mentioned this Speedy Reset concern in final month’s roundup. It impacts Home windows, ASP.NET, .NET, and Visible Studio.
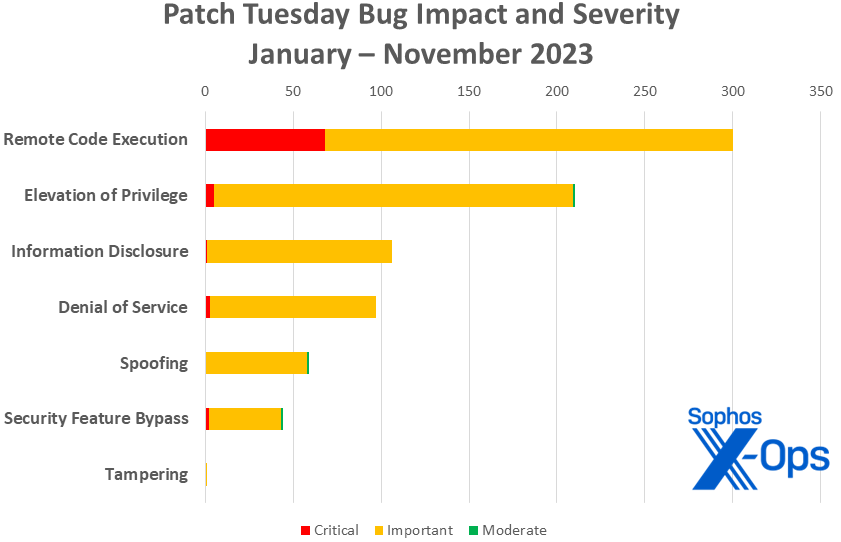
Determine 3: With one month to go in 2023, the tally of distant code execution patches releases reaches 300. In the meantime, it’s barely seen, however the 12 months’s first critical-level information-disclosure concern exhibits on the chart
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2023-36033 | Exp/2336033-A | Exp/2336033-A |
| CVE-2023-36036 | Exp/2336036-A | Exp/2336036-A |
| CVE-2023-36394 | Exp/2336394 | Exp/2336394 |
| CVE-2023-36399 | Exp/2336399-A | Exp/2336399-A |
| CVE-2023-36413 | sid:2309050 | sid:2309050 |
| CVE-2023-36424 | Exp/2336424-A | Exp/2336424-A |
As you possibly can each month, if you happen to don’t wish to wait on your system to tug down Microsoft’s updates itself, you possibly can obtain them manually from the Home windows Replace Catalog web site. Run the winver.exe software to find out which construct of Home windows 10 or 11 you’re operating, then obtain the Cumulative Replace bundle on your particular system’s structure and construct quantity.
Appendix A: Vulnerability Influence and Severity
It is a listing of November’s patches sorted by influence, then sub-sorted by severity. Every listing is additional organized by CVE.
Elevation of Privilege (17 CVEs)
| Crucial severity | |
| CVE-2023-36400 | Home windows HMAC Key Derivation Elevation of Privilege Vulnerability |
| Vital severity | |
| CVE-2023-36033 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-36047 | Home windows Authentication Elevation of Privilege Vulnerability |
| CVE-2023-36049 | .NET, .NET Framework, and Visible Studio Elevation of Privilege Vulnerability |
| CVE-2023-36394 | Home windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36399 | Home windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36403 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36405 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36407 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36408 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36422 | Microsoft Home windows Defender Elevation of Privilege Vulnerability |
| CVE-2023-36424 | Home windows Widespread Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36427 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Safety Function Bypass Vulnerability |
| CVE-2023-36705 | Home windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-36719 | Microsoft Speech Software Programming Interface (SAPI) Elevation of Privilege Vulnerability |
Distant Code Execution (16 CVEs)
| Crucial severity | |
| CVE-2023-36397 | Home windows Pragmatic Common Multicast (PGM) Distant Code Execution Vulnerability |
| Vital severity | |
| CVE-2023-36017 | Home windows Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2023-36028 | Microsoft Protected Extensible Authentication Protocol (PEAP) Distant Code Execution Vulnerability |
| CVE-2023-36041 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2023-36042 | Visible Studio Denial of Service Vulnerability |
| CVE-2023-36045 | Microsoft Workplace Graphics Distant Code Execution Vulnerability |
| CVE-2023-36393 | Home windows Person Interface Software Core Distant Code Execution Vulnerability |
| CVE-2023-36396 | Home windows Compressed Folder Distant Code Execution Vulnerability |
| CVE-2023-36401 | Microsoft Distant Registry Service Distant Code Execution Vulnerability |
| CVE-2023-36402 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
| CVE-2023-36423 | Microsoft Distant Registry Service Distant Code Execution Vulnerability |
| CVE-2023-36425 | Home windows Distributed File System (DFS) Distant Code Execution Vulnerability |
| CVE-2023-36437 | Azure DevOps Server Distant Code Execution Vulnerability |
| CVE-2023-36439 | Microsoft Change Server Distant Code Execution Vulnerability |
| CVE-2023-38151 | Microsoft Host Integration Server 2020 Distant Code Execution Vulnerability |
| CVE-2023-38177 | Microsoft SharePoint Server Distant Code Execution Vulnerability |
Spoofing (9 CVEs)
| Vital severity | |
| CVE-2023-36007 | Microsoft Ship Buyer Voice survey from Dynamics 365 Spoofing Vulnerability |
| CVE-2023-36016 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36018 | Visible Studio Code Jupyter Extension Spoofing Vulnerability |
| CVE-2023-36030 | Microsoft Dynamics 365 Gross sales Spoofing Vulnerability |
| CVE-2023-36031 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36035 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36410 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Data Disclosure (6 CVEs)
| Crucial severity | |
| CVE-2023-36052 | Azure CLI REST Command Data Disclosure Vulnerability |
| Vital severity | |
| CVE-2023-36043 | Open Administration Infrastructure Data Disclosure Vulnerability |
| CVE-2023-36398 | Home windows NTFS Data Disclosure Vulnerability |
| CVE-2023-36404 | Home windows Kernel Data Disclosure Vulnerability |
| CVE-2023-36406 | Home windows Hyper-V Data Disclosure Vulnerability |
| CVE-2023-36428 | Microsoft Native Safety Authority Subsystem Service Data Disclosure Vulnerability |
Safety Function Bypass (5 CVEs)
| Vital severity | |
| CVE-2023-36021 | Microsoft Host Integration Server 2020 Safety Function Bypass Vulnerability |
| CVE-2023-36025 | Home windows SmartScreen Safety Function Bypass Vulnerability |
| CVE-2023-36037 | Microsoft Excel Safety Function Bypass Vulnerability |
| CVE-2023-36413 | Microsoft Workplace Safety Function Bypass Vulnerability |
| CVE-2023-36560 | ASP.NET Safety Function Bypass Vulnerability |
Denial of Service (4 CVE)
| Vital severity | |
| CVE-2023-36038 | ASP.NET Core Denial of Service Vulnerability |
| CVE-2023-36046 | Home windows Authentication Denial of Service Vulnerability |
| CVE-2023-36392 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-36395 | Home windows Deployment Companies Denial of Service Vulnerability |
Appendix B: Exploitability
It is a listing of the November CVEs judged by Microsoft to be extra more likely to be exploited within the wild throughout the first 30 days post-release, in addition to these already identified to be beneath exploit. Every listing is additional organized by CVE.
| Exploitation detected | |
| CVE-2023-36025 | Home windows SmartScreen Safety Function Bypass Vulnerability |
| CVE-2023-36033 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
| Exploitation extra seemingly inside 30 days | |
| CVE-2023-36017 | Home windows Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2023-36035 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36394 | Home windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36399 | Home windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36413 | Microsoft Workplace Safety Function Bypass Vulnerability |
| CVE-2023-36424 | Home windows Widespread Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36439 | Microsoft Change Server Distant Code Execution Vulnerability |
| CVE-2023-38177 | Microsoft SharePoint Server Distant Code Execution Vulnerability |
Appendix C: Merchandise Affected
It is a listing of November’s patches sorted by product household, then sub-sorted by severity. Every listing is additional organized by CVE. Patches which might be shared amongst a number of product households are listed a number of instances, as soon as for every product household.
Home windows (29 CVEs)
| Crucial severity | |
| CVE-2023-36397 | Home windows Pragmatic Common Multicast (PGM) Distant Code Execution Vulnerability |
| CVE-2023-36400 | Home windows HMAC Key Derivation Elevation of Privilege Vulnerability |
| Vital severity | |
| CVE-2023-36017 | Home windows Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2023-36025 | Home windows SmartScreen Safety Function Bypass Vulnerability |
| CVE-2023-36028 | Microsoft Protected Extensible Authentication Protocol (PEAP) Distant Code Execution Vulnerability |
| CVE-2023-36033 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-36046 | Home windows Authentication Denial of Service Vulnerability |
| CVE-2023-36047 | Home windows Authentication Elevation of Privilege Vulnerability |
| CVE-2023-36392 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-36393 | Home windows Person Interface Software Core Distant Code Execution Vulnerability |
| CVE-2023-36394 | Home windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36395 | Home windows Deployment Companies Denial of Service Vulnerability |
| CVE-2023-36396 | Home windows Compressed Folder Distant Code Execution Vulnerability |
| CVE-2023-36398 | Home windows NTFS Data Disclosure Vulnerability |
| CVE-2023-36399 | Home windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36401 | Microsoft Distant Registry Service Distant Code Execution Vulnerability |
| CVE-2023-36402 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
| CVE-2023-36403 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36404 | Home windows Kernel Data Disclosure Vulnerability |
| CVE-2023-36405 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36406 | Home windows Hyper-V Data Disclosure Vulnerability |
| CVE-2023-36407 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36408 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36423 | Microsoft Distant Registry Service Distant Code Execution Vulnerability |
| CVE-2023-36424 | Home windows Widespread Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36425 | Home windows Distributed File System (DFS) Distant Code Execution Vulnerability |
| CVE-2023-36427 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36428 | Microsoft Native Safety Authority Subsystem Service Data Disclosure Vulnerability |
Dynamics 365 (5 CVEs)
| Vital severity | |
| CVE-2023-36007 | Microsoft Ship Buyer Voice survey from Dynamics 365 Spoofing Vulnerability |
| CVE-2023-36016 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36030 | Microsoft Dynamics 365 Gross sales Spoofing Vulnerability |
| CVE-2023-36031 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36410 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Change (4 CVEs)
| Vital severity | |
| CVE-2023-36035 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Change Server Spoofing Vulnerability |
| CVE-2023-36439 | Microsoft Change Server Distant Code Execution Vulnerability |
Workplace (4 CVEs)
| Vital severity | |
| CVE-2023-36037 | Microsoft Excel Safety Function Bypass Vulnerability |
| CVE-2023-36041 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2023-36045 | Microsoft Workplace Graphics Distant Code Execution Vulnerability |
| CVE-2023-36413 | Microsoft Workplace Safety Function Bypass Vulnerability |
Visible Studio (4 CVEs)
| Vital severity | |
| CVE-2023-36018 | Visible Studio Code Jupyter Extension Spoofing Vulnerability |
| CVE-2023-36042 | Visible Studio Denial of Service Vulnerability |
| CVE-2023-36049 | .NET, .NET Framework, and Visible Studio Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Safety Function Bypass Vulnerability |
ASP.NET (3 CVEs)
| Vital severity | |
| CVE-2023-36038 | ASP.NET Core Denial of Service Vulnerability |
| CVE-2023-36560 | ASP.NET Safety Function Bypass Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Safety Function Bypass Vulnerability |
Azure (3 CVEs)
| Crucial severity | |
| CVE-2023-36052 | Azure CLI REST Command Data Disclosure Vulnerability |
| Vital severity | |
| CVE-2023-36043 | Open Administration Infrastructure Data Disclosure Vulnerability |
| CVE-2023-36437 | Azure DevOps Server Distant Code Execution Vulnerability |
.NET (2 CVEs)
| Vital severity | |
| CVE-2023-36049 | .NET, .NET Framework, and Visible Studio Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Safety Function Bypass Vulnerability |
Defender (1 CVE)
| Crucial severity | |
| CVE-2023-36422 | Microsoft Home windows Defender Elevation of Privilege Vulnerability |
Host Integration Server (1 CVE)
| Vital severity | |
| CVE-2023-38151 | Microsoft Host Integration Server 2020 Distant Code Execution Vulnerability |
On-Premises Information Gateway (1 CVE)
| Vital severity | |
| CVE-2023-36021 | Microsoft Host Integration Server 2020 Safety Function Bypass Vulnerability |
SharePoint (1 CVE)
| Vital severity | |
| CVE-2023-38177 | Microsoft SharePoint Server Distant Code Execution Vulnerability |
Appendix D: Different Merchandise
It is a listing of advisories and knowledge on different related CVEs within the November Microsoft launch, sorted by product.
Microsoft Servicing Stack Updates
| ADV990001 | Newest Servicing Stack Updates |
Adobe Acrobat Reader Bulletin APSB23-54: Safety updates accessible for Acrobat Reader (17 CVEs)
| CVE-2023-44336 | Use After Free (CWE-416) |
| CVE-2023-44337 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44338 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44339 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44340 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44348 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44356 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44357 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44358 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44359 | Use After Free (CWE-416) |
| CVE-2023-44360 | Out-of-bounds Learn (CWE-125) |
| CVE-2023-44361 | Use After Free (CWE-416) |
| CVE-2023-44365 | Entry of Uninitialized Pointer (CWE-824) |
| CVE-2023-44366 | Out-of-bounds Write (CWE-787) |
| CVE-2023-44367 | Use After Free (CWE-416) |
| CVE-2023-44371 | Use After Free (CWE-416) |
| CVE-2023-44372 | Use After Free (CWE-416) |
Adobe ColdFusion Bulletin APSB23-52: Safety updates accessible for Adobe ColdFusion (7 CVEs)
| CVE-2023-44347 | Improper Entry Management (CWE-284) |
| CVE-2023-44350 | Deserialization of Untrusted Information (CWE-502) |
| CVE-2023-44351 | Deserialization of Untrusted Information (CWE-502) |
| CVE-2023-44352 | Cross-site Scripting (Mirrored XSS) (CWE-79) |
| CVE-2023-44353 | Deserialization of Untrusted Information (CWE-502) |
| CVE-2023-44354 | Improper Authentication (CWE-287) |
| CVE-2023-44355 | Improper Enter Validation (CWE-20) |
Related MITRE releases (2 CVEs)
| CVE-2023-24023 | MITRE: CVE-2023-24023 Bluetooth Spoofing Vulnerability |
| CVE-2023-44487 | MITRE: CVE-2023-44487 HTTP/2 Speedy Reset Assault |
Related to CBL-Mariner (5 CVEs)
| CVE-2020-8554 | Kubernetes man within the center utilizing LoadBalancer or ExternalIPs |
| CVE-2023-46753 | [FRRouting issue; no title provided] |
| CVE-2023-46316 | [traceroute issue; no title provided] |
| CVE-2020-14343 | [PyYAML library issue; no title provided] |
| CVE-2020-1747 | [PyYAML library issue; no title provided] |
Related to Edge / Chromium (21 CVEs)
| CVE-2023-36014 | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |
| CVE-2023-36022 | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |
| CVE-2023-36024 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2023-36027 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2023-36029 | Microsoft Edge (Chromium-based) Spoofing Vulnerability |
| CVE-2023-36034 | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |
| CVE-2023-5346 | Chromium: CVE-2023-5346 Sort Confusion in V8 |
| CVE-2023-5480 | Chromium: CVE-2023-5480 Inappropriate implementation in Funds |
| CVE-2023-5482 | Chromium: CVE-2023-5482 Inadequate information validation in USB |
| CVE-2023-5849 | Chromium: CVE-2023-5849 Integer overflow in USB |
| CVE-2023-5850 | Chromium: CVE-2023-5850 Incorrect safety UI in Downloads |
| CVE-2023-5851 | Chromium: CVE-2023-5851 Inappropriate implementation in Downloads |
| CVE-2023-5852 | Chromium: CVE-2023-5852 Use after free in Printing |
| CVE-2023-5853 | Chromium: CVE-2023-5853 Incorrect safety UI in Downloads |
| CVE-2023-5854 | Chromium: CVE-2023-5854 Use after free in Profiles |
| CVE-2023-5855 | Chromium: CVE-2023-5855 Use after free in Studying Mode |
| CVE-2023-5856 | Chromium: CVE-2023-5856 Use after free in Facet Panel |
| CVE-2023-5857 | Chromium: CVE-2023-5857 Inappropriate implementation in Downloads |
| CVE-2023-5858 | Chromium: CVE-2023-5858 Inappropriate implementation in WebApp Supplier |
| CVE-2023-5859 | Chromium: CVE-2023-5859 Incorrect safety UI in Image In Image |
| CVE-2023-5996 | Chromium: CVE-2023-5996 Use after free in WebAudio |